In this issue:
Editor’s Corner. This Week in IT. Still running Windows Server 2008 or 2012? Planning an Azure Hybrid solution? Azure Virtual Desktop news. Word What? IT Bookshelf: The GDPR Challenge. How to Merge Two Columns in Microsoft Excel. Bequeathing electrons. Plus lots more — read it all, read it here on WServerNews!

Are you smart enough to solve this puzzle? And more importantly, are you smart in how you deploy Windows? Photo by Volodymyr Hryshchenko on Unsplash
Got questions? Ask our readers!
WServerNews goes out each week to almost 200,000 IT pro subscribers worldwide! That’s a lot of expertise to tap into. Do you need help with some technical problem or are looking for expert advice on something IT-related? You can Ask Our Readers for help by emailing us your problem or question. Do it today!
Help spread the news!
Please tell all your colleagues and friends about WServerNews and its companion newsletter FitITproNews, and let them know that they can subscribe to these and other TechGenix newsletters for free by going here. Thanks!!
Editor’s Corner
A few weeks ago the following news item entered my inbox:
PDQ.com, a leading provider of IT asset management software, announced today its acquisition of SmartDeploy, an industry leader in remote computer management. “We’re fortunate to team up with SmartDeploy,” said Jaren Nichols, CRO of PDQ.com. “Our customers passionately endorse SmartDeploy’s imaging capabilities. Internally, we love it. The combination of PDQ and SmartDeploy should prove even more convenient for sysadmins. We’re thrilled to welcome SmartDeploy’s team and customers into the PDQ family.”
That’s a pretty smart business move in my opinion. I actually first received my Microsoft MVP award in the technical area of Setup-Deployment (see proof below) and I used to write articles on deployment for TechGenix quite often around a decade ago. This was back when Microsoft Deployment Toolkit (MDT) was hot stuff. MDT still can be pretty useful for some customers, but Windows Autopilot is all the rage nowadays, at least from Microsoft’s perspective.
That perspective has a limited horizon of course, because Redmond tends to look only as far as their own city limits. But there’s more out there in the big wide world than just Microsoft’s way of doing things. That’s where SmartDeploy comes into the picture. I mentioned it several years ago calling it “MDT on steroids” in an article I wrote describing some third-party alternatives for building and deploying Windows images. Then later I dedicated a whole article to SmartDeploy, describing its features and capabilities with a brief walkthrough of how IT can use it to deploy Windows from the cloud.
And this recently announced acquisition of SmartDeploy by PDQ is also, in my opinion, pretty smart. PDQ is one of several popular patch management solutions that I briefly reviewed in this TechGenix article, the other solutions I covered being Patch My PC, GFI LanGuard, Manage Engine Desktop Central, Ivanti, SolarWinds Patch Manager, BatchPatch and 0patch. All of these are good, solid patching solutions used by many of my colleagues. But by combining the patching power of PDQ with the cloud deployment capabilities of SmartDeploy, PDQ steals a bit more thunder from Redmond’s storehouse.
It’ll be interesting to see how things develop in the Windows management solutions marketplace during the next couple of years. Will some vendors disappear? Will more acquisitions occur? Only time will tell, I guess. What are your thoughts?
–Mitch
P.S. Almost forgot the proof I promised:
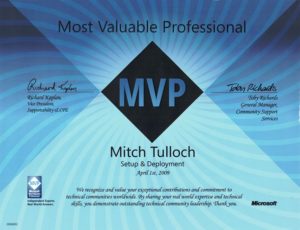
Caption: My Microsoft MVP award certificate proudly hanging in my Gallery of Self-Effacement.
Anyways, the above will have to do as I threw out the hunk of lucite.
This Week in IT
A compendium of recent IT industry news compiled by Your Editors. Feel free to email us if you find a news item you think our newsletter readers might be interested in.
