Communication between computers is streamlined, quick, and efficient today, and this has opened a world of applications for our ease of living. One of the aspects that have made it possible is the Open Systems Interconnection (OSI) model. In this article, let’s explore what is OSI and how it is beneficial for IT pros, both beginners and experienced, as a tool for network troubleshooting.
What is the OSI model?
The OSI model is a conceptual framework consisting of seven layers that allow computers to communicate with each other. This standardized model was adopted by all major technology companies in the early 1980s to create an ecosystem that allowed computers to send and receive messages quickly and reliably.
A brief history
The journey of every invention or development starts with a problem and knowing this helps to better understand its use and relevance. So, let’s step back a bit to understand the evolution of the OSI model.
It all began in the late 1970s when two groups started working independently to define a common standard that would lay the foundation for the architecture of networking systems. The first group was a part of the International Standards Organization (ISO) while the second was a part of the International Telegraph and Telephone Consultative Committee (CCITT). Both these groups developed and presented two networking models, one apiece each respectively.
In 1983, it was decided to merge the two models to form the Open Systems Interconnection or the OSI model. Though it went through many changes over the years, it continues to be relevant even today, as the de-facto framework for networking.
Next, we will take a look into the working of the OSI model.
How does the OSI model work?
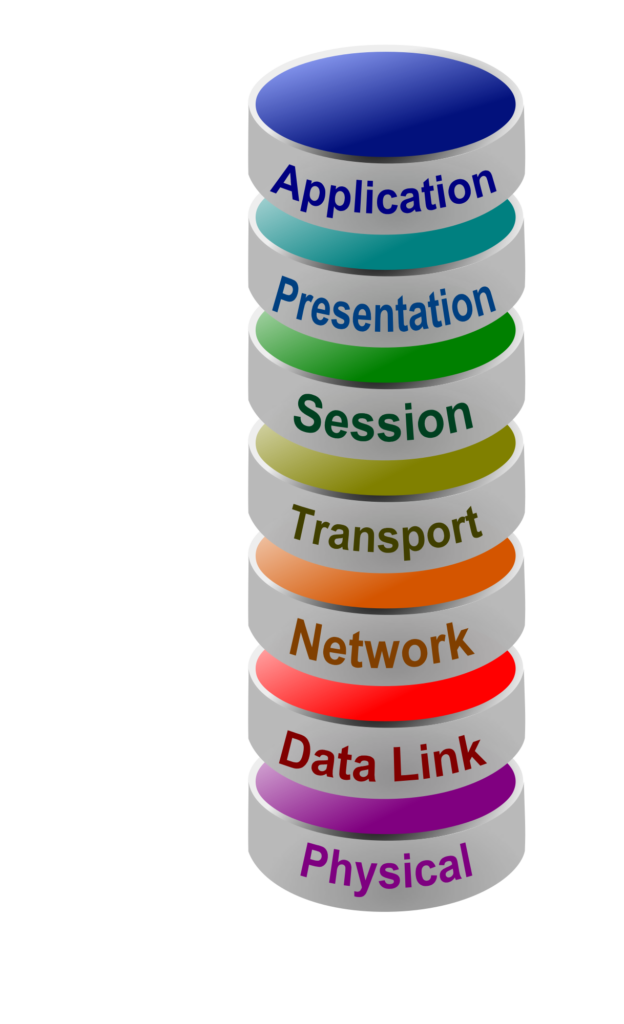
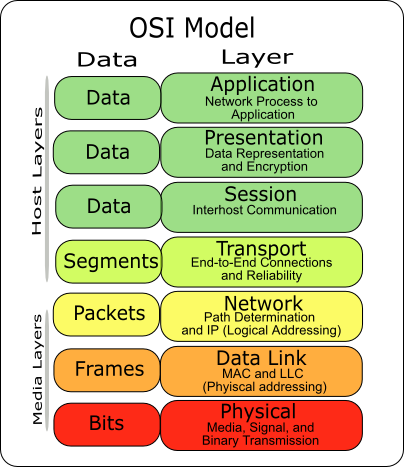
This model consists of seven layers, in this order:
- Physical layer
- Datalink layer
- Network layer
- Transport layer
- Session layer
- Presentation layer
- Application layer
Let’s now take a detailed look at each of these layers.
1. Physical layer
This is the first and the lowest layer and consists of the electronic circuit transmission technologies. Essentially what this means is that the physical layer is responsible for transmitting individual bits from one node to another. It is also responsible for establishing, maintaining, and severing the physical connections.
It also represents the electrical and physical aspects of the system and includes the layout of pins, voltages, cables used, and more. This is why professionals dive into the physical layer to check if the cables are connected and the power is plugged on.
2. Datalink layer
The data link layer is the second layer that is responsible for the transmission of data frames from one node to the other. Besides simply sending and receiving data frames, it also establishes a unique identification number for every device on the network, defines the data format, and also handles error correction.
Since it handles a ton of work such as physical addressing, flow control, and error control, it is divided into two logical sublayers, and they are:
- Logical link control layer: This layer does the bulk of data transmission and is responsible for identifying the address of the receiving layer, transferring packets, and for providing logical control.
- Media access control layer: This layer acts as a link between the logical link layer and the underlying physical layer.
3. Network layer
This is the third layer and is responsible for tracking the location of devices on the network. This layer determines the best routing path for a packet based on the network conditions, priority, and other factors.
As you may have guessed, this is where the routers are specified, and they route your data efficiently to computers located in any part of the world.
Thus, these three lower layers are closely tied to the underlying network, and they deal primarily with data transmission. Also, these layers are implemented with both hardware and software.
4. Transport layer
The transport layer is the fourth layer, and it ensures that messages are transmitted in the order received, without any data duplication. This layer receives data from the upper layers and segments them into small units for easy transmission.
Notably, this layer creates a point-to-point connection between the source and the destination computers to deliver the data efficiently. This layer splits data into small packets, transmits, and reassembles them at the destination using a set of protocols or rules.
Broadly speaking, there are two protocols used for data transmission, and they are Transmission Control Protocol (TCP) and User Datagram Protocol (UDP).
- TCP: This protocol establishes a connection between the hosts and allows the systems to communicate through data packets, where these packets are sent through multiple routes, and eventually, are reassembled by the destination layer.
- UDP: This is another protocol that transmits data packets. The key difference between TCP and UDP is that the latter is highly unreliable as the receiver doesn’t send an acknowledgment and the sender doesn’t wait for one. This can lead to the loss of data packets, hence TCP is considered to be the standard and efficient protocol for data transmission.
5. Session layer
The session layer, as the name suggests, is responsible for managing a session between processes. Typically, a session is required for two devices to talk to each other, and this layer is responsible for creating and managing these sessions. Its activities include setting up the session, managing it, and ending it between applications.
In the process, it handles data control and synchronization between devices.
6. Presentation layer
Also known as the syntax layer, this presentation layer is responsible for preparing and translating the application format to network format, and vice-versa. A good example is the encryption and decryption of data handled by this layer.
It handles data compression as well and is often a part of the operating system.
7. Application layer
This is the top-most layer of the OSI model and it acts as a window for a user to access the network service for data transmission. It handles a wide range of functions including resource allocation, File Transfer, Access, and Management (FTAM), directory services, and mail services.
Some examples of applications that work in this layer include web browsers, email clients, messaging clients, and any other device that interacts with the underlying network for data transmission and receipt.
The upper four layers (4 to 7) handle application-related issues and are implemented in software only.
Example of transmission through the OSI model

To get a better understanding of how these layers come together, let us take the example of an email.
- The application layer is the email client through which a user sends data for transmission.
- The presentation layer converts the data into ASCII format and provides the necessary compression and encryption.
- The session layer starts a session and adds a header to specify it. Next, it establishes a connection between nodes.
- In the transport layer, the messages are divided into data segments and transmitted using the Transmission Control Protocol. It adds the source and destination ports as well.
- The network layer determines the best routing path for the data segments. It also adds the necessary headers and converts these segments into data packets that are passed to the data link layer.
- The data layer converts the packets into frames and adds the physical address of the node.
- Finally, the physical layer puts the data packets received from the data link layer to the physical medium (LAN or WAN) for transmission.
Thus, this is how the data is transmitted through the OSI model.
Advantages of the OSI model
This distinct separation of work across different layers helps with debugging and network troubleshooting and acts as a guide to develop any network model. It supports both connection and connectionless services as well. The OSI model helps administrators to determine the right hardware and software and helps device manufacturers to create devices that can communicate through this model.
For end-users, it helps to quickly and efficiently debug problems as you can work at the right layers instead of sifting through the entire network.
Finally, it is a fairly secure model for data transmission.
Thus, these are the different layers of the OSI model, and due to the many advantages mentioned above, this model has become the de-facto one for data communication.
Featured image: Shutterstock



