Introduction
A null session attack is something that has been around since the days of Windows 2000, but amazingly enough it is something that system administrators often neglect to consider when hardening networks. This can lead to disastrous results as enumeration of a null session can divulge just about every bit of useful information an attacker needs to remotely gain access to a system. Although old hat, null session attacks are just as common now as they were years ago. As a matter of fact, even though modern systems are no longer fully vulnerable, when performing penetration testing exercises against Windows devices null session enumeration is still one of the first things I attempt. The goal of this article is to explain exactly how a null session attack works and then to explain how to prevent this from happening on your systems.
How Null Sessions Work
A remote session is created when a user logs on to a computer remotely using a username and password that has access to system resources. This is accomplished through the Server Message Block (SMB) protocol and the Windows Server service. These connections are entirely legitimate when proper credentials are supplied.
A null session comes into play when a user makes a connection to a windows system with no username or password. This type of connection can not be made to any typical windows share, but it can be done to the Interprocess Communication (IPC) administrative share. The IPC share, as the name alludes to, is used by Windows processes (via the SYSTEM username) to communicate with other processes across the network. The IPC share is used exclusively by the SMB protocol.
Using the IPC share with no credentials is typically reserved for programs communicating with one another, but there is nothing to say that a user could not connect to a machine via the IPC connection instead. This would not allow for unrestricted access to the machine, but will allow for pretty extensive enumeration that could aide an attacker.
Enumeration through a Null Session
Now that we know how null sessions work, how easy is it for an attacker to use this attack vector? Unfortunately, it is pretty easy. The null session connection can be created straight from the Windows command line with no additional tools necessary by simply using the NET command. The NET command can be used for a variety of administrative functions. Using the NET command we can attempt to make a connection to a standard share on our target host (appropriately named HACKME), but this fails because we did not supply proper credentials.
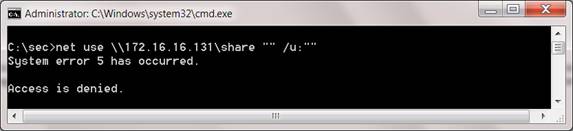
Figure 1: A failed connection attempt to a share using the NET command
Using this same NET command, we can modify the share name connect to the IPC$ administrative share. This has a more positive result.

Figure 2: A successful null session connection using the NET command
At this point, we have now established a null session connection to our victim. So what’s next? We do not have administrative access to the machine so we can not just start browsing the hard drive or extracting password hashes. Remember, the IPC share is used for communication between processes, so our access is limited to that of the SYSTEM username. We can use the NET command to extract more information from the target, but there are automated tools that will take a bit of the leg work out of the equation for us.
My favorite tool for extracting information from null sessions is a utility called Enum. Enum is a free command-line based utility that we can use to extract usernames, group names, system information, and more. As an attacker one of the most important things to me is a list of users on the system. With this list I can begin password guessing and even brute force attempts at cracking passwords. In order to obtain a user list with Enum, you can issue the following command:
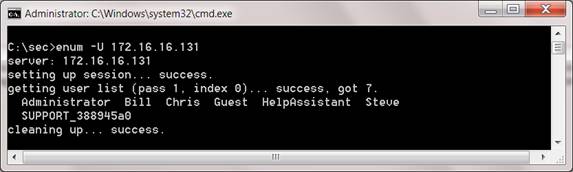
Figure 3: Using Enum to enumerate users on the system
With a user list in hand, we can then retrieve the systems password policy to better aide our password guessing attempts:

Figure 4: Using Enum to enumerate the password policy on the system
Taking things even further, we can gather a list of the shares on the victim machine:
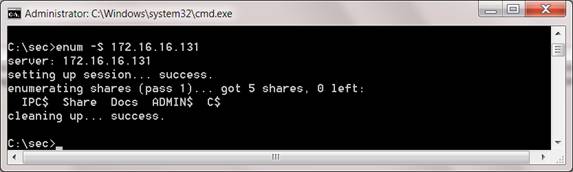
Figure 5: Using Enum to enumerate shares on a system
Enum provides several other options that can be used to pull the same type of information, and even includes a basic dictionary attack engine that can be used to crack passwords based upon a user supplied word list.

