If you would like to read the other parts in this article series please go to:
- Managing Outlook 2007 through Group Policies (Part 1)
- Managing Outlook 2007 through Group Policies (Part 3)
Introduction
In the last article we saw the process involved in downloading and adding templates on both operating System Windows Server 2003 and Windows Server 2008 to add Outlook 2007 extensions to a Group Policy. In this article we are going to play with some features that are usually required for most of the administrators such as PST management, management attachment security and etc…
PST files
PST can be a nightmare for some Exchange Administrators, and they may become difficult to manage and to create a protection strategy in a medium/large organization. PSTs can be fully managed through Group Policies and through this section we will learn how to eradicate PST usage from a network or at least change some default settings.
There are some archive products that play with PST files where the archive solution can search the network and move PST files to the archive repository. In this kind of scenario, the usage of PST can be banned from the network.
Note:
All PST settings can be found on the following path in the Group Policy: User Configuration / Administrative Templates / Microsoft Office Outlook 2007 / Miscellaneous / PST Settings.
By default, PSTs can be added to an Outlook profile. In order to prevent new PSTs to be added, we can enable the setting Prevent users from adding PSTs to Outlook profiles and/or prevent users using Sharing-Exclusive PSTs, and then click on Enabled and select No PSTs can be added (Figure 1).

Figure 1
The result will be that an end-user will not be able to pick up any option if it tries to add a PST, as shown in Figure 2.

Figure 2
Now that we have blocked end-users from adding PST files, we can also configure the current PSTs to be just a read only file which the end-user would not be able to create or delete content from. The setting that controls this behavior is Prevent users from adding new content to existent PST files, shown in Figure 3.

Figure 3
Using the previous setting the result will be an error message when a user tries to add any new content to an existent PST (Figure 04).

Figure 4
Okay, let us say that we have an internal policy where PSTs are allowed locally and we want to keep all of them in a standard path to facilitate the process to protect them changing the default location for PST and also OST files. To configure this setting, double click on Default location for PST and OST files and type in the new path (environment variables can be used), as shown in Figure 5.
Note:
The new path will be used by all PST or OST created after the policy has been applied.

Figure 5
Besides of the configuration that we have just seen, we can also change other settings related to PST, such as PST maximum size, file format and etc.
Managing Attachments
Outlook 2007 handles attachments using security level. Outlook uses 3 (three) different groups: Level 1 (unsafe attachments), Level 2 (they must be saved on the disk before opened) and others attachments where the end-user is able to open an attachment directly from Outlook.
We can use Group Policies to add and remove extensions from level 1 and level 2 groups. Just to keep us on the same page, these are the default extensions included in the Level 1 of Outlook 2007: .ade, .adp, .app, .asp, .bas, .bat, .cer, .chm, .cmd, .com, .cpl, .crt, .csh, .der,, .exe, .fxp, .gadget, .hlp, .hta, .inf, .ins, .isp, .its, .js, .jse, .ksh, .lnk, .mad, .maf, .mag, .mam, .maq, .mar, .mas, .mat, .mau, .mav, .maw, .mda, .mdb, .mde, .mdt, .mdw, .mdz, .msc, .msh, .msh1, .msh2, .mshxml, .msh1xml, .msh2xml, .msi, .msp, .mst, .ops, .pcd, .pif, .plg, .prf, .prg, .pst, .reg, .scf , .scr, .sct, .shb, .shs, .ps1, .ps1xml, .ps2, .ps2xml, .psc1, .psc2, .tmp , .url, .vb, .vbe, .vbs, .vsmacros, .vsw, .ws, .wsc, .wsf, .wsh, .xnk.
If you do not get the picture about attachments yet, we can look at Figure 6 where the attachment with .xxx extension has a Level 1 assigned to it. If you look at that figure you will see that there is no way for the user to play with that file and Outlook displays Outlook block access to the following potentially unsafe attachments: <attachment name>.

Figure 6
However, if we have the same .XXX extension is configured as Level 2, the end user will be able to see the file on the message (Figure 7), but, the message in Figure 8 will be displayed which will force the end user to save the file on the disk and does not allow it to run directly from Outlook 2007.

Figure 7

Figure 8
In order to manage the file extensions for Level 1 and Level 2 we need to change the Outlook Security Mode setting. Expand Security, and click on Security Forms Settings. Let’s select Enabled and select Use Outlook Security Group Policy, and click on OK, as shown in Figure 9.

Figure 9
Now that we defined the Outlook Security Mode in the previous step, we can expand the Attachment Security and on this location we can either Add, Remove or Disable Level 1 and Level 2 as well. In Figure 10 we are adding the extension XXX to the level 1, as soon as the client receives the Group Policy definitions and Outlook is restarted the extension XXX will be considerate level 1 which does not allow an end-user to play with the file.

Figure 10
We can also add/remove Level 1 and Level 2 extension, allow Level 1 to be displayed in Outlook and so on.
Blocking account types
Outlook 2007 supports a variety of account types to be configured through Outlook profile creation process. Using group policies we can control which protocols will be available to the end user during the profile creation. We can prevent these following protocols to be configured: HTTP, Exchange, POP3, IMAP4 and any other type.
To block specific protocols, the option Prevent users from adding e-mail account types has to be configured for that. Click on Enable and tick all services that you want to prevent to the final users (Figure 11).
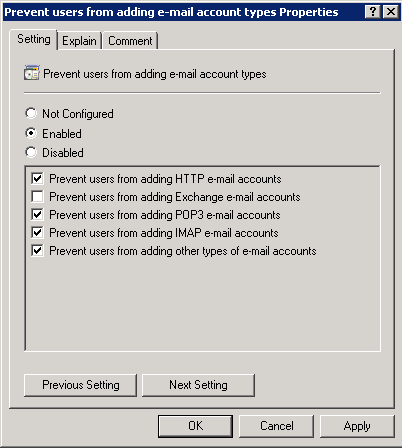
Figure 11
The result of the previous configurations is that the service configured in the Group Policy will not show up during the profile creation.
Conclusion
In this article we went over the process of configuring some Outlook 2007 settings using Group Policy. You can use this article series as a base to create your own policies based on your company requirements.
More Information:
Check out this Level 1 Attachment
If you would like to read the other parts in this article series please go to:



