If you would like to read the other parts in this article series please go to:
Introduction
Windows 7 is Microsoft’s newest desktop-based client operating system which builds on the strengths and weaknesses of its predecessors, Windows XP and Windows Vista. Every aspect of the base operating system as well as the services it runs and how it manages the applications loaded within it has been reviewed and made more secure if possible. All services have been enhanced and new security options making it more reliable. Aside from basic system enhancements and new services, Windows 7 delivers more security functionality, enhanced auditing and monitoring capabilities and the ability to encrypt remote connections and your data. Windows 7 also has newly developed internal protection enhancements to secure system internals such as Kernel Patch Protection, Service Hardening, Data Execution Prevention, Address Space Layout Randomization, and Mandatory Integrity Levels.
Windows 7 is designed to be used securely. For one, it was developed Microsoft’s Security Development Lifecycle (SDL) framework and engineered to support Common Criteria requirements allowing it to achieve Evaluation Assurance Level (EAL) 4 certification which meets Federal Information Processing Standard (FIPS) #140-2.When used as a stand-alone system, Windows 7 can be secured for personal security. Windows 7 has many helpful security-based toolsets contained within, but it’s only when Windows 7 is used with Windows Server 2008 (R2) and Active Directory, that it turns into a bullet-proof vest. By leveraging additional security from tools such as Group Policy, you can control every aspect of desktop security. If Windows 7 is used mainly for your home office or personal use, it can still be secured to prevent many current methods of hacking and attacking and can be restored quickly if disaster does in fact strike, so although beneficial, Windows 2008 is not completely necessary to apply a high level of security to Windows 7. You should also consider that Windows 7 is inherently secure, but it doesn’t necessarily mean that you should rely on the default configuration without making any adjustments to extend your security coverage. You should also consider that you will eventually be subjected to some form of malware or Internet-based attack when the computer is being utilized on any public network. If a computer is used for any type of public Internet access, your system and the network on which it is connected, becomes opened up to possible attack.
In this article, we will cover the fundamentals you need to know to secure Windows 7 correctly, achieve a baseline level of security, review advanced security configurations and explore some of the lesser known security functionality Windows 7 provides in order to prevent or protect against a possible attack. We will also look at the many ways you can safeguard your data and get back up and running quickly if you do in fact suffer from some form of attack or catastrophic system malfunction you cannot recover from. This article introduces the concepts of security, how to harden Windows 7, how to install and provide security for your running applications, how to manage security on a Windows 7 system and how to prevent the problems caused by malware. This article also covers the process of safeguarding your data, the backup and recovery operating system features, how to restore your operating system to a previous state and ways to recover you data and system state if a disaster does occur. We also cover strategies to do it quickly. Topics are also covered on how to work safely while working online or over the Internet, how to configure biometric control for advanced access control and how Windows 7, and when used with Windows Server 2008 (and Active Directory), how you can securely integrated more options for control, management and monitoring. The goal of this article is to familiarize you with Windows 7 security features, enhancements and their application as well as to give you some insight on how to plan for and apply these security features correctly. The concepts we cover are divided up and organized in a building-block approach.
Caution:
If working in a corporate or other professional environment, do not make adjustments to your company’s computer. Make sure you work within the published security plan (or policy), published best practices, principles and/or guidelines. If you are unfamiliar with security topics and Microsoft products, read the production documentation before applying any changes to your system.
Disaster Recovery
Windows 7 once fully secured should be backed up for quick restoration. You can use imaging software to take a snapshot of your base install for quick reinstallation if needed. If you have to reinstall Windows 7 from scratch, you will also need to take all of the steps already taken to secure it for use. Since this may take a while, you should consider recovery solutions, especially if Windows 7 is used in the enterprise. Corporate solutions provide for imaging. Home users can also create a snapshot of their systems for quick recovery. Either way, you can always use tools such as System Restore, which will allow you to take a snapshot of your system, but that’s only if you can boot your system, or if malware corrupts the use of System Restore, or disables it completely. The only way to recover from a complete disaster is to plan for it to happen and build a plan to recover from it. A simple recovery plan would be, once installation is completed, to then make sure installation disks are secured for later use. If disaster strikes, attempt to fix system and if unfixable, try to recover data and reinstall Windows from installation disks. This process will take a long time and you risk losing your data. A disaster recovery / incident response plan that would include ways to secure your data and offer options for quick recovery and can be followed to secure your data and provide a solution for quick recovery:
- Install Windows 7, applications, toolsets and harden
- Create backup of system (imaging, virtualization, restore point, etc)
- Prepare solution for centralized data backup and recovery / restoration
- Deploy for use, wait for incident or disaster
- Incident occurs, attempt to find root cause and attempt to repair
- A disaster causes a system to be beyond repair / user un-productive
- Quick restoration of base OS with applications, updates via imaging or virtualization
- Reapplication of data (PSTs, etc) via centralized data storage and drive mappings
- User of system back to work quickly without any loss of critical data
All systems will inevitably have some form of failure no matter how much preparation you do. Disk drives fail. Applications fail. Security fails. So, in your security plan you should consider these things and give yourself a chance to recover. You also need to consider how you will recover from any problem with your system. Windows 7 provides a plethora of options to get you back up and running quickly in the event of disaster.
If you need to repair your system files, or restore to a previous copy of the OS, you can do so very easily with Windows 7. Windows 7 provides many tools to help you protect and backup your personal data, as well the OS itself. Using tools such as ERDs, ASRs, Backup and Restore, System Restore, Recovery Console, Safe Mode, Last Known Good Installation option and others have helped administrators and end users navigate disaster since the release of XP. Many of us may have even used a few Sysinternals tools to get a system up and running after suffering from a critical error (BSOD).
Backup and Restore handles Data Backup. The backup of the system itself is done with System Restore (Figure1), where you can configure an OS restoration point for later use.
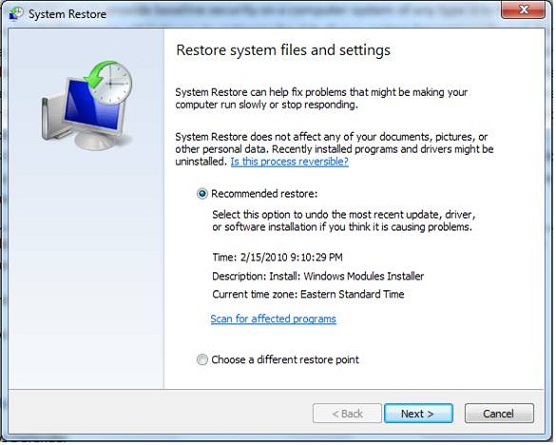
Figure 1: Using System Restore to Create a Restore Point
Warning:
System Restore is used to create a snapshot of your system which is then saved to your hard drive. If you want to go back to that point, you will need to be able to use System Restore again to use it. If System Restore is compromised; you will not be able to use the restore point and may need to rely on imaging, or reinstallation.
You could also rely on imaging tools which can quickly reinstall the OS which may not be repairable. Installing Windows desktops from scratch can be a long process, especially if you are running a system such as XP which is still used (not EOL yet) and supported. There are dozens of hot fixes, updates and service packs that need to be applied, as well as updates for your applications like Microsoft Office. A way to fix the time needed to recover from a virus that leaves your computer inoperable, is to have an image of it that can be applied quickly without having to reinstall from scratch. If System Restore or any other tools (or trick) can’t get you running again, you need to apply a fresh copy of Windows and by not applying the hot fixes, etc – you may fall victim to the same problem that caused your system to fail in the first place.
Data is the most important thing anyone should consider. Personal (or corporate) data needs to be available at all times and never lost. In an enterprise environment, data is normally backed up and sent off site to be brought back and restored if disaster strikes. In the home the same format should be applied. You may or may not want to take a copy of your data offsite, but backing it up so that you can restore it later if needed is the first thing you should consider even before thinking about how to restore Windows 7 in an emergency. The proper design methodology should be to keep a copy of your personal data on an external drive. Connected via USB (or FireWire), your data can be accessed at anytime. You can also mirror a copy to a secondary drive, or even use a tape solution in the home to further safeguard your data. If running a home based business, information is critical so you may want to add a fireproof safe into the mix so that in case something catastrophic happens to your home, your business doesn’t go down with it. So, in general – you need to be prepared. The best way to recover from corruption of data or accidental deletion is to back up your data for safe keeping.
Using centralized solutions is the key to keeping your important data highly available and secure. For example, if you store all of your data on your internal hard disk and never back it up, you stand the chance of losing it the hard drive fails and cannot be repaired. A simple solution would be to use backup options to at minimum, copy it to an external hard drive. This way, you stand a chance. All hard drives are subject to failure so until newer technology catches up to deployed technology, we will see home PCs and corporate arrays filled with drives waiting to fail for quite some time. You have to backup your data or you stand to lose it. Once you have that figured out, then all you need to do is find a way to quickly restore Windows with the least amount of effort and time.
Tip:
It’s always best to plan for the worst case scenario. If you consider that your system will eventually be exposed to something that cannot be repaired, having a good backup of your system and data will be your only hope at restoring functionality. In short, security planning and prevention even if done perfectly, are still not 100% safe so always plan for a way to reapply Windows 7 if you need to.
You could however set up a disaster recovery plan for your OS very easily by considering virtualization. You can download and install Virtual PC, or Enterprise versions of virtualization are available with Microsoft’s Hyper-V. Hyper-V offers a platform for creating, managing and monitoring virtual machines (VMs). If running Windows 7 at home, you can still virtualize your system or resources and take advantage of its benefits within Virtual PC as an example. This way, if you wanted to create a VM as backup, you can. A handy trick which you can apply at home is what enterprises are deploying to change the way they manage their software and system deployment. Using virtualization (Virtual PC/Server or Hyper-V) provides many opportunities to radically change the way you do business at home. If you use a VHD (a virtual hard drive file), then you ‘always’ have a copy of your system ready to go. You can use Disk Management to create a virtual hard drive file of Windows 7 as seen in Figure 2.
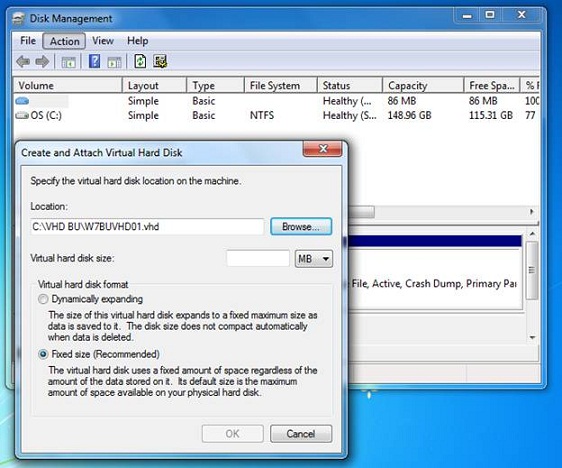
Figure 2: Creating a Virtual Hard Disk with Disk Management
If in the enterprise, systems and resources can be virtualized and data can be highly available on a Storage Area Network (SAN) or Network Attached Storage (NAS) device. This solves the problems associated with long recovery times when disaster strikes. If all files used by the client computer user are found via a mapped drive to a file server cluster, then basically all you need to do is wait for a system hardware failure to happen and bring the system back up on a new computer, or even a kiosk. Most corporate environments with end system users keep spare hardware in stock for just this occasion. If you design and apply the concepts of redundant servers (clustered or load balanced) and apply virtualization to the equation, you could literally have a layout where if a computer failed, within seconds the end user could be back up and running without missing a beat.
In sum, always backup your data and protect your system. Harden it the best you can, but also give yourself the ability to get back up and running, without too much time spent installing software, drivers and reconfiguring your system for use.
Note:
Incorporate a fireproof safe, or an offsite backup solution for your data in case of environmental disasters.
Advanced Security Features
Windows 7 has many other advanced security features you can use, such as advanced encryption options and biometrics. Safe connectivity over unsecure connections must be guaranteed. Access control, theft and possible exploitation of gathered information is something you should plan for when deploying Windows 7, because disasters occur and data is lost. Worse, because of the mobile workforce and mobile laptop used for personal use, security is jeopardized once a user loses their laptop, forgets it somewhere or if it’s stolen. If USB thumb drives are used and lost, how would your data remain secure? To prepare for these and other possibilities, you can deploy the following security features with Windows 7:
Biometrics – Biometrics are used to control access. Most computers (especially the IBM/Lenovo ThinkPad line) come ready with a fingerprint reader. On the horizon of technological advancement is full biometric use for any and all systems, devices of technology in the home, business or elsewhere. Public libraries will forgo a library card in lieu of a retina scan. Abuse of your personal information by those aimed at taking advantage keep this technology at bay for the time being, but soon enough online banking, the application of parental controls for children at home and other personal functions will be done with some form of biometric ID. Windows 7 is biometric ready. Microsoft worked closely with fingerprint reader developers and hardware vendors to make sure that Windows 7 was ready to do what it promised. Identity management is a very important consideration when applying security
BitLocker Drive Encryption (BDE) – BitLocker (and BitLocker to Go), are used to provide security to data contained on internal and external hard drive systems. With Windows 7, you can use both versions of BitLocker to secure data on internal hard drives, external drives, thumb drives and other forms of external/removable storage. BDE can protect data stored on these drives by requiring credentials to access it and also utilized TPM.
Microsoft’s Trusted Platform Module (TPM) Management feature is only available on TPM compliant hardware. When complaint, Windows Vista/7 and Windows Server 2008 can utilize advanced security features and functionality. Microsoft’s Trusted Platform Module (TPM) Management is a new feature available in Windows Vista/7 and Microsoft Windows Server 2008. Its primary function is to allow Windows systems to utilize advanced processing and encryption functions at the hardware level. As mentioned earlier within this article, some of these advanced features require advanced (and compatible) hardware in order to be used. If you try to use a feature and find it grayed out or unusable, it’s likely because your hardware is not complaint with the feature, or it is possible you are using the wrong version of Windows 7 and the feature it not available.
Tip:
TPM can be configured and managed through the computers BIOS and the MMC snap-in we installed earlier.
You can also securely connect to remote resources with Windows 7 by configuring IPsec/VPN connections. A Virtual Private Network (VPN) is a term used to describe the security applied to keep you safe from attack. You are still making a connection over an unsecure public network (Internet), but because a tunnel of encryption is applied to keep the connection private, you can do so safely. You can create a new VPN connection quickly by going to the Start menu, typing VPN and follow the Control Panel link for creating a new VPN connection as seen in Figure 3.
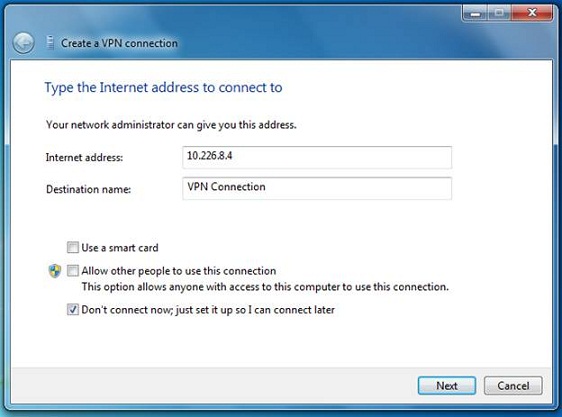
Figure 3: Configure a VPN Connection
You can create connections with other systems using advanced protocols that provide an extremely high level of security through encryption algorithms. This usually requires a CPU processor with the ability to provide hardware-based encryption. This removes the need for the base OS to process it, which would tax system resources considerably. VPNs can be used to make secure connections to other systems.
Note:
If managing remote Microsoft systems, you can use Remote Desktop Connection (RDC). If using Telnet as a remote connection tool for Unix systems and Cisco network devices (as examples), you should consider disabling this service (disabled by default), and using Secure Shell (SSH).
You can also create manageable tunnel connections with the IPsec protocol and manage them with the MMC console snap-in or Windows Firewall. There are even features within the console that allow you to manage and troubleshoot IPsec connections such as mismatched keys, problems with security association (SA), issues with encryption sets, proposals, lifetime settings and other ISAKMP based configuration issues. This can be managed in the Windows Firewall, Advanced Features.
Once access control and data recovery options have been selected and you can securely connect to network resources via encrypted tunnels, what if you wanted to share resources securely over a home-based or corporate network? Windows 7 provides a new function called HomeGroup, found in the Control Panel. You can configure it to make changes to your system in order to link other computers on your home network securely in order to share resources as seen in Figure 4.

Figure 4: Configure Windows 7 HomeGroup
Windows 7 can be configured to share resources with other systems on your home network securely. HomeGroup when configured can provide basic security for accessing, using and sharing data. For example, if you configure two computers on your home computer and one of them uses a local printer, HomeGroup allows you to share that as a resource so all systems can use it. You can also password protect it and specify who can use it and who cannot. With Windows 7, this replaces the use of the Workgroup function. Not all versions of Windows 7 allow you to create a HomeGroup. Any version of Windows 7 can join a HomeGroup, but you can only create a HomeGroup in Home Premium, Professional, or Ultimate editions.
Of course, Windows 7 can best be leveraged (and secured) by using it with Windows Server 2008 in an Active Directory environment. Running a enterprise-class operating system opens the doors to full lockdown and monitoring capabilities. For example, Web surfing can be controlled and monitored with Active Directory, Group Policy, specialized lockdown templates and kits and other tools like proxy servers. A user could log in to the directory (Domain) and be completely managed and monitored. Anything the end user does can be logged and recorded. Any tool or service Windows provides can be customized, altered or removed entirely.
With Forefront products, every aspect of computer usage, identity verification, logging and monitoring can be covered and managed in a centralized console. You can then leverage Windows Server even further by integrating with Forefront. Forefront is a new line of Microsoft software that aims to provide for a full security experience across the enterprise. It has offerings for servers, desktops, access control and specialized solutions for SharePoint, amongst others. When running Windows clients in a business environment, this solution can provide for granular application of security settings, as well as more options for centralized management and monitoring.
In some cases, you may have to run Active Directory. For example, what if you by law had to audit all access to corporate resources and retain a copy of all employee email? When working in the enterprise you are more than likely going to be confronted with being audited – especially if you are a publicly-traded company. Data ‘must’ be safeguarded and recoverable. Certain levels of security must be met and this is done primarily with government legislation. (Sarbanes Oxley and HIPPA).
In an enterprise, you will be able to provide more security to your workstations or desktops simply by using Active Directory directory services (AD DS), a domain model, Group Policy and many other tools to centralize and control your security functions. Kerberos is leveraged to keep all transactions secure through tickets. This creates a secure foundation in which to build upon. If you build on that foundation, the opportunities to apply advanced levels of control are endless.
Windows 7 can be managed as a client and when doing so in a domain model, Active Directory provides security by integrating all services and access control into it and it comes with many options for secure deployment strategies, such as installing only the ‘core’ of what is needed keeping a limited footprint open for attack, or install and configure and endless amount of services all equally securable through options and toolkits. Also, Group Policy when applied correctly can help you deploy many of the features we have discussed, for example, you can integrate BitLocker into AD and then deploy with a policy. You can control Internet Explorer as well, limiting access or blocking it entirely with configured lists of known malware sites and blacklisted networks.
You can also deploy other advanced Windows 7 security features to tighten security further such as:
Advanced DNS Security – Domain Name System Security (DNSSec) extensions support with Windows 7 brings a new level of security to name resolution security. Because DNS is so important and most times, the backbone of most solutions, it’s also the target of many attacks, and relies on security enhancements to stay operational and exploit-free. RFCs 4033, 4034 and 4035 list out new standards in achieving DNS security and Microsoft has complied with Windows 7.
DirectAccess – DirectAccess is a Windows 7 feature that allows the mobile workforce the ability to work remotely over the Internet without the use of VPN technology. DirectAccess is tied closely into your enterprises resources allowing you to securely access them remotely. It also allows mobile users the ability to receive remote support from the IT staff. DirectAccess allows you to manage computers remotely and update them via Group Policy. DirectAccess uses IPv6 over IPsec to encrypt traffic over the public Internet.
AppLocker – When working with the Local Security Policy Editor (or Group Policy), you can now configure AppLocker, which is a Windows 7 feature that controls your installed applications. When configured, you can lock down, restrict and control your desktop applications. It does this with a rule set. You can configure rules for application control, how updates are managed and more. Figure 5 shows the Local Security Policy editor in Windows 7 where you can configure application security with AppLocker.
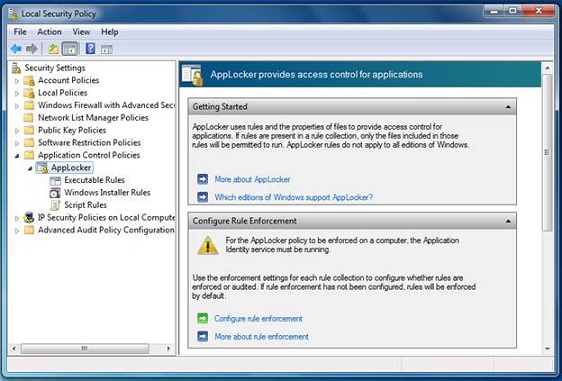
Figure 5: Using AppLocker to Secure your Applications
Lastly, you should always consider your network. Wireless systems are hotbeds for intrusion and penetration. Routers, switches and any other managed devices on your network are prone to attack if not hardened as well. This is why the concept of Defense in Depth is critical to consider – you need to cover every entry point and possible exploit area.
Tip:
With Windows Server 2008 R2 and third party vendor products such as Cisco Systems, you can deploy NAP/NAC to secure and enforce policy for access control. With Microsoft, the Network Access Protection (NAP) infrastructure consists of NAP clients and Health Registration Authority (HRA) servers and can be controlled further via a Network Policy Server (NPS). NAP will control client access via a preconfigured compliance policy. If the client does not meet policy requirements, it can dynamically be forced to comply. It can also be configured to block or deny access. Cisco uses similar technology called Network Admission Control (NAC). When used together in Microsoft/Cisco environments, you can create a high level of security and control.
Summary
A Windows 7 system at home can be locked down and managed easily. You can even configure it securely to be accessed over the Internet from another remote location if left on and active. Windows 7 can be made bullet-proof if you really wanted to harden it to the point of complete lockdown. It can still become subject to attack and likely will be if you use the computer on the Internet, as an example. We can plan for this possibility and harden Windows 7 accordingly.
When considering the use of Windows 7, in today’s atmosphere of hack attacks and exploits, security options and flexibility are a top priority when making that decision. Windows 7 is absolutely secure, but it’s not 100%. You have to apply knowledge, other tools and advanced configurations in order to secure all aspects of it and then update and monitor them often. Well worth it if you want to avoid attack. Windows 7 has many security enhancements and can be configured for quick recovery.
As well, basic security principles such as Defense in Depth must be applied in conjunction with other security guidelines and best practices so that not only are you applying security for protection, but multiple layers of it that cover the full architecture and the code that runs it.
We only scratched the surface here, there is so much more to know and learn, but hopefully this articles information shines a light. To learn more, read the material listed in the Reference Links that contain more detailed information as well as free tools, templates and guides. Make sure you check out Windows 7 Security Primer parts 1 and 2 for full coverage.
Reference Links
- Windows 7 Security Features
- Windows 7 Security Enhancements
- Windows 7 Security TechNet Blog
- Windows 7 Security Checklist
- Ten Things IT Professionals Should Know About Windows 7
- Microsoft Malicious Software Removal Tool and Safety Assessment Scan
- Windows 7 System Requirements
- Virtual PC and XP-Mode
- Windows 7 Compatibility Center
- Windows Performance and Hardware Compatibility
- AppLocker
- Download and Install Microsoft Security Essentials for Windows 7
- BitLocker Drive Encryption Step-by-Step Guide for Windows 7
- Windows Trusted Platform Module Management Step-by-Step Guide
- Microsoft Security Compliance Management Toolkit
- Windows Server 2008 Security Compliance Management Toolkit
- Enterprise Security Management with Forefront
- Network Access Protection (NAP)
- Cisco Network Admission Control (NAC)
- Introduction to DNSSEC
- DNSSEC Components and Terminology
- The Trustworthy Computing Security Development Lifecycle (SDL)
- Common Criteria Certification: Microsoft Windows Platform Products
- Responding to IT Security Incidents (Incident Response Planning)
- An Introduction to Kernel Patch Protection
- Data Execution Prevention
- Windows Integrity Mechanism Design
- Understanding and Working in Protected Mode Internet Explorer
- Strategies for Managing Malware Risks
- Security Risk Management Guide and Toolkit
- Security Monitoring and Attack Detection
- Windows 7 and Windows Server 2008 R2: Controlling Communication with the Internet
- Leverage Windows 7 Security in Business Environments
- Windows 7 Security in the Enterprise
- Request for Comments (RFC) Search
Articles by Rob Shimonski: on WindowsNetworking.com – on WindowSecurity.com – on VirtualizationAdmin.com
If you would like to read the other parts in this article series please go to:



