Wireless Attacks Primer

“For a complete guide to security, check out ‘Security+ Study Guide and DVD Training System’ from Amazon.com“
Rob Shimonski would like to thank Martin Grasdal (contibuting author on the Security+ book) for original content creation. Martin has by far created one of the most outstanding and complete chapters on Wireless fundamentals and security in the Security+ book that you will find anywhere.
Common Exploits of Wireless Networks
In general, attacks on wireless networks fall into four basic categories: passive attacks, active attacks, man-in-the middle attacks, and jamming attacks. Lets review what these attacks mean on a wireless network.
Passive Attacks on Wireless Networks
A passive attack occurs when someone listens to or eavesdrops on network traffic. Armed with a wireless network adaptor that supports promiscuous mode, the eavesdropper can capture network traffic for analysis using easily available tools, such as Network Monitor in Microsoft products, or TCPdump in Linux-based products, or AirSnort. A passive attack on a wireless network may not be malicious in nature. In fact, many in the wardriving community claim their wardriving activities are benign or “educational” in nature. It is worth noting that wardriving, looking for and detecting wireless traffic, is probably not illegal, even though propagandistic claims to the contrary are often made. Wireless communication takes place on unlicensed public frequencies-any one can use these frequencies. This makes protecting a wireless network from passive attacks more difficult.
Passive attacks are by their very nature difficult to detect. If an administrator is using DHCP on the wireless network (this is not recommended), he or she might notice that an authorized MAC address has acquired an IP address in the DHCP server logs. Then again, he or she might not. Perhaps the administrator notices a suspicious-looking car sporting an antenna out of one of its windows. If the car is parked on private property, the driver could be asked to move or possibly charged with trespassing. But, the legal response is severely limited. Only if it could be determined the wardriver was actively attempting to crack any encryption used on the network or otherwise interfering or analyzing wireless traffic with malicious intent would he or she be susceptible to being charged with a data-related crime, but this would depend on the country or state in which the activity took place.
Passive attacks on wireless networks are extremely common, almost to the point of being ubiquitous. Detecting and reporting on wireless networks has become a popular hobby for many wireless wardriving enthusiasts. In fact, this activity is so popular that a new term, “war plugging”, has emerged to describe the behavior of people who actually wish to advertise both the availability of an AP and the services they offer by configuring their SSIDs with text like, “Get_food_here”!
Most of these wardriving enthusiasts use a popular freeware program, called Netstumbler, which is available from www.netstumbler.com. The Netstumbler program works primarily with wireless network adaptors that use the Hermes chipset because of its ability to detect multiple APs that are within range and WEP, among other features (a list of supported adaptors is available at the Netstumber web site). The most common card that uses the Hermes chipset for use with Netstumbler is the ORiNOCO gold card. Another advantage of the ORiNOCO card is that it supports the addition of an external antenna, which can greatly extend the range of a wireless network to many orders of magnitude, depending on the antenna. A disadvantage of the Hermes chipset is that it doesn’t support promiscuous mode, so it cannot be used to sniff network traffic. For that purpose, you need a wireless network adaptor that supports the PRISM2 chipset. The majority of wireless network adaptors targeted for the consumer market use this chipset, for example, the Linksys WPC network adaptors. Sophisticated wardrivers will arm themselves with both types of cards, one for discovering wireless networks and another for capturing the traffic.
In spite of the fact that Netstumbler is free, it is a sophisticated and feature-rich product that is excellent for performing wireless site surveys, whether for legitimate purposes or not. Not only can it provide detailed information on the wireless networks it detects, it can be used in combination with a GPS to provide exact details on the latitude and longitude of the detected wireless networks. Figure 1 below shows the interface of a typical Netstumbler session.
