If you would like to read the other parts in this article series please go to:
- Hardening an Exchange Server 2003 Environment (Part 1)
- Hardening an Exchange Server 2003 Environment (Part 3)
- Hardening an Exchange Server 2003 Environment (Part 4)
Windows 2003 SP1 Security Configuration Wizard
When hardening a messaging server, it makes sense to harden the underlying operating system first. Fortunately Windows Server 2003 Service Pack 1 introduced a neat tool, the Security Configuration Wizard (SCW). This tool is not installed automatically with SP1, instead you must go to Add/Remove Windows Components and select to install it.
Figure 1: Add/Remove Windows Components
SCW is an attack surface reduction tool that uses roles (e.g. “Exchange Server”, “Web Server”, “Domain Controller“, etc.) to determine the desired functionality of a particular type of server, then disables functionality that is not required for the role(s) specified. Specifically, SCW:
- Disables unneeded services
- Blocks unused ports
- Allows further (address or security) restrictions for ports that are left open
- Prohibits unnecessary web extensions (if running IIS)
- Reduces Protocol Exposure (SMB, LanMan, LDAP)
- Defines an Audit Policy
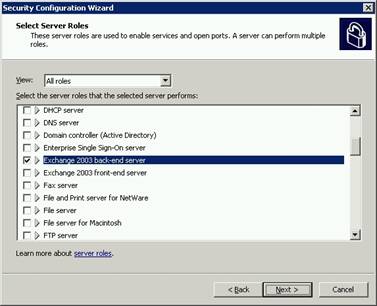
Figure 2: Exchange back-end server role
SCW creates customized security policies, which are stored as XML files, that configure services, network security, specific registry values, audit policy, and if applicable, Internet Information Services (IIS). You can take any given policy and apply it to other servers.
If you want to learn more about this tool, visit Security Configuration Wizard for Windows Server 2003.
There are some known issues when using this tool. One possible problem occurs when a policy created on the “default installation path” Exchange server is imported to a “non-default installation path” Exchange server, and vice versa. There are a couple of KB articles describing some other minor issues:
Exchange Security Guide Templates
In the previous tip I wrote about some minor issues with SCW. In one of the links I provided (KB 896742), Microsoft states that: “To harden Exchange 2003 computers, we recommended that you perform the procedures that are described in the Microsoft Exchange Server 2003 Security Hardening Guide. You should perform these procedures instead of running the Security Configuration Wizard on the Exchange 2003 computer”. In fact, the Exchange Server 2003 Security Hardening Guide is a great source of information. It has essential information about how to harden an Exchange Server 2003 environment. I must say I don’t fully agree with Microsoft’s position, or I wouldn’t have referred Security Configuration Wizard as a valid option to you. SCW works with Exchange servers, I know, I’ve tried it, and it’s simpler to use than the Exchange Security Guide templates, so it’s up to you whether you use it or not.
As a companion of this guide you get a collection of Group Policy Security Templates that you can apply at the organizational unit level. These templates include many security settings, such as auditing, security options, registry settings, file permissions, and service settings. There’s a total of 12 different GPO templates, each one representing a server role in an Exchange environment.
Table 1 lists all the included security templates and the correspondence to each server role.
|
Server Role |
Description |
Security Templates |
|
Exchange 2003 back-end server |
Server for mailbox and public folder access; when using POP, IMAP4, or NNTP, include the corresponding incremental template |
|
|
Exchange 2003 front-end server |
Common settings for all front-end servers; disables all protocols; must apply a specific protocol for the server to function. |
|
|
Exchange 2003 HTTP server |
Dedicated front-end server for HTTP; used by Outlook Web Access, Outlook Mobile Access, Exchange Server ActiveSync, and WebDAV applications |
|
|
Exchange 2003 POP3 server |
Dedicated front-end server for POP3, or added incrementally to an Exchange 2003 back-end server |
|
|
Exchange 2003 IMAP4 server |
Dedicated front-end server for IMAP4, or added incrementally to an Exchange 2003 back-end server |
|
|
Exchange 2003 NNTP server |
Added incrementally to an Exchange 2003 back-end server |
|
|
Exchange 2003 SMTP server |
Dedicated Internet-facing gateway server for SMTP or bridgehead |
|
Table 1: Exchange 2003 server roles and corresponding security templates
The Exchange Server 2003 Security Guide should be implemented together with the Windows Server 2003 Security Guide, since some of the templates are cumulative.
Figure 3 illustrates the recommended organizational unit structure to accommodate the server roles, including which security policy and security template corresponds to each organizational unit.
