AWS customers can use AWS Directory Service, which is our well-known Active Directory running on Windows Server 2012 R2, as a managed service by AWS. Being a managed service comes with a twist, though: We don’t have access to manage the domain controllers. But just use administrative tools to create objects; it is AWS’ responsibility to monitor, eventual recovery, replication, snapshots, and software updates of the environment.
Although we don’t have the same flexibility of having a domain controller, this product can be used in a variety of scenarios where Active Directory is required to run applications on the cloud or for simple authentication.
We have some additional functionalities, such as the capability to upgrade the schema through LDIF files and create trust between Active Directory forests.
Configuring the network environment
Although we can start a VPC (Virtual Private Cloud) from within the AWS Directory Service creation wizard, it is not recommended, because the page that the administrator is redirected to has the option to create just a simple VPC.
There is a subtle difference when using the VPC Wizard and Create VPC. On the first option, an Internet gateway and the routing tables will be updated to allow internet access automatically; using the second option we must do our work manually.
Since AWS is the responsible for hosting, they require two subnets in different Availability Zones in order to provide high availability and resilience for the service. If you are planning to use AWS, this service can be the first one to be deployed because it will create the basic infrastructure for your future instances right from the get-go.
Let’s get started
Logged on the AWS Console, click on Services, and then on VPC. In the main page, click on Start VPC Wizard.
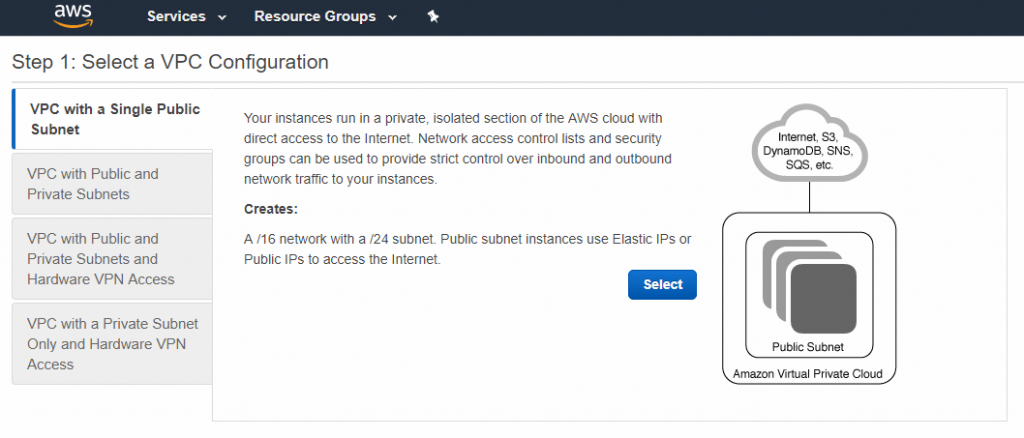
Step 1: Select a VPC Configuration page. In this article, we will use a simple network topology, which is VPC with a Single Public Subnet, where we can control the access to our servers through a Security Group or Network access control lists. Click on Select to continue.
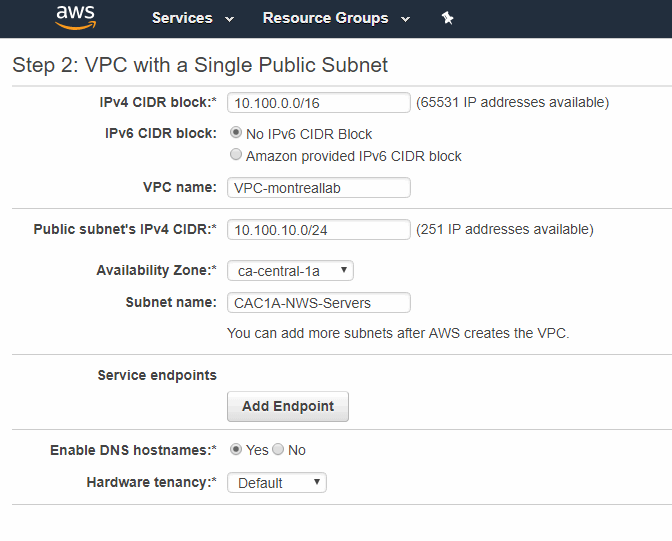
Step 2: VPC with a Single Public Subnet page. We are going to define the IPv4 block for the new VPC (10.100.0.0/16 in our article), and define the first subnet, including the IP range (10.100.10.0/24), its availability zone (Canada Central 1A), and its name. After that, click on Create VPC button.
