These devices are extremely convenient, but they can also pose a big risk to company networks. You never know what users may be doing with them: installing unauthorized or unlicensed software, uploading programs or documents that contain viruses or Trojans, or even downloading sensitive data such as trade secrets, internal memos or company financial information. Even if you make policies prohibiting them, users can sneak the devices in easily. They’re small and many are disguised as keychain fobs or concealed inside pens or other objects. You can see some examples of these devices at http://www.forensics-intl.com/art22.html. As the accompanying article indicates, law enforcement agencies and computer forensics experts are sounding the alert about the potential security threats inherent in these concealable devices.
Product: GFI EndPointSecurity
Product Homepage: GFI EndPointSecurity – Network device control
30-day Trial Version: Download GFI EndPointSecurity

It’s essential for administrators to have a way to technologically control the use of portable storage devices, and that’s what PSC is designed to do. In addition to USB and FireWire (IEEE 1394) drives, you can also control connection to computers on your network of such devices as digital cameras, MP3 players, smartphones and handheld computers (Pocket PCs and Palm OS PDAs). You can even control users’ access to floppy disks and CD drives. In this article, we’ll take a look at GFI’s new product and how it works to protect your network.
Why You Need a Way to Control Portable Storage Devices
The key advantage of portable storage devices is easy access. With a flash drive or a CD writer, users can copy files from their work computers to take home or they can bring programs and data files from their off-site computers and put them on their office systems. That sounds great in theory, but we all know that access and security are at opposite ends of the continuum, and the more you have of one, the less you have of the other. There are a lot of problems with giving your users free reign over what goes onto your network’s computers, including the following:
- Users can deliberately or unintentionally introduce viruses that can then spread to all the computers on your network, in some cases crashing systems and bringing the entire network down.
- Users can copy company information that should remain confidential, exposing your business data to competitors, the media and others who have no business seeing it. If your business is covered by laws or governmental regulations requiring you to keep certain information private (for example, HIPAA in the health care industry or the GLB Act in financial services businesses), your organization could even be held legally liable.
- Users can transfer data to company computers that should not be there, such as pornography or other offensive material. In addition to wasting time and decreasing productivity, this could result in a civil suit (for example, for sexual harassment if the offensive material makes another employee uncomfortable) or even a criminal investigation (for example, in the case of child pornography or communications involving other illegal activities such as terrorism).
Newer versions of portable storage devices pose even more of a risk than before, simply because they can transfer data much faster. USB 2.0 and FireWire (IEEE 1394) have much higher transfer rates than older technologies. That means a data thief can get away with more of your precious information, and a careless employee can dump more viruses onto your network even when connecting for only a short time. At the same time, capacity is increasing; flash memory devices can now hold a gigabyte or more of data and prices are falling all the time. To make it worse, Windows 2000 and XP computers will automatically mount these devices so that they appear as (and can be used as) just another drive on the computer.
If you have any data on your company network that is sensitive or should not be leaked outside the organization, or if your company falls under privacy statutes or has any employees at all who could conceivably lodge sexual harassment complaints, or if there is any chance whatsoever that any employee cannot be trusted not to ever do anything illegal, you should prohibit or restrict the use of personal portable storage devices.
Gartner Research analysts agree, and so do security instructors for the SANS institute, as reported at http://www.arcamax.com/cgi-bin/news/story/1017/11162/332261.
You can make rules against the use of these portable devices, but there are always a certain number of employees who disregard rules in favor of convenience. Rather than rely on voluntary compliance, you can ensure that these devices don’t wreak havoc on your network by putting technological barriers in the way of their use.
Note:
You may have read that Microsoft has recognized the threat posed by portable storage devices and after Service Pack 2 is installed on Windows XP, you can configure a registry key to make USB storage devices read-only. This is commendable and might help prevent data theft. However, it doesn’t go nearly far enough to solve the problems discussed above. Employees can still display illicit material from the devices on their computers. Further, many companies are using desktop machines running Windows 9x, NT or 2000, and many companies that have upgraded to Windows XP are holding off on installing SP2 for a variety of reasons.