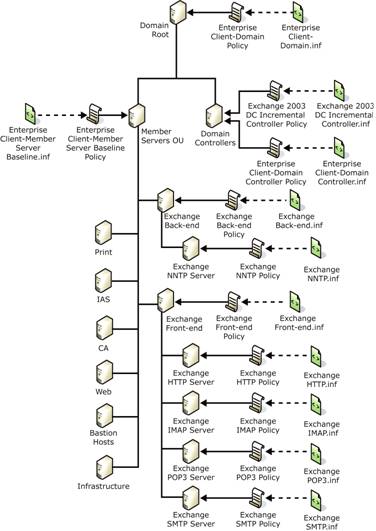
Figure 3: Organizational unit structure with additional Exchange 2003 organizational units
If you don’t have all the different roles implemented in different servers (and let’s face it, most Organizations don’t!), you can combine server roles into a single organizational unit, since the security policies included with the guide are additive.
As a final remark, I would like to remind you again of the importance of testing these policies in a controlled environment before applying them in production.
Install Exchange Server 2003 SP2
Exchange Server 2003 Service Pack 2 (SP2) is a cumulative update that enhances your Exchange Server 2003 messaging environment with some new security features, namely:
- Better protection against spam
- Updated and integrated Exchange Intelligent Message Filter.
- New support for Sender ID e-mail authentication protocol.
- Policy setting. Unlock a device with a password.
- Local wipe. Decide how many incorrect logon attempts are permitted before your data might be at risk.
- Remote wipe. Lost, stolen, or misplaced devices are never out of reach. You decide when it’s prudent to reset devices remotely over the Web.
I say it’s an obvious security measure, but my experience tells me that people often tend to resist installing the latest security pack, especially those Organizations with Exchange Servers with a previous service pack in production.
ISA Server
If you’re thinking about publishing Exchange services to the Internet, ISA Server is your best friend. ISA Server and Microsoft Exchange Server 2003 are designed to work closely together in your network environment to provide a secure messaging environment.
In an Exchange environment, ISA Server will control traffic entering your internal corporate network and outbound communication from your messaging environment. All inbound Internet traffic bound to your Exchange servers, such as Microsoft Office Outlook Web Access, RPC over HTTP communication from Microsoft Office Outlook 2003 clients, Outlook Mobile Access, POP3 and IMAP4 are processed by ISA Server.
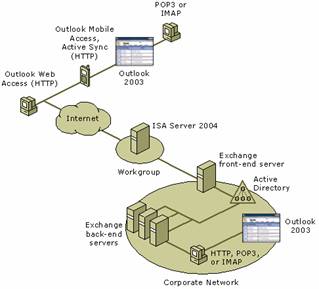
Figure 4: Exchange network topology with ISA Server
Besides all the security features that ISA Server adds to your network, the main advantage of using it is that Exchange front-end servers no longer need to be located in the perimeter network (it’s not even recommended by Microsoft), and your Exchange resources are protected from attack.
Denial of Service (DoS) Protection
A Denial-of-Service (DoS) attack is characterized by an explicit attempt by attackers to prevent legitimate users from using a specific service. Examples include attempts to flood a network, thereby preventing legitimate network traffic attempts to disrupt service to a specific system or person by means of system misuse.
Although DoS attacks are generally difficult to guard against, Exchange 2003 includes settings that can help you protect against such attacks. Most of these settings are available through the Exchange System Manager, more specifically in the SMTP Virtual Server Properties.
The SMTP settings you can tweak to further prevent your system against DoS are:
- Maximum number of recipients per message – Exchange Server returns a non-delivery report (NDR) to senders whose messages exceed the maximum number of recipients.
- Maximum message size – The largest size of a message that can be transmitted through the virtual server.
- Maximum number of messages per connection – Configures the system to drop the connection after it reaches the specified number of messages.
- Maximum session size – The largest size of the complete email transaction over a single session over SMTP.

Figure 5: SMTP Virtual Server message limit parameters
Note:
Because replication needs likely require the transfer of large messages, you should not configure internal (non-Internet facing) SMTP virtual servers to disallow messages larger than 10 MB.
I must say that I’ve never changed the SMTP Virtual Server Settings from their default values to anything different. This is probably because the large majority of big companies don’t use Exchange as their gateway server, with security as an excuse. I’m not going to waste my time arguing this choice, so if you have an Exchange Server facing the Internet and want to tweak those anti-DoS settings, now you know where they are.
Another important setting you should configure has to do with storage limits: set a limit for both mailboxes and public folders. This will prevent another common DoS attack that consists in sending a large number of e-mail messages to a particular server until it runs out of disk space.
Since Exchange 2003 relies on some IIS components, on a Windows Server 2003 installation, Application Pools can also help to mitigate DoS attacks.
Summary
And so we conclude part 2. In part 3 I’ll cover what Microsoft calls messaging hygiene. If you’re willing to take some homework, read this document: Messaging Hygiene at Microsoft: How Microsoft IT Defends Against Spam, Viruses, and E-Mail Attacks.
If you would like to read the other parts in this article series please go to:
