If you missed the other parts in this article series, check them out at:
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 1)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 3)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 4)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 5)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 6)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 7)
In the first part of this series on how to use the branch office connectivity wizard to create a site to site VPN between a main and branch office, we went over the example network infrastructure and discussed some key concepts in creating site to site VPNs.
In this, part 2 of the series, we’ll explore the DNS issues required to make the solution work, and then install the CSS and create the main and branch office ISA Firewall arrays.
Configure the DNS Server to Reject Dynamic Updates and Enter Host (A) Records for the ISA Firewall Computer and Array Names
Before we begin with installing the CSS at the main office and the ISA Firewall arrays, the first step is to configure the DNS server on the corporate network to deny dynamic updates. We need to do this so that when the branch office ISA Firewall connects to the main office ISA Firewall that it’s virtual IP address isn’t registered in DNS instead of the actual internal IP address of the branch office ISA Firewall. This will also prevent the main office ISA Firewall from registering its virtual IP address in DNS as well.
This is a very common issue for connectivity problems related to site to site VPN connections. For example, suppose you use Web proxy and Firewall clients on the main office network and those clients are configured to use the name of the ISA Firewall to connect to the ISA Firewall’s Firewall and Web proxy services. Everything works fine until the site to site connects. After the site to site connection establishes, the virtual IP address of the main office registers itself in the DDNS. Now when the Web proxy and Firewall clients try to connect to the main office ISA Firewall, they try to connect to the main office ISA Firewall’s virtual IP address (RAS interface address) and the connections from the Web proxy and Firewall clients fail.
Another scenario where registration of the virtual (RAS) interface IP address creates problems is when the branch office ISA Firewall tries to connect to the main office CSS. When the site to site connection completes, the branch office ISA Firewall registers it’s virtual (RAS) interface address in the CSS. The CSS tries to communicate with the branch office array Firewall using this address and the connection fails.
We can prevent these problems by disabling DDNS on the DNS server. You might ask “do we need to do this permanently, or is there a way that we can configure the demand-dial interfaces to not register in the DDNS?” The answer to this question is “maybe”. I don’t want to give away the answer this early in the article series, or else you might not continue reading.
We need to create Host (A) records in our Active Directory integrated DNS for the following names:
- isa2006se.msfirewall.org (10.0.0.1)
- isa2006branch.msfirewall.org (10.0.1.1)
- main.msfirewall.org (10.0.0.1)
- branch.msfirewall.org (10.0.1.1)
We don’t need to enter records for the CSS machine or the domain controller because those machines have already been installed and registered in DNS using DDNS. We don’t need to worry about those machines because their IP addressing information isn’t going to change based on the connection state of the site to site VPN connection.
Before you create the Host (A) records, you need to create a reverse lookup zone for the branch office network ID. In our current example, the branch office network ID is 10.0.1.0/24. Perform the following steps to create the reverse lookup zone:
- On the domain controller, click Start and then point to Administrative Tools. Click DNS.
- In the DNS management console, expand the server name and then click the Reverse Lookup Zones node.
- Right click the Reverse Lookup Zone node and click New Zone.
- On the Welcome to the New Zone Wizard page, click Next.
- On the Zone Type page, select the Primary Zone option and click Next.

Figure 1
- On the Active Directory Zone Replication Scope page, select the To all DNS servers in the Active Directory domain msfirewall.org option. We select this option because there is only a single domain in our organization. If you had multiple domains, you might want to replicate this reverse lookup zone to all DNS servers in the forest. Click Next.

Figure 2
- On the Reverse Lookup Zone Name page, select the Network ID option and enter the network ID for the branch office in the text box. In this example the branch office network ID is 10.0.1.0/24, so we’ll enter 10.0.1 and click Next.

Figure 3
- On the Dynamic Update page, select the Allow only secure dynamic updates (recommend for Active Directory) option. We don’t want to take away the option of using dynamic updates for this zone, since we want the branch office servers to be able to register in the DDNS. We only want to avoid the demand-dial interfaces from registering in DNS, and we’ll check later to see if this is possible. Click Next.

Figure 4
- Click Finish on the Completing the New Zone Wizard page.
- You’ll see the new zone in the left pane of the DNS management console.

