If you missed the other parts in this article series, check them out at:
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 1)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 2)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 3)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 5)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 6)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 7)
In the first three parts of this series on using the branch office connectivity wizard to connect the branch office ISA firewall to the main office ISA firewall, we discussed the example network infrastructure, went over important concepts in creating site to site VPNs, configured the supporting network services, and then installed the CSS, main office ISA Firewall and branch office ISA Firewall. At the end of part 3 in this series, the branch office ISA Firewall was ready to accept the answer file that will be used by the branch office connectivity wizard.
|
Discuss this article |
In this, part 4 in the series we’ll continue by configuring the main office ISA firewall with the Remote Site Network that is used to create the site to site VPN connection from the main office to the branch office. After we create the Remote Site Network, we can use the answer file wizard to create the answer file that the branch office connectivity wizard will use to create the site to site VPN connection from the branch office to the main office. The branch office connectivity wizard will also allow you to automatically join the branch office ISA Firewall to the domain, which provides us with the highest security and flexibility possible.
Create the Remote Site Network to Connect to the Branch Office over Site to Site VPN
Now we need to create the remote site network that initiates the site to site VPN connection from the main office to the branch office. After the site to site VPN connection configuration is completed, we can create an answer file and copy it to the root of the C: drive of the branch office ISA Firewall. The branch office connectivity wizard will automatically find the answer file to complete the configuration of the branch office ISA Firewall’s site to site VPN connection to the main office.
Perform the following steps to create the site to site VPN connection at the main office ISA Firewall that connects to the branch office ISA Firewall:
- At the CSS machine, expand the Arrays node and then expand the Main array node. Click the Virtual Private networks (VPN) node. Click the Remote Sites tab in the middle pane of the ISA Firewall console and then click the Tasks tab in the Task Pane. On the Task Pane, click the Create VPN Site to Site Connection link.

Figure 1
- On the Welcome to the Create [sic] VPN Site to Site Connection Wizard page, enter a name for the remote site in the Site to site network name text box. This is the name of the demand dial interface on this ISA Firewall that will accept the incoming connection from the branch office ISA Firewall. You will need to create a user account on this machine that has dial-in permissions that has this same name. The wizard will warn us about this later and we’ll create the user account after we complete the wizard. Click Next.

Figure 2
- On the VPN Protocol page, select the Layer Two Tunneling Protocol (L2TP) over IPSec option. This is the preferred option when you’re connecting two ISA Firewalls in a site to site VPN connection, which is the case in our scenario. You can use the branch office connectivity wizard only when there are ISA Firewalls on both sides of the site to site VPN link. The branch office connectivity wizard only works when you use either L2TP/IPSec or IPSec tunnel mode. Avoid the use of IPSec tunnel mode, as it is less secure and has much lower performance compared to L2TP/IPSec, because of its lack of header compression. If you choose PPTP as your VPN protocol, the option to create the answer file based on the remote site network configuration will not be available. Click Next.

Figure 3
- A warning dialog box will appear the informs you that you need to create a user account with the same name as the demand dial interface on this machine, which is the same as the name you gave to the remote site network at the beginning of the wizard. We’ll create this account when we finish creating the remote site network site to site VPN connection. Click OK.

Figure 4
- On the Local Network VPN Settings page, select the method the ISA Firewall will use to assign IP addresses to remote access VPN clients and VPN gateways. In our current example, the main office has an on-subnet DHCP server, so we’ll select the Dynamic Host Configuration Protocol (DHCP). Note that DHCP isn’t supported for multiple member ISA Firewall arrays. Click Next.

Figure 5
- Accept the default setting on the connection owner page. Since this is a single member ISA Firewall array, there is only a single machine that can be the connection owner. If we had multiple members in this ISA Firewall array, and had NLB enabled, then NLB would automatically assign the connection owner for the site to site VPN connection. Click Next.

Figure 6
- On the Remote Site Gateway page, enter the FQDN or IP address of the branch office ISA Firewall. In this example, the IP address of the branch office ISA Firewall will be 192.168.1.73 so we enter that value into the text box (note that I’m using private IP addresses in the lab – in a production environment the ISA Firewall would of course be on the network edge and have a public IP address). Enter the IP address in the Remote site VPN server text box and click Next.

Figure 7
- On the Remote Authentication page, you enter credentials the main office ISA Firewall can use to connect to the branch office ISA Firewall for the site to site VPN connection. Put a checkmark in the Allow the local site to initiate connections to the remote site, using this user account checkbox, then enter the User name, Domain, Password and Confirm Password information into the text boxes.
I prefer to use a local account on the machine, rather than a domain account. In fact, we can’t use a domain account in this scenario, because the branch office ISA Firewall will not be a domain member until after the initial site to site VPN connection is established. In our scenario, we will, on the branch office ISA Firewall, create a user account with the name main on the branch office ISA Firewall which is named ISA2006BRANCH. This explains the information in the figure below. Click Next.

Figure 8
- On the L2TP/IPSec Outgoing Authentication page, you select whether you want to use certificate authentication or a pre-shared key. In a production environment, I typically start with a pre-shared key and then after everything is working the way we expect, move to machine certificate authentication.
Select the Pre-shared key authentication option and then enter a key. In this example I’m using 123 for simplicity sake. In a production environment, use a complex key of more than 14 characters. Click Next.

Figure 9
- On the Incoming L2TP/IPSec Authentication page, select the authentication method you want the branch office ISA Firewall to use when creating the IPSec connection with the main office ISA Firewall. In this example, we’ll use the same method we use to dial out from the main office, using a pre-shared key and the key value of 123. Click Next.

Figure 10
- On the Network Addresses page, you enter the IP address ranges used on the remote site network. Click the Add Range button. In the IP Address Range Properties dialog box, enter the range of addresses used at the branch office. In this example, the branch office machines are located on network ID 10.0.1.0/24. Enter 10.0.1.0 in the Start address text box and 10.0.1.255 in the End address text box. Click OK.
|
Discuss this article |

Figure 11
- The branch office address range now appears in on the Network addresses page. Click Next.

Figure 12
- On the Remote NLB page, remove the checkmark from the The remote site is enabled for Network Load Balancing checkbox, since we’re not using NLB at the branch office. Click Next.

Figure 13
- On the Site to Site Network Rule page, you are given the opportunity to create a Route Network Rule between the main and branch offices over the site to site VPN. Accept the default selection Create a network specifying a route relationship option and the default name for the rule and then click Next.

Figure 14
- On the Site to Site Network Access Rule page, you can create an Access Rule that controls traffic moving over the site to site VPN at the main office ISA Firewall. In this example, select the Create an allow access rule option. Leave the default name for the Access Rule in the Access Rule name text box. From the Apply the rule to these protocols drop down list, select the All outbound traffic option. We’ll lock things down later, but at the beginning we want to make sure the site to site VPN successfully establishes and that the branch office ISA Firewall is able to join the domain. After the site to site VPN connection is stabilized, we’ll lock things down so that access to the appropriate intradomain communications and server access is allowed. Click Next.

Figure 15
- On the Completing the New VPN Site to Site Network Wizard page, click Finish.

Figure 16
- The Remaining VPN Site to Site Tasks dialog box appears informing you that you need to create the user account on the main office ISA Firewall that the branch office ISA Firewall can use to authenticate to the main office ISA Firewall for the site to site VPN connection. Click OK.

Figure 17
- Click Apply to save the changes and update the firewall policy. Click OK in the Apply New Configuration dialog box.
- Click on the Branch entry in the site list of the site to site VPN connections and click on the Tasks tab. Notice in the Related Tasks list that there is a new option: Create Answer File for Remote VPN Site. This option becomes available after creating the site to site VPN remote network and is only available in ISA 2006 Enterprise Edition. If you’re using ISA 2006 Standard Edition, then you’ll have to do all this work yourself, without benefit of answer files.

Figure 18
Now we need to carry out the configuration task the site to site VPN wizard asked us to carry out: we need to create the user account that the branch office ISA Firewall will use to authenticate to the main office ISA Firewall. Perform the following steps on the main office ISA Firewall computer (NOT the CSS) to create the user account and finish up the configuration:
- Right click on the My Computer object on the desktop and click the Manage command.

Figure 19
- In the Computer Management console, expand the System Tools node and then expand the Local Users and Groups node. Right click in an empty portion of the right pane and click the New User command.

Figure 20
- In the New User dialog box, enter Branch in the User name text box. This is a critical setting, as the name of this user must be the same as the name assigned to the demand dial interface on the main office ISA Firewall used to connect to the branch office ISA Firewall. Enter a password and confirm the password. Remove the checkmark from the User must change password at next logon and put checkmarks in the User cannot change password and Password next expires checkboxes. Click the Create button.

Figure 21
- Click Close in the New User dialog box.
- Double click on the Branch user to bring up the Branch Properties dialog box.
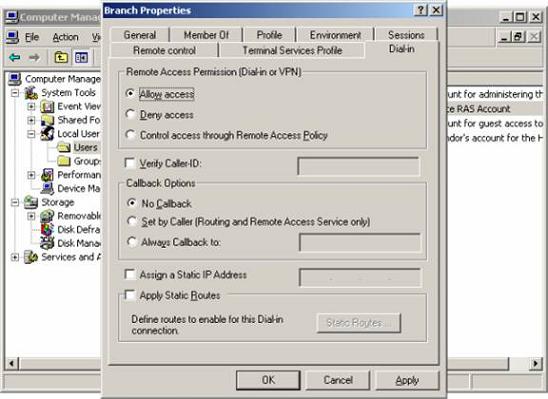
Figure 22
- Close the Computer Management console.
- Restart the ISA Firewall computer.
|
Discuss this article |
Summary
In this article, part 4 of our series on creating a site to site VPN using the branch office connectivity wizard, we went through the procedures required to create the Remote Site Network that enables the site to site VPN connection from the main office to the branch office. We also created the user account at the main office that the branch office ISA Firewall will use to establish the site to site connection from the branch office to the main office. In the next part of this series, we’ll use the site to site VPN answer file wizard to create the answer file that we’ll transfer to the branch office ISA Firewall. See you then!
If you missed the other parts in this article series, check them out at:
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 1)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 2)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 3)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 5)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 6)
- Creating a Site to Site VPN using the ISA 2006 Firewall Branch Office Connection Wizard (Part 7)