Biggest item in the news probably is that two factories used by Western Digital and Kioxia have discovered contamination that affects at least 7 billion gigabytes of flash memory (Ars Technica). For another take on this matter see this article on How-To Geek. We wonder whether this will set off a rush of hoarding to corner the flash memory market. Another related worry is the potential impact that a Russia-Ukraine conflict might have on the chip materials market. Tom’s Hardware reminds us that prices rose nearly 600% during the Crimean crisis in 2014. Strange times we live in, especially if you’re a cyborg.
In other news, Microsoft is apparently looking to buy Mandiant a cybersecurity company previously known as FireEye (Seeking Alpha). Cyberattacks are big problems nowadays, even if you’re running Linux as ZDNet informs us. Fortunately there seem to be effective steps companies can take—such as Google’s decision to turn on 2FA by default for users which they claim has resulted in 50% fewer account breaches (Engadget). TechGenix has a number of good articles on multi-factor authentication including implementing it with Microsoft Teams, enabling it for Microsoft 365, and using it when resetting passwords with Specops uReset. Kerio Control, the next-generation firewall from GFI for small and medium-sized businesses, also employs two-step verification to protect access to your network when administering from the Internet.
And for more cyber worries, Security Week informs us about almost two dozen UEFI vulnerabilities that affect millions of devices from 25 major vendor, including HP, Lenovo, Fujitsu, Microsoft, Intel, Dell, Bull (Atos) and Siemens. This is seriously not very good news for many of us IT wranglers. That’s it now for this week as I’m scared enough as it is!!
Still running Windows Server 2008 or 2012?
If you’re running any older versions of Windows Server you should be aware of end of support timelines and how you can purchase extended security updates for your servers to keep them secure. This article on the Microsoft Tech Community blogs has more info.
Planning an Azure Hybrid solution?
If you are then you should check out the Azure Stack HCI video playlist that uber-geek Thomas Maurer has put together. It’s great—check out the link on his blog post on the ITOps Talk Blog. Make sure you have some popcorn handy while you watch the videos.
Azure Virtual Desktop news
And continuing with Azure, Justin Shiah at Microsoft informs us about a new feature of Azure Virtual Desktop called Trusted Launch virtual machines which let’s you use Secure Boot and virtual TPM and other security features to strengthen the security posture of your VMs. See the details here on the Azure Virtual Desktop Blog.
Also another great new feature of Azure Virtual Desktop that is now in public preview is using FSLogix profiles for Azure AD-joined VMs in Azure Virtual Desktop. FSLogix is a terrific platform that was acquired by Microsoft several years ago and makes it easy to manage user profiles in Windows remote computing environments.
And finally, Start VM on Connect is now generally available for Azure Virtual Desktop. This feature lets users turn on their VMs only when they need them. Which means of course it can save your organization money if you have Azure Virtual Desktop deployed in your environment.
AND FINALLY: Word What?
And in the “Golly are they still around?” department comes this review of Corel WordPerfect Office 2021 (PCMag). Wow, I didn’t know that WordPerfect was still in development let alone still available for purchase! Makes me remember the days when we used Word 6.0 on MS-DOS 6.22 for our business. Are any of our newsletter readers using WordPerfect? Let us know.
And speaking of those good old times, I confess I didn’t even know that PCMag is still around. (Checking…) OK so it’s no longer in print, just online only since 2009. But I haven’t heard about PCMag for years, guess I must travel in other circles nowadays.
But Maximum PC is still in print—yay!
Let’s kill a tree today.
Got comments about anything in this issue?
Email us! We love hearing from our readers!
Meet the Editors!

MITCH TULLOCH is Senior Editor of both WServerNews and FitITproNews and is a widely recognized expert on Windows Server and cloud technologies. He has written more than a thousand articles and has authored or been series editor for over 50 books for Microsoft Press and other publishers. Mitch has also been a twelve-time recipient of the Microsoft Most Valuable Professional (MVP) award in the technical category of Cloud and Datacenter Management. He currently runs an IT content development business in Winnipeg, Canada that produces books, ebooks, whitepapers, case studies, courseware, documentation, newsletters and articles for various companies.

