If you would like to read the other parts in this article series please go to:
- Introduction to Configuration Manager 2012 (Part 1)
- Introduction to Configuration Manager 2012 (Part 2)
- Introduction to Configuration Manager 2012 (Part 3)
- Introduction to Configuration Manager 2012 (Part 5)
- Introduction to Configuration Manager 2012 (Part 6)
- Introduction to Configuration Manager 2012 (Part 7)
- Introduction to Configuration Manager 2012 (Part 8)
Introduction
With the release of System Center 2012, Microsoft also released a new version of Configuration Manager 2012.
Part 1: We went through a complete installation of System Center 2012 Configuration Manager and, by the end of the article, had a fully operational system.
Part 2: We began investigating the new features and the console.
Part 3: We explored the discovery process.
In this, part 4, and the next two parts, parts 5 and 6, we’ll dive into client settings.
Client Settings
Client settings are a crucial aspect of System Center Configuration Manager 2012. In older versions of SCCM, these were called client agents, but they still serve the same purpose in SCCM 2012. These settings control how the managed clients in SCCM 2012 will operate. In this article series, we’ll go through each and every client setting and explain in detail the parameters that you can adjust.
Background Intelligent Transfer
Background Intelligent Transfer Service (BITS) is a Windows service that

Figure 1: Background Intelligence Transfer Service settings
- Limit the maximum network bandwidth for BITS background transfers. Limits the amount of bandwidth that BITS will use for background transfers. This can be useful in slow link scenarios or when bandwidth is at a premium.
- Throttling window start time. Provide the time of day at which throttling should start.
- Throttling window end time. Provide the time of day at which throttling should cease.
- Maximum transfer rate during throttling window (Kbps). Determine the maximum transfer rate that is allowed during the throttling window. For example, 1 Mb would be 1,000 Kb.
- Allow BITS downloads outside the throttling window. Decide whether or not BITS transfers are allowed outside the defined throttling window.
- Maximum transfer rate outside the throttling window (Kbps). Determine how fast transfers can take place outside the throttling window.
Client Policy
Think of the client policy as a meta policy. This is the policy that determines how clients will handle receiving and updating their individual policies. The configuration for this client setting is pretty important as other SCCM functions often require machines to retrieve an updated client policy before they can work their own magic.

Figure 2: Client Policy settings
- Client policy polling interval (minutes). This value indicates to SCCM the interval by which clients should check in with the SCCM server to retrieve any policy updates that may have been made since the last check in.
- Enable user policy polling on clients. When SCCM is appropriately configured, enabling this parameter users logged in to managed clients are able to have programs targeted at them. Note that disabling this parameter will mean that applications targeted at users will not be deployed, even if they are required, and users may not see applications in the Application Catalog.
- Enable user policy requests from Internet clients. For sites that support Internet clients, when this parameter is set to True, endpoints on the Internet will receive both machine and user policy updates.
Compliance Settings
Compliance Settings are an updated form of Desired Configuration Management, which was included in older versions of SCCM. With Compliance Settings, administrators can determine when a managed client has deviated from established baselines.
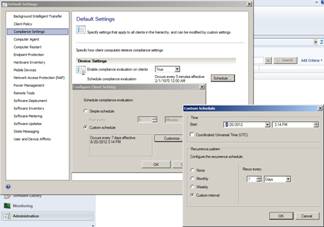
Figure 3: Compliance settings
- Enable compliance evaluation on clients. Decide whether or not clients will use their compliance evaluation capabilities.
- Schedule compliance evaluation. Determine the schedule by which compliance evaluation should take place.
Computer Agent
The computer agent is another set of settings that are pretty core to how SCCM manages clients. The items here define some general settings that dictate how a wide swath of SCCM functionality will operate.

Figure 4: Computer Agent settings
- Deployment deadline greater than 24 hours, remind user every (hours). When a software deployment action is pending and is more than 24 hours out, choose the interval by which users will be reminded about the deployment.
- Deployment deadline less than 24 hours, remind user every (hours). For deployments that have a deadline that takes place within the next 24 hours, notify users about the deployment every X number of hours.
- Deployment deadline less than 1 hour, remind user every (minutes). Likewise, for deadlines in the next hour, choose the interval (in minutes) by which users should be notified of the deployment.
- Default Application Catalog website point. Define the address at which the client can find the Application Catalog. By default SCCM clients are configured to automatically detect the Application Catalog. Administrators can choose instead to force clients to use an automatically created intranet fully qualified domain name or the NetBIOS name for the server holding the Application Catalog. Administrators may choose instead to specify a custom URL.
- Add default Application Catalog website to Internet Explorer trusted sites zone. By setting this option to True, an administrator can direct clients to ensure that IE protected mode doesn’t interfere with a client attempting to browse to the Application Catalog.
- Organization name displayed in Software Center. The Software Center is a part of a client installation and is one of the locations at which users can choose to install software that has ben deployed. This client setting is often populated with the name of the company.
- Install permissions. Specifies the users that are allowed to start the installation of deployed software.
- All Users. Any user logged in to a managed client can initiate a deployed software installation.
- Only Administrators. Only users that are members of the local administrators group can initiate a software installation.
- Only Administrators and primary users. This is the same as the previous option with one exception. If the device has been associated with a user through user/device affinity, the primary computer user can also initiate a software installation.
- No Users. Users can never initiate software installations. Only software marked as required will be installed.
Computer Restart
If SCCM initiates an action that requires a computer restart, the settings here help to define what will happen when that restart takes place. After all, you don’t want users to just have their PC all of a sudden restart with no warning whatsoever. That would result in lost work and a frustrated user base!

Figure 5: Computer Restart settings
- Display a temporary notification to the user that indicates the interval before the user is logged off or the computer restarts (minutes). The user is able to close this window and continue working, but the countdown to restart continues for the interval shown.
- Display a dialog box that the user cannot close, which displays the countdown interval before the user is logged off or the computer restarts (minutes). This is where SCCM means business. The user cannot close the display window and the countdown continues.
Summary
As you can probably see, there are a number of options associated with each client setting. Administrators can adjust these options to control client behavior in the environment. In the next part of this series, we’ll continue our look at client settings.
If you would like to read the other parts in this article series please go to:
- Introduction to Configuration Manager 2012 (Part 1)
- Introduction to Configuration Manager 2012 (Part 2)
- Introduction to Configuration Manager 2012 (Part 3)
- Introduction to Configuration Manager 2012 (Part 5)
- Introduction to Configuration Manager 2012 (Part 6)
- Introduction to Configuration Manager 2012 (Part 7)
- Introduction to Configuration Manager 2012 (Part 8)