Introduction
Forefront Threat Management Gateway (TMG) 2010 is a highly effective secure web gateway solution that includes advanced web protection capabilities designed to enhance your organization’s overall endpoint protection strategy. It features gateway-integrated URL filtering to prevent access to web sites based on their categorization. TMG also includes virus and malicious software scanning which protects against file-based attacks, and enhanced network intrusion detection and prevention to protect against protocol-based attacks and prevent certain application and operating system vulnerabilities from being exploited remotely. In addition, TMG includes HTTPS inspection which makes all of these security features more effective. TMG is a Common Criteria certified enterprise-class firewall that provides unrivaled protection from sophisticated attacks that are common on the Internet today.
Monitoring TMG Advanced Web Protection
Monitoring the performance and effectiveness of TMG’s advanced web protection is essential. TMG provides three ways in which this can be measured. They are:
- Logging – Forefront TMG 2010 is, at its core, a firewall that logs all traffic to and through the system. Without exception, each packet is logged in detail. Using the built-in log viewer the security administrator can, in real-time, observe the effectiveness of the various web protection mechanisms provided by TMG.
- Reporting – For analysis of historical data, the native reporting tools included with Forefront TMG 2010 allow security administrators to create custom reports which can be used to conduct long term trending and identify patterns of potential threats.
- Performance Monitor – Forefront TMG 2010 is highly instrumented, allowing the security administrator to leverage the Windows Performance Monitor to obtain highly detailed, granular information about the efficiency and performance of TMG’s advanced web protection features.
Access Logs
The first tool that a security administrator is likely to use to assess the effectiveness of Forefront TMG’s web protection capabilities is the firewall and web proxy access logs. To view these logs, open the TMG management console, highlight the Logs & Reports node in the navigation tree, then click the Logging link located at the top of the center pane. You can view live log data immediately by clicking the Start Query link in the Tasks pane.
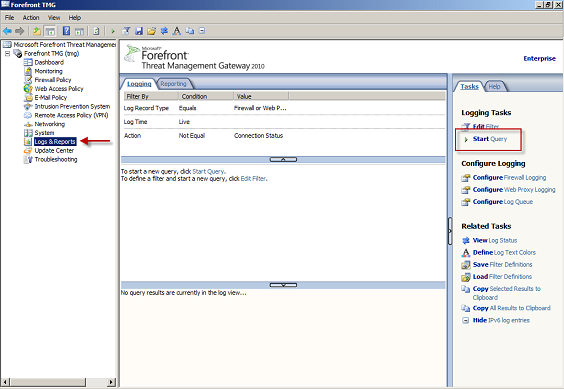
Figure 1
This will show all traffic flowing through the firewall, which you are not likely to find useful. To drill down to find more meaningful data, click Edit Filter in the Tasks pane. For example, if you’d like to know if any users are visiting gambling web sites, select URL Category from the Filter by drop down list, then select Equals from the Condition drop down list, and finally choose Gambling from the Value drop down list. Click the Add to List button, and then click Start Query.
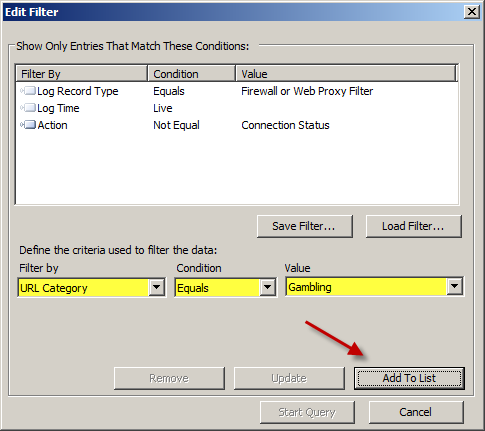
Figure 2
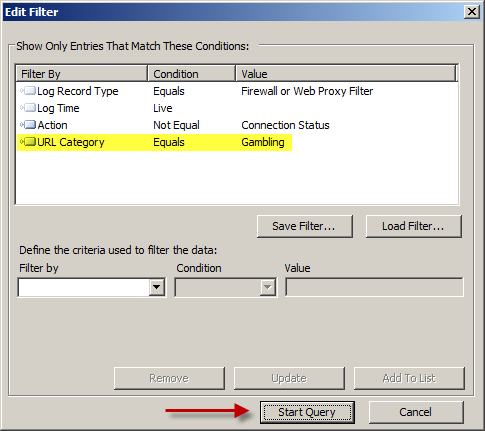
Figure 3
If a user attempts to access a gambling site it will be displayed in the main window.
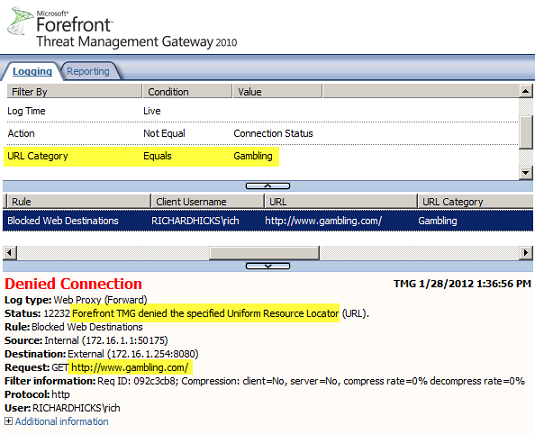
Figure 4
By scrolling the window horizontally you can view additional detail about the denied request. Of particular interest when viewing denied web requests are the Log Time, Client IP, Action, Rule, HTTPS Status Code, Client Username, URL, and URL Category fields.
Tip:
You can right-click anywhere on the column headings to add or remove columns. Here you can choose specifically which data you want to see in the log viewing pane.
The log viewer can also be used to determine how well the virus and malicious software scanning engine is working. Click Edit Filter in the Tasks pane and select Malware Inspection Action from the Filter by drop down list, then select One Of from the Condition drop down list, and then select Blocked and Cleaned from the Value list. Click the Add to List button, and then click Start Query. If a user attempts to download malicious software it will be displayed in the main window.

Figure 5
To use the log viewer to observe intrusion detection and prevention details, click Edit Filter in the Tasks pane and select NIS Scan Result from the Filter by drop down list, then select One of from the Condition drop down list, and then select Blocked and Detected from the Value list. Click the Add to List button, and then click Start Query. If a user visits a web site that attempts to exploit a vulnerability for which the Network Inspection System (NIS) identifies with a signature it will be displayed in the main window.
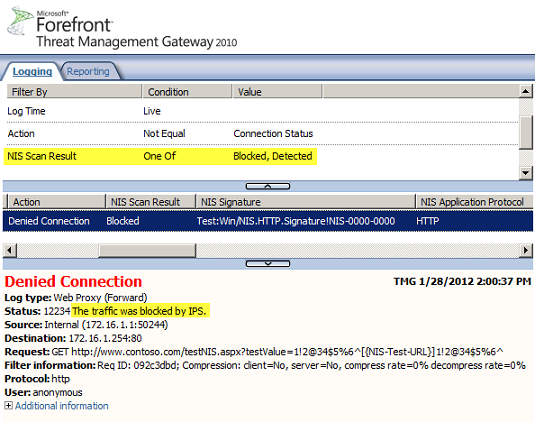
Figure 6
Reporting Tools
Viewing access logs is great for point-in-time information regarding firewall performance, but often security administrators need detailed reports to share with management to demonstrate that protection mechanisms are functioning as designed. To generate a report, click the Reporting tab and then click Create One-Time Report. When the report wizard opens, give the report a descriptive name and then select a suitable report period and date range. The Malware Protection, URL Filtering, and Network Inspection System report categories will provide the most detailed information.
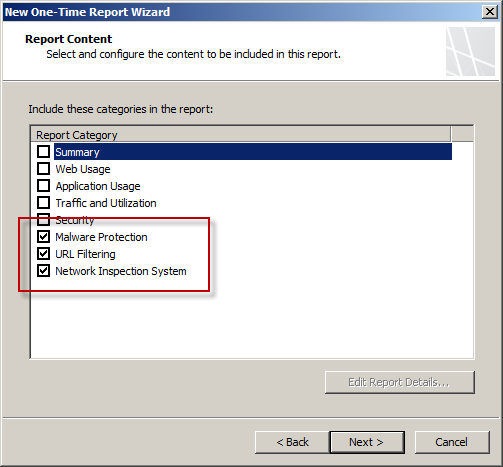
Figure 7
Choose the option to Send e-mail notification for completed reports if required, and optionally select a directory to which the reports should be published. Once complete, apply the configuration. Next, right-click the report and choose Generate and View Report.
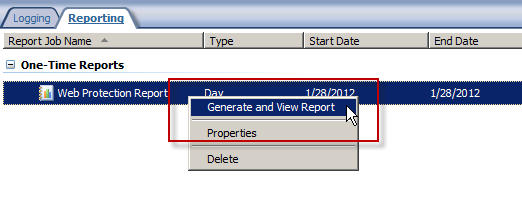
Figure 8
The report is in HTML format and will include statistics on blocked users, restricted web sites, threats, inspection times, and much more. Additional information about details contained in TMG reports can be found here.

Figure 9
Windows Performance Monitor
Forefront TMG 2010 is highly instrumented, and using the Windows Performance Monitor allows the security administrator to peer deep in to the inner workings of TMG to gather detailed information about the performance of TMG’s web protection components. There are 52 counters for the malware inspection feature alone! The relevant Performance Monitor objects and counters can be found here:
Summary
Forefront Threat Management Gateway (TMG) 2010 includes advanced web protection capabilities that provide essential security for today’s corporate networks. To evaluate and assess web protection performance there is a plethora of information available to the Forefront TMG administrator. Viewing the access logs provides a real-time view of the actions taken by the firewall. TMG’s native reporting tools allow the administrator to configure detailed reports that can be provided to management to demonstrate that TMG’s web protection is functioning as designed. In addition, the Windows Performance Monitor provides in depth information on the various web protection components. With all of these tools available, the security administrator will never be without information about the effectiveness of TMG’s advanced web protection features.