Why We Like GFI LANguard PSC
We believe a third-party solution is the best way to control portable device usage. Rooting around in the registry always poses some risk, and in this case, it accomplishes only part of what we need to do (even assuming all our systems are running Windows XP with Service Pack 2). So we downloaded the PSC software from http://www.gfi.com/downloads/register.aspx?pid=esec. A free trial version is available at the Web site (it times out after 30 days, or 60 days with a key that is e-mailed to you after you download the program). Pricing ranges from $295 (for 25 computers) to $1495 for an unlimited license. You also get three months of free support and upgrade protection.
Note that you have to be logged on with administrative credentials and you can only install on Windows 2000, XP or Server 2003. Other than that, the installation process was pretty straight forward.
We were pleased to find that you can select any or all of the following removable media types to block or restrict:
- Removable storage media
- Floppy disk
-
CD or DVD drive
Control is user/group based, which makes it easy for Windows administrators who are familiar with this type of access control. You can choose to use either Active Directory global groups, or the local computer’s security groups. In a domain environment, you’ll probably want centralized control through AD. If you have standalone systems, you can use local groups, but you’ll want to be sure that the users aren’t local administrators; otherwise they would be able to circumvent the program’s protection by killing the process.
Ease of Management
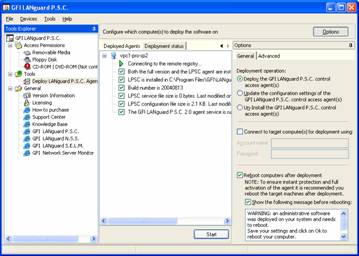
When you launch the PSC program, it may take a while to start as it checks for updates. This is actually a good thing, as it means the program will always have the most recent updates as long as the computer on which it’s installed is connected to the Internet. The console interface is shown in Figure 1. It’s highly intuitive and in most cases, you can accomplish what you want to do in a few easy clicks. For some reason, we were not able to resize the console window.
Figure 1: The PSC Console Interface
You can configure which users will be allowed to use removable media, the floppy disk drive and the CD or DVD drive(s) by adding them to the authorized users list. We especially liked the fact that you can configure access in one of two ways:
- Specify the users and groups that are allowed to access the device
- Specify the users and groups that are NOT allowed to access the device
That means that whether your company’s philosophy is “block all unless you have a reason to grant access” (also known as the principle of least privilege or the “need to know” method) or it’s to “allow all unless you have a reason to deny access” (an open access policy), PSC will be equally easy for you to configure.
We were afraid it would be a pain to install the software on all the computers in a large organization. That would take a lot of time and might require either physically visiting each computer, creating an MSI package so you could use Windows Group Policy’s software installation feature, or using an expensive deployment tool such as SMS. We were in for a pleasant surprise. You can deploy the agent software on one or more computers right from within the PSC console interface, using the “Deploy LANguard P.S.C. Agents” option under the Tools node in the left console pane. You can deploy the agents to a single computer, a list of computers from the domain, or a list of computers from a file.
It’s equally easy to keep tabs on which computers on your network are protected by PSC. You can click the Deployed Agents tab to view the status of computers on which the agent has been deployed. You’ll be shown which software is installed (full version and/or agent), path in which the software is installed, the build number, file sizes and whether the agent service is running, as shown in Figure 2.
Figure 2: You can view the status of computers on which the agent is deployed
Once we got the software installed, agents deployed and access controls configured, PSC did what it said it would do – when we tried to access the removable media drives with an account that was not included in the authorized users (or a member of a group listed in the authorized users list), we were denied access.
Summary
We found the software easy to install and use. The interface is simple, and we like that GFI included links to their support center and Knowledge Base within the management console. There is a definite need for a program like this. Administrators are sure to sleep easier at night, knowing they have a way to keep rogue USB drives and other removable media from threatening the integrity of their networks.
The program’s good points include:
- straight-forward, easy installation
- intuitive interface
- flexibility in configuring access
- deployment tool makes it easy to install agent on remote computers
We did encounter a few minor annoyances:
- inability to resize the management console
- no control over rebooting after installation
- local administrators can circumvent the program by killing the process.
WindowSecurity.com Rating: 4/5

GFI LANguard Portable Storage Control is now GFI EndPointSecurity – device control and monitoring