Imagine that tomorrow morning, you get up out of bed and check your E-mail. There is a message from your bank indicating that you are overdrawn on your checking account because a check that you wrote for $2457.83 bounced. You don’t remember writing a check for this amount. What do you do?
Hopefully, you answered that you would call the bank rather than logging onto the bank’s Web site to check out the problem for yourself. The situation that I just described is known as a Phishing (pronounced fishing) scam. Here’s how it works.
The person who is initiating the scam sends an E-mail to millions of people. The E-mail message is designed to appear to come from a bank, Internet Service Provider, online auction company, or from anyone else that you could potentially have regular business dealings with. The From header on the message is spoofed, and the message is designed to look as official as possible. The message’s sole purpose is to gather information.
Let’s go back to my earlier example in which a message allegedly came from your bank indicating that your account is overdrawn because of a check that you didn’t write. The vast majority of the people who receive the message don’t even use the bank that the message claims to be from. In this case though, the message just happens to appear to be from the bank that you use. Because the message appears to be related to a serious matter involving your bank, the person initiating the scam now has your attention.
Typically, such a message will urge you to take action and will provide a link to the bank’s Web site and / or the banks’ phone number. Although the phone number may or may not actually be the bank’s phone number, the Web site URL is never legitimate even if it appears to be legitimate.
Sometimes a person involved in a Phishing scheme will put the bank’s actual phone number in the E-mail in hopes of making the message seem more authentic. Other times though, they will put another number and have someone just waiting for calls from panicked bank customers. This person will typically ask the person who is calling for an account number, a PIN number, and any other information that might be useful, such as a social security number or birth date. The phony bank employee will then pretend to solve the problem while you are on the phone. In actuality though, the problem is just beginning. You weren’t actually overdrawn on your checking account, and now you have given your account information directly to a thief who can use it to clean out your bank account or to launch other identity theft scams.
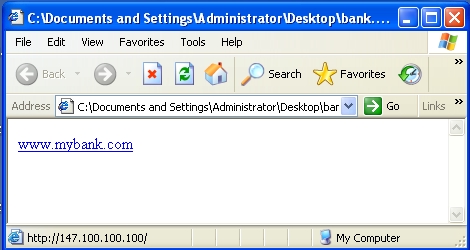
So what about that official looking URL on the E-mail message? Sure, it probably looks like the bank’s official Web site, but try hovering your mouse over the URL. When you hover your mouse over the URL, you will see the hyper link appear. If the URL is legitimate, the hyperlink should match the URL displayed in the message EXACTLY. Typically, the person who created the message will replace the URL with an IP address, or they will use a domain name that is spelled very similarly to the bank’s domain name. To show you what I am talking about, have a look at Figure A. Figure A contains a very simple Web page that I have created. This page appears to have a link to mybank.com, but if you look at the bottom of Internet Explorer, you will see that the link is actually being directed to http://147.100.100.100. If such a link had been E-mailed to me, the hyperlink would appear in a small pop up rather than at the bottom of the window.
Figure A: This Web page appears to be directed to mybank.com, but is actually pointed at some other Web site instead.
Obviously, the idea behind a Phishing scam is to panic you into clicking on the link contained in the E-mail message and then getting you to enter your bank account number and password. Therefore, you might be wondering how someone could enter their account information into a Web site that does not belong to their bank?
Truthfully, it is very easy to scam someone into entering information into a false Web site. To see how easy it is, try this little experiment. Go to your bank’s Web site and then select the Source command from Internet Explorer’s View menu. This will show you the source code to your bank’s Web site, as shown in Figure B.
Figure B: This is the source code for Bank of America’s Web site.
Actually, you aren’t really looking at the source code. Remember that HTML stands for Hyper Text Mark Up Language. The information that you are seeing is simply the HTML instructions used to display the bank’s home page. Financial institutions typically use a server side scripting language such as ASP to control what visitors to the site actually see.
None of that really matters though because the hacker doesn’t need to recreate the bank’s entire Web site. They only need to recreate the first screen, and the bank has provided them with the HTML code to do it!
The person performing the Phishing scam would simply make a few minor modifications to the code and then upload it to their own Web site. Typically, the modifications would involve the login prompts. Remember that the victim of the scam can’t really log into the fake bank Web site, because the person who created the site has no way of validating the bank customer’s credentials. Instead, the person conducting the scam simply re-engineers the bank’s HTML code so that when the customer enters their account number and password, the account number and password is added to a database. What typically happens next is that the victim is then redirected to the bank’s real home page. Of course they are not logged in when they get there. The victim assumes that they typed the password incorrectly and enters it again. This time they are logged in because they are on the bank’s real Web site. The victim has no idea that they have just given their account number and password to a scam artist.
How Not To Be A Victim
So far, I have given you detailed instructions for how to pull off a Phishing scam. I am not however giving you this information so that you can go rip people off. Instead, I am showing you how a Phishing scam works so that you can avoid being ripped off. Of course, understanding how the scam works is only half of the battle. You still need to know how to spot the scam and avoid being victimized by it.
The best advice that I can give you is that if you ever get an E-mail message from your bank, your ISP, PayPal, EBay, Amazon, etc., read the note over several times. Odds are that the note will appear legitimate, but you need to look for something fishy (no pun intended). For example, does the note have misspellings or bad grammar? Is this the first message that you have ever gotten from the company? Does the company even have your E-mail address on file? If you have any suspicions at all about the message, then the message is probably illegitimate.
The best thing that you can do is to call the company that allegedly sent you the message. Never use the phone number included in the message though. Instead, take the time to look the phone number up in the phone book. It’s better to spend a few extra minutes looking up a number that you already have in front of you than to be a victim of a scam.
Obviously, you should never click on a link within a suspicious message. If you really must visit the Web site that the message claims to be from, enter the site’s address into your browser manually.
Other precautionary steps that you can take are to review your bank statements and credit card statements regularly to make sure that no one is stealing from you or making purchases in your name.
Finally, if you do receive an E-mail message that proves to be a Phishing scam, you should report the message to the company that the message claims to be from. Doing so makes the company aware of the scam so that they can report it to the proper authorities and help keep other people from being ripped off.
Conclusion
As you can imagine, countless people fall victims to Phishing scams each year. These scams end up costing the victims millions of dollars. In this article, I have explained how to spot and avoid being victimized by this type of scam.