One of the biggest security issues you may have seen with older versions of Windows based servers is that when you assign permissions, you may accident be assigning too much because of a design flaw with anonymous access. When you have members of the Anonymous Logon group, they were also granted access to data because when an administrator thinks of ‘anonymous’, the administrator may also think this implies non-authentication. When you think of the Everyone Group, you may imply authentication of users. By design (and flaw), anonymous users where also part of the Everyone Group.
In Windows .NET Server, the “Anonymous” Logon user group is not a member of the “Everyone” group. This is a good thing, as you will find that assigning everything yourself can be a chore at times, but its safe. If you do however need to grant these rights, then you can by going to the Local Security Policy MMC be going to:
Start => Programs => Administrative Tools => Local Security Policy
Once opened you will see the MMC as seen here:

If you need to grant access to the Anonymous logon group to the Everyone group (perhaps you upgraded a server and now lost access to it anonymously) you should then explicitly add the permission back to the Anonymous Logon security group. To do this, do to the following:
You MMC should still be open (figure 1)
In the left hand navigation pane of the MMC, navigate down to the Security Options folder.
Change the security setting as follows => Network access: Let Everyone permissions apply to anonymous users.
Double click it and enable it.
Now you will have the unsecure permissions back, but if after an upgrade you lost this service, you can now function again until you can plan to protect this at another time. Group Policy can also be used in the same manner.
Everyone Group
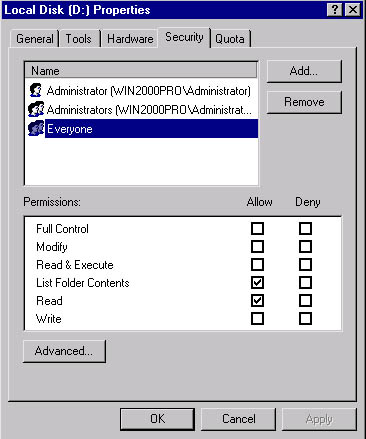
Another difference is the Everyone Group that you can see in Windows 2000 to Windows .NET Server. Take a look at the Everyone Group for a Windows 2000 machine:
Now, when you look at a default installation of Windows .NET Server, you can see that there is a slight difference between the Everyone group:
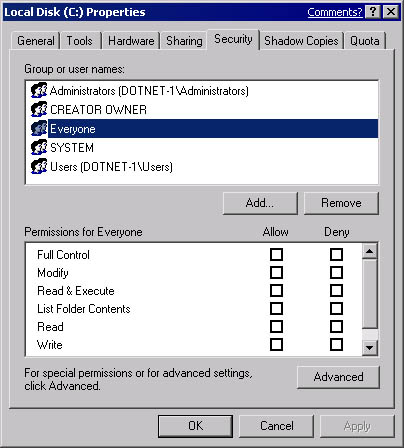
Looks the same right? But its not. Scroll down a little and you will see a permission at the bottom of the list:

Special permissions are configured. Lets click on the advanced button and take a look at what exactly they are:

When you click on the Advanced button, specify the Group you would like to check advanced permissions on by entering the object name (everyone) and clicking OK.
Once you click the OK button, you can see the Effective permissions tab and see that the following permissions are allowed:
* Traverse Folder
* List Folder / Read Data
* Read Attributes
* Read Extended Attributes
* Read Permissions

In this article we looked at the fundamental differences in the Everyone Group from Windows 2000 to the new Windows .NET Server. You can see that security is taken in a more serious manner, and more so, you can see that permissions assigned can be more granular in nature. You have more flexibility and you are not exposed to possible threats from Anonymous users to your servers.



