Active Directory is one of the most important services in your Windows network and is a requirement for most of Microsoft products, such as Exchange, Skype for Business, System Center, and other related services.
Active Directory has several components worth exploring, so let’s take a look at some of those components and provide some guidance on how simple changes can improve your administrative user experience. At the same time, these changes will reduce operational costs to maintain the Active Directory by creating consistency among all servers in the same domain.
We will be working on some settings and features that by default are not configured. The services and components that we will looking at are:
- DNS
- Windows Time
- Directory Services Restore Mode
- Group Policies
- Recycle Bin
- Best Practices Analyzer
Managing DNS
DNS is the core service of Active Directory and requires special attention from a network administrator. The best practice is to make sure that all your endpoint devices (workstations, mobile devices, laptops, network devices, etc.) are using the local domain controllers on their DNS client configuration (at the adapter level).
Domain controllers are responsible to resolve names on the Internet to clients. There are several ways to configure them to help on the DNS resolution and are as follows:
- Use Internet root hints and the domain controllers will cache the queries and be responsible for all recursive queries
- Use DNS resolvers on the Internet to speed up the name resolution. This could be Google DNS (8.8.8.8 or 8.8.4.4) or even your ISP DNS resolvers.
- Use paid DNS resolvers that can help on the security side (for example, they do not allow clients to go to suspicious sites)
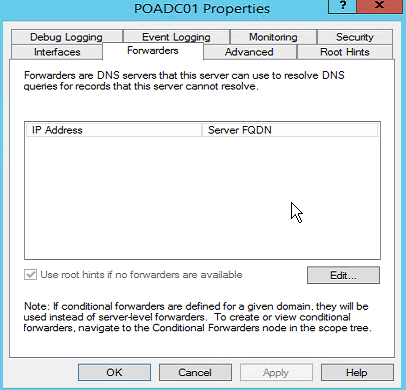
Either method requires the administrator to configure the Forwarders tab in the server’s properties when using the DNS Manager on new domain controllers. By default, all new domain controllers will have another domain controller added to the Forwarders tab.
If you are using root hints, just remove all entries that are listed, and if you want to use Google DNS or paid DNS resolvers, add them to the list.
Managing Windows Time
Active Directory relies on time, and all clients, servers, and domain controllers should have their time synchronized up to the second. The recommendation is to use the physical domain controller located on the main site of the domain/forest to synchronize its clock with an atomic clock on the Internet using NTP protocol, and that server should hold the PDC (primary domain controller) role.
Before applying the changes below, make sure to talk to your firewall administrator and open up the port 123 (TCP/UDP) from your domain controller to the Internet.
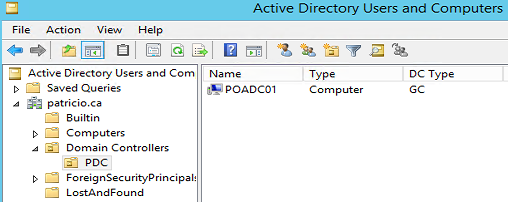
The first step is to create an Organization Unit (OU) underneath Domain Controllers and move the Domain Controller that will hold the PDC FSMO (Flexible Single Master Operation) role. Pictured below is a new PDC OU to manage Windows time to the PDC emulator role.
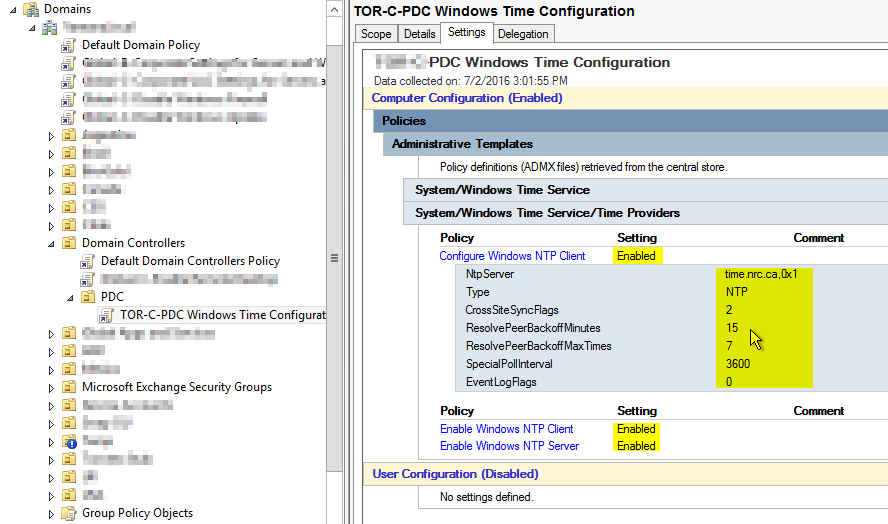
The second step is to create a Group Policy (Computer Configuration > Policies > Administrative Templates > System > Windows Time Service > Time Providers) and configure the settings as shown in the image below. In this article, we are using a NTP server in Canada (time.nrc.ca), but look for a sufficient NTP server in your country/region.
A good way to test after having the Group Policy applied on the domain controller that belongs to the PDC Organization Unit is using the w32tm /query /status. The expected result is to see NTP Server being listed on the Source: line, as depicted in the image below.

Managing the Directory Services Restore Mode (DSRM) password
During the domain controller deployment process, the administrator has to define the DSRM password manually. However, we want to keep consistency, and that becomes key when you have several sites all over the place. Also, you don’t want to share that password with different team members when the deployment is decentralized.
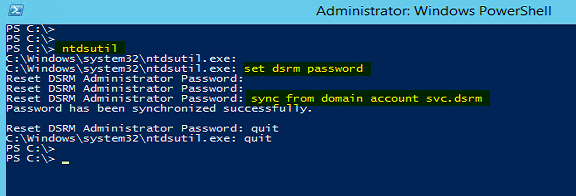
A good way to achieve that is creating an account in Active Directory and defining a strong password. In our scenario, we will create one account called svc.dsrm. It is a simple account without any special configuration.
In order to keep consistency and leave the password secure at the same time, for every new domain controller in your environment, add the following steps and you will have a consistent password on all domain controllers.
Note: If you want to change the DSRM password later on, the proper method is to change the Active Directory account password and execute the same procedure on all servers again.
Ntdsutil
Set dsrm password
Sync from domain account svc.dsrm
Managing Group Policies
Using Group Policies, the administrator is able to manage settings from a central location for users and computer objects in Active Directory.
By default, all policy definitions (all settings that are exposed when using Group Policy Management Editor comes from ADMX files) are located on the local computer, which means that consistency is not the rule, especially if an administrator adds new ADMX files on any given domain controller.
When we edit any Group Policy and expand Administrative Templates, the Group Policy Management Editor will inform you where the settings are coming from. In the image below, we can see that is coming from the Local Computer.

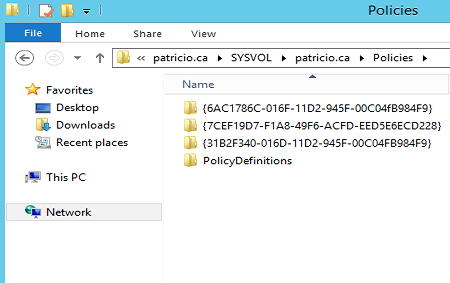
In order to keep consistency among all domain controllers, we can configure a central repository which will be automatically replicated in the Active Directory domain. The process is straightforward. The first step is to create a folder called PolicyDefinitions under \\patricio.ca\SYSVOL\patricio.ca\Policies (replace patricio.ca for your domain name) as shown in the image below.
The final step is to copy the local files (C:\Windows\PolicyDefinitions) from a domain controller to the new location. From that point on, the administrator has only the PolicyDefinitions folder to manage updates and new admx files will be available on all domain controllers automatically.
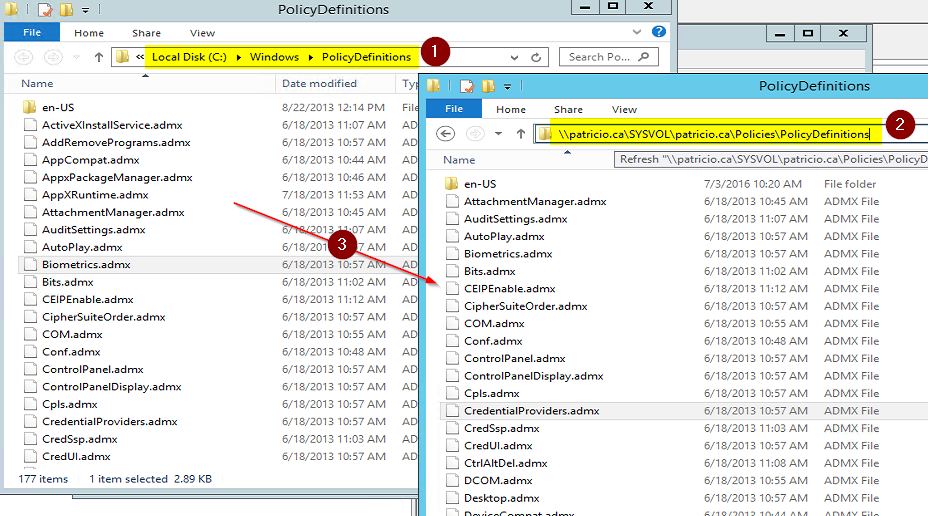
In order to validate the change, close any instances of Group Policy Management Editor, and then edit any existent Group Policy. At this time, when the Administrative Templates is expanded, the message should be Policy Definitions (ADMX files) retrieved from the central store.

Managing your Recycle Bin
By default, the Recycle Bin feature is disabled on new Active Directory environments, and it requires at least Windows Server 2008 R2 forest functional level. However, the Recycle Bin feature helps a lot because an administrator is able to restore users and group memberships, and it has an extremely easy to use graphical user interface.
In order to enable this feature, open Active Directory Administrative Center, select the domain from the left, and then click on Enable Recycle Bin. A confirmation dialog box will be displayed. Confirm by clicking on OK and then another dialog box requesting a refresh will show up; click on OK.
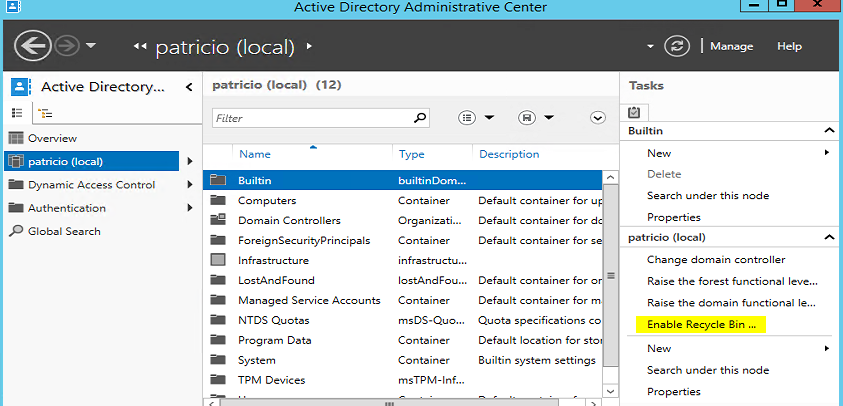
After performing a refresh on the Active Directory Administrative Center, a new container called Deleted Objects will be available. Click on it and all deleted objects will be available (however, note that there is a default soft limit of 20,000 objects being listed). The process to perform a restore is straightforward. Just right-click on the desired object and click on Restore.

Managing Best Practices Analyzer (BPA)
The Best Practices Analyzer has existed in the Exchange universe for a long time, and it has been introduced in Active Directory during the Windows Server 2008 release and remained in Windows Server 2012 R2.
In order to check your environment, open Server Manager, click on AD DS (Item 1), and scroll down to Best Practices Analyzer section (Item 2), click on Tasks (Item 3), and then Start BPA Scan and wait the process to complete. The results for Active Directory will be listed on the same section (Item 4).

So how’s that for a kickass Windows Active Directory configuration? We thought so too. By making minor tweaks, we worked on several components of Active Directory that will keep consistency among several domain controllers, and at the same time reducing complexity when managing Active Directory domain controllers.



Instead of moving the domain controller with the PDC role to a new OU (which Microsoft RAPs will flag), why not use security filtering to target the DC? Or better yet, use WMI filtering to dynamically target the PDC Emulator role, and if the roles get transferred or seized the GPO is applied to the new PDC.
Hi Marty,
Thanks for the feedback. You brought up a really good point.
Personally, I won’t be worried about the RAP because the DC is still on the same structure, but your suggestion is more elegant for sure. I will blog a post with your suggestion here at Techgenix.com (can I share your name on the post?)
Cheers,
Anderson Patricio (@apatricio on Twitter)