If you missed the first part in this article series please read Configuring the Windows Server 2008 Terminal Services Gateway (Part 1)
In the first part of this article series, we did a basic installation of Terminal Services and Terminal Services licensing and configure the Terminal Server licensing mode. In this, part two of the article series, we will finish up by installing and configuring the TS Gateway and the RDP client. Then we will make the connection and see it work.
Install the Terminal Services Gateway Service on the Terminal Services Gateway
Now we will move our attention to the Terminal Services Gateway computer. This is the machine that external clients will initially connect to when making their Terminal Services client connections.
Perform the following steps to install the Terminal Services Gateway on the Terminal Services Gateway computer:
- Open Server Manager on the Terminal Services Gateway computer. Click on the Roles node in the left pane of the console and then click the Add Role link in the right pane.
- Click Next on the Before You Begin page.
- On the Select Server Roles page, put a checkmark in the Terminal Services checkbox.
- On the Terminal Services page, click Next.
- On the Select Role Services page, put a checkmark in the TS Gateway checkbox. You will then see an Add Roles Wizard dialog box asking if you want to Add role services and features required for TS Gateway. Click the Add Required Role Services button.

Figure 1
- Click Next on the Select Role Services page.
- On the Choose a Server Authentication Certificate for SSL Encryption page, select the Choose a certificate for SSL encryption later option. We choose this option because we have not yet created a certificate for the TS Gateway to use for the SSL connection between itself and the RDP client. We will ask for this certificate later and then configure TS Gateway to use the certificate. Click Next.
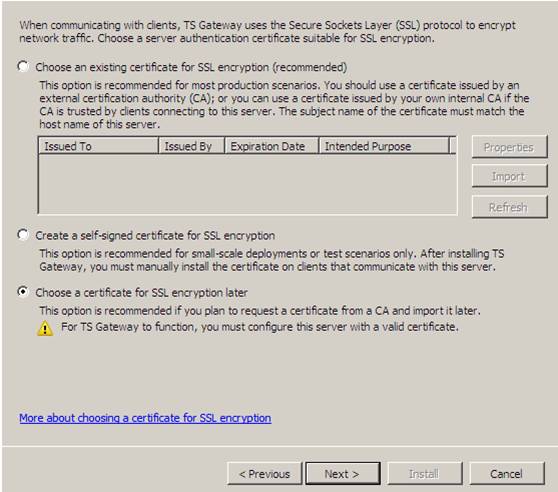
Figure 2
- On the Create Authorization Policies for TS Gateway page, select the Later option. We select this option because I want to take you into the TS Gateway console and show you how to configure authorization policies in the console. Click Next.
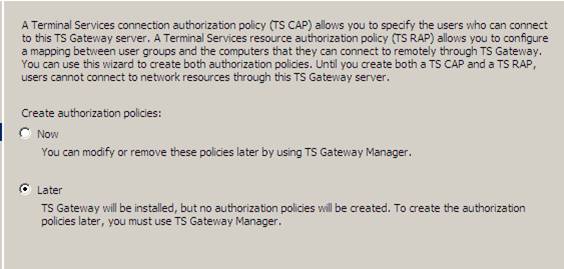
Figure 3
- Click Next on the Network Policy and Access Services page.
- On the Select Role Services page, confirm that the Network Policy Server checkbox is checked. Click Next.
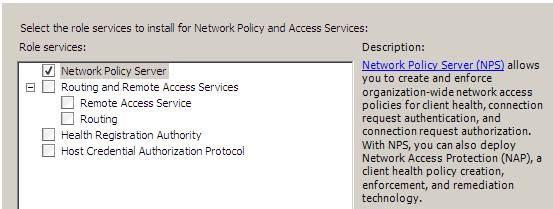
Figure 4
- On the Web Server (IIS) page, click Next.
- On the Select Role Services page, accept the default role services selected by the wizard. These are the services required to run the TS Gateway service. Click Next.
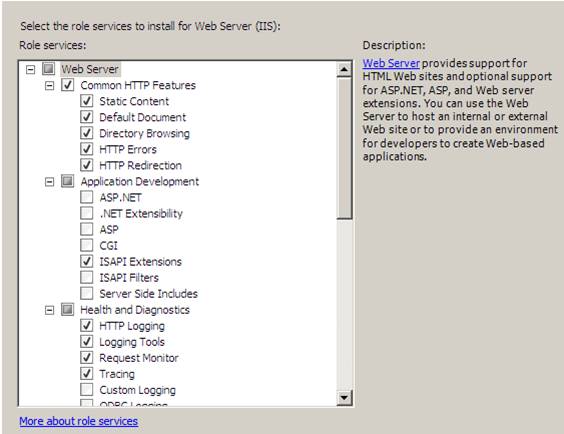
Figure 5
- Review the information on the Confirm Installation Selections page and click Install.
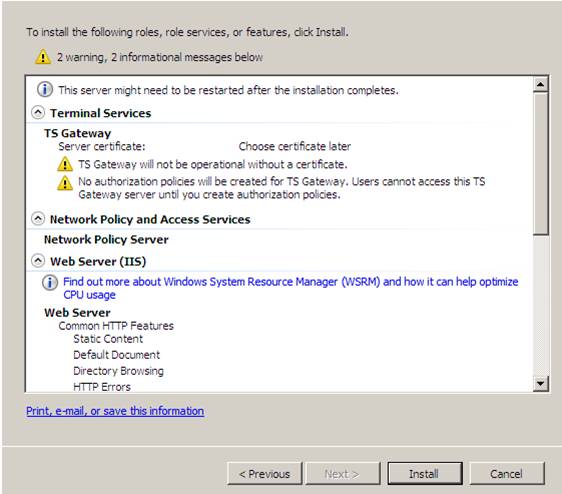
Figure 6
- Click Close on the Installation Results page which shows that the install succeeded.
Request a Certificate for the Terminal Services Gateway
Now we can request a certificate that the TS Gateway Web site can use to establish the SSL connection with the RDP client.
Perform the following steps to request the certificate for the TS Gateway computer:
- From the Administrative Tools menu, click Internet Information Services (IIS) Manager.
- In the Internet Information Services (IIS) Manager console, click on the server name in the left pane of the console. Double click the Server Certificates icon in the middle pane of the console.
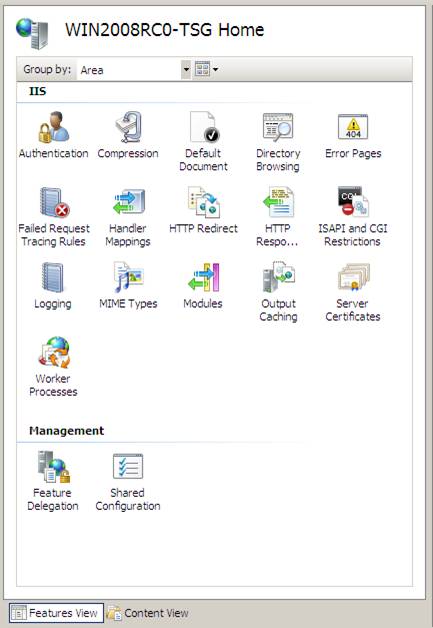
Figure 7
- In the right pane of the console, click the Create Domain Certificate link.
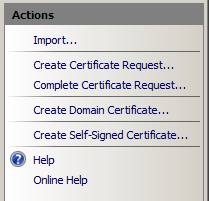
Figure 8
- On the Distinguished Name Properties page, enter the information specified on this page. The most important entry is the Common name entry. The name you enter here must be the same name that the Terminal Services client is configured to use to contact the TS Gateway computer. This is also the name that your public DNS servers would be configured to provide the public address that allows access to the TS Gateway. In most cases, this will be a router or NAT device’s external interface, or perhaps the external interface of an advanced firewall, such as the Microsoft ISA Firewall. Click Next.
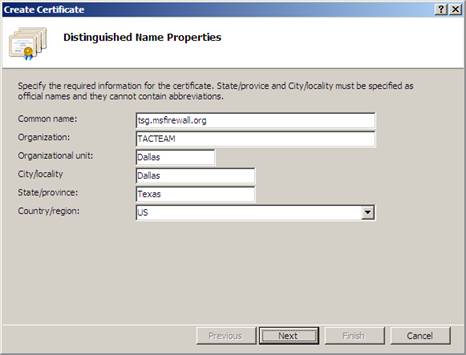
Figure 9
- On the Online Certification Authority page, click the Select button. In the Select Certification Authority dialog box, select the name of the Enterprise CA that you want to obtain the certificate from. Remember, we are able to obtain this domain certificate and automatically install it because we are using an Enterprise CA. If you were using a standalone CA, you would have to suffer from using the Web enrollment site, and that would only be after you created an offline request, and then you would have to manually install the computer certificate. Click OK after selecting the Enterprise CA.
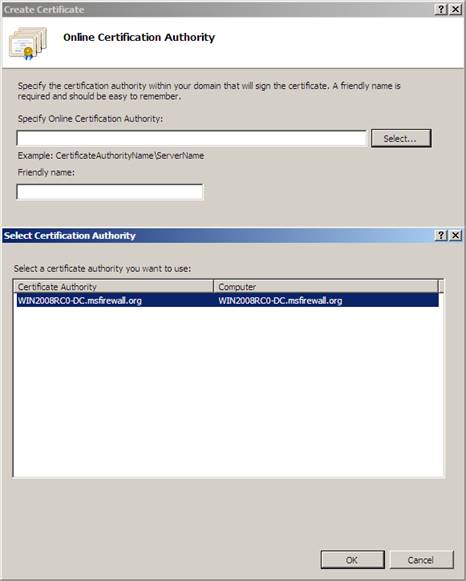
Figure 10
- Enter a Friendly name on the Online Certification Authority page. In this example we will give the certificate a friendly name of TSG Cert. Click Finish.
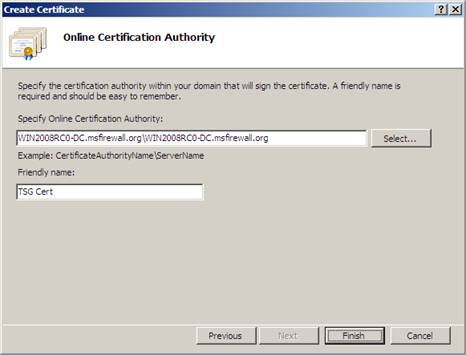
Figure 11
- After receiving the certificate, you will see certificate related information in the middle pane of the console. If you double click the certificate, you will see the Certificate dialog box, which shows you the common name in the Issued to field and the fact that You have a private key that corresponds to this certificate. This is crucial, since the certificate will not work if you do not have a private key. Click OK to close the Certificate dialog box.
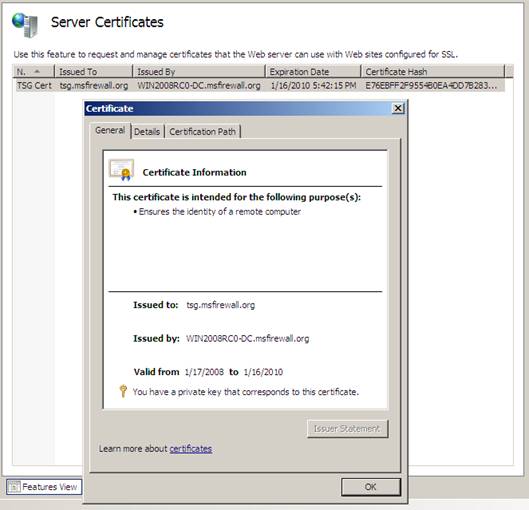
Figure 12
Configure Terminal Services Gateway to Use the Certificate
With the certificate now installed in the machine’s computer certificate store, you can assign the TS Gateway to use this certificate.
Perform the following steps to configure the TS Gateway to use this certificate:
- In the Administrative Tools console, click the Terminal Services entry and then click TS Gateway.
- In the TS Gateway Manager, click the name of the TS Gateway computer in the left pane of the console. The middle pane provides useful information about configuration steps that need to be completed in order to finish the setup. Click the View or modify certificate properties link.
