If you thought that running Windows Vista, with the latest virus software and updates installed, and with Internet Explorer or Firefox locked down was enough to be protected on the Internet, you are in the same boat as the rest of us who were wrong. There is a new, high tech attack that is running around the Internet. The new attack is from the MPACK kit, available from foreign attackers. To date, mostly foreign countries have been attacked, but the exploit is so stealthy, it will be finding its way into the United States very soon. There are ways to protect yourself, but if you don’t take action, you are most certain to be attacked and infected by the MPACK kit.
The Root Problem Exposed
A team of Russian hackers developed the kit back in 2006 and have been selling it for $300 to $1000. The kit is very easy to use and can even come with another tool called DreamDownloader, shown in Figure 1. This is a tool that is used for creating downloaders usually sold with MPACK. DreamDownloader is used by simply inputting the URL of the file they want to download and the tool generates an executable file that performs the task.

Figure 1: DreamDownloader is used in conjunction with MPACK kit
The problem is that these kits and tools are used in combination to alter Web pages on common Web sites. The altered Web pages contain new IFrame entries. The new IFrame entry is short, but effective, an example is shown below:
<html>
<head>
<title>Inline Frames – demonstration</title> </head> <body> The material below comes from the website http://example.com: <iframe src=”http://example.com“ height=”100″ width=”200″ frameborder=”0″ scrolling=”no”> Alternative text for browsers that do not understand IFrames. </iframe> </body></html>
The entry redirects the browser to another Web site, as the current site is loaded. If there are no antivirus updates installed, this malicious redirection is undetected. At the other end of the redirection is a PHP server running the MPACK kit.
The server running the MPACK kit is very intelligent, as it must determine what the target computer is running for the attack. The target computer browsing the Web page is evaluated for the OS and browser, which then triggers the download of specific files that will be installed on the target computer. These files, typically additional Root Kits or keystroke capturing tools, can be installed without the user even being aware that something has occurred. At this point, the target computer is compromised and it is very hard to detect that anything has occurred. This link gives in depth detail on a typical attack scenario.
The hackers are using these exploits with the iFrame Manager to continually connect to the infected Web server, as shown in Figure 2. This means that even though a Web site is fixed, it is then reinfected by the hacker using this manager at regular intervals. The only way to get around this is to modify the password that is associated with the FTP server user on a regular basis. (For more information on this IFrame Manager, view this YouTube video)
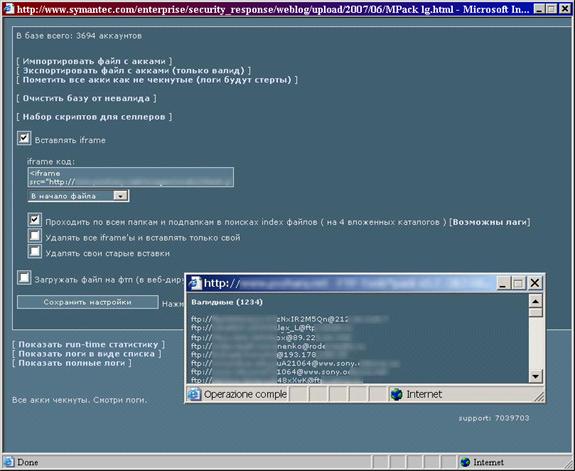
Figure 2: FTP manager
How you Get Involved
As a computer user browsing the Internet, you are at risk. This attack can occur on almost any site, as long as it has been compromised. You are merely connecting to a Web site, maybe even one that you have been using for years. If the site has been compromised, you might not even be aware of it, unless you are running the appropriate spyware, anti-virus, or other security tools.
It is very easy to get yourself involved with this attack, which is something you want to avoid! If you ignore normal security practices, which are documented everywhere, you are bound and determined to get involved. Ignoring good security practices is the easiest way to get infected by MPACK.
The problem is that even if you keep up with the latest antivirus updates, you could still be at risk. This is because the MPACK kit is constantly being updated. It is currently at v0.84. The manufacturer of the MPACK kit guarantees that no virus scan software will detect new versions.
Therefore, you also need to be running additional software or configuring your Windows desktops to detect malicious activity. This will include running Windows Vista, which includes UAC enabled. You also need to be running a firewall, either at the perimeter of the network or locally on the desktop. If you don’t take these precautions, you are going to be involved with the MPACK kit at some point.
How you Detach from being involved or Stay Clean from MPACK
I wish I could give you some spectacular tricks and configurations that would help protect you against MPACK. Unfortunately, MPACK is just like everything else when it comes to protecting your own computer and network. If you take the tried and true security methods and behaviors into account, you will stay away from MPACK and keep your computer clean.
Here is a list of things that you should be doing on or to your computer to help protect against the MPACK kit. In reality, these things will protect against any vulnerability that you will be exposed to from Email or the Internet.
- Run Windows Vista, with User Account Control enabled.
- Install the latest Service Pack for all operating systems, browsers, and other Internet related applications when they are available.
- Have a good antivirus application installed.
- Update your virus database files constantly.
- Do not log on as an administrator or with administrator privileges.
- Do not elevate Internet related applications to run with administrative privileges.
- Don’t allow applications to run from Internet Explorer, unless you are 100% aware of what they are for.
- Be aware of where your browser is going, by viewing the bottom left of the browser window, which will indicate the URL you are connecting to.
- View the URL of all hyperlinks in Web pages, before you click on them (hovering over the link will show you the URL, which might be different than you expect!).
After you implement these measures, you will be very close to eliminating these types of exploits from infecting your computer. There is no silver bullet, which is why the list of actions is so long. You must take a proactive approach to security on the Internet. Attackers and hackers are becoming more and more agile, so keeping up with them is a full time job.
Summary
So, how do you stay safe and away from MPACK? The answer is as easy as it has been for all of the other malicious viruses, malware, adware, and Trojans that have come across the IT community over the last few years. Be smart when you are on the Web, don’t open ridiculous emails that you are not familiar with, etc. MPACK is a little different, as it can wiggle its way into a legitimate Web site, but if you have the appropriate operating system features enabled (UAC and firewall with Vista), you will be notified of the behavior before you can be infected. Taking precautions and enabling the best security techniques are more than enough to protect you until you can get the virus protection that you need to fight off MPACK.



