In this article, we will create the basic infrastructure on Amazon EC2 (Elastic Compute Cloud) to support a new domain controller and member servers joining that new infrastructure. We will be starting with the network side, then spinning the first instance to be the domain controller, and finish the settings to make sure that the infrastructure supports the new Active Directory environment. (For Azure admins new to AWS, check out our previous article here.) When we’re done, you will have built an Active Directory infrastructure in AWS EC2.
Our environment will be simple: A single domain controller, using the infralab.org DNS domain name, and infralab as NetBIOS. However, the same principles applied to this article can be used when extending your datacenter from on-premises to the cloud or when you have a complex cloud environment containing more than two sites.
Active Directory infrastructure in AWS EC2: Setting up the VPC network
Logged on the AWS Console, click on Services and then VPC, which will bring the VPC Dashboard. Since we are using a brand-new subscription, we should have just a few default items. Our first objective is to create a network to support our Active Directory in the AWS Cloud. Click on Start VPC Wizard to commence the process to create the network.
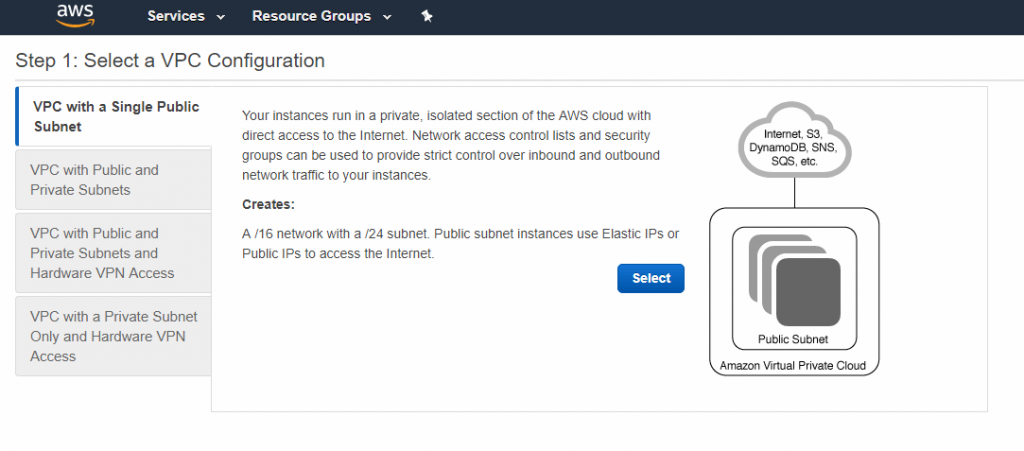
Step 1: Select a VPC Configuration page. We will have four templates to start with. The simplest one is the VPC with a Single Public Subnet. In this scenario, the administrator is able to control the access to the servers either using Security Groups or Network Access controls. That is the VPC configuration that we will be using in this article. Click on Select.
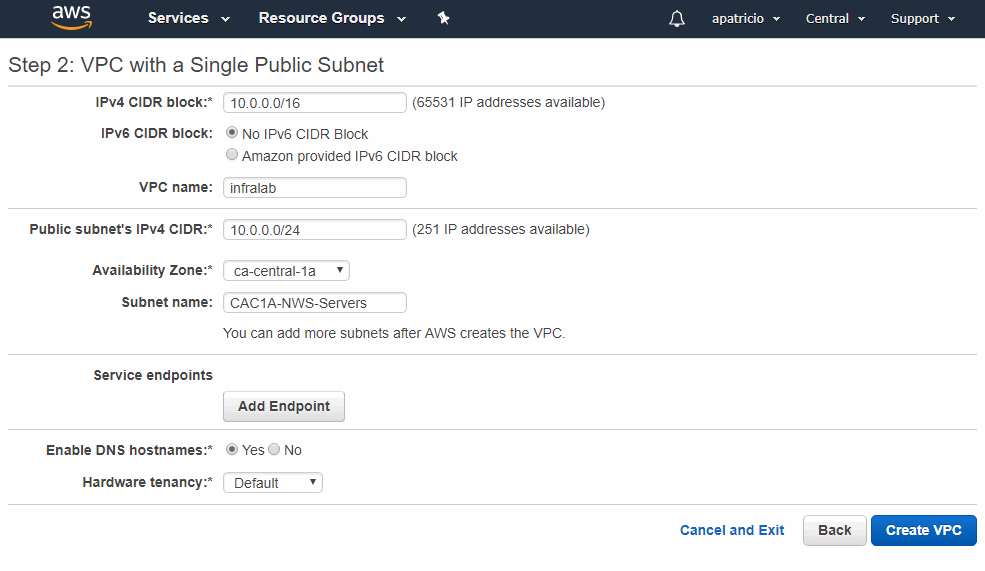
Step 2: VPC with a Single Public Subnet page. The first step is to define the IPv4 block for our VPC. We will be using 10.0.0.0/16, and we need to name the VPC; in our case, it will be called infralab. After that, we need to define one subnet and associate it to an availability zone and define a name for it.