INGRID TULLOCH is Associate Editor of both WServerNews and FitITproNews. She was co-author of the Microsoft Encyclopedia of Networking from Microsoft Press and collaborated on developing university-level courses in Information Security Management for a Masters of Business Administration (MBA) program. Ingrid also manages Research and Development for the IT content development business she runs together with Mitch.
Mailbag
Our last newsletter titled Is Open Source security an illusion? produced the following comments from reader Matt Western in Australia:
Hi Mitch, re Open Source (OS) security. I’ve always considered OS software to be dicey. If the software is open for anyone to modify, then it’s open to anyone to inject nastiness into it. I would have thought that was obvious to anyone.
There’s something else to consider as well, which is compensation. I’m no lawyer, but if you use an item and that item causes you and/or your business significant loss, you should be able to pursue compensation for your loss from the items’ manufacturer. Would that be possible with OS software? It is with Microsoft software.
Who is answerable for failures within OS software? Can an individual who added a component be held accountable for any damage or loss incurred due to their component being faulty? If your business losses significant income due to component XYZ failing, who do you chase up for compensation?
Personally I’ve only ever broadly considered OS software for use in home or low risk environments & that’s based mainly on business reasons, not technical reasons.
Those are good questions especially the one about liability (who answers) when bugs in or other issues with open source software result in business losses for you. IANAL so I don’t know the answer to that one, or even whether such matters have ever been litigated. Are any other readers out there familiar with the legal liability side of using open source software? Email us.
And reader Jeffrey Harris was inspired by our February 7th newsletter Make sure you sanitize (your data!) to send us some observations and recommendations:
Regarding sanitizing disks, I have used different methods. First, for physical destruction, nothing beats taking a drive apart, removing the platters, and sanding them, but I would recommend that technique only if the drive has failed and cannot be wiped with a software method.
For software wiping, I use a’Parted Magic disk (link on this page:’https://www.pcworld.com/article/461014/how-to-securely-erase-your-hard-drive.html).’It calls the BIOS secure wipe command that is built into all modern BIOSes since about 2005 (see https://www.techrepublic.com/article/perform-a-secure-disk-wipe-with-windows-10s-format-command/).’It used to be free (which is how I have a copy), but now requires a payment to obtain.
Here is an alternate free mechanism using a Linux live disk: https://grok.lsu.edu/Article.aspx?articleid=16716.
Also, Windows versions since Vista have a secure wipe parameter /P:<number of passes> built into the format command.’However, the boot drive itself and any drives in use (i.e., having page files) cannot be formatted themselves without booting into recovery mode or using a Windows PE disk or Windows installer disk to boot from, or the boot drive being moved to another system as a secondary drive.
The methods above are for hard disks, and some of them are for hard disks directly connected to an PATA or SATA controller.’For SSDs, I would follow the advice that you provided, which is to use the manufacturer’s utility.’There are too many pages that alternatively support and refute the ability to securely wipe SSD devices (including flash drives) using hard drive tools.
Great suggestions, thanks!
IT Bookshelf: The GDPR Challenge
The GDPR Challenge: Privacy, Technology, and Compliance in an Age of Accelerating Change (CRC Press, 2021) is a useful and necessary book for IT senior management in businesses and organizations whose operations, workforce or sales span geographical areas that include countries in the European Union.
While many expected the COVID-19 pandemic to shift attention of EU authorities away from enforcing GDPR compliance towards more pressing challenges, this has clearly not been the case as is demonstrated by the recent news about how Google Analytics has been found to be in breach of EU privacy laws in France (TechCrunch). And when I talk with my IT pro colleagues around the world about GDPR compliance, I find this still to be a hot issue for many of them. For example, Martin Urwaleck who leads IT team for a pharmaceutical payroll company based in Vienna, Austria, recently shared with me the following comments on how the sudden need to move towards remotework during the pandemic has been complicated by the need to remain GDPR-compliant:
“Ensuring GDPR compliance has had a severe impact on our remotework solution. Currently, we use two remotework technologies: office equipment over VPN tunnel and personal equipment using RDS. The problem? Microsoft Teams. Teams just doesn’t play well with RDS, yet it’s an essential part of our daily business because a lot of our business information is shared via Teams. And our business information must of course be GDPR compliant, but this is difficult to do with Teams over RDS.
