If you would like to read the next part in this article series please go to Using DPM 2010 to protect mail on client machines (Part 1).
Using DPM Client on the workstation
So far in the first article, we covered the protection of a machine. Now it’s time to work on the restore process. First things first, let’s start playing with the DPM Client. In order to install it we just need to run the file dpmui.msi that can be found on the X:\DPM2010\dpmcli folder on the DPM installation disk (where X represents the DVD drive letter).
The installation process does not ask any question and the result will be two new icons underneath Microsoft System Center Data Protection Manager group in the All Programs (Figure 1), and a new entry to start DPM Client in the user Startup (Figure 2).
Figure 1
Figure 2
After restarting the machine, a new DPM icon will show up in the systray, as shown in Figure 3. At a glance we will be able to see useful information about the client protection, such as: Data being protected, when was the last synchronization, start a new Sync, open the client or even restore data.
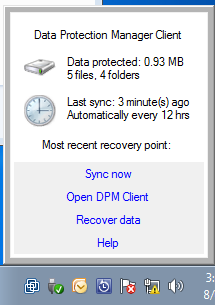
Figure 3
If you click on Open DPM Client, the first tab will be Summary (Figure 4) where we can check all information about protection out in a single page. We can force synchronization and validate when the last time that the data was transferred to the DPM Server.
Note:
When you create a Protection Group for clients we are in fact creating a policy that will be applied to all machines that belong to that Protection Group.
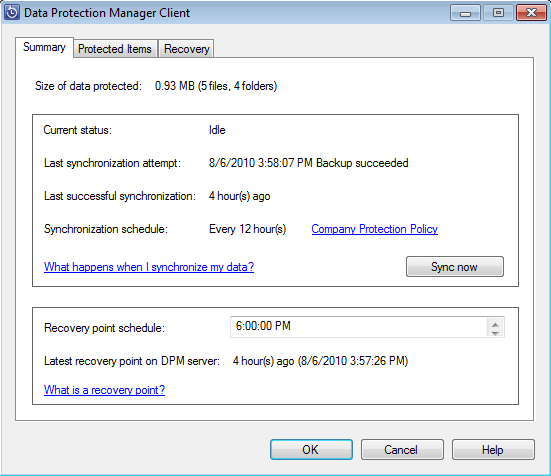
Figure 4
If you click on Company Policy in the main page (Figure 5), you will be able to check all policies configured by DPM Administrator, such as: What extensions will be excluded from the protection, folders that will be excluded, when synchronization will occur and recovery point creations.
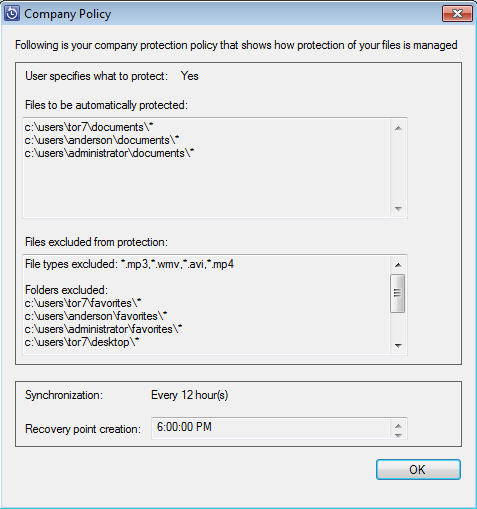
Figure 5
In the Protected Items tab (Figure 6), we can visualize the policy in action where all items in bold cannot be changed by the end-user because they were defined at the policy level in DPM. Also, if the DPM Administrator has enabled the user to protect their data on the client selecting the option Allow users to specify protection group members during the Protection Group creation, then the end-user will be able to check which folders he wants to be protected always using a format that the end-user understands such as: it will show in context not a physical path. In the same page, an end-user can click on Calculate to validate how much space will be protected based on its selections.
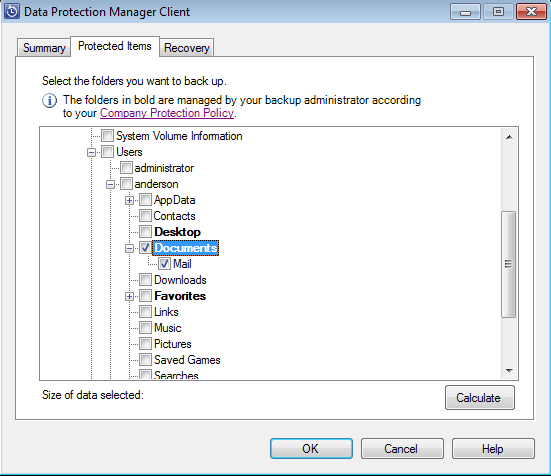
Figure 6
Recovering Data Using DPM Client
The main objective of this article is to provide an alternative to protect PST from VIP users. Based on that scenario, as soon as we have DPM Server settings in place (agents installed and protection group created) we can accomplish the restore of VIP users in three different ways; using the Previous versions, Recovery Points using DPM Client or on the server side restore the data from DPM Management Console.
The most common way to restore a data is using the local copy of the data. In order to restore from the client, the end-user just need to right click on a file or folder and click Properties, and then Previous Versions, as shown in Figure 7. Just by doing that the user will have the options available to restore the data, the available methods are: use Copy button where a copy of the protected file will be available and then the user can merge or play with different versions of the file; and the second option is Restore… that will overwrite the original file.

Figure 7
The second method is to restore data that is being kept in the DPM Server, for instance, the user can open DPM Client, click on Recovery tab (Figure 8) and type in the DPM Server and click on Search button, the result will be all recovery points available for that user. The user can restore the data or just click open to visualize and check which information is available on that specific recovery point.
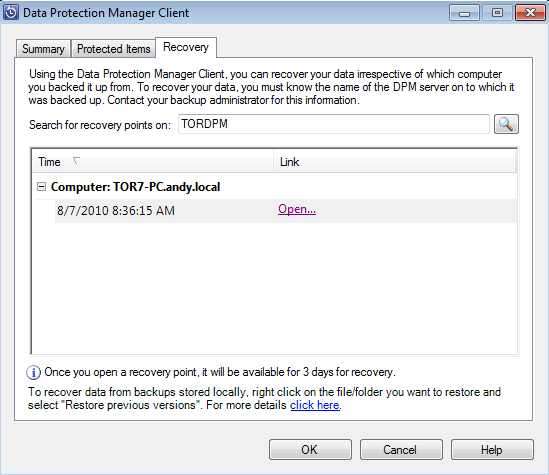
Figure 8
The last but not least method is using DPM 2010 Administrator Console, where the administrator can check what has been protected and then restore files, folders and etc.
The process is really simple, just open DPM 2010 Administrator Console, click on Recovery and expand the desired computer agent from the list, as soon as you click on User data (Figure 9) for that computer a list of all users of that specific computer will be listed and we have a calendar that says which day we can restore data and what time the recovery points are available.
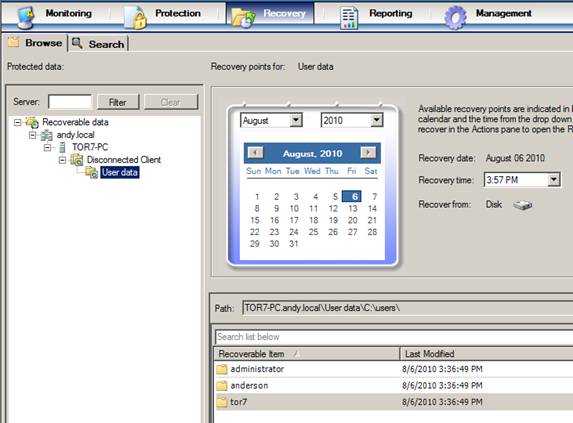
Figure 9
For this article, let’s open the username and let’s find the folder mail where all users’ PST files are kept. Click on that folder, we can click on Restore item that can be found in the Toolbox Actions. After that these steps can be performed to restore the content, as follows:
- In the Review Recovery Selection page. The items selected in the console will be displayed, also the Recovery Point date and time, where this restore will come from (in our case Disk) and finally the recovery source. Let’s click Next. (Figure 10)
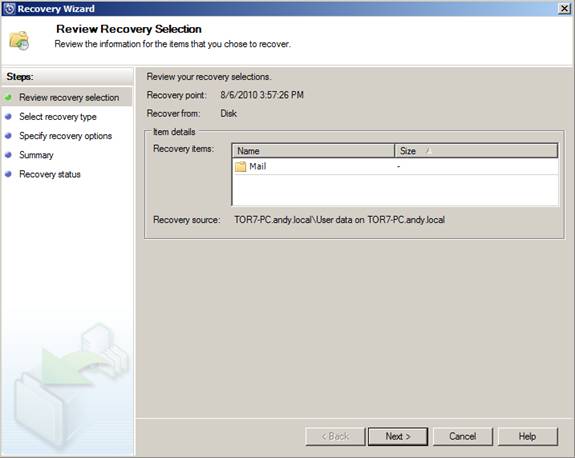
Figure 10
- In the Select Recovery Type page. We can restore the data to the original location or to an alternate location which can be a folder on DPM Server or even on the original client. In our example below we are going to use the original machine however in a different folder. Click Next. (Figure 11)
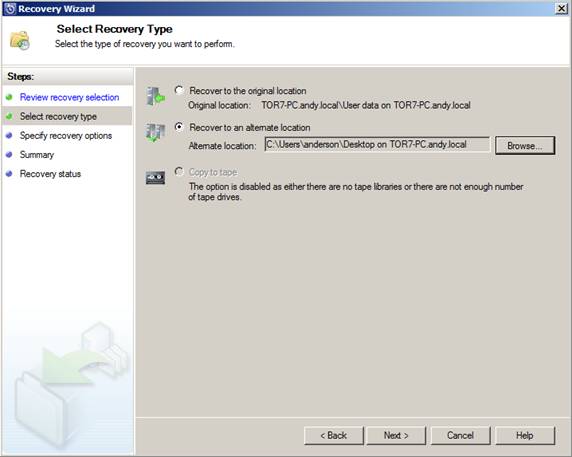
Figure 11
- In the Specify Recovery Options page. We can define what we are going to do if there is an existent file/folder, security restore options, SAN Recovery and Notification (Figure 12). Click Next.
Note:
If your Notification area is grayed out and you want to use it to inform the user that the restore is complete, then you need to go to DPM Options and configure SMTP Servers, as soon as you have it configured you are good to go with Notifications.
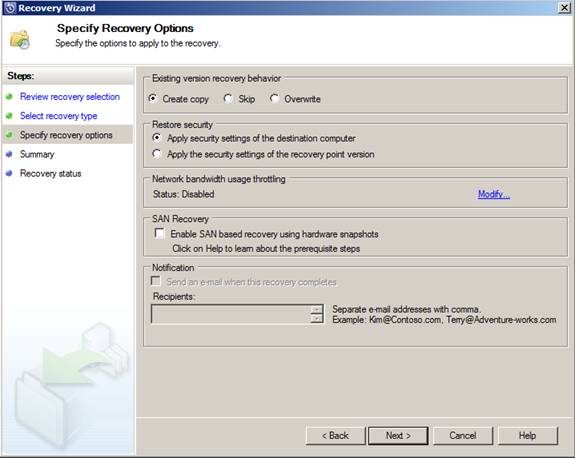
Figure 12
- In the Summary page. A summary of all options that we selected so far will be displayed, to start the restore process just click on Recover.
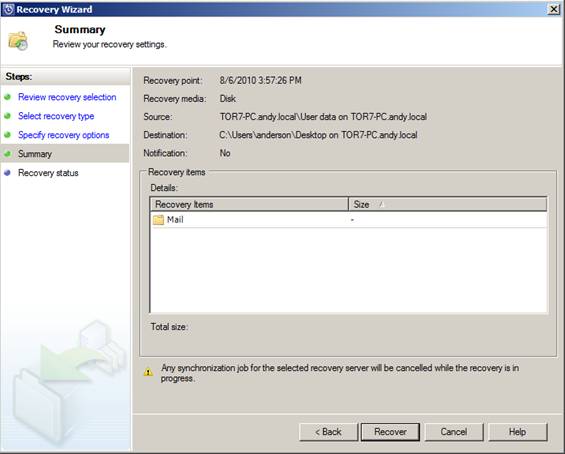
Figure 13
- In the Recovery Status page. The results of the operation will be displayed, such as: Start and End time, how data was transferred and if it was successful or not the operation. Just click on Close to finish the wizard. (Figure 14)
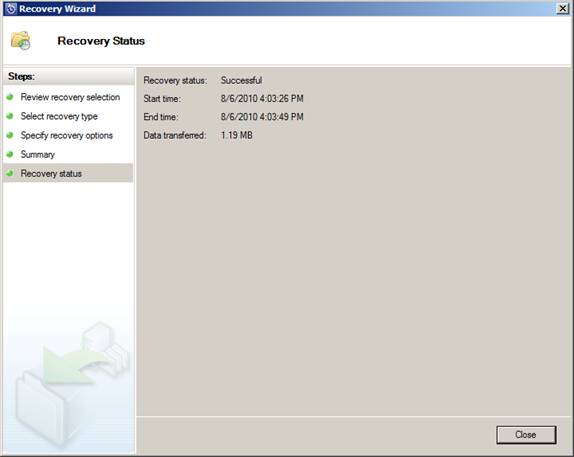
Figure 14
Generating Reports for Current Protection
DPM 2010 has a new report capability that is really handy for administrators and you can use those reports to get a flavor how protected your VIP users are. In order to generate a Recovery Point status report, open DPM 2010 Administrator Console, go to the Protection Area, and then click on Recovery Point Status (Figure 15) in the Toolbox Action. In the new dialog box, define the date range and click on Generate report. The result can be seen in the Figure 16 where the letter A represents that we have a recovery point available.
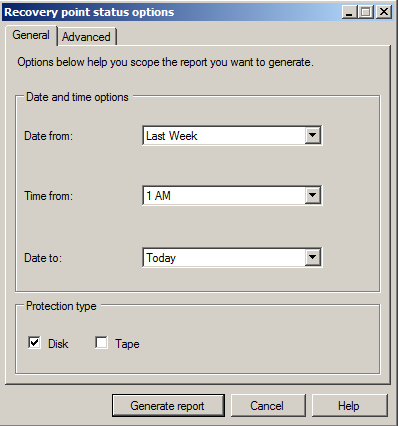
Figure 15

Figure 16
Common Scenarios Where DPM Server and DPM Client can Help your VIP Users
Now that we validated the process to protect and restore data from a workstation, now we can use it for some special users and situations, as it follows:
Scenario 01: VIP User lost his laptop and he wants his PST files on the new laptop ASAP!
Well, the previous ASAP word came to the picture because we are talking about VIP Users. So… somehow the user lost his laptop and he wants to retrieve his files including an important PST.
That’s easy, using DPM even if your computer does not belong to a protection group (figure 17), based on his credentials he will be able to click on Recovery tab and all available recovery points of his old computer will show up and the user can easily restore his data to the new laptop.
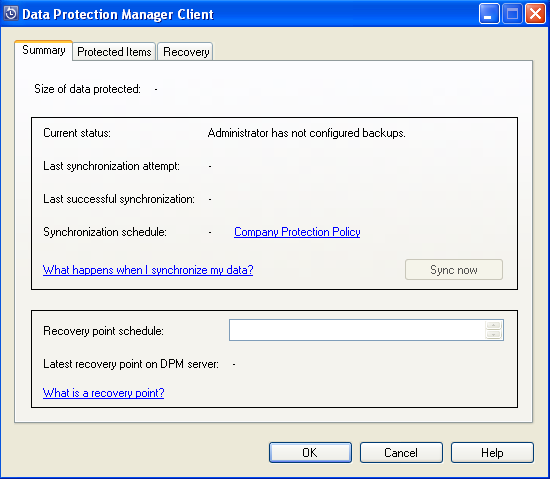
Figure 17
Scenario 02: VIP user doesn’t have his laptop handy and he wants an important e-mail through OWA.
Well, you may be asking why he hasn’t copied from his PST to the Mailbox if that was so important. I’ve seen it happening a couple of times before and for all of them the IT dept had to come up with a plan because it came from a VIP user. There are several solutions for this one: the first one is make sure to instruct users about technology to avoid this kind of stuff; make them use large mailboxes (Exchange 2010 is here and helps a lot!).
There is also the painful one where the IT has to bring that data and it doesn’t matter what it cost, so using DPM 2010 it’s sort of easy to restore such data. Basically, we need to restore the PST file to a location and import it to the user mailbox in a specific folder. Make sure that the user has enough quota limits on his mailbox and restore the data using Import-Mailbox cmdlet.
Conclusion
In this second article we went through the restore process for end-users using DPM Client and also using DPM Server. The main idea of this article series is to bring the DPM technology also for end-users where they can have their files protected by DPM like the backend is protected by the same tool.
Applying the concepts that we have seen here can save headaches from IT side just by protecting special user PST and any other important files.
If you would like to read the next part in this article series please go to Using DPM 2010 to protect mail on client machines (Part 1).



