If you missed the first part in this article series please read ISA Server 2006 as a Kitchen Utensil: Part 1 – External Attacks.
This is the final part of a two part article on how hackers see our firewalls. In this part we’ll see how ISA Server reacts to attacks coming from the internal network, like ARP poisoning, spoofing and man in the middle attacks.
Ok, now I know my external surface. Can I take a break?
Unfortunately, no. 80% of attacks come from the internal network. Usually you will have, at most, a dozen servers published on the Internet, but you can have hundreds of servers in your internal network.
The figure below provides a high level view of the example network used in this article.
Diagram 1: Example Network
Internal networks are a nightmare for security administrators. Internal networks are usually segmented into DMZs but it is common to find users and servers in the same network.
For servers that do not live in DMZs, you can use IPSec or local firewalls, but…. What happens with the DMZs if the hacker is inside?
There are two possibilities in this nightmare; ARP Poisoning with all its variants, and the sniffers.
In internal networks ISA Server administrators can use two elements in order to distinguish the authorized users:
- The source IP: the IP of a computer is easily replaced. And with ARP techniques it is possible to hijack a network through IP and a MAC. Internet hackers can only see the ports that the firewalls publish to all IPs or their public subnet, but in internal networks, hackers can find all ports that the firewalls publish to internal networks although the hacker does not have the appropriate IP to access them.
- The user logged in the source computer; using ARP Poisoning and a sniffer, it is easy to sniff passwords. In internal networks the security is less than on the Internet, hundreds of different services are running, in many cases, with old unpatched versions. Basic and clear authentication and services like low encrypted terminal services, proxies or webs make it possible for a hacker to sniff passwords.
For the following tests our ISA will have a rule allowing the traffic from the whole internal network except an IP (internal hacker) to a server in the DMZ (192.168.10.2).
Figure 1: ISA Server Rule for internal testing

Figure 2: Rule details (1)

Figure 3: Rule details (2)
At this point, if you scan the Web server in DMZ, the results are that all the ports are open or filtered.

Figure 4: Scan results
The only thing that separates us from our objective is our source IP and a password.
What if we use Nmap to send the packets spoofing an IP? What if the IP is from another ISA´s network?
Figure 5: Using NMap to spoof an IP of other segment with the command; “nmap –p 80-90 –e eth0 –S 10.10.10.2 –P0 192.168.10.2”
Figure 6: ISA detects the spoofed packet and denies the traffic

Figure 7: ISA detects the spoofing attack and creates an event
OK, but what if the packet comes from the correct network?
We can use Nmap to spoof MACs and IPs, but the best tool for this job is IRS from the Cain & Abel developers.
With IRS we can scan a specific target and port, spoofing IPs on the entire subnet. Additionally we can spoof the source MAC.
Figure 8: Using IRS (1)

Figure 9: Using IRS (2), setting the interface

Figure 10: Using IRS(3), setting the target
Figure 11: Using IRS (4), Results
Now you know which addresses can access the resource.
ARP and sniffers provide us with other interesting options.
We could sniff the network searching for passwords. In the real world, security is a relative thing, either everything is secure or nothing is secure. If you have insecure systems and you can’t secure them, isolate them from the rest of your systems. Create another domain for insecure systems and use separate user accounts for the users that need access to them. If your users use the same password to access secure systems and insecure systems, a hacker can use a sniffer and ARP attacks like man-in-the-middle (mitm) to discover user passwords. Software, like Ettercap, can do both, sniff the network using protocol decodes, search for passwords, and also makes it possible for a hacker to do some types of “man-in-the-middle” attacks.
Figure 12: Using Ettercap (1) Sniffing the network
Figure 13: Using Ettercap (2) Protocol and plugins loaded, starting sniffing
Figure 14: Using Ettercap (3) Passwords detected
Figure 15: Using Ettercap (4), Mitm attacks
With these two steps, hackers within internal networks have all the information they need to attack your DMZ services, but… what if a hacker is a really bad man and we have not taken precautions; hackers can avoid the firewall communication with other networks including internet? In our example network the firewall reaches Internet through a router with IP 10.10.10.2. What if a hacker deceives the firewall, communicating a false router´s MAC? Answer: the firewall can´t communicate with the internet; this attack is a D.O.S (Denial Of Service).
Figure 16: Using Nemesis to inject an ARP packet to firewall
Ok, you have seen the bad and the worst, let me show you the good
The first thing you need to know is that the ARP and MITM attacks are very difficult to do on the Internet. The hackers have tools, but the admins do too. To avoid DOS or MITM ARP attacks you must add static ARP entries in your firewall and network devices. You can use the ARP command to add a static ARP entry in your firewall.

Figure 17: Creating a static ARP entry
Network devices can be the best allies to fight spoofing and sniffing. You can make VLANS avoid ARP broadcast, and many network devices have features to make your network more secure. Other tools for administrators are IDS (Intrusion Detection System). IDS use sniffers to analyze network traffic and find malicious patterns. To find these patterns they use rules. Snort is one of the most famous free IDS programs and IDSCenter is a front end for snort. You can configure snort to detect ARP attacks to specified IPs, like firewalls, routers, proxys, etc. Snort also detects port scans, and hundreds of other security related events.
Figure 18: Configure Snort to detect ARP attacks
Also, you can configure Snort to run a script to block the traffic from the hacker IP or send an email when an alert is logged.
Figure 19: Configure snort alert notification

Figure 20: Snort event: ARP Spoof detected

Figure 21: Snort event: Port scan detected
If you install MOM agent in the snort server, you can read the snort alert in the event logs and trigger an alert in the MOM console.
Flood Mitigation
Some of the new features in ISA 2006 are the flood mitigation options. These options allow us to avoid D.O.S attacks, worms, and other risks.

Figure 22: Flood mitigation (1)

Figure 23: Flood mitigation (2)

Figure 24: Flood mitigation (3)
For each potential attack you can define a limit and custom limit. The custom limit only applies to the IP exception list. In this example, we will include the IP of one internal computer in the list of IP exceptions and also define a custom limit of 3 to the concurrent TCP/IP connections.

Figure 25: Flood mitigation (4)

Figure 26: Flood mitigation (5)
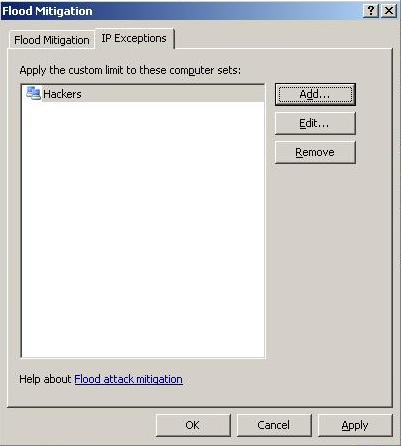
Figure 27: Flood mitigation (6)
With these settings the computer with the IP 192.168.0.30 has limited its concurrent connections to 3.
We will use telnet from 192.168.0.30 to create connections and performance monitor in ISA Server to view the concurrent TCP Connection counter.
Figure 28: Flood mitigation (7)
When the computer tries to make fourth concurrent connection, ISA denies the traffic and logs an event.
Conclusion
ISA Server is a great product, has high level security certifications and is “secure by default”. Windows provides us with many security features to help us fight hackers, but the final responsibility of having a secure network is in your hands, your work, and of course your skills.
If you missed the first part in this article series please read ISA Server 2006 as a Kitchen Utensil: Part 1 – External Attacks.

