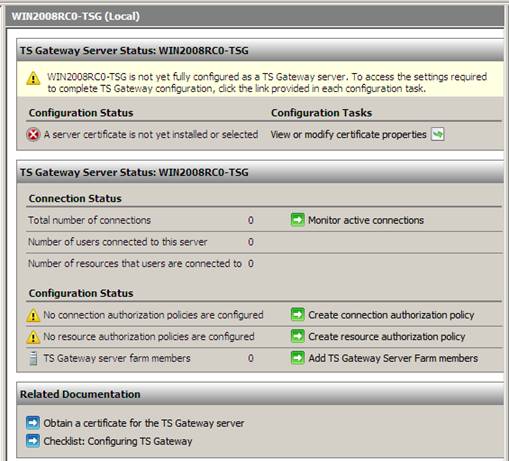
Figure 13
- In the Properties dialog box for the TS Gateway, on the SSL Certificate tab, confirm that the Select an existing certificate for SSL encryption is enabled and then click the Browse Certificates button. This brings up the Install Certificate dialog box. Click the certificate, which is in this case, tsg.msfirewall.org and then click the Install button.

Figure 14
- The SSL Certificate tab now shows information about the certificate that the TS Gateway will use to establish SSL connections. Click OK.
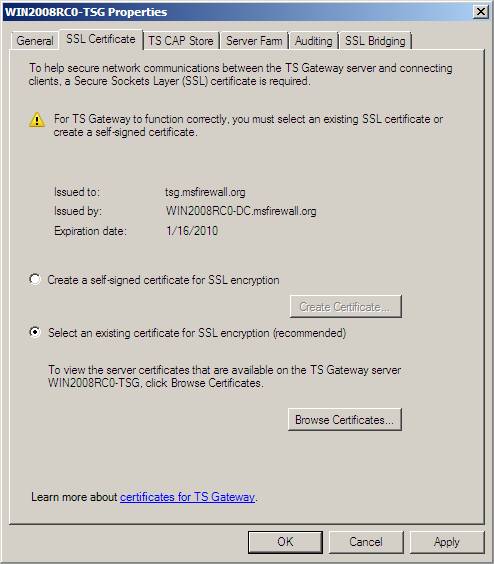
Figure 15
- The contents of the middle pane change, reflecting the fact that the certificate is now installed on the TS Gateway. However, we now see in the Configuration Status section that we need to create both a connection authorization policy and a resource authorization policy.
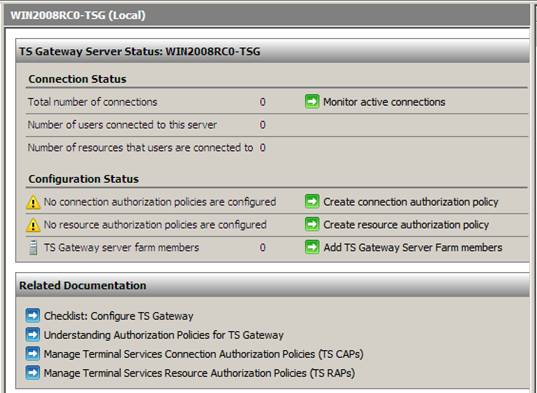
Figure 16
Create a Terminal Services Gateway CAP
A connection authorization policy (CAP) allows you to control who can connect to the Terminal Server through the Terminal Services Gateway.
Perform the following steps to create a connection authorization policy:
- In the left pane of the console, click the Connection Authorization Policies node that lies under the Policies node. In the right pane of the console, click the arrow to the right of Create New Policy and then click Wizard.
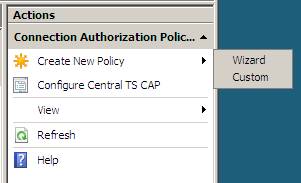
Figure 17
- On the Authorization Policies page, select the Create only a TS CAP option. Click Next.
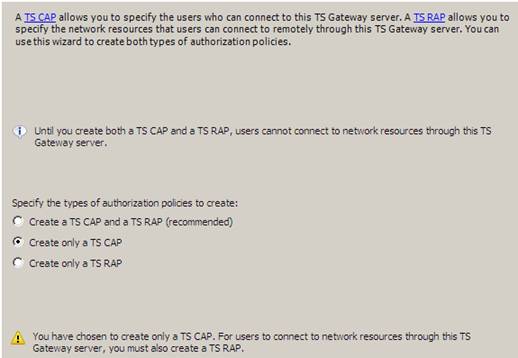
Figure 18
- On the Connection Authorization Policy page, enter a name for the CAP. In this example we will name the CAP General CAP. Click Next.
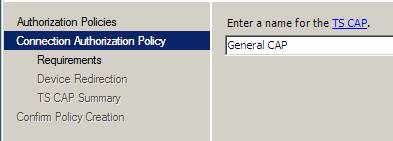
Figure 19
- On the Requirements page, put a checkmark in the Password checkbox. If you plan on using Smartcard authentication, then you would select the Smartcard option. Now you need to configure what groups can access the Terminal Server through the TS Gateway. To do this, click the Add Group button. In the Select Groups dialog box, enter the name of the group you want to allow access and click Check Names. In this example, enter Domain Users and then click OK.
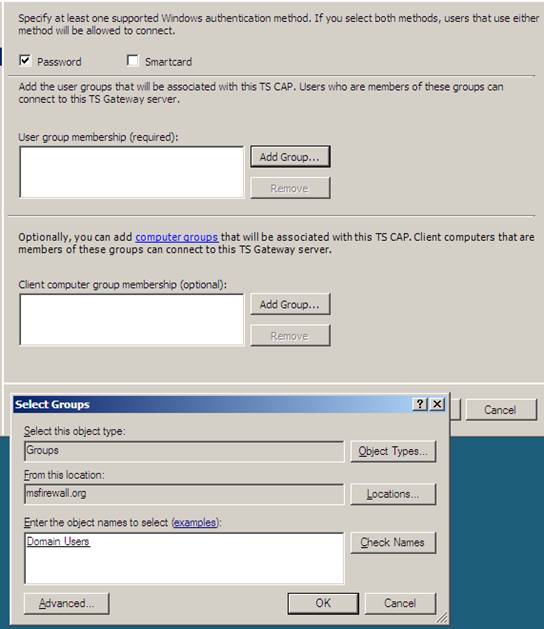
Figure 20
- Notice on the Requirements page that you also have an option to create computer groups and allow access only to specified computers. We will not configure that option in this example. Click Next.
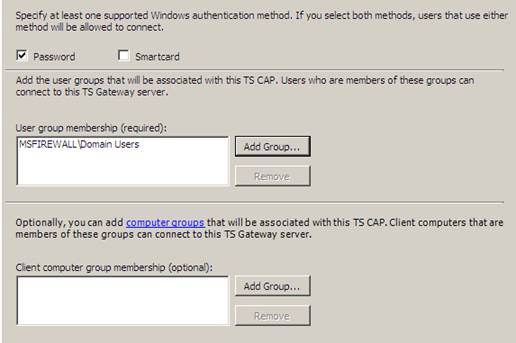
Figure 21
- On the Device Redirection page, select the Enable device redirection for all client devices option. Note that if you want a higher security environment, you might consider selecting the Disable device redirection for the following client device types and then select the Drives and Clipboard options. For even higher security, you might even select the Disable device redirection for all client devices except for smart cards. Click Next.
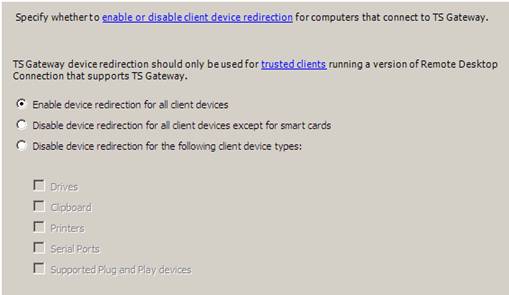
Figure 22
- On the Summary of TS CAP Settings page, read the results of your selections and then click Finish.
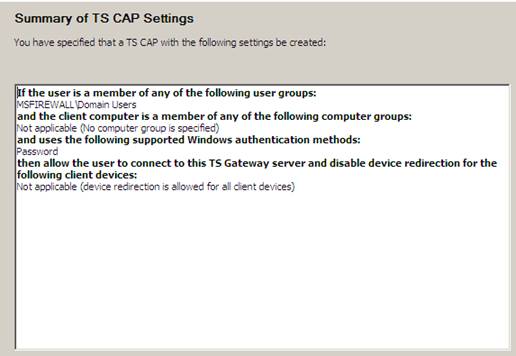
Figure 23
- Click Close on the Confirm Policy Creation page.
Create a Terminal Services Gateway RAP
The next policy we need to create is a Resource Authorization Policy or RAP. RAP’s are used to control which Terminal Servers can be accessed through the Terminal Services Gateway.
Perform the following steps to create the RAP:
- Click on the Resource Authorization Policies node in the left pane of the TS Gateway Manager console. In the right pane of the console, click the arrow sitting to the right of the Create New Policy link and then click Wizard.
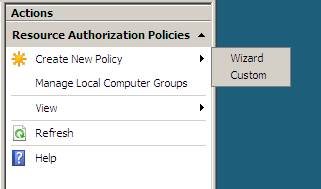
Figure 24
- On the Authorization Policies page, select the Create only a TS RAP option.
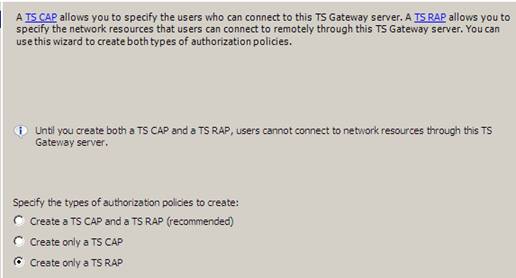
Figure 25
- On the Resource Authorization Policy page, give a name for the RAP in the Enter a name for the TS RAP text box. In this example, we will name the RAP General RAP. Click Next.
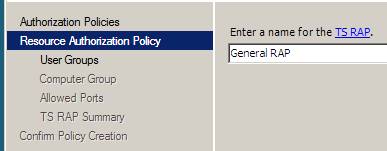
Figure 26
- On the User Groups page, you select the user groups to which this RAP will apply. This gives you fined tuned control over which users are able to access which Terminal Servers. Some groups might be allowed to access Terminal Server A and some other groups might want to have access to Terminal Server B. The RAP gives you this kind of control. In this example, click the Add Group button and add the Domain Users group. Click Next.
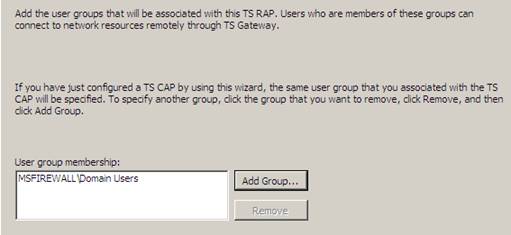
Figure 27
- On the Computer Group page, you have the option of defining what Terminal Servers are accessed through this RAP. You have the option of selecting an Active Directory defined group of computers, or you can create a TS Gateway managed group. In this example, since we only have a single Terminal Server, we will choose the most simple option, which is the Allow users to connect to any network resource (computer) option. This will allow users to connect to all Terminal Servers on the network. Click Next.
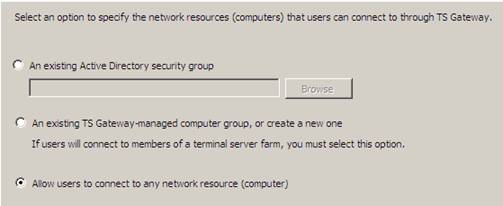
Figure 28
- On the TS Rap summary page, confirm your settings and click Finish.
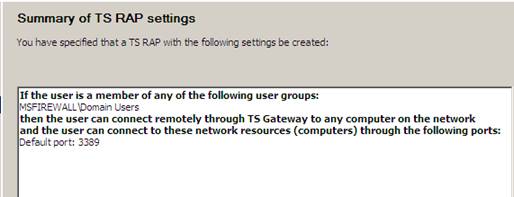
Figure 29
- Click Close on the Confirm Policy Creation page.
- Click on the server name in the left pane of the console. You will see in the middle pane that there are no more issues that we need to handle. The TS Gateway is now ready to handle new incoming connections to any Terminal Server on the network.

Figure 30
Configure the RDP Client to use the Terminal Services Gateway
We are almost home! The Terminal Server and the TS Gateway are now configured and ready to go. The last step is to configure the RDP client on the Vista computer. We need to configure the client with the name of the Terminal Server that it should connect to and the name of the Terminal Services Gateway computer that it will use to reach the Terminal Server.
Note:
I have configured the Vista client computer with a HOSTS file entry for tsg.msfirewall.org so that it will resolve the name of the Terminal Services Gateway to the IP address of the external interface of the NAT device in the front of the network.
Perform the following steps to configure the RDP client on the Windows Vista computer:
- On the Vista computer, click the Start button and then click Accessories. Double click Remote Desktop Connection.
- In the Remote Desktop Connection dialog box, on the General tab, enter the computer name of the Terminal Server in the Computer text box. Enter your user name in the User name text box. If you want the client to save your credentials, you can put a checkmark in the Allow me to save credentials check box.

Figure 31
- Click on the Advanced tab. In the Server authentication section, make sure that the Warn me option is selected. Click the Settings button in the Connect from anywhere section.

Figure 32
- In the TS Gateway Server Settings dialog box, select the Use these TS Gateway server settings option. Enter the name of the TS Gateway in the Server name text box. For the Logon method, select the Ask for password (NTLM). Note that the Automatically detect TS Gateway server settings option allows you to configure the RDP client to pull its settings via Group Policy. Click OK.

Figure 33
- Click on the General tab and then click Connect.

Figure 34
- A Windows Security dialog box will appear. Enter your password and then click OK.
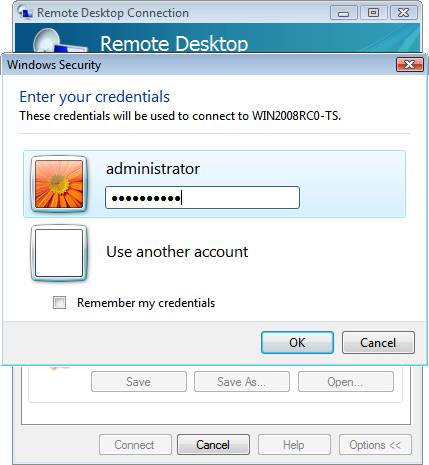
Figure 35
- The Terminal Services session opens up and you can see the desktop and applications running for your account in the Terminal Services session.
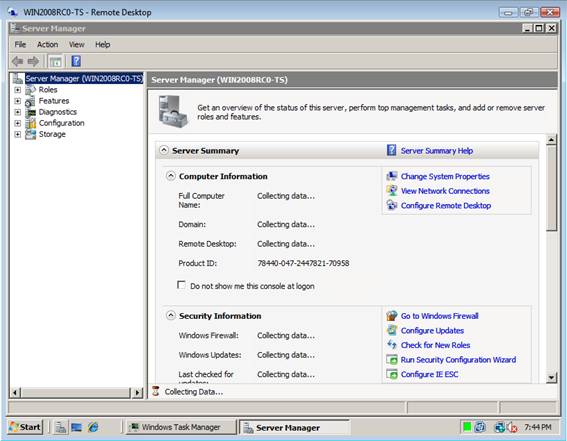
Figure 36
- Go to the TS Gateway computer and click on the Monitoring node in the left pane of the Terminal Services Gateway console. Here you can see information about the Terminal Services sessions going through the TS Gateway.
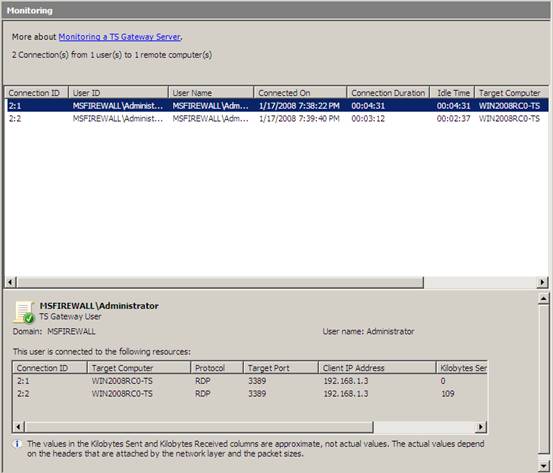 Figure 37
Figure 37
Summary
In this, part 2 of our article series on the TS Gateway, we installed and configured the TS Gateway and the RDP client. We then connected to the TS Gateway and then to the Terminal Server through the TS Gateway. We also saw that the monitoring node on the TS Gateway provides us useful information about who’s connecting to the Terminal Server through the TS Gateway. I hope you found the information in this article useful and if you have any questions, please feel free to write to me at [email protected]
If you missed the first part in this article series please read Configuring the Windows Server 2008 Terminal Services Gateway (Part 1)




Pls, can anyone suggest me :How to Backup Terminal Services/Configuration in a Shared Server in which are being logged Remotely a lot of users?
Regards