“At the moment for internal reasons we cannot enforce that Teams be only used on company equipment, though we are planning do that in the near future. As a result we are currently considering moving from RDS to Azure Desktop Services since Teams has no problem with that approach. But unfortunately we also have a GDPR issue with that approach—think of the Schrems II decision. Our argument in this case is that we can in fact do GDPR but only as good as is possible.
“We also have other options deployed involving Microsoft Intune and mobile devices, both company-owned and personal devices. And this is working fine now but for one exception and an unresolved issue. The exception is that with Apple’s devices it’s possible to completely wipe personal devices, but under GDPR it’s clear that this shouldn’t be possible. And the unresolved issue is that when we move apps from company-managed devices to personally-managed devices, it can take up to 8 hours for the data on them to be removed. We’re still working on that. So we’ve had lots of GDPR-related challenges to deal with regarding remotework accelerated by the pandemic.”
Stories like Martin’s and similar ones I’ve heard from other colleagues demonstrate that GDPR compliance is still a very big concern with many organizations. And this is true regardless of which country they operate in, because GDPR has effectively become the de facto international standard for data privacy around the world.
The GDPR Challenge consists of a series of essays on different topics written by different legal and cybersecurity experts. Topics cover a wide spectrum including governance, eDiscovery, biometrics, cyberinsurance, social media, and more. The book is more of a reference work than a primer on these subjects, so some chapters will probably be more useful than others for your IT management team.
Some of the things I learned reading through this book include:
- How Article 22 impacts companies like Facebook and Google through the matter of algorithmic accountability (bringing their algorithms into the sunshine).
- How the US and EU differ in their legal approach on matters of data privacy, free speech and the right to be forgotten.
- The complexity of performing eDiscovery across international borders and the resulting need for organizations to plan for data-intensive litigation.
- That the GDPR has been the biggest boon imaginable for the cyberinsurance business because of the many unknowns companies face regarding their potential GDPR exposure.
There’s a lot more necessary and useful information to be gleaned by reading this book, and I recommend your IT management get hold of it and review its contents with their legal department. You can buy the book here on Amazon.
Admin Toolbox
FastAdmin is a practical system administrators utility that allows you to remotely monitor and manage Windows computers and servers in your Active Directory domain:
https://wizardsoft.nl/products/fastadmin
TraceWrangler is a network capture file toolkit running on Windows that supports PCAP as well as PCAPng which is the standard file format used by Wireshark:
https://www.tracewrangler.com/
RandSearch lets you use randomly different search providers to get different perspectives, ideas, and results with every search:
https://randsearch.daniel.priv.no/
The Windows 10 Update Assistant downloads and installs feature updates on your device:
https://support.microsoft.com/en-ca/help/3159635/windows-10-update-assistant
Tip of the Week
This week’s tip can be found on How-To Geek:
How to Merge Two Columns in Microsoft Excel
https://www.howtogeek.com/782211/how-to-merge-two-columns-in-microsoft-excel/
Factoid: Bequeathing electrons
Our previous factoid and question was this:
Fact: Researchers use tiny magnetic swirls to generate true random numbers.
Source: https://phys.org/news/2022-02-tiny-magnetic-swirls-true-random.html
Question: When was the last time you ran a program to generate a random number?
Not even a random answer came into our Inbox for this question, just the usual spam.
Let’s move on to this week’s factoid:
Fact: Love and logins: Who gets custody of passwords in a breakup?
Source: https://apnews.com/article/technology-lifestyle-philanthropy-0237c5054c9e020c6929700ddd0caa48
Question: Boy this article got me thinking. About wills in particular. Technology has disrupted many aspects of our society in recent years, and I’m wondering, has it also disrupted the traditional way of writing up wills, powers of attorney and similar documents? Are these done online now in some jurisdictions? Can you write up your will on your phone and have it legally enforced? Can you have digital-only wills or does there still need to be a hardcopy stored somewhere? Are people including clauses in their wills that grant password usage rights to beneficiaries or to executors? And what about bequeathing digital-only items like NFTs to beneficiaries? I can hear it now: “And to Roger my younger son, I bequeath all of my electrons.” Anyways, what examples if any of such practices have our tech-savvy IT pro readers seen or heard about? Let us know!
Email us your answer and we’ll include it in our next issue!
Subscribe today to WServerNews!
Subscribe today and join almost 200,000 other IT professionals around the world who subscribe to our newsletter! Just go to this page and select WServerNews and you’ll receive it every Monday in your inbox.
Conference Calendar
NOTE: Conference dates and locations are subject to change
Big Data & AI World — March 2-3, 2022 in London, UK
https://www.bigdataworld.com/welcome
Mobile World Congress — June 29-July 1, 2022 in Shanghai
Cisco Live Las Vegas – June 12-16, 2022
https://www.ciscolive.com/us.html?zid=cl-global
HPE Discover 2022 – June 28-30 in Las Vegas, USA
https://www.hpe.com/us/en/discover.html
Def Con 30 — Aug 11-14, 2022 in Las Vegas, USA
Big Data Expo — Sept 14-15, 2022 in Utrecht, The Netherlands
https://www.bigdata-expo.nl/en
Podcast Corner
RunAsRadio: Getting Beyond Internet Explorer with Joel Hawks
Heavy Networking: Go Vs. Python For Network Engineers
https://packetpushers.net/series/weekly-show/
Clear To Send: 802.11ax 1024-QAM & HE-MCSs
Risky Business: FBI arrests deeply annoying cryptocurrency influencers
https://risky.biz/netcasts/risky-business/
Microsoft Cloud Show: Microsoft Tries to Make Nice With FTC and Microsoft Teams Saving the Environment
http://www.microsoftcloudshow.com/podcast
New on Techgenix.com
Do You Like Your PowerShell Wet or Dry?
https://techgenix.com/do-you-like-your-powershell-wet-or-dry/
How to Check Your Windows Server Uptime with PowerShell
https://techgenix.com/check-windows-server-uptime-with-powershell/
Exchange 2016 – AirSync Exceeded Errors
https://techgenix.com/exchange-2016-airsync-exceeded-errors/
Top 6 Open Source AI and ML Tools
https://techgenix.com/open-source-ai-ml-tools/
Exchange 2016 – Working with Nimbus Storage
https://techgenix.com/exchange-2016-working-with-nimbus-storage/
Fun videos from Flixxy
History of Evolution – Hyundai IONIQ 5 Superbowl Ad
https://www.flixxy.com/history-of-evolution-hyundai-ioniq-5-superbowl-ad.htm
Austin Powers Cast Reunites In General Motors Super Bowl Ad
https://www.flixxy.com/austin-powers-cast-reunites-in-general-motors-super-bowl-ad.htm
Don’t Miss Out – Larry David – Super Bowl Ad
https://www.flixxy.com/dont-miss-out-larry-david-super-bowl-ad.htm
Arnold Schwarzenegger Stars as Zeus in BMW’s Super Bowl Commercial
https://www.flixxy.com/arnold-schwarzenegger-stars-as-zeus-in-bmws-super-bowl-commercial.htm
Please tell others about WServerNews!
We hope you enjoyed this issue of WServerNews! Feel free to send us feedback on any of the topics we’ve covered—we love hearing from our readers! And please tell others about WServerNews! It’s free and always will be free—and they can subscribe to it here. Thanks!!!