Figure 5
Now we’re ready to create the Host (A) records. Use the following procedure to add the Host (A) records to DNS:
- On the domain controller, click Start, point to Administrative Tools and click DNS.
- In the DNS management console, expand the server name and then expand the Forward Lookup Zones node. Click on the msfirewall.org node.
- Right click on the msfirewall.org node and click the New Host (A) command.
- In the New Host dialog box, enter the host name of the server in the Name (uses parent domain name if blank) text box. In this example we’ll enter the name of the branch office ISA Firewall, which is isa2006branch. The FQDN will then appear in the Fully qualified domain name (FQDN) text box. Enter the internal IP address of the branch office ISA Firewall in the IP address text box. In this example the IP address of the branch office ISA Firewall is 10.0.1.1, so we’ll enter that into the text box. Click Add Host.
Figure 6
- The New Host dialog box remains open to allow you to enter more Host (A) entries. Enter the names and IP addressing information for the entries noted in the list above for the local ISA Firewall name, as well as the array names.
- After you enter all the records, click Cancel in the New Host dialog box.
- Your list should look something like that in the figure below.
Figure 7
- We now need to get these entries loaded into the DNS database. We can do that by restarting the DNS server. In the DNS console, right click the server name, point to All Tasks, and click Restart.
Figure 8
To finish off the DNS configuration, we need to disable dynamic updates (at least temporarily). In the left pane of the DNS console, click on the msfirewall.org entry in the Forward Lookup Zones node. Right click the msfirewall.org node and click Properties.
In the Properties dialog box, click the General tab. On the General tab, select the None option from the Dynamic updates drop down list. Click OK. There’s no need to restart the DNS service for this option to take effect. Minimize the DNS console.

Figure 9
Install the CSS on the Dedicated CSS Computer
Now that the critical step of setting up DNS is completed, we can move to the next step, which is installing the CSS on the dedicated CSS computer. While it’s possible to install the CSS on a DC, or even on the ISA Firewall array itself, the best and most secure configuration is to place the CSS on a dedicated device that is off DCs and array members.
In an ideal setup, the CSS is placed on a dedicated network security segment where no other machines are located, and no traffic is allowed to the CSS machine from any other segment, using the ISA Firewall to protect the CSS from all other machines. However, in order to simplify things a bit in this article series which already has its own complexities, I haven’t set things up that way. In the future I might focus on how to set up this configuration. However, you can use the principles discussed in the many DMZ articles on this site, especially those on how to secure FE Exchange Servers.
Perform the following steps to install the CSS on the dedicated CSS computer:
- Put the ISA 2006 CD into the computer. If the autorun menu doesn’t start, double click on the ISAAutorun.exe file to bring up the autorun menu.
- On the autorun menu, click the Install ISA Server 2006 link.
- Click Next on the Welcome to the Installation Wizard for Microsoft ISA Server 2006 page.
- Select the I accept the terms in the license agreement option on the License Agreement page and click Next.
- Enter your customer information on the Customer Information page and click Next.
- On the Setup Scenarios page, select the Install Configuration Storage Server option and click Next.

Figure 10
- Click Next on the Component Selection page.

Figure 11
- On the Enterprise Installation Options page, select the Create a new ISA Server enterprise option. This option allows you to create a new enterprise. In contrast, the Create a replica of the enterprise configuration option allows you to create a copy of an existing ISA Firewall enterprise, which can be used as a backup CSS in case the primary CSS goes down. In this example we need to create a new enterprise which will contain all of our arrays. Click Next.

Figure 12
- On the New Enterprise Warning page you see information about the value of using a single enterprise to manage all of your arrays. Click Next.

Figure 13
- On the Create New Enterprise page, enter a name for the new ISA Firewall enterprise in the Enterprise name text box. In this example, we’ll use the name Enterprise. You can enter a description for this ISA Firewall enterprise in the Description text box. Click Next.

Figure 14
- In the Enterprise Deployment Environment dialog box, you tell the installation wizard whether or not the ISA Firewalls, as the CSS, are part of the same domain, or if they’re in a workgroup. ISA Firewall best practices for security and ease of configuration dictate that all should be part of the same domain, so we’ll go with those best practices. There are some circumstances where the “network guys” may have hijacked network security and thus don’t understand the ISA Firewall and thus will try to force you to deploy in a less secure and less flexible workgroup configuration. If you’re in that unfortunate position, you’ll need to deploy in a workgroup, which means deploying a PKI and making sure all machines have the appropriate certificate.
Since we’re deploying a secure configuration, the ISA Firewall members and the CSS are part of the same domain, so select the I am deploying in a single domain or in domains with trust relationships option. Click Next.