The naming convention is key to keeping consistency on your cloud environment. For this article, we use a name that provides information about the site (CAC1A), the object type (NWS for Network Subnet), and a brief description (Server segment). After configuring the basic networking, click on Create VPC.
By default, the new subnet created during this wizard will not assign Public IPv4 for the servers, which is a nice built-in security feature.
However, in this article we don’t have a VPN connection between our on-premises environment and our AWS Cloud. Thus, we will need Internet access to manage those servers. We will be changing the default settings by clicking on Subnets, select the new subnet that we have just created (CAC1A-NWS-Servers), and click on Subnet Actions, and select Modify auto-assign IP settings, and select Enable auto-assign public IPv4 address on the new page, and click on Save, and then Close.
Creating the new domain controller
At this point we created the basic network infrastructure to support our new environment. Our next step is to create the instance for the first domain controller. Logged on the AWS Console, click on Services, EC2, and on the EC2 Dashboard page, click on Launch Instance. These are the steps required to build the first instance that will run the domain controller.
Step 1: Choose an Amazon Machine Image (AMI) page, select Windows Server 2016 base.
Step 2: Choose an Instance Type page, leave default settings.
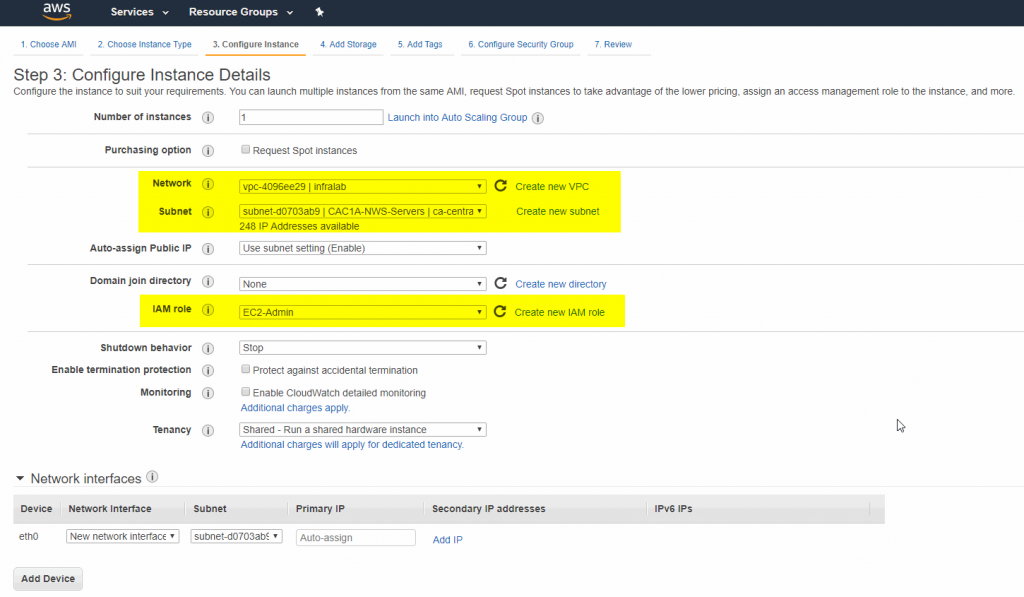
Step 3: Configure Instance Details page. In this step, make sure to configure the new VPC that we have created in the last section, as well as the subnet. One more thing is to configure the IAM Role. We will use a role that has full permission to manage EC2 instances.
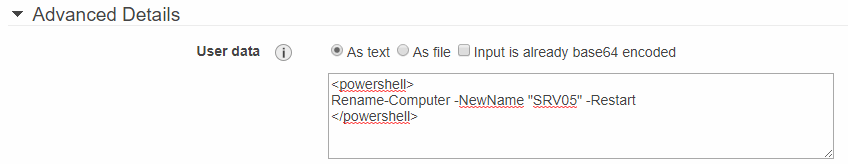
Before moving forward with the wizard, we will add a PowerShell cmdlet to rename the computer name as part of the provisioning process. We will add the following text in the Advanced Details section (see screenshot below). That cmdlet will be executed during the first boot after the instance creation.

Step 4: Add Storage page. Leave default settings.
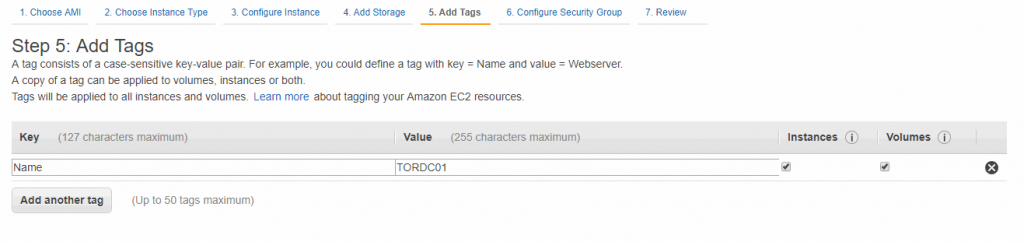
Step 5: Add Tags page. Configure the name to match the name that we added on the server name PowerShell cmdlet.
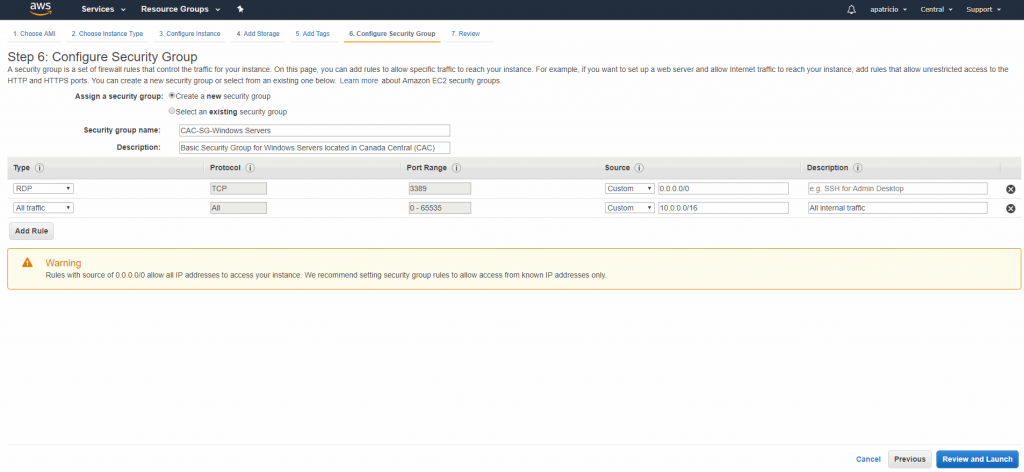
Step 6: Configure Security Group page. In this page, we will create a Security Group to be associated to all servers from this article. We will be using a simple naming convention where we provide the datacenter (CAC, which is Canada Central), a two digit number for the object type (SG for Security Group), and a brief description.
Beside the regular RDP from the Internet to connect on the instances, we are going to allow all traffic among the servers from the subnet that we created as part of our new VPC (10.0.0.0/16). Click on Review and Launch and start the provisioning of the first instance.
We will need a private key to connect on the server. We will create one for all Windows Servers instances that will be part of our infrastructure. Create a new Key Pair and let’s label it as windows.pem file.

Building the first domain controller and adjusting the DHCP
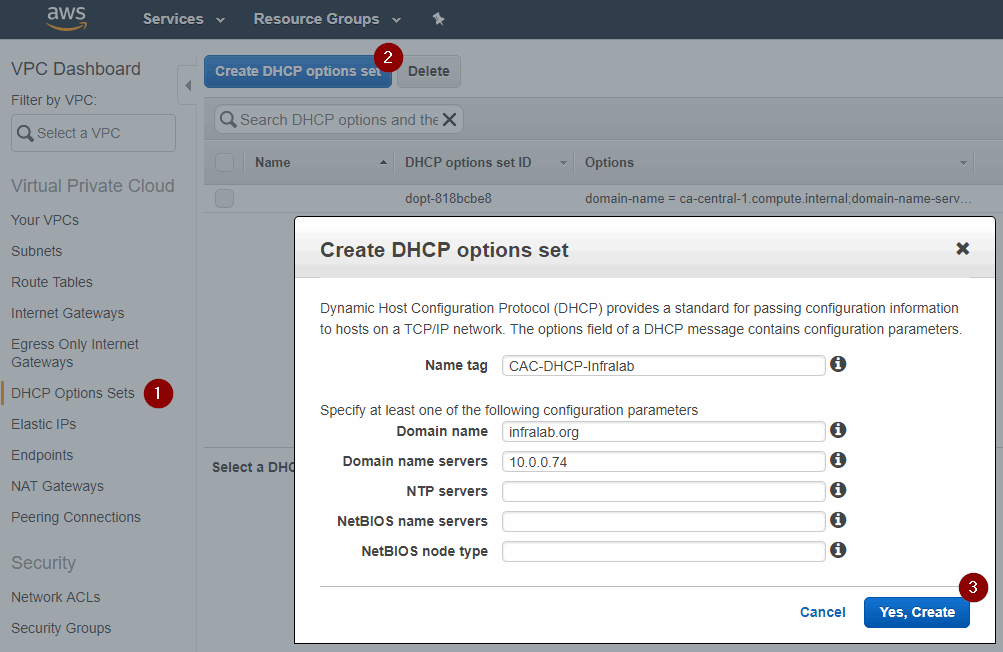
Logged on the new instance (using the private key that we created in the previous step), our first task is to retrieve the current IP of our new instance. In our article the IP is 10.0.0.74. We will need that information to configure the DNS server setting to be assigned to all servers connected to our VPC.
Logged on AWS Console, click on Services, and then VPC. In the new page, click on DHCP Options Sets, and then click on Create DHCP options set, and configure the DNS settings, domain, etc.
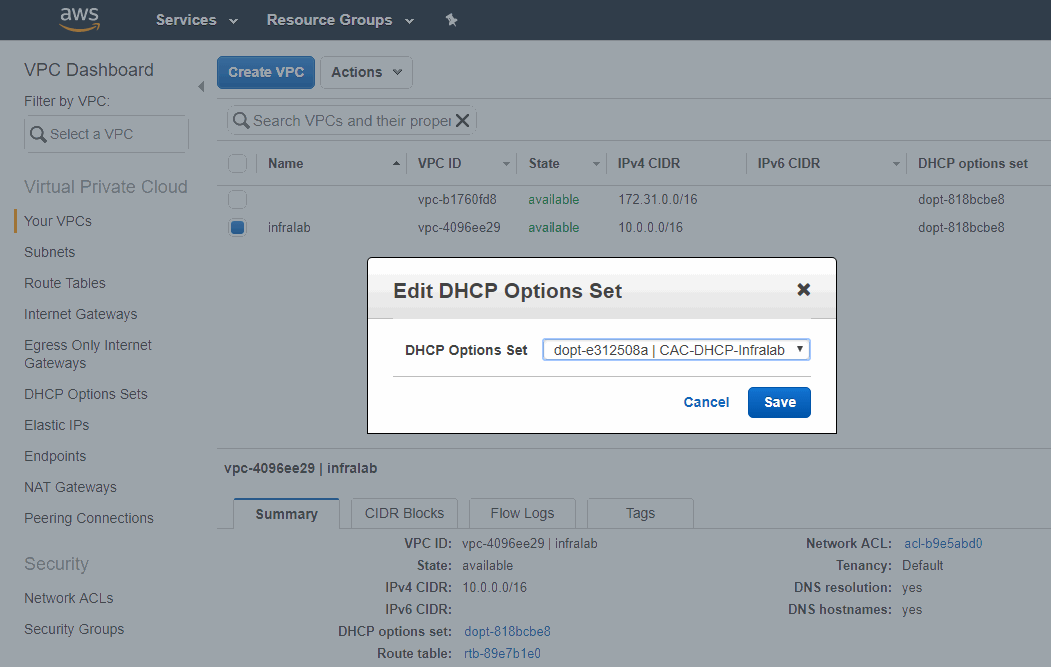
The final step is to associate this brand-new DHCP option to the VPC. Click on Your VPCs item on the left side, select infralab, click on Actions, and then Edit DHCP Options Set. In the new page, select the DHCP options set and click on Save.
After performing the change on the DHCP, we have two options to refresh the setting on the instance that will be our future domain controller. We can either restart the instance or run the ipconfig /release && ipconfig /renew on the command prompt as administrator.
Time to configure the domain controller: The first step is to add the role Active Directory Domain Services to the server, and it can be easily done using PowerShell, as follows:
Add-WindowsFeature AD-Domain-Services -IncludeManagementTools
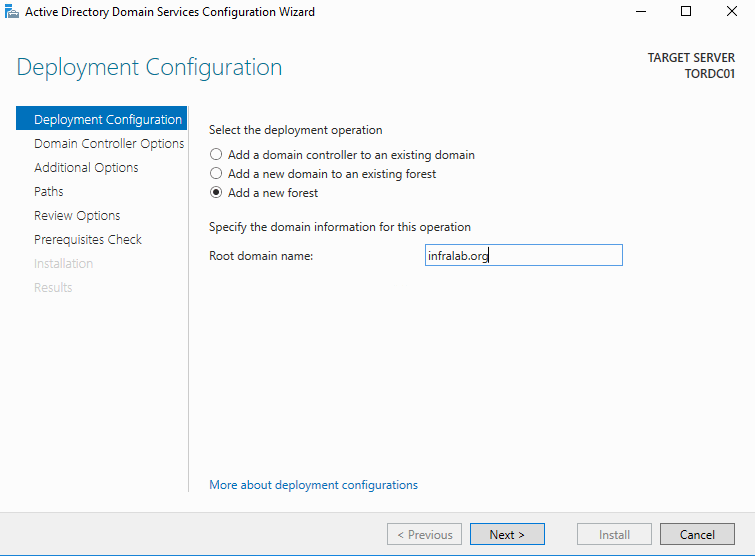
After that, we need to complete the process using Server Manager, and using the option Promote this server to a domain controller. In this article, we are creating from scratch, so the only decision-making required is on the first page where we need to select Add a new forest, and then type in the desired domain name (in our case infralab.org). Also make sure to define the NetBIOS domain name when asked for. In our example it is going to be INFRALAB.
After completing the wizard, the server will be restarted and the server will be ready to be used. After the first logon, my recommendation is to create a second admin account, and rename the password for the administrator. From this point on, this server will no longer use the private key to decrypt the password.
Adding additional servers
Now that we have the infrastructure in place and our first domain controller is up and running, we can start provisioning new servers. Make sure to rename the servers before joining them to the domain. If you are going to create a single instance from the AWS Console, make sure to add the user data for the new server, which will rename it automatically. If not, make sure to rename the server before joining to the domain.
After having the instance up and running, just join the computer into the domain as depicted in the image below and the process should be seamless. Just type in the domain name and enter the credentials.

In these few steps, we have demonstrated how to build the AWS EC2 infrastructure to support a domain controller running on an EC2 instance and all new domain controllers.




awesome , detailed steps are helped a lot. Do we have anything like DNS configuration etc
Thanks so much for whoever put this together! Extremely helpful. I am surprised at the lack of information on how to install AD on AWS instances. Again, thanks so much!
Is it possible to connect on premise Computers and servers. In this setup