We are using Canada Central as the region, and we will assign a simple naming convention to our new subnets, where we are going to use three fields: the first will inform the region and the availability zone (CAC1A, which means Canada Central 1A). The second piece of information is the type of the object (where NWS means Network Subnet). And the third, which is the purpose of the subnet, in our case Servers.
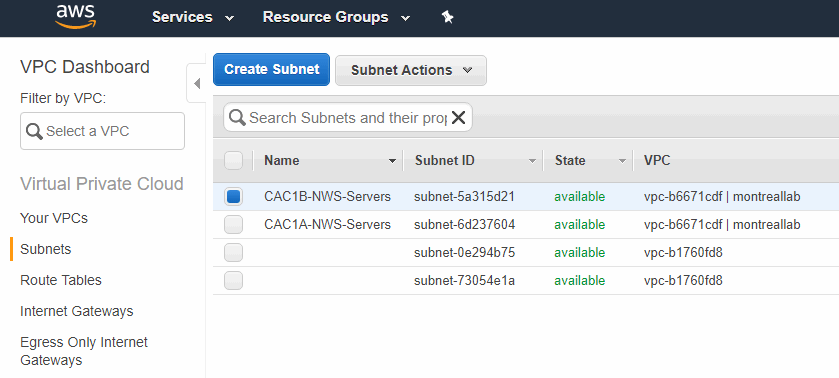
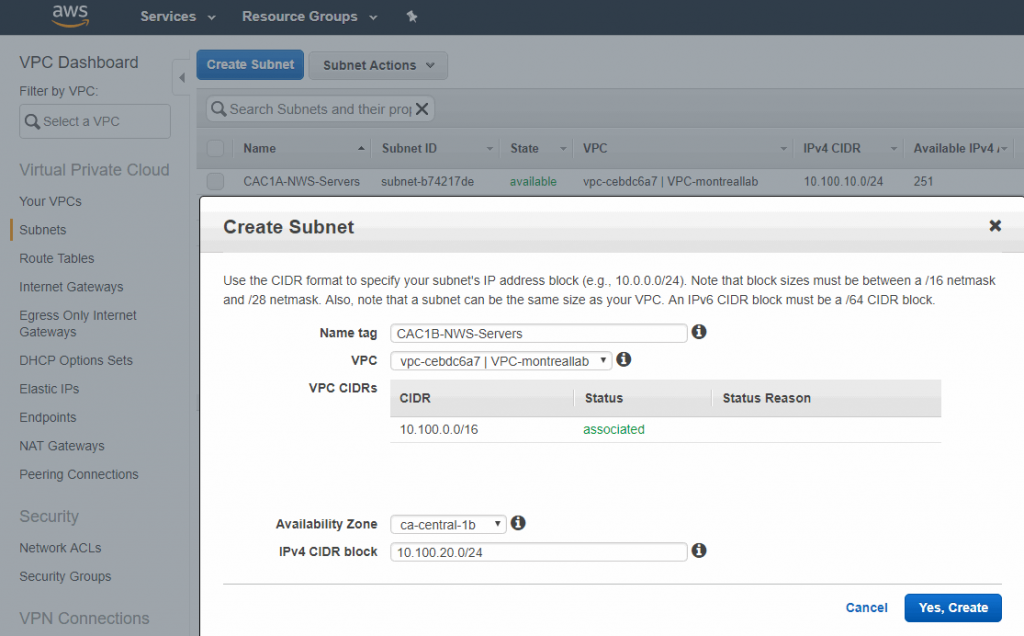
The next step is to create the second subnet. Click on Subnets item on the left, and then click on Create Subnet button, and let’s create a subnet (10.100.20.0/24) and name it as CAC1B-NWS-Servers.
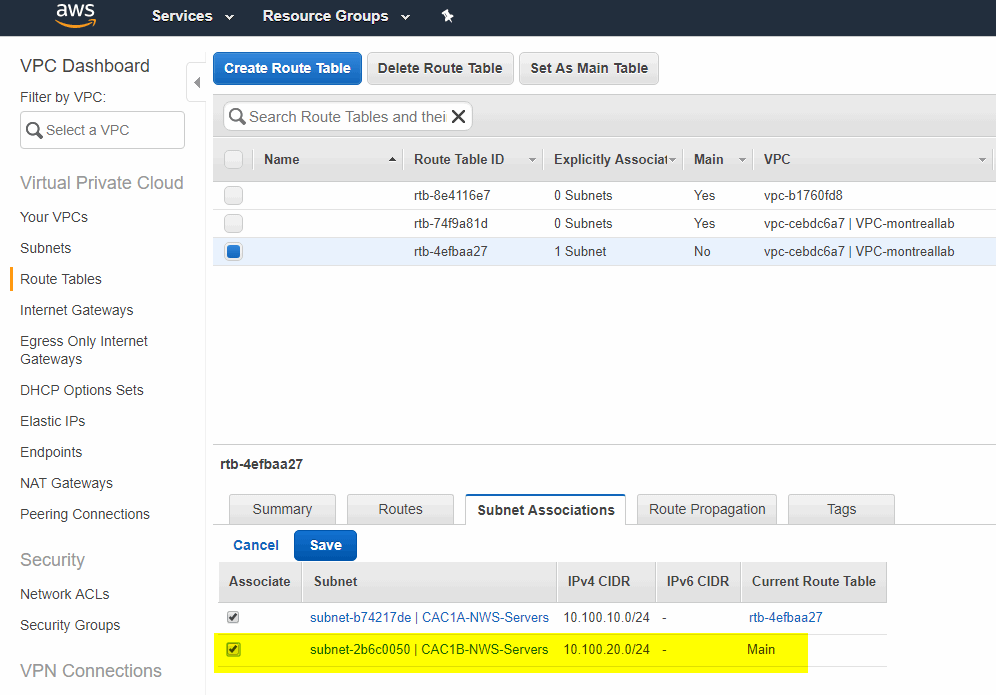
To keep consistency, click on Route Tables, select the route table ID that is associated to the VPC-montreallab (the one that we have just created), and that route table should have one explicit association already in place. Select Subnet Associations tab and add the missing subnet, which is the one that we have just created.
Creating an IAM role
To join the new instances in the AWS Directory Service, it is recommended to create a new role. Logged on the AWS Console, click on Services, and then IAM. In the Welcome to Identity and Access Management dashboard, click on Roles located on the left side, and click on Create Role.
In the first page (Trust), select EC2, and then EC2 Role for Simple System Manager, and click Next: Permissions.
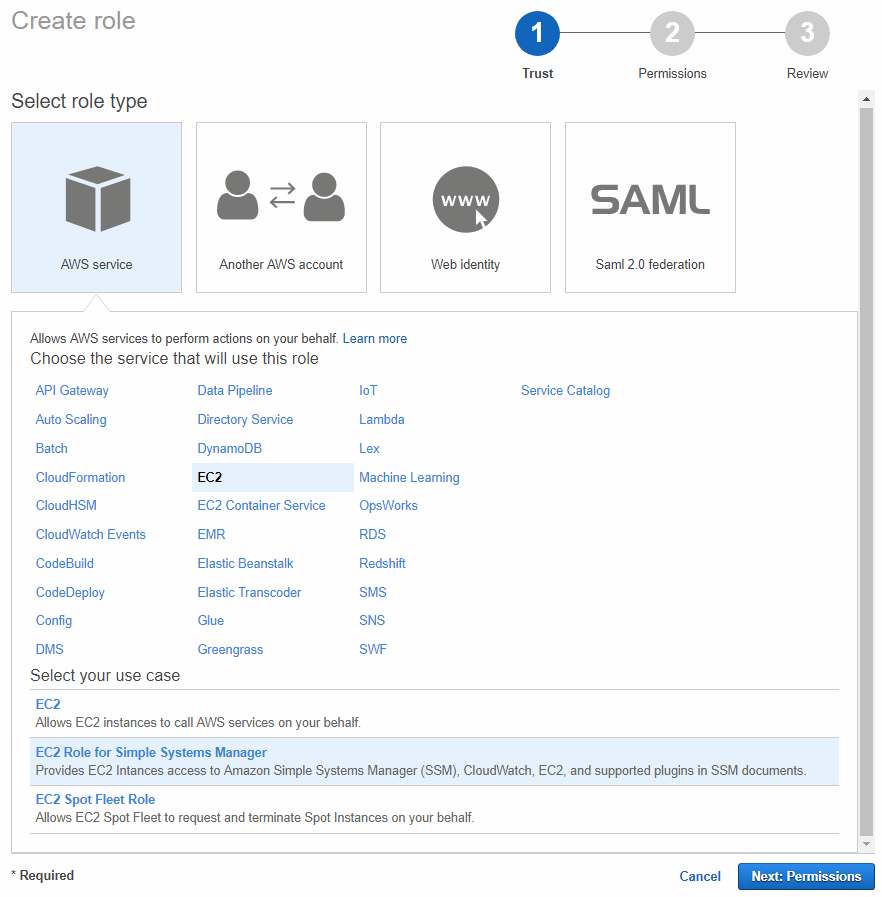
In the second page (Permissions), leave the default settings and click on Next: Review.
In the final page of the wizard (Review), label the new role and click on Create Role. We will be using this new role during the provisioning of new instances at the end of this article.
AWS Directory Service
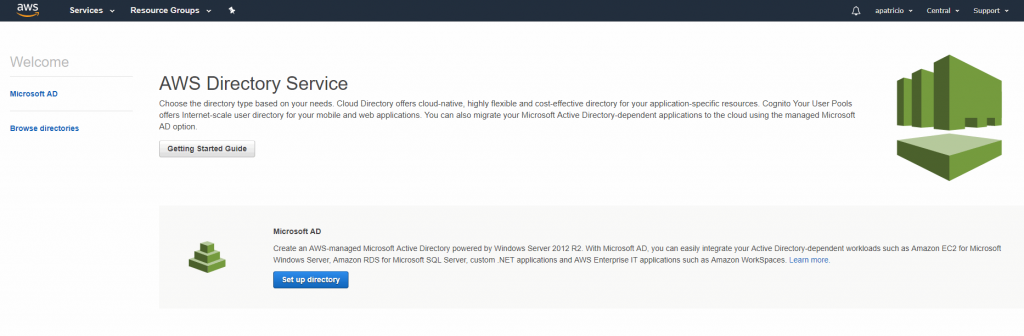
We will use a brand-new AWS subscription to test the AWS Directory Service. Logged on the AWS Console, click on Services, and then on Directory Service located underneath Security, Identity & Compliance section.
In the welcome page, click on Set up directory on the Microsoft AD item.
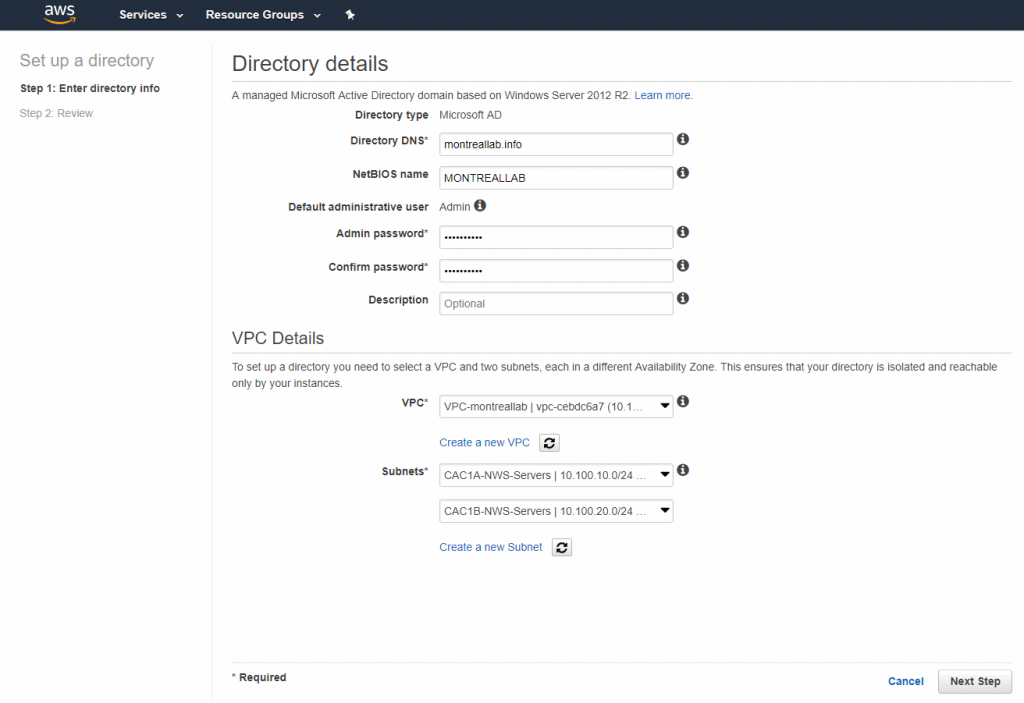
The AWS Directory Service creation is simple. It has two main sections: Directory Details and VPC Details. In the Directory details, we need to enter the FQDN of the domain (montreallab.info), the NetBIOS (MONTREALLAB), and provide the administrator password. All that information will be used to build our Active Directory domain as part of the provisioning process.
In the same page, we need to select the VPC and subnets that we created in the previous step. After that click Next Step. A summary page will be displayed. Click on theCreate Microsoft AD button to start the provisioning process. This process will take some time to complete.
After creation is complete and the Status column shows as Active, click on it. A summary of the AWS Directory Service will be displayed, including the domain controllers created for the service. In our example, one on each subnet (10.100.10.76 and 10.100.20.118).

Our next step is to configure DHCP to provide the proper DNS servers to be provided to our new instances. The DNS Server IPs we retrieved from the last step are the domain controller IPs that were provisioned as part of the AWS Directory Service.
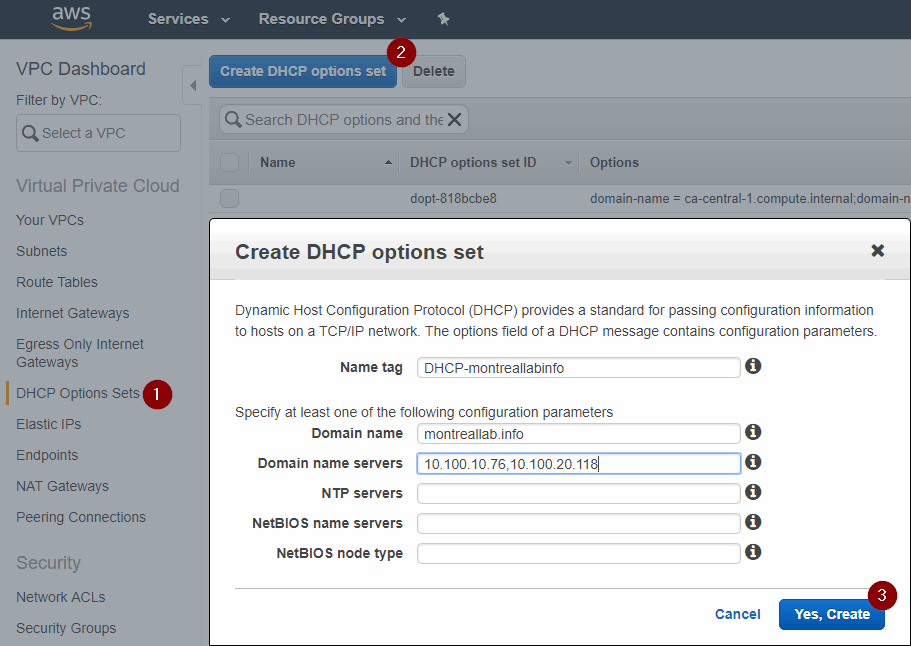
Logged on the AWS Console, click on Services, and then VPC. Click on DHCP Options Sets (1), and then Create DHCP options set (2). In the new page, type in a name, FQDN domain name (it must match the FQDN that we entered on the AWS Directory Service wizard), and the IPs for the DNS Servers. After that, click on Yes, Create (3).
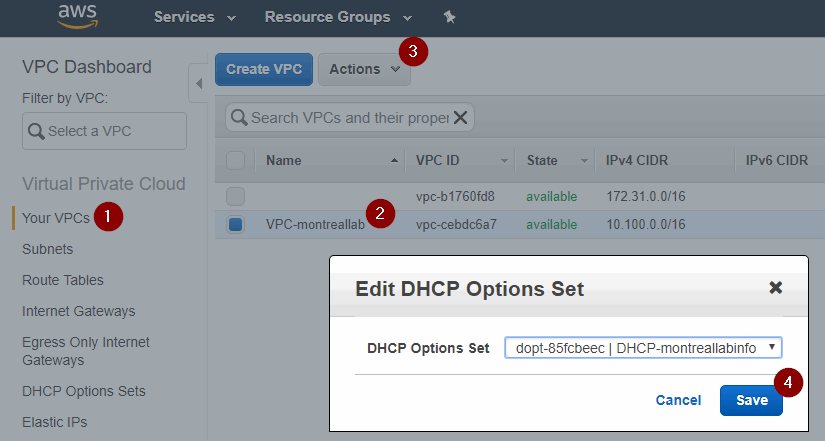
After creating the DHCP Option Set, click on Your VPCs (1), select the item from the list, and click on Actions (3) and select Edit DHCP Option Set. In the new dialog box, select the DHCP Option set that we have just created, and click on Save (4).
Creating new instances and joining them into the AWS Directory Service
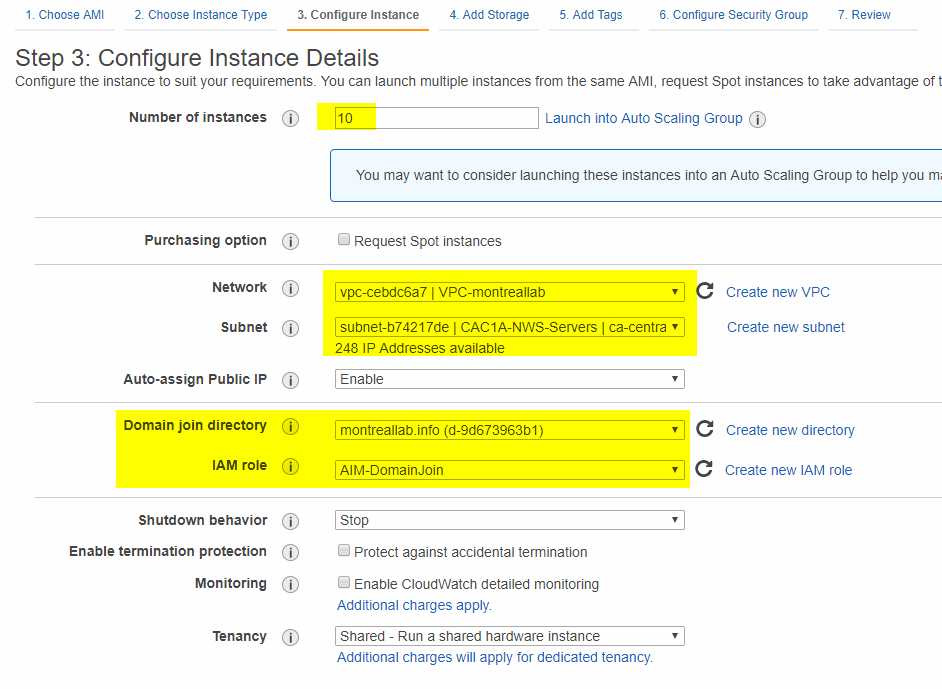
Now that we built the infrastructure and enabled the AWS Directory Service, it is time to put the solution to the test. Let’s spin 10 instances of Windows Server 2016 base image. During the provisioning, we will select the VPC and one of the two subnets that we have created previously.
Another important point is to select our AWS Directory Service (montreallab.info) and the IAM Role with enough permissions to join the machines into the domain. After that, just complete the wizard and wait for the provision of the new instances.
The beauty now is that the access is easier. Since we have the instances part of a domain, we don’t need to use the private key to retrieve the administrator password. We just need a credential from the domain. By default, we know the admin and the password that we defined during the AWS Directory Service creation.
Logged on the first instance, we can install the Active Directory management tools, and from that point, we can explore the Active Directory Users and Computers and we can see that the structure is well-defined.
All new instances will be created underneath Domain-NetBIOS\Computers Organization Unit (OU), and the users should be created underneath Users OU to keep the organization of the tenant.

Scaling up your domain controllers
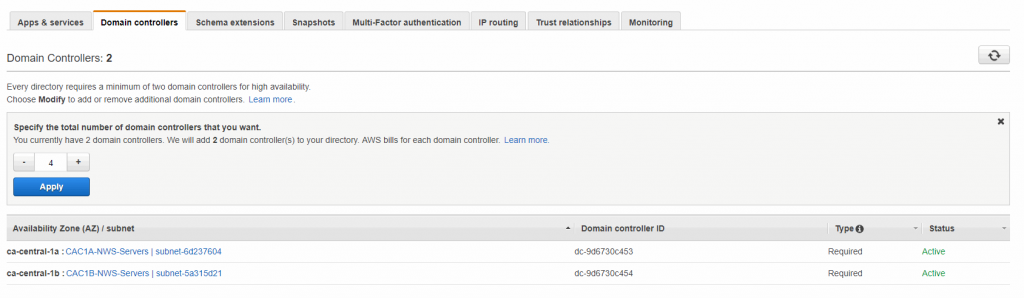
AWS enforces the use of at least two domain controllers, and they place each one in a different availability zone/subnet, but if you are from the old school like me, we would like to have two domain controllers per site, right? The process is simple. Just open the current Directory Service and click on the Domain Controllers and click on Modify.
In the new page, change to the number of domain controllers we will configure to four, and click on Apply. AWS will add the new domain controllers (one on each site).
That’s it. You should be up and running.




Hi Anderson – Wondering how you can send domain join info to cloud watch