Figure 15
- On the Ready to Install the Program page, click Next.

Figure 16
- The progress bar will inform you the state of the installation and what activities the installer is performing at any point in time.

Figure 17
- On the Installation Wizard Completed page, put a checkmark in the Invoke ISA Server Management when the wizard closes. Click Finish.

Figure 18
Create the Arrays and Configure the Enterprise Management Station
Now we’re ready to create the arrays for the main and branch offices. An array is a collection of ISA Firewalls that act as a single logical firewall, in that they all have the same firewall policy and configuration. An ISA Firewall array can consist of 1 to 32 servers. At least one interface on each ISA Firewall array member must be on the same network ID as all other ISA Firewall array members in the same ISA Firewall array, as this interface is used for intra-array communications. In practice, this means that you cannot extend arrays across WAN links or site to site VPNs, as all interfaces in the remote offices are going to be on a network ID which is different from that at the main office.
In the example used in this series, we will have two arrays: a main office array named Main and a branch office array named Branch. We could create multiple main office arrays and multiple branch office arrays, and each array could contain up to 32 members. In practice, branch offices will typically contain a single array member, while main offices and large branch offices will contain arrays members of 2-32 servers.
One of the great advantages of using multiple array members is that the CARP and NLB load balancing mechanisms allow you to increase effective throughput by the sum of the array members per array times the link speed available to each array member.
For example, for stateful packet inspection, a typically configured ISA Firewall can pass traffic at approximately 1.5Gbps. If you have a main office array containing 5 array members, the effective throughput through the array is 7.5Gbps. Try pricing out a “hardware” firewall that has 7.5Gbps throughput and compare it to the cost of the five member array on stock computer hardware.
You’ll be impressed by the cost savings, as well as the ability to get parts and replacement parts at commodity prices, and not at the insane markups charged by the “hardware” firewall vendors. Take the money you save and buy yourself a Corvette, instead of buying the Corvette for the hardware firewall sales guy.
Let’s get back to the ISA Firewall console. After you click Finish on the last page of the installation wizard, the ISA Firewall console opens as well as the security Web page. Perform the following steps to add the CSS to the Enterprise Remote Management stations in enterprise policy:
- Read the Protect the ISA Server Computer Web page and then close it.
- In the ISA Firewall console, expand the Enterprise node and then expand the Enterprise Policies node. Click on the Default Policy node.

Figure 19
- Click the Toolbox tab in the Task Pane. Click the Network Objects heading. Click the Computer Sets folder and then double click on the Enterprise Remote Management entry.

Figure 20
- In the Enterprise Remote Management Computers Properties dialog box, click the Add button and click the Computer entry.

Figure 21
- In the New Computer Rule Element dialog box, enter a name for the CSS machine, which also acts as an enterprise remote management station. We’ll name this computer CSS and enter that name in the Name text box. In the Computer IP Address text box, enter the IP address of the CSS machine. In our example, the IP address is 10.0.0.3. Enter a description for this machine in the Description (optional) text box. Click OK in the New Computer Rule Element dialog box.

Figure 22
- Click OK in the Enterprise Remote Management Computers Properties dialog box.
- Click Apply to save the changes and update the firewall policy. Click OK in the Apply New Configuration dialog box.
Now we need to create the arrays. There will be two arrays in this scenario: a main office array and a branch office array. Both arrays will be managed in the same ISA Firewall enterprise and will be manageable using the centralized enterprise policies. Perform the following steps to create the Main array:
- In the left pane of the ISA Firewall console, right click on the Arrays node. Click the New Array command.

Figure 23
- In the Welcome to the New Array Wizard dialog box, enter a name for the array in the Array name text box. In this example we’ll name the array Main. Click Next.

Figure 24
- In the Array DNS Name text box, enter a FQDN that identifies the array name. This is useful for when you’re using NLB or client side CARP for load balancing. In this example, we’ll use the name main.msfirewall.org which resolves to the IP address of the internal interface of the main office ISA Firewall. If we had NLB enabled, this name would resolve to an internal VIP, and if we were using client side CARP, we would have multiple Host (A) records for this name and use DNS round robin for distributing the initial connections to receive the array table information. Click Next.

Figure 25
- On the Assign Enterprise Policy page, select the default option, Default Policy. Later we’ll investigate how to use enterprise policies that apply to all arrays managed by the same ISA Firewall enterprise. Click Next.

Figure 26
- On the Array Policy Rule Types page, you can exert some centralized control over the types of rules that can be configured by array administrators. Leave the default settings “Deny” Access Rules, “Allow” Access Rules and Publishing rules (Deny and Allow) enabled and click Next.

Figure 27
- Click Finish on the Completing the New Array Wizard page.

Figure 28
- A Creating a new array progress bar appears as the array is created.

Figure 29
- Click OK after The new array was successfully created appears.

Figure 30
- Click Apply to save the changes and update the firewall policy. Click OK in the Apply New Configuration dialog box.
Now let’s create the branch office array:
- Right click on the Arrays node and click New Array.

Figure 31
- Enter Branch in the Array name text box. Click Next.

Figure 32
- Enter branch.msfirewall.org in the Array’s DNS name text box. This will resolve to the internal IP address on the branch office ISA Firewall. Click Next.

Figure 33
- Accept the Default Policy entry on the Assign Enterprise Policy page and click Next.
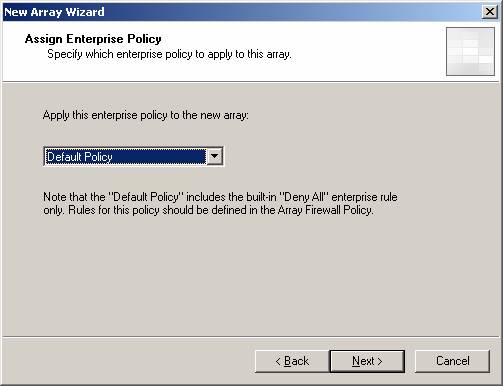
Figure 34
- Accept the default settings on the Array Policy Rule Types page and click Next.
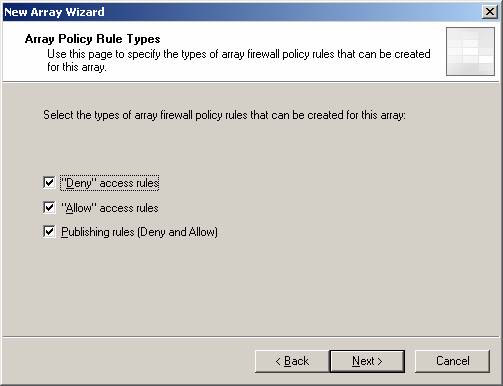
Figure 35
- Click Finish on the Completing the New Array Wizard page.

Figure 36
- The status bar indicates the progress in creating the new array.

Figure 37
- Click OK when you see The new array was successfully created.
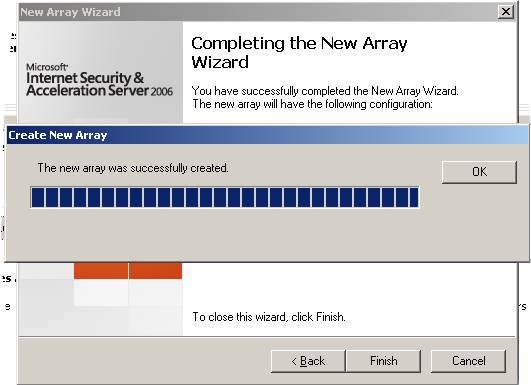
Figure 38
- Click Apply to save the changes and update the firewall policy. Click OK in the Apply New Configuration dialog box.
One last thing to do before we finish. Click the link at the top of the middle pane regarding the customer experience improvement program. This brings up the Customer Feedback dialog box. I highly recommend that you participate in the program, as it helps the ISA Firewall product group understand how you use the ISA Firewall and how to more quickly respond to problems or issues you might be having with your ISA Firewall. No information that could compromise your security posture is sent to Microsoft and the end result will be a more secure and stable ISA Firewall product for you and everyone else who uses the ISA Firewall.

Figure 39
Summary
In this article on how to create a site to site VPN using the branch office connectivity wizard, we configured the DNS server with Host (A) records to support the solution. After configuring DNS, we installed the CSS on a dedicated CSS machine and then configured the main and branch office arrays on the CSS. Next week we’ll continue by using the branch office connectivity wizard to create the answer file and then use that answer file to create the site to site VPN connection and join the branch office ISA Firewall to the domain and main office CSS. See you then! – Tom.
If you missed the other parts in this article series, check them out at:
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 1)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 3)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 4)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 5)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 6)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 7)