Discovering Wireless LANs Using Netstumbler
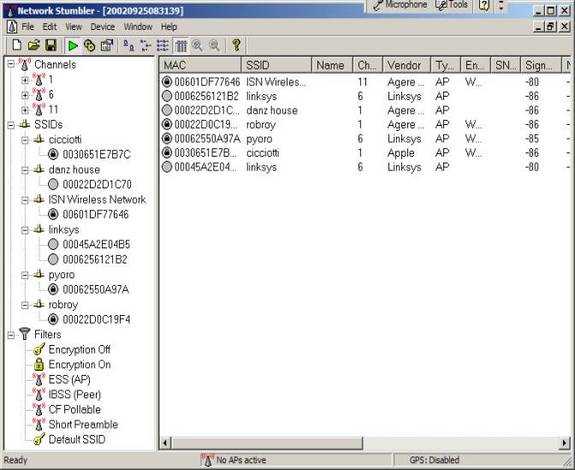
As you can see from the above figure, Netstumbler displays information on the Service Set Identifier (SSID), the channel, and the manufacturer of the wireless AP. There are a few things that are particularly noteworthy about this session. The first is that a couple of APs are still configured with the default SSID supplied by the manufacturer, which should always be changed to a non-default value upon set up and configuration. Another is that at least one network uses a SSID that may provide a clue about the entity that has implemented it; again this is not a good practice when configuring SSIDs. Finally, we can see what networks have implemented WEP.
If the network administrator has been kind enough to provide a clue about the company in the SSID or is not encrypting traffic with WEP, the potential eavesdropper’s job has been made a lot easier. Using a tool such as Netstumbler is only a preliminary step for the attacker. After discovering the SSID and other information, the attacker can connect to the wireless network to sniff and capture network traffic. This network traffic can reveal a lot of information about the network and the company that uses it. For example, looking at the network traffic, the attacker can determine what DNS servers are being used, the default home pages configured on browsers, network names, logon traffic, and so on. The attacker can use this information to determine if the network is of sufficient interest to proceed further with other attacks. Furthermore, if the network is using WEP, the attacker can, given enough time, capture a sufficient amount of traffic to crack the encryption.
Netstumbler works on networks that are configured as open systems. This means that the wireless network indicates that it exists and will respond with the value of its SSID to other wireless devices when they send out a radio beacon with an “empty set” SSID. This does not mean, however, that wireless network can be easily compromised, if other security measures have been implemented. To defend against the use of Netstumbler and other programs to detect a wireless network easily, administrators should configure the wireless network as a closed system. This means that the AP will not respond to “empty set” SSID beacons and will consequently be “invisible” to programs such as Netstumbler which rely on this technique to discover wireless networks. However, it is still possible to capture the “raw” 802.11b frames and decode them through the use of programs such as Ethereal and WildPacket’s AiroPeek to determine this information. As well, RF spectrum analyzers can be used to discover the presence of wireless networks. Notwithstanding this weakness of closed systems, you should choose wireless APs that support this feature.
We should note that on the wireless side, APs are half-duplex devices and work just like other half-duplex devices, such as hubs and repeaters. This means that all the devices on the network can potentially see all the traffic from other devices. The only defense against sniffing on a wireless network is to encrypt Layer 2 and higher traffic whenever possible through the use of WEP, VPNs, SSL, Secure Shell (SSH), Secure Copy (SCP), and so on. Some of these defensive strategies will be more effective than others, depending on the circumstances.
Active Attacks on Wireless Networks
Once an attacker has gained sufficient information from the passive attack, the hacker can then launch an active attack against the network. There are a potentially large number of active attacks that a hacker can launch against a wireless network. For the most part, these attacks are identical to the kinds of active attacks that are encountered on wired networks. These include, but are not limited to, unauthorized access, spoofing, and Denial of Service (DoS) and Flooding attacks, as well as the introduction of Malware and the theft of devices. With the rise in popularity of wireless networks, new variations of traditional attacks specific to wireless networks have emerged along with specific terms to describe them, such as “drive-by spamming” in which a spammer sends out tens or hundreds of thousands of spam messages using a compromised wireless network.
Because of the nature of wireless networks and the weaknesses of WEP, unauthorized access and spoofing are the most common threats to a wireless networks. Spoofing occurs when an attacker is able to use an unauthorized station to impersonate an authorized station on a wireless network. A common way to protect a wireless network against unauthorized access is to use MAC filtering to allow only clients that possess valid MAC addresses access to the wireless network. The list of allowable MAC addresses can be configured on the AP, or it may be configured on a RADIUS server that the AP communicates with. However, regardless of the technique used to implement MAC filtering, it is a relatively easy matter to change the MAC address of a wireless device through software to impersonate a valid station. In Windows, this is accomplished with a simple edit of the registry, in UNIX through a root shell command. MAC addresses are sent in the clear on wireless networks, so it is also a relatively easy matter to discover authorized addresses.
WEP can be implemented to provide more protection against authentication spoofing through the use of Shared Key authentication. However, as we discussed earlier, Shared Key authentication creates an additional vulnerability. Because Shared Key authentication makes visible both a plaintext challenge and the resulting ciphertext version of it, it is possible to use this information to spoof authentication to a closed network.
Once the attacker has authenticated and associated with the wireless network, he or she can then run port scans, use special tools to dump user lists and passwords, impersonate users, connect to shares, and, in general, create havoc on the network through DoS and Flooding attacks. These DoS attacks can be traditional in nature, such as a ping flood, SYN, fragment, or Distrbuted DoS (DDoS) attacks, or they can be specific to wireless networks through the placement and use of Rogue Access Points to prevent wireless traffic from being forwarded properly.
Man-in-the-Middle Attacks on Wireless Networks
Placing a rogue access point within range of wireless stations is wireless-specific variation of a man-in-the-middle attack. If the attacker knows the SSID in use by the network (which as we have seen is easily discoverable) and the rogue AP has enough strength, wireless users will have no way of knowing that they are connecting to an unauthorized AP. Using a rogue AP, an attacker can gain valuable information about the wireless network, such as authentication requests, the secret key that may be in use, and so on. Often, the attacker will set up a laptop with two wireless adaptors, in which one card is used by the rogue AP and the other is used to forward requests through a wireless bridge to the legitimate AP. With a sufficiently strong antenna, the rogue AP does not have to be located in close proximity to the legitimate AP. So, for example, the attacker can run the rogue AP from a car or van parked some distance away from the building. However, it is also common to set up hidden rogue APs (under desks, in closets, etc.) close to and within the same physical area as the legitimate AP. Because of their undetectable nature, the only defense against rogue APs is vigilance through frequent site surveys using tools such as Netstumbler and AiroPeek, and physical security.
Frequent site surveys also have the advantage of uncovering the unauthorized APs that company staff may have set up in their own work areas, thereby compromising the entire network and completely undoing the hard work that went into securing the network in the first place. Even if your company does not use or plan to use a wireless network, you should consider doing regular wireless site surveys to see if someone has violated your company security policy by placing an unauthorized AP on the network, regardless of their intent.
Jamming Attacks on Wireless Networks
Jamming is a special kind of DoS attack specific to wireless networks. Jamming occurs when spurious RF frequencies interfere with the operation of the wireless network. In some cases, the jamming is not malicious and is caused by the presence of other devices, such as cordless phones, that operate in the same frequency as the wireless network. In a case like this, the administrator must devise and implement policies regarding the use of these devices, such a banning the use of Bluetooth devices, or choose wireless hardware that uses different frequencies. Intentional and malicious jamming occurs when an attacker analyzes the spectrum being used by wireless networks and then transmits a powerful signal to interfere with communication on the discovered frequencies. Fortunately, this kind of attack is not very common because of the expense of acquiring hardware capable of launching jamming attacks. Plus, jamming a network represents a kind of pyrrhic victory for the attacker-a lot of time and effort expending merely to disable communications for a while.
Rob Shimonski would like to thank Martin Grasdal (contibuting author on the Security+ book) for original content creation. Martin has by far created one of the most outstanding and complete chapters on Wireless fundamentals and security in the Security+ book that you will find anywhere.



