Creating URL and Domain Deny Lists using ISA Server 2004
By Greg Mulholland
|
Have Questions about the article? Go to: |
One of the great benefits of the ISA firewall in both the 2000 and 2004 versions is its ability to block access to any specific Web URL or domain or indeed a compiled list of such.
It must be said that whilst this is not cutting edge technology, it definitely has its place in the workplace and should be taken into serious consideration by all firewall and network administrators. Having said this, one of the drawbacks of such lists is that they are “static”. By this I mean that the ability of the Web Administrators of such sites to move within domains is both quiet simple and regular. Given that I block www.porn.com today, the same site might pr0n up at www.notporn.com the next day or week. So these lists should only be used as a starting point and not a definitive list.
There are several lists available but because of the amount of time it would take to compile a useful list I will give you a few I have seen and used. Also note that some of the sites may overlap in both of the lists.
First is Steve Moffat’s comprehensive list of sites:
Look under the Destinations Sets menu. Available for ISA Server 2000 and 2004
Also, check out Rich Krol’s blocklists:
http://www.tacteam.net/isaserverorg/download/blocklists.zip which work with ISA Server 2004
Lets take the URL Set .xml file from Rich Krol’s set and demonstrate how we would implement this.
First of all we need to create, or in this case, import a new Network Object for the URL Set. To do this we select the Toolbox and then the Network Objects tab. We see we can create a number of Network Objects, however we want to create a URL Set on this occasion. If we right click on URL Sets then we can choose to Import a predefined list.

Finding the extracted files which we downloaded previously we choose to import the blocklist.xml file.
Note:
The BNSD.xml file is a Domain Name Set which is not part of this current procedure.
The import is successful!
Step one done. We have successfully imported the list of blocked URL’s. To check this you should see an entry under the URL Sets in the Toolbox.
|
Have Questions about the article? Go to: |
But that’s not all, We need to tell ISA that we want to specifically block that list of URL’s. So we create a new Access Rule.
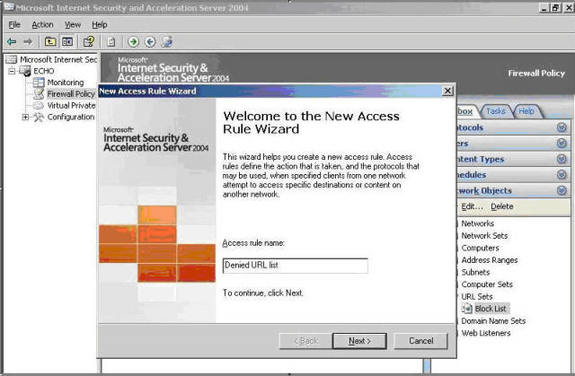
This Access Rule will be a deny rule, as we are not allowing these sites to be accessed. So we would select the Deny radio button.
There is no need in this case to block all outbound access to these websites. You may wish to do so when doing Domain Set Rules, but essentially we are trying to stop web access to them, since URL Sets only apply to Web access. For the super paranoid, you may, but otherwise just go with this.
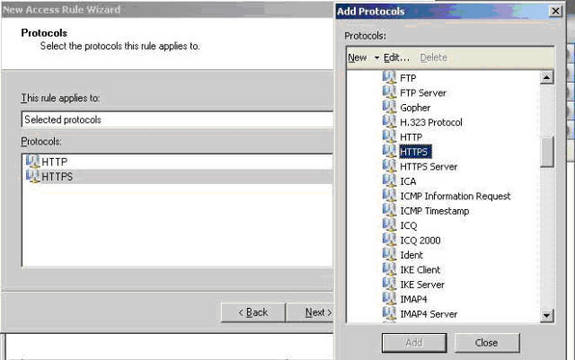
Choose the HTTP and HTTPS protocols, in the event of them using HTTPS you will be covered as well. You may also want to choose FTP as well, but it would be unlikely you would need it.
Next step in the wizard is to specify from what sources these requests should be denied. Choose the Internal, VPN Clients and Local Host in the event a browser ever gets configured on the firewall.

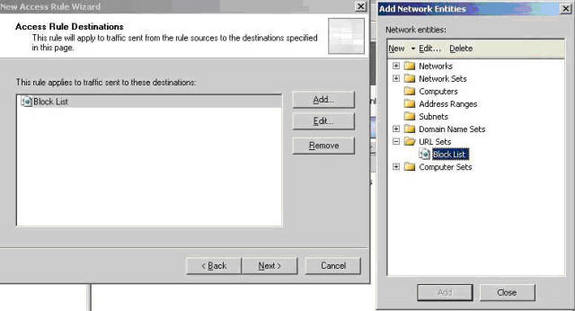
In this step, we will specify the sites or networks to which we don’t want requests to be forwarded to. Do not select the External network as that will block all of your web surfing, to any website. Of course no one would do that! What we need to select here is the URL Set we imported previously.
Click the Next button and then the Wizard will have completed. Click Finish and your nearly home.
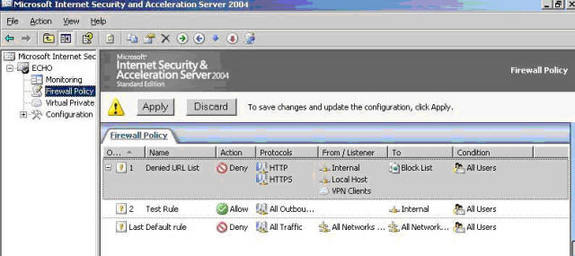
One thing you must make sure of before you finish is that you want to have your deny rules at the top of the list so they will get processed first. This will prevent any deny rules being overlooked. Hit the Apply button to update the changes and you are done.
To create the Domain Name Sets using Rich Krol’s file, BNSD.xml, the process is the same except for one small thing. Instead of importing that list into the URL Sets you would obviously import it into the Domain Name Sets instead. You may also want to think about adding the FTP protocol to the selected protocols step shown earlier, or all protocols, since you never know what those spyware vendors and hackers will use to transfer data.
|
Have Questions about this article? Go to: |
For more information on Access Rule Processing check out Stefaan Pouseele’s article:
http://www.isaserver.org/articles/ISA2004_AccessRules.html
That’s all for now
Greg Mulholland
[email protected]
I hope you enjoyed this article and found something in it that you can apply to your own network. If you have any questions on anything I discussed in this article, head on over to http://forums.isaserver.org/ultimatebb.cgi?ubb=get_topic;f=25;t=000701 and post a message. I’ll be informed of your post and will answer your questions ASAP. Thanks! –Tom
If you would like us to email you when Greg Mulholland releases another article on ISAserver.org, subscribe to our ‘Real-Time Article Update’ by clicking here. Please note that we do NOT sell or rent the email addresses belonging to our subscribers; we respect your privacy



