\The Exchange cyberattack in 2020, created a race to secure servers and environments from the internet. This has crept into the ethos of most companies with many server tools taken offline. Yet, not all companies got the wake-up call and some administrators are still accessing Exchange over the internet.
Many admins use the Exchange Control Panel (ECP) or Exchange Admin Center (EAC) to perform daily functions. PowerShell can also run many of these commands to perform Exchange functions. These functions include setting up servers to create mailboxes, setting forwarders, updating or adding receive connectors, and many more.
Since Exchange administration is critical for the daily operations of a company, it’s important to find the best ways of working. In this article, we delve into ways to mitigate your risk when dealing with Exchange and server-side activities.
How Do Companies Use Exchange Admin Centers?
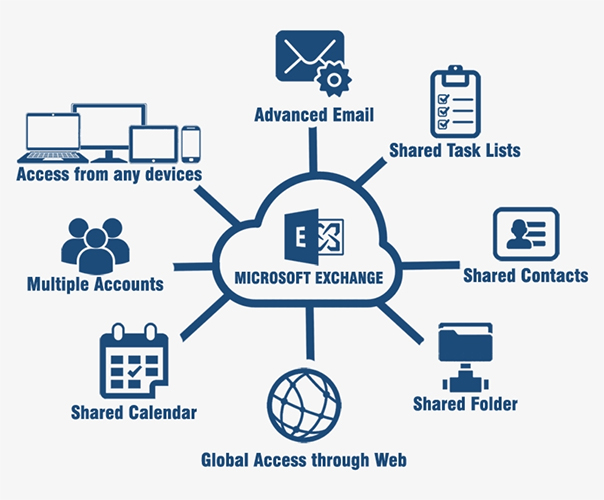
Essentially Exchange is designed to mimic an organization; the users, roles, groups, and their workflows. This helps easily relate administrative policy to each group and user quickly by administrators.
With Exchange, you can create user email addresses, assign Microsoft licenses, and security permissions.
Before Exchange, you would access a terminal inside the secure server room to conduct administrative changes. These days accessibility is prized over security with Exchange allowing administrators to conduct administrative tasks from anywhere in the world. So, what if you care about security and don’t trust your server connection?
Potential Security Threats and Vulnerabilities
Security threats and vulnerabilities exist for a server hosted in a green zone that is also connected to the internet. ‘Man in the middle’(MIM) attacks, phishing-based injection attacks, and social engineering are all common challenges for Exchange. This is because the connection between the client and server is highly vulnerable. The client device used along with any network between the user and the server will also have systemic weaknesses that can be exploited. Finally, the person using the system may at some point in time miss a key security step.
If you’ve been paying attention you would’ve already realized the lack of data control and human error are key vulnerabilities. If using hardwired connections to the server from the server room you’ll likely bypass these. Unfortunately, your time is valuable and accessibility is possible.
Let’s now take a look at what you can do to reduce your risk of being a victim of cybercrime.
Why Should You Patch Your servers?
An issue exists with the Exchange Admin Center running on an Exchange server or management server. The exploit occurs when the Exchange Admin Center is exposed to the internet and the software isn’t kept up to date. If the server does not use the Exchange Admin Center across the internet then it stops the problem. It’s so common that many organizations just by default, only use their enterprise software from the server room.
That said, what happens if you still want to use it? What can you do? Here are 5 things.
1. Common Vulnerabilities and Exposures (CVE) Website
In the event you want to use Exchange over the internet or remediate against another vulnerability, then check out the CVE website entry. This will give you complete information about any cyberattack.

Here CVE-2021-26855 allows you to identify the Exchange exploit. Essentially, an unauthenticated attacker can send HTTP requests and authenticate as the Exchange server.
If you’re familiar with ‘Server-Side Request Forgery (SSRF)’, you know once an attacker has exploited this vulnerability, they can access mailboxes and other information.
They can also escalate permissions and gain access to other sectors of your environment. No matter the route taken, once a hacker has administrative privileges, it’s all over.
2. Cybersecurity and Exchange Admin Center
Even though the CVE-2021-26855 was announced in 2021, you’ll be amazed how many companies running Exchange 2013, Exchange 2016, and Exchange 2019 have not applied updates since the release of the versions listed. I’ve had techs message me asking if they can go from an antiquated version to the latest cumulative update (CU) on Exchange as they have not been patched. The Cybersecurity & Infrastructure Security Agency website has more information about this exploit.
While it is good to want to patch, the damage could have already occurred as the attacker may already be on your system. Some attackers block servers from being patched to close a vulnerability. It makes sense then to regularly patch everything by actively checking for patches regularly as part of your administrative duties. If you don’t already, block-off time in your calendar specifically for these checking activities. You’ll also need time to test, document, and roll out the solution after a full system backup too!
3. Exchange Management Shell
Some admins aren’t comfortable using the Exchange Management Shell (EMS) and only use it to perform basic daily functions, including managing active directory with it. If this is you, then you’ll need to work on the Exchange Admin Center. This means locking the machine down and restricting internet access. Alternatively, upskill and learn EMS on a test system. Try creating scripts and running these through more rudimentary cmds.
4. Enhancing Cybersecurity with VPNs
Some admins have said, “we have a VPN so traffic is encrypted when the Exchange Admin Center is exposed to the internet”. Applications like SonicWall, FortiGate, and F5, however, have all their fair share of issues. Most VPNs aren’t true end-to-end solutions and attackers can still attack your system. Cybercriminals use traffic interception if firewalls and network devices are not patched. This means administrators could have a VPN stating it’s encrypted, but all data is routed through an attacker’s computer. Allowing them to decode encrypted data and then relaying an encrypted version to the final destination. These attacks require very little in terms of skill and one of the first attack vectors learnt by cybercriminals.

5. Cyberattacks and Vulnerabilities
So why do I keep mentioning that we need to protect Exchange and block the Exchange Admin Center?
Zero Day Logon attacks are devastating. This is where the attack halts your domain controllers, dumps the usernames and password hashes for the attacker to gain access. This affects everything including Exchange as everything stops working as there are no domain controllers.
Closing vulnerabilities should be something you’re doing constantly or must do to avoid complete shutdown or loss of data. Attackers want money and they’ll either sell your information to the highest bidder, or destroy your data if a ransom isn’t paid.
Final Thoughts
Connect with a VPN only if you have a fully patched solution. Also ensure your VPN is a true end-to-end solution that cannot be intercepted. You can get information about endpoint security from your VPN