If you would like to read the other parts in this article series please go to:
Introduction
Windows 7 is Microsoft’s newest desktop-based client operating system which builds on the strengths and weaknesses of its predecessors, Windows XP and Windows Vista. Every aspect of the base operating system as well as the services it runs and how it manages the applications loaded within it has been reviewed and made more secure if possible. All services have been enhanced and new security options making it more reliable. Aside from basic system enhancements and new services, Windows 7 delivers more security functionality, enhanced auditing and monitoring capabilities and the ability to encrypt remote connections and your data, Windows 7 also has newly developed internal protection enhancements to secure system internals such as Kernel Patch Protection, Service Hardening, Data Execution Prevention, Address Space Layout Randomization, and Mandatory Integrity Levels.
Windows 7 is designed to be used securely. For one, it was developed Microsoft’s Security Development Lifecycle (SDL) framework and engineered to support Common Criteria requirements allowing it to achieve Evaluation Assurance Level (EAL) 4 certification which meets Federal Information Processing Standard (FIPS) #140-2.When used as a stand-alone system, Windows 7 can be secured for personal security. Windows 7 has many helpful security-based toolsets contained within, but it’s only when Windows 7 is used with Windows Server 2008 (R2) and Active Directory, that it turns into a bullet-proof vest. By leveraging additional security from tools such as Group Policy, you can control every aspect of desktop security. If Windows 7 is used mainly for your home office or personal use, it can still be secured to prevent many current methods of hacking and attacking and can be restored quickly if disaster does in fact strike, so although beneficial, Windows 2008 is not completely necessary to apply a high level of security to Windows 7. You should also consider that Windows 7 is inherently secure, but it doesn’t necessarily mean that you should rely on the default configuration without making any adjustments to extend your security coverage. You should also consider that you will eventually be subjected to some form of malware or Internet-based attack when the computer is being utilized on any public network. If a computer is used for any type of public Internet access, your system and the network on which it is connected, becomes opened up to possible attack.
In this article, we will cover the fundamentals you need to know to secure Windows 7 correctly, achieve a baseline level of security, review advanced security configurations and explore some of the lesser known security functionality Windows 7 provides in order to prevent or protect against a possible attack. We will also look at the many ways you can safeguard your data and get back up and running quickly if you do in fact suffer from some form of attack or catastrophic system malfunction you cannot recover from. This article introduces the concepts of security, how to harden Windows 7, how to install and provide security for your running applications, how to manage security on a Windows 7 system and how to prevent the problems caused by malware. This article also covers the process of safeguarding your data, the backup and recovery operating system features, how to restore your operating system to a previous state and to ways to recover you data and system state if a disaster does occur. We also cover strategies to do it quickly. Topics are also covered on how to work safely while working online or over the Internet, how to configure biometric control for advanced access control and how Windows 7, and when used with Windows Server 2008 (and Active Directory), how you can securely integrated more options for control, management and monitoring. The goal of this article is to familiarize you with Windows 7 security features, enhancements and their application as well as to give you some insight on how to plan for and apply these security features correctly. The concepts we cover are divided up and organized in a building-block approach.
Caution:
If working in a corporate or other professional environment, do not make adjustments to your company’s computer. Make sure you work within the published security plan (or policy), published best practices, principles and/or guidelines. If you are unfamiliar with security topics and Microsoft products, read the production documentation before applying any changes to your system.
Security Management and Monitoring
Windows 7 can be secured like a fortress. If using Windows 7 in the enterprise, you can use an Active Directory infrastructure and take advantage of many security enhancements provided when logging into a Domain, or using Group Policy to further enforce your security posture. Either way, centralized management of security tools, settings and logs is generally the most important consideration when trying to apply security – how will you manage it, monitor it and then update it once installed and configured? With Windows 7, many of the changes you will see are in the basic layout of tools and services apply to security. For example, the Start menu keyword ‘Security’ option we discussed earlier centralizes the management of security application for Windows 7.
A rule of thumb is that you want to make applying security (and then managing it) as easy as possible. Nobody enjoys sifting through the OS to find applications, services, logs and events or actions to configure or monitor. With Windows 7, arguably as a new user could get lost in a sea of paths, wizards, applets and consoles before even finding and configuring Windows Firewall, the most basic security feature provided. Even some of the more experienced techs have cursed yet another Windows OS that ‘moved things around on you so you can’t find it…again’. It is however the easiest of all the past Windows versions to manage since all information can be indexed and provided via the Start menu for quick searching.
Other than the Start menu, a handy way to manage many of the security functions in Windows 7 is to build a custom Microsoft Management Console (MMC) and add your toolsets into it. One of the things that will confuse many new users of Windows is that Microsoft enterprise solutions provide a clean way to centralize control and monitor everything on every system on your network (MOM is a perfect example), The client OS is a stand-alone unit that also must be secured locally, so for home users, a custom management console may be the answer to your centralized security management questions. Unfortunately, the Security Center will only get you so far when using XP and Vista and then in Windows 7, it’s further fragmented to Control Panel applets and MMC Snap-ins – so how can you quickly centralize access to key tools? To apply security to the Windows 7 OS, you must access many different areas of the system to customize your configuration in order to harden it, so if you took the applications and functions you needed and placed them in one area, you can now quickly and easily gain access back to them for security audits or log reviewing. This custom MMC may just do the trick.
To create a custom console, simply go to the Start menu and type ‘MMC /A’ and you will launch a new Microsoft Management Console (MMC). You can save it to any location on your system and name it whatever you want. To populate it, you need to go to the File menu and select Add/Remove Snap-in. Add all the tools you want or need. Figure 1 shows a custom console with most if not all of the available security options installed.

Figure 1: Creating a Custom Centralized Security Console with Microsoft Management Console Snap-Ins
You will find many useful tools within the snap-in options available. For example, TPM Management is a Microsoft Management Console (MMC) snap-in that allows administrators to interact with Trusted Platform Module (TPM) Services. TPM services are used to administer the TPM security hardware in your computer. This means you need specialized hardware, updated BIOS code and the correct CPU chip. Just like virtualization needs a specialized chip, so does TPM. TPM is a way to introduce a new level of hardware level security in to the equation so that you know you are getting a hardened system. You can manage it here if you are TPM compliant. TPM will use the hardware bus to transfer messages and can be used in conjunction with software features like BitLocker.
Once you have your consoles created and you know how to access the areas in which to apply security configurations within the OS, your next step is to monitor your system. There are many ways to do this. For example, you can keep it simple (home user) and just keep an eye on it from time to time on some sort of simple schedule. Like, every Sunday night after surfing, you check the console firewall logs and Event Viewer logs. If you dig into the configurable options, you will find out that you can schedule alerts and notifications, have logs filtered and saved automatically for review and so on. Make sure that you keep an eye on things. Just because you secured it well doesn’t mean it will remain secure.
So, in sum – the general areas where you will access and apply security to Windows 7 is by quickly accessing it within the Start menu. You can also work within the Control Panel (applets such as Administrative Tools, Windows Firewall and Windows Defender as examples) to gain access to security tools and settings. You can also create a custom MMC and configure it to gain access to hidden tools, as well as provide a centralized console for security administration. You can however browse the various areas of the OS and do the same thing, but hopefully this tip helps you apply security a little easier by giving you access to security tools provided with Windows 7. You can apply templates; create tasks and actions and even script advanced security configurations with advanced toolsets.
Tip:
You can also apply security management with tools like PowerShell and Netsh (such as the netsh advfirewall command), so there are easy ways to apply scripting functions and/or command line based options for applying security in Windows 7.You can also use ‘tasks’ to kick off jobs, scripts or batch files and services so that you can (as an example) keep a backup of Event Viewer logs for audits, review or simple safekeeping.
Next, you need to be able to access and further configure the base system after install to harden it for use and since Windows Updates are inevitable, you should create a plan to have them download and installed as soon as possible. Most times, updates come after the attacks, so it’s wise to get them tested and installed as soon as possible. There are reasons why they have been released. They are titled ‘Security Updates’ as seen in Figure 2. These updates are always numbered and can be researched online for more information.
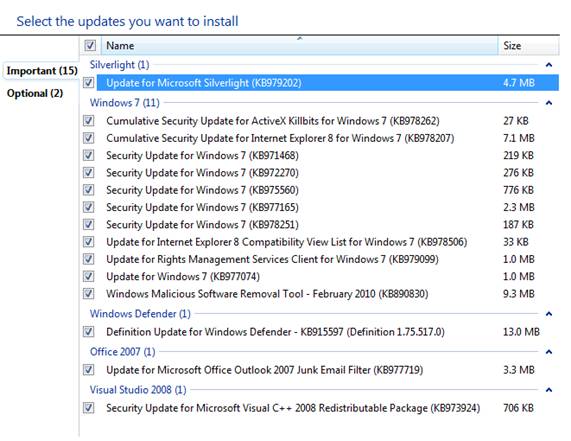
Figure 2: Installing Windows Security Updates with Windows Update
You also need to keep Service Pack levels up to current releases and reapply them as necessary. Other running applications and services in your system need to be managed, monitored and updated often as well, sometimes too often as is the case with Antivirus and Spyware removal programs.
Once your system has been completely patched and configured for use, next is to install Microsoft Security Essentials (MSE), a third party Antivirus (AV) program, configure Windows Defender (spyware) for use and configure security for malicious software (malware) protection.
Note:
Microsoft recently released a new line of security software called Forefront. This line covers all aspects of deploying and managing enterprise security in the enterprise. They also made sure that the client OS is secured with new functionality as well, such as Microsoft Antivirus, found within the MSE pack.
Malware Prevention and Protection
Every system whether it be a Windows file server, Linux desktop or Apple OS X workstation are all prone to malware. Malware is the term used to define all types and designations of malicious software that can infiltrate, penetrate, hijack and ultimately destroy your computers operating system, applications or data beyond repair. Worse, malware targets not only your base operating system, but also your personal data, privacy and identity. Malware comes in many forms, such as viruses, worms, logic bombs and Trojans. To keep Windows 7 secure, you need to configure it to keep malicious software off your system. Malware comes in most commonly from accessing the public Internet and getting emails, (instant messaging) IM messages, using shared data on Web and FTP servers, or other public network connection-based software applications such as peer-to-peer (P2P) file sharing software. Once a single system (or email mailbox) gets infected, the malware can spread quickly and sometimes without your knowledge. Malware can also access your system from foreign or unprotected external drives, thumb drives and sometimes over the network itself. It’s almost guaranteed that either through receiving email or viewing content on servers on the public Internet, you will be subjected to some form of eventual attack.
To keep malware out, you must try not to introduce it. Malware prevention is different from malware protection; however both work together towards a mutual goal which is virus-free computing. Prevention focuses on the steps that must be taken to keep malware out and off your system so that you can try to prevent future attacks or issues from taking place. You can limit your exposure in many ways. Prevention is about having discipline and keeping aware and applying these security concepts consistently when configuring any vendor-based software platform. Protection comes in the form of installed applications such as Antivirus and Spyware software scanners. Protection is what you can apply in the form of scanning and filtering tools, auditing tools and protocols or encryption made for secure communications.
Note:
There are two types of security applications; proactive and reactive. Good brainstorming, design and consideration during the planning phase will get you on track, but for continued support, you need to consider how you will manage and support it. With malware, you need to stay on top of updating your AV program so that you are scanning for and stopping new threats and exploits. Proactively plan so that you can keep everything updated and secure, but always have a plan for the possibility of your defenses being breached.
To manage, monitor and secure the system against potential malware threats, it’s recommended that you install, configure and continually update Antivirus and Spyware removal software packages. You can install a third-party software application, or use some of Microsoft tools, such as Windows Defender seen in Figure 3.
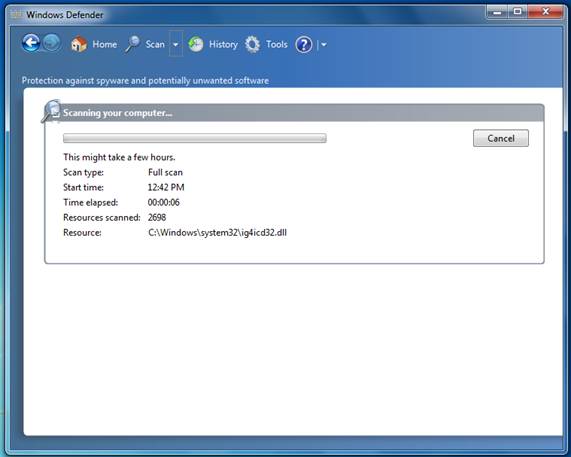
Figure 3: Using Windows Defender
Windows Defender scans for and removes Spyware. An antivirus application will actively scan for and attempt to find and remove viruses, worms and Trojans. If both are used together, you proactively protect your system against most attacks. As with the OS itself, you also need to keep these applications updated with hot fixes and patches or they become subject to attack. As well, new definition files need to be downloaded and installed often to scan for new threats.
Windows Defender is helpful for scanning your system files (Quick or Full), and is updated often which is what is most important when selecting any spyware software. If definitions are not updated to match the updates in attacks worldwide, it’s practically useless at thwarting new attacks, unless it has some form of hysterical behavior with active scanning.
Some AV programs also intelligently scan your system for ‘things out of the ordinary’, or the ‘match a pattern from a similar attack’, which is called heuristics. Although helpful, it doesn’t catch everything so keep these tools updated. Windows Update will update Windows Defender when you run it. Third party applications (with the exception for key device drivers) are commonly not found through Microsoft. It’s also important to consider that running these tools in an active state, costs processing power, memory usage and overall taxes your system resources considerably. Therefore, it’s wise to consider planning for this deployment prior and make sure that your Windows systems can handle it. Once you have malware protection up and running, you should actively harden any other areas that need to be locked down such as Internet Explorer settings.
You can secure Windows 7 by using a new feature called Data Execution Prevention (DEP). This is a feature that monitors your programs and how they use your system memory. This adds a level of security to programs that stay resident and use memory as a way to launch attacks. You can turn it on for all programs, or just ones you select. To configure it for use, go to the Start menu and open the Control Panel. Click the System applet, and then select the Advanced Tab, Performance Options, Data Execution Prevention tab as seen in Figure 4.
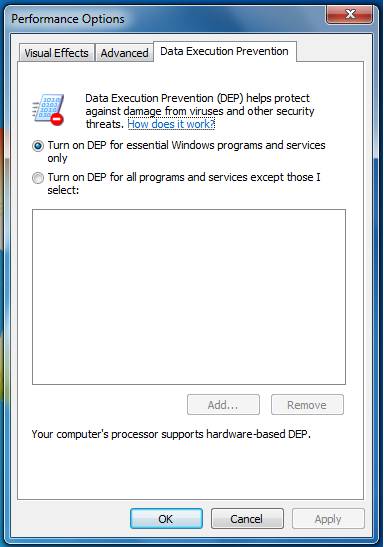
Figure 4: Configuring Data Execution Prevention (DEP) in Windows 7
Viruses today are far more complex than the ones from the past. As each year passes, hacks become more difficult to prevent and malware becomes more and more advanced to keep itself hidden (stealth) and deliver a catastrophic payload. Also, it does this without the end user or administrator of the systems knowing about it. This is because as technology of the past became more complex, so did the attacks. For example, by going to a Web page and viewing it, you could install malware on your system without your knowledge through scripts taking advantage of exploits in the Web browser’s bugs. Also, because of flexibility, the browser is obviously made to function with all types of protocols, scripting languages, plug-ins and toolbars; it’s difficult to keep a high level of security without constantly updating the browser to lock it back down. It’s also cumbersome to visit sites to do business (or pleasure) and constantly be asked questions about adding sites to your safe zone before being granted access, or letting the Web browser quickly check to see if the Web site is legitimate. Yes it will keep you more secure, but you will have to deal with some of the headaches revolved around restricting or permitting access based on your wishes, and not that of a configuration file or default settings list.
Since surfing the Internet is likely to be done for either business or pleasure, Internet Explorer (IE) lockdown is required unless you want to expose yourself to malware and possible browser attacks by going online. Internet Explorer has been updated considerably so that you have many options in which to secure it, surf privately and be alerted to a potential risk so that you can decide whether or not to proceed. In previous versions of Windows, this was mitigated in many ways and with many tools but the core of the problem was how Explorer, IE and how it was closely tied into the base OS, was the real issue. The software was analyzed and completely re-written to include all aspects of security application and an integrated security toolset, such as the Phishing filter. As well, technology advancements when integrated into Microsoft products force advancement in the code and thus more application of security. Today, IE is as secure as any other Web browser available, and even more so when deployed with Group Policy.
