If you would like to read the second part of this article series please go to Registry Keys for Tweaking Windows Update (Part 2).
Although Windows Update and WSUS are both generally pretty simple to configure, you can sometimes gain a higher level of control over them by making a few minor modifications to the Windows registry. In this article, I will show you some registry keys that are associated with Windows Update. As I do, I will show you the various settings that you can assign to those registry keys.
Before I Begin
Before I get started, I need to keep the lawyers happy by telling you that modifying the Windows registry can be dangerous. Incorrectly modifying the registry can destroy Windows and / or your applications. I therefore strongly recommend that you perform a full system backup prior to attempting any of the techniques that I am about to show you.
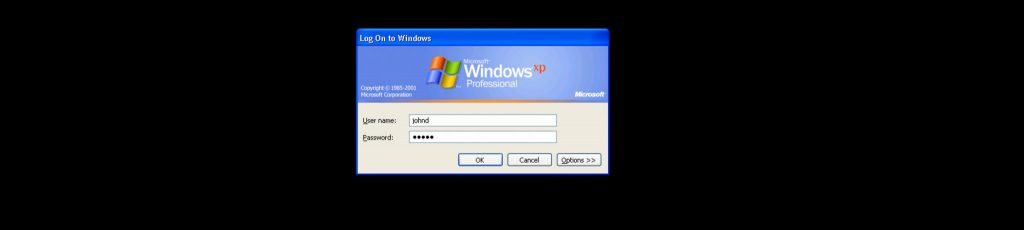
Now that I’ve gotten the standard disclaimer out of the way, there is one more thing that I need to tell you before I get started. The registry tweaks that I am about to show you are intended for machines that are running Windows XP. You can apply the tweaks to individual machines directly, or you can apply modifications as a part of a login script. Also, some of the keys that I am going to be talking about may not exist by default. If you want to use a key that does not exist, you will have to create it. You should also keep in mind that Windows Update’s behavior can be controlled by a group policy, and that if a group policy is in effect, it can cause portions of the registry to be overwritten after you have made changes.
Elevation of Privileges
One of the problems with receiving updates from a WSUS server is that users are not allowed to approve or disapprove of updates unless they are a member of the local administrators group. However, you can use the registry to give users an elevation of privileges that will allow them to approve or disapprove of updates regardless of whether or not they are a local administrator. On the flip side, you could also deny end users the ability to approve updates, reserving that right for Admins.
The registry key that controls this behavior is: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\ElevateNonAdmins
The ElevateNonAdmins key has two possible values. The default value of 1 allows non administrators to approve or deny updates. If you change this value to 0, then only administrators will be allowed to approve or deny updates.
Target Groups
One of the nice things about WSUS is that it allows you to use client side targeting. The idea behind client side targeting is that you can set up different computer groups, and you can roll out updates on a group basis. Client side targeting isn’t used by default, but if you decide to use it, then there are two different registry keys that you will have to create. One of these keys enables client side targeting, while the other specifies the name of the target group that the computer belongs to. Both of these registry keys must be created at: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\
The first key is a DWORD key named TargetGroupEnabled. You can assign this key a value of either 0, which disables client side targeting, or of 1, which enables client side targeting.
The other key that you will have to create is string value named TargetGroup. The value that you would assign to this key is the name of the target group that the computer should be assigned to.
Assigning a WSUS Server
If you have been involved in networking for a while, then you probably know that network designs tend to change over time. Things like company growth, new security requirements, and corporate restructurings often force the underlying network to change. So what does this have to do with Windows Update? Well, WSUS is scalable and can be deployed in a hierarchical manner. This means that an organization can have a multitude of WSUS servers deployed. If a PC is moved to a different part of the company, then the WSUS server that it was initially configured to use may no longer be appropriate for its new location. Fortunately, a couple of simple registry modifications can be used to change the WSUS server that the PC gets its updates from.
There are actually two registry keys that are used when specifying a WSUS server. Both of these keys are located at: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\. The first key is named WUServer. This registry key holds a string value which should be entered as the WSUS server’s URL (example: http://servername).
The other key that you will have to change is a string value named WUStatusServer. The idea behind this key is that the PC must report its status to a WSUS server so that the WSUS server knows which updates have been applied to the PC. The WUStatusServer key normally holds the exact same value as the WUServer key (example: http://servername).
The Automatic Update Agent
So far I have talked about how to connect the PC to a specific WSUS server or to a specific target group, but this is only half of the process. Windows Update uses an update agent that actually installs the updates. There are a number of registry keys located at HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU that control the automatic update agent.
The first of these keys is the AUOptions key. This DWORD value can be assigned a value of either 2, 3, 4, or 5. A value of 2 indicates that the agent should notify the user prior to downloading updates. A value of 3 indicates that updates will be automatically downloaded and the user will be notified of installation. A value of 4 indicates that updates should be automatically downloaded and installed according to a schedule. For this option to work, the ScheduledInstallDay and ScheduledInstallTime keys must also be set. I will talk more about those keys later on. Finally, a value of 5 indicates that automatic updates are required, but can be configured by end users.
The next key that I want to talk about is the AutoInstallMinorUpdates key. This key can be set to a value of either 0 or 1. If the key is set to 0, then minor updates are treated just like any other update. If the key’s value is set to 1, then minor updates are silently installed in the background.
Another key related to the Automatic Update Agent is the DetectionFrequency key. This key allows you to specify how often the agent looks for updates. The key’s value must be a whole number between 1 and 22, and indicates the number of hours between each detection attempt.
A related registry key is the DetectionFrequencyEnabled key. As the name implies, this key either enables or disables the Detection Frequency function. Setting this key to a value of 0 causes the DetectionFrequency key to be ignored, while setting it to a value of 1 causes the agent to use the DetectionFrequency value.
The next key that I want to talk about is the NoAutoUpdate key. If this key is set to a value of 0, then automatic updates are enabled. If the key’s value is set to 1, then automatic updates are disabled.
The last registry key that I want to talk about is the NoAutoRebootWithLoggedOnUsers key. As you probably know, some updates simply cannot be applied without rebooting the system. If a user happens to be logged in, then a system mandated reboot can be very disruptive. This is especially true if the user has walked away from their desk without saving their work. This is where the NoAutoRebootWithLoggedOnUsers key comes into play. The key can be assigned either a value of 0 or 1. If the value is set to 0, then users will receive a five minute warning and then the system will reboot automatically. If the value is set to 1, then users will simply receive a message asking them to reboot their systems, but they can reboot at their leisure.
Conclusion
There are a whole lot more registry keys related to Windows update. I will be discussing the rest of them in Part 2 of this article series.
If you would like to read the second part of this article series please go to Registry Keys for Tweaking Windows Update (Part 2).


Brian,
Great write up. Just a minor tweak on the keys…
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate
Thanks Brien,
Great article and easy to understand and implement.
Thanks!
If the NoAutoUpdate key is enabled, set to a value of 1, does this disable the PC from both WSUS updates from our server and Windows Updates from Microsoft?