Figure 6: All of the possible flags for Enum
These things do not exactly give away the keys to the castle, but they are a good start and a crucial element for an attacker attempting to gain access to a victim.
Defending Against Null Sessions
The first question you will find yourself asking is, “Am I vulnerable?” The answer to this depends on the operating systems in your network environment. If you are running Windows XP, Windows Server 2003, or Windows 2000, then the answer is yes to at least some extent. This may not seem to be applicable since most people are well beyond these versions of the operating systems, but Windows XP and Server 2003 are still the most prolific operating systems in production. There are a few other things you can do to prevent the creation of null sessions.
Restrict Null Sessions in the Registry
Legacy software compatibility alongside the fact that most companies have to adhere to tight budgets, are just a couple of reasons why I still see Windows 2000 workstations and servers floating around. If you still require Windows 2000 clients then there is a simple registry change you can apply to prevent information extraction through null sessions.
If you open regedit and browse to HKLM/System/CurrentControlSet/Control/LSA/RestrictAnonymous you can configure three possible options.
0 – Default setting. Unrestricted null session access
1 – Doesn’t eliminate null sessions but prevents the enumeration of usernames and shares
2 – Virtually eliminates any value to null sessions by restricting access to basically everything
As you can see, you can not 100% eliminate null sessions but you can severely limit their power by setting this to 2. Be careful when configuring this option on a Windows 2000 server, as it may break clustering.
You can perform a similar action in Windows XP and 2003 Server through three separate registry keys.
HKLM\System\CurrentControlSet\Control\Lsa\RestrictAnonymous
0 – Default setting. Null sessions can be used to enumerate shares
1 – Null sessions can not be used to enumerate shares
HKLM\System\CurrentControlSet\Control\Lsa\RestrictAnonymousSAM
0 – Null sessions can enumerate user names
1 – Default setting. Null sessions can not enumerate user names
HKLM\System\CurrentControlSet\Control\Lsa\EveryoneIncludesAnonymous
0 – Default setting. Null sessions have no special rights
1 – Null sessions are considered part of the everyone group (quite dangerous and can allow for share access)
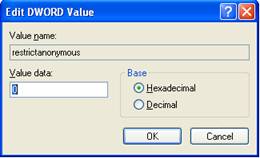
Figure 7: Modifying the RestrictAnonymous key in the registry
You can clearly see from the figure above that, by default, Windows XP only allows for enumeration of shares by the default function. This is more secure than what we see in Windows 2000 but still provides information to a potential intruder.
Block Access at the Network Level
If you can not make the registry changes listed above then you can block things with the Windows firewall or network firewall. This can be done by blocking access to the ports associated with NetBIOS and SMB over TCP/IP. These are:
TCP Port 135
UDP Port 137
UDP Port 138
TCP Port 139
TCP and UDP Port 445
These ports are used for all sorts of Windows networking functions including file sharing, network printing, clustering, and remote administration. That being said, blocking access to these ports should be thoroughly tested before being blindly done to a multitude of hosts.
Identify Null Sessions with IDS
If the registry changes or firewall rules mentioned earlier break the functionality of network applications, then you must switch to a reactive approach rather than a proactive one. Rather than preventing enumeration through null sessions the best we can hope to do is catch it when it happens and react to it as we would a normal network security incident.
If you are using Snort, the most popular IDS in production today, then the following rule will detect null session enumeration (taken from the Intrusion Detection with Snort, by Jack Koziol):
alert tcp $EXTERNAL_NET any -> $HOME_NET 139 (msg:”NETBIOS NT NULL session”; flow:to_server.establshed;
content: ‘|00 00 00 00 57 00 69 00 6E 00 64 00 6F 00 77 00 73 00 20 00 4E 00 54 00 20 00 31 00 33 00 38 00 31|’; classtype:attempted-recon;)
This would not prevent null session connections from occurring, but it will alert you when they do so you can react appropriately.
Conclusion
The null session concept is by no means a new threat but it is often forgotten about and misunderstood. It is still a very viable enumeration tactic for potential intruders and is even taught in most professional ethical hacking courses. Understanding how null sessions work is a must if you are responsible for the security of systems on a network.