Tip:
To keep the risk of attack low, simply show restraint in going to Web servers hosting content known to cause this problems to your system. This includes porn sites, download sites for free software, file sharing or Peer to Peer(P2P) software, public FTP servers, IRC chats and anything else that you do not need to do on your personal computer at home in which you do your banking, social network and/or legitimate online shopping. You can however create a virtual machine and use that for added security, but this solution is not totally securable either. If you limit exposure, you lower the possibility of a being the victim of an attack.
Surfing discipline is important. Aside from being careful, Internet Explorer can be configured in such as way that you cannot do anything without explicitly allowing it. In this article we have covered the balance between security and flexibility and this is one of the best examples to learn from. How do you use the public Internet safely without spending twice the amount of time you do accessing it? Find a happy medium and as mentioned earlier, have a plan to recover from a possible attack.
IE Lockdown steps (such as turning on and configuring the Phishing filter, using InPrivate Browsing, or other security features and functionality will keep you far safer than if you did not use it at all, so its recommended that you make the browser as secure as you can, and then turning off or relaxing security options as you see fit once you are acclimated to how everything works within your current surfing habits. When configuring the Internet Properties of IE, as seen in Figure 5, you can apply security configurations on the Security tab, as well as on just about every other tab shown.

Figure 5: Configuring Internet Properties Security Tab Options
Tip:
In the Internet Properties Security tab, you will find a checkbox within where you can enable Protected Mode. This provides a baseline level of security to your Web browser.
For example, if you select the General tab, you can change your homepage to blank so every time you open your browser, you select where you want to go, not the browser. If hijacked, the current default page could be changed to something else without your knowledge. You can also choose to delete your browsing history whenever you exit IE. You can configure safety zones, restriction lists, filtering, proxy services, advanced protocols and more. Make sure you spend the time learning how your Web browser can be secured, because it may be your first line of defense in a malware attack.
All these tools work together as well – IE can stay locked down, but if something gets through, then the UAC will flag it if its tries to install itself. That is if active memory scanning of the systems RAM didn’t find a TSR, or other malicious process.
Keeping malware off your system is done with many different features of your system aside from AV and Spyware software applications. For example, the UAC (covered earlier) is a prime example of why it’s important to have such a tool. If your visit a malicious Web server to view or download content, scripts in the home page itself can be configured to run applications that will install silently in the background while you use your computer. If anything tries to install itself on Windows 7, the UAC (if configured at its highest level), can protect you from this type of attack.
Other things you can to do prevent malware is to fine tune Windows Firewall and check its logging activity once in awhile and try to familiarize yourself with what is actually running on your system and how much of your systems resources is it using up (launching and staying resident in memory, disk space usage, etc). Using Task Manager is a great way to quickly find many of the items just mentioned. Figure 6 shows what is running on your system. If you look at the Processes tab, you can see what is running in memory and see if its legitimate or not, or if you do in fact want it running in memory, even after you have shut down the application after using it.
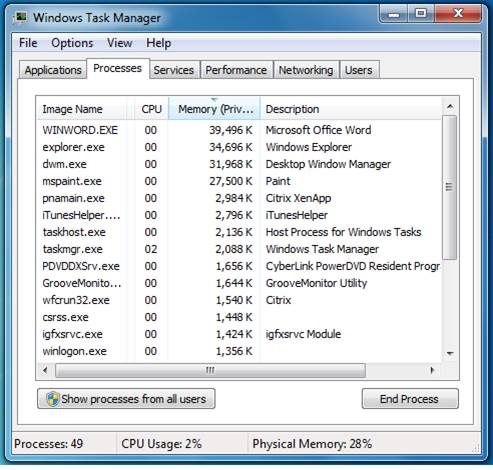
Figure 6: Using Task Manager
You should also check the Event Viewer logs to verify that virus definitions are downloaded, updated and installed as well as the services running as they should and no critical errors are being listed without being attended to. And with all that prevention and protection, you can still get malware on your system which can cause it harm or ruin it (and your data) entirely.
Since malware could still potentially ruin your system even after you completely secured it (as well as updated), you should consider backup. You should always backup your personal data regardless of install on Windows, Linux or Apple systems. You can do this in many ways, such as using the backup utility in Windows 7, using a third party tool, or simply copying your data over to an external hard drive or burned to a CD/DVD-ROM for safekeeping. Obviously, the simple solution is to ignore it and hope for the best. If you rely on your data and or find it important for any reason, you should back it up.
Once your data is backed up and protected, you should backup your system with System Restore as well as consider other disaster recovery methods of getting yourself functional again after an issue. If unfamiliar to you, then you may want to launch and run System Restore and start working with it. This tool is extremely helpful as it will take a snapshot of your current system configuration and back it up in for when needed later. Although it will take up some of your disk space, its well worth it when you consider how helpful it can be in getting you back up and running quickly.
Other malware access points are in Windows Office documents, and can be run as programs used for automation as an example with the intent to infiltrate your system. Macros are useful tools, but by default blocked entirely. The danger with allowing Macros (by default), is that if you receive an email with an Office document delivering a payload, you could accidently open it and inject the malware into your system. There are many infiltrators (and testers) of your security. So much thought goes into the application of security on the base OS, that sometimes little thought is put into the programs that run on it, or the network that the computer connects to. Malware is also injected over the network. Worms travel from Windows share to Windows share, scanners sweep your system in hopes to learn from it and if found, targeted. Trojans are installed to connect to remote servers and report detailed information about your system and much more. Network security – aside from system security, must not be overlooked. Network firewalls block access from attack, routers and switches can be hardened and advanced encryption configuration can be used to create secure connections to remote network safely. Even management over the network needs to be considered. For example, if you did not disable the Telnet service (found in Windows Features) and are actively using it instead of Secure Shell (SSH) as an example, you are using a TCP/IP protocol that can hacked easily. All of the security you created for your systems is now jeopardized because you didn’t catch the packet capture/sniffer application on your network that actively scanned for and captured your clear text/unencrypted password, which happened to also be the same password used for the Windows Administrator default service account. Since you are using the Administrator account and did not practice good password creation and management techniques, you gave away the ‘keys to the castle’. Always consider the network as a potential access point for malware and attacks because it’s often overlooked.
Microsoft Security Essentials (MSE) pack is software freely downloadable from Microsoft (figure 12) which when installed, adds AV scanning software to your system. Made for XP, Vista and Windows 7, the Security Essentials pack is only available from Microsoft if you have a legitimate copy of Windows 7. If you don’t, you can’t download and install it. If you can, install it. You will need to validate your copy of Windows 7 if you did not already do so during the installation process. Once validated, the installation program will check your system to see if other AV programs are running. You will be given a recommendation to only use one form of AV protection, because unfortunately, if you choose to run both you run the risk of them interfering, you have more to manage and monitor (as well as update) and the performance hit you will take because of the over utilization of processing power and memory will be quite high and drastically impact the performance of the system. Once installed, you can now update it as seen in Figure 7.
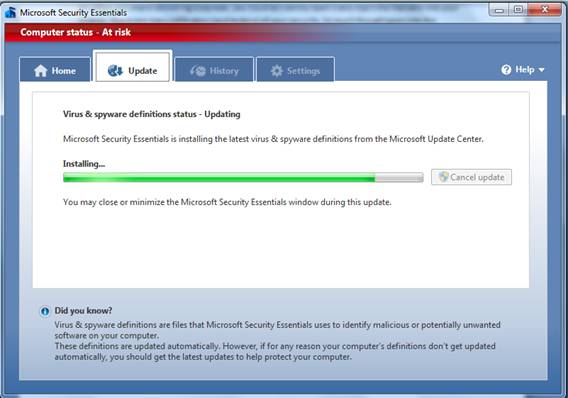
Figure 7: Running Microsoft Security Essentials Updates
Next (Figure 8), you can run a Quick, Full or Custom scan to check your systems for malware. Performing active scans and setting up real-time protection can be done quickly and easily. Simply run MSE and keep it updated for complete AV protection. Another benefit is that it can now be updated with Windows Update.
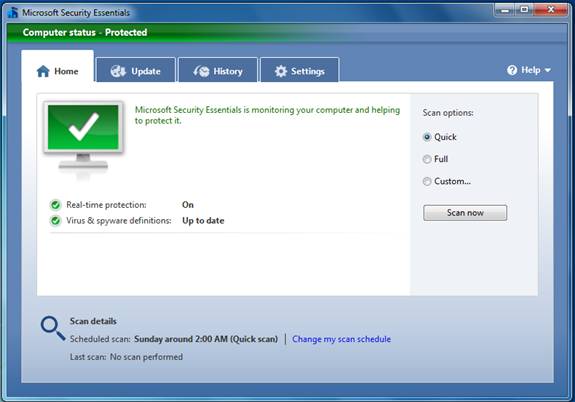
Figure 8: Scanning the System for Malware with Microsoft Security Essentials
Once you have malware protection installed and doing things to actively prevent it, you can continue to harden it, image it, set a restore point or move on to actually making it a production system and using it.
Using a computer on the Internet opens you up to possible attack. Install and use malware and spyware protection and keep it updated. Always consider that one you are protected, you need to keep yourself updated to remain protected and try to discipline your surfing habits.
Tip:
Consider not using items like Desktop Gadgets or any other ‘live’ content because as mentioned before, you open holes in your system by using these, even if they are signed. If you do not need something, or do not use it, a safe practice is to remove it. Not only do you save space and processing power, you lower your risk of attack by limiting the possibility of accidently installing a gadget (or other live content) that is unsigned and potentially dangerous. Anything unsigned, from an un-trusted source or questionable should not be installed.
Summary
A Windows 7 system at home can be locked down and managed easily. You can even configure it securely to be accessed over the Internet from another remote location if left on and active. Windows 7 can be made bullet-proof if you really wanted to harden it to the point complete lockdown. It can still become subject to attack and likely will be if you use the computer on the Internet, as an example. We can plan for this possibility and harden Windows 7 accordingly.
When considering the use of Windows 7, in today’s atmosphere of hack attacks and exploits, security options and flexibility are a top priority when making that decision. Windows 7 is absolutely secure, but it’s not 100%. You have to apply knowledge, other tools and advanced configurations in order to secure all aspects of it and then update and monitor them often. Well worth it if you want to avoid attack. Windows 7 has many security enhancements and can be configured for quick recovery.
As well, basic security principles such as Defense in Depth must be applied in conjunction with other security guidelines and best practices so that not only are you applying security for protection, but multiple layers of it that cover the full architecture and the code that runs it.
We only scratched the surface here, there is so much more to know and learn, but hopefully this articles information shines a light. To learn more, read the material listed in the Reference Links that contain more detailed information as well as free tools, templates and guides. Keep on the lookout for Windows Security Primer part 3 coming soon, stay tuned!
Reference Links
- Windows 7 Security Features
- Windows 7 Security Enhancements
- Windows 7 Security TechNet Blog
- Windows 7 Security Checklist
- Ten Things IT Professionals Should Know About Windows 7
- Microsoft Malicious Software Removal Tool and Safety Assessment Scan
- Windows 7 System Requirements
- Virtual PC and XP-Mode
- Windows 7 Compatibility Center
- Windows Performance and Hardware Compatibility
- AppLocker
- Download and Install Microsoft Security Essentials for Windows 7
- BitLocker Drive Encryption Step-by-Step Guide for Windows 7
- Windows Trusted Platform Module Management Step-by-Step Guide
- Microsoft Security Compliance Management Toolkit
- Windows Server 2008 Security Compliance Management Toolkit
- Enterprise Security Management with Forefront
- Network Access Protection (NAP)
- Cisco Network Admission Control (NAC)
- Introduction to DNSSEC
- DNSSEC Components and Terminology
- The Trustworthy Computing Security Development Lifecycle (SDL)
- Common Criteria Certification: Microsoft Windows Platform Products
- Responding to IT Security Incidents (Incident Response Planning)
- An Introduction to Kernel Patch Protection
- Data Execution Prevention
- Windows Integrity Mechanism Design
- Understanding and Working in Protected Mode Internet Explorer
- Strategies for Managing Malware Risks
- Security Risk Management Guide and Toolkit
- Security Monitoring and Attack Detection
- Windows 7 and Windows Server 2008 R2: Controlling Communication with the Internet
- Leverage Windows 7 Security in Business Environments
- Windows 7 Security in the Enterprise
- Request for Comments (RFC) Search
Articles by Rob Shimonski: on WindowsNetworking.com – on WindowSecurity.com – on VirtualizationAdmin.com
If you would like to read the other parts in this article series please go to:



