Editor’s note: In response to the coronavirus crisis gripping the world, TechGenix is republishing a selection of recent articles, tutorials, and product reviews that contain relevant information for IT pros as their jobs change dramatically. In this review, originally published Oct. 30, 2019, we review Kerio Control, a network-security solution with an included VPN that enables secure remote work.
Product homepage: click here
Free trial offer: click here

Network security tools are notorious for being complex. Many such tools require a steep learning curve, even for seasoned IT pros. However, GFI is bucking the trend with its Kerio Control. Kerio Control is a comprehensive network security application for SMBs that has been specifically designed to be easy to use.
Deployment process
Kerio Control can be downloaded as an ISO file or as a VMware or Hyper-V virtual appliance (physical appliances are also available). For this review, I opted to use the Hyper-V option. The download consisted of a virtual hard disk file (in VHD format). I simply created a Hyper-V virtual machine, and then attached the VHD file.
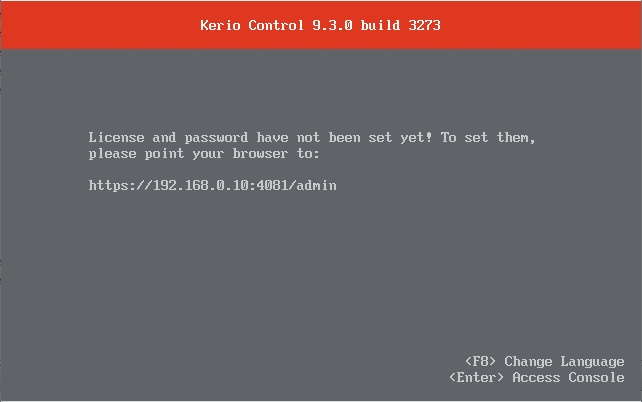
Once the VM had been set up, I booted it and was presented with a message telling me where to point my browser to access the administrative interface. If you look at the screenshot below, you can see that there is a message stating that you can press “Enter” to access the console. I used this option so that I could assign the VM an IP address that fell within the range used on my virtual network.
When I opened a web browser on another machine and navigated to the specified URL, I was presented with the server’s Activation Wizard. The activation process consisted of specifying a language, accepting the license agreement, and setting an initial password.
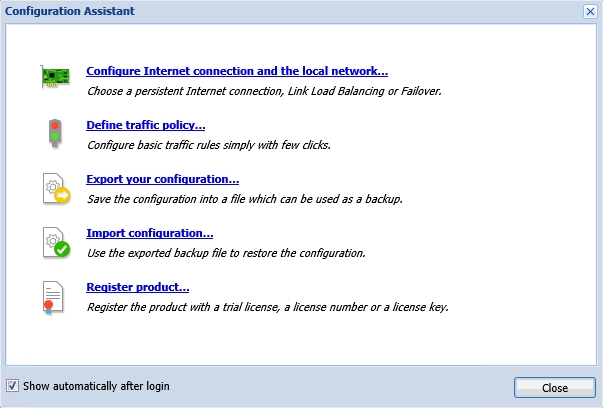
Once I completed the Activation Wizard, I was taken to the Configuration Assistant. As you can see in the screenshot below, the Configuration Assistant helps with all of the initial configuration tasks such as registering your license and configuring Internet connectivity. I found the process of configuring Internet connectivity and registering the product to be simple and intuitive.
With Kerio Control fully configured, I decided to turn my attention to its firewall. The Kerio Control firewall can be configured through a series of traffic rules. One thing that I especially like about Kerio Control is that it displays the traffic rules in a simple and unambiguous way that should make sense to anyone who has basic networking knowledge. You don’t need to be a networking expert to configure the traffic rules. In fact, the most essential rules exist by default. GFI even went so far as to color-code the rules to help illustrate what they do. You can see the traffic rules in the screenshot below.
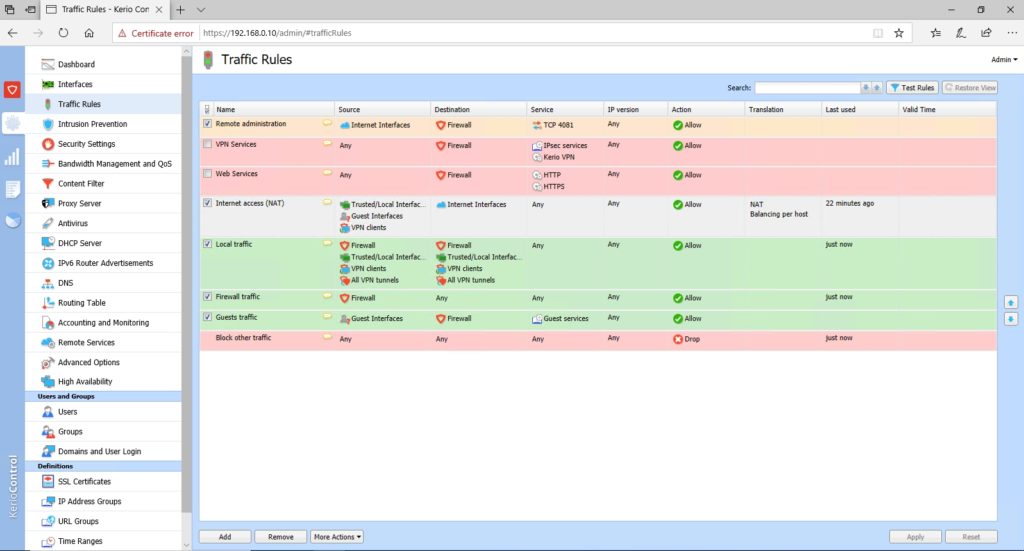
Because these rules exist by default, I didn’t have to do anything special to make Kerio Control function as a NAT router. Once I configured the machines on my test network to use the Kerio Control server as a default gateway, those machines received Internet access without any issues.
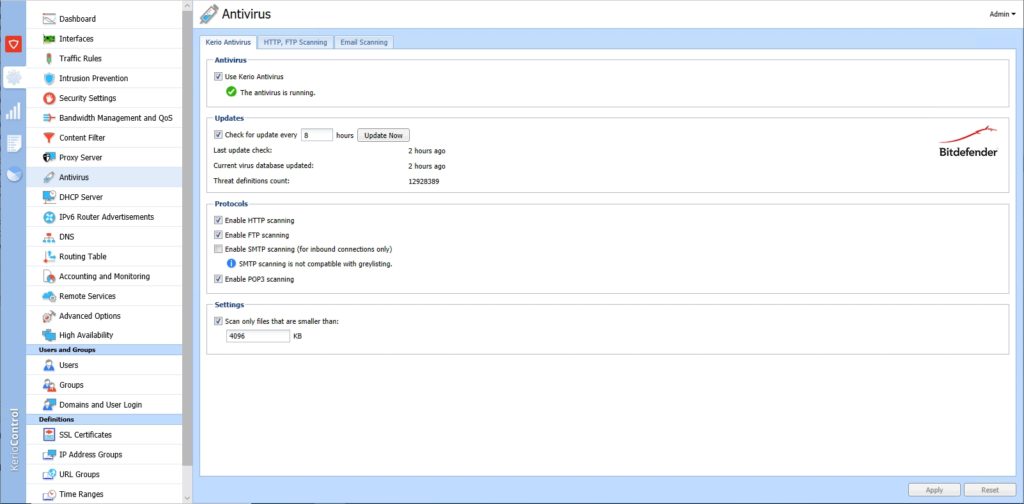
Antivirus
One of Kerio Control’s most noteworthy features is its antivirus capabilities. While legacy antivirus products often focus on scanning files to determine whether or not they contain malicious code, Kerio Control can scan network traffic. As you can see in the next screenshot, Kerio Control can scan both HTTP and FTP traffic. Additionally, the software can check inbound email for malware through SMTP and POP3 protocol scanning.
Web content filtering
Another key capability found within Kerio Control is its ability to filter web content. The content filter interface is nearly identical to the interface used for managing traffic rules but allows admins to regulate the types of Internet traffic that are and are not allowed within the organization. As you can see in the next screenshot, Kerio Control is configured by default to block advertisements and banners, audio and video files, peer-to-peer traffic, and traffic related to hacking and malware. As such, the content rules are not merely designed to prevent users from accessing inappropriate content, but they can also be used as a tool for shielding the organization from attack.
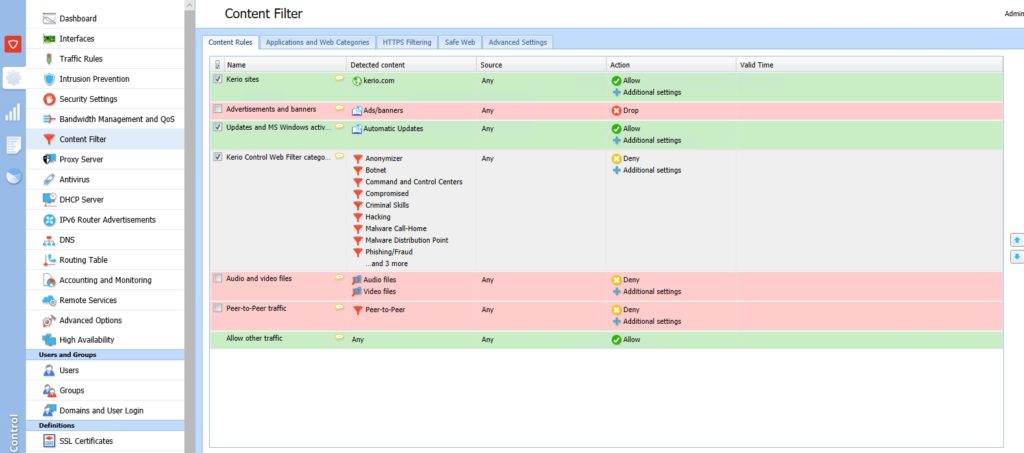
In addition to the content filtering capabilities shown in the figure above, Kerio Control can also enforce the use of safe search and block pages containing various words or phrases. The software also contains a whitelist option that can be used to override the filters for sites that are known to be safe.
Additional infrastructure and reporting features
Kerio Control includes many infrastructure components that can help to make life a bit easier for smaller organizations. For example, the software provides DNS caching, which can help users experience more responsive browsing. There is also built-in secure VPN functionality for remote workers and the Kerio Control server can even be configured to act as a DHCP server.
One of the things that impressed me about Kerio Control is that it can be configured to map groups and user accounts from the Active Directory. By doing so, it becomes possible to keep track of activity on a user-by-user basis. The software includes reporting capabilities that allow you to track which sites users are visiting, and how much network traffic users are generating, among other things. You can see an example of this in the screenshot below.
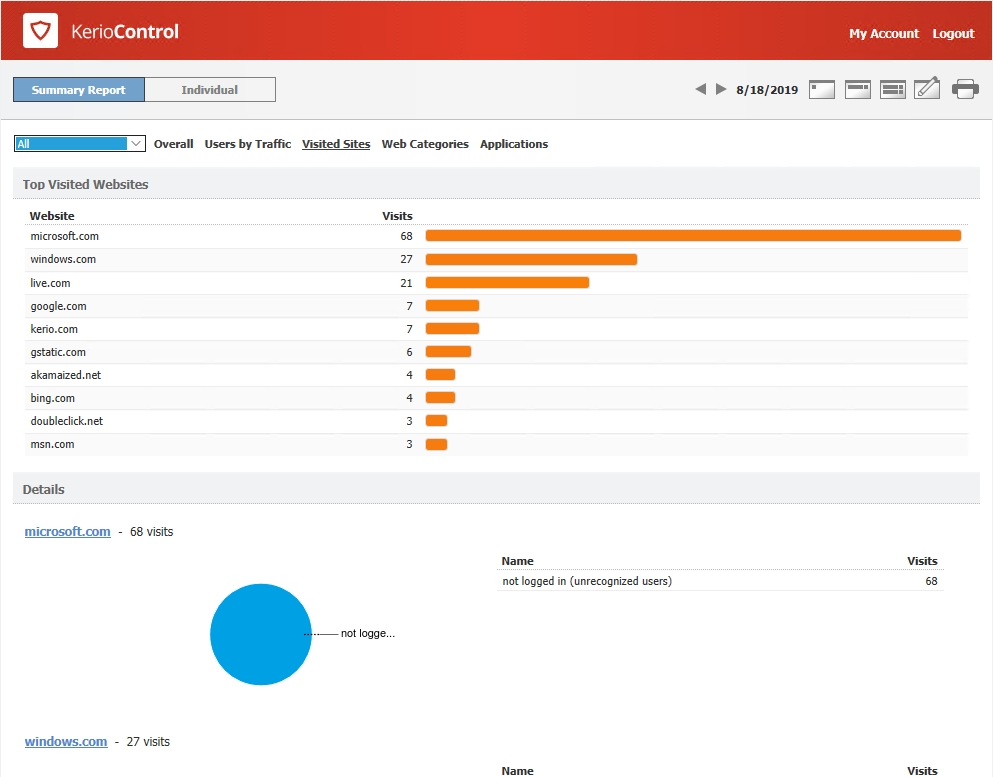
If Kerio Control is mapped to an Active Directory, the report shown in the screenshot above will show you which specific users accessed which sites. It is even possible to block web access to users who are not logged in to prevent users from acting anonymously.
Pricing
Pricing for a Kerio Control virtual appliance like the one that I based my evaluation on starts at $320 per year (covering the minimum of 10 licenses). Prices decrease per user at higher volumes. GFI offers several different Kerio Control hardware appliances with prices ranging from $575 to $1,599 per year, plus required software licenses. You can find the full pricing information, and a listing of the various available plans here.
The verdict
I always wrap up the reviews I write for TechGenix by assigning a numerical score to the product that I am evaluating. These scores range from zero to five stars, with five stars being the highest possible score. I decided to give Kerio Control a score of 4.9, which is a Gold Star review.
Throughout my evaluation, I consistently found Kerio Control to be completely intuitive. That’s quite an accomplishment for a network security tool. So many of the competing tools that I have used in the past seem needlessly overcomplicated.
The other thing that impressed me about Kerio Control is the sheer number of features it includes. As you may have gathered from the screen captures, its feature set goes far beyond what I can cover within a review.
Kerio Control is an excellent choice for any small or medium-sized business that needs a reasonably-priced network security suite that is not overly difficult to use.
Rating 4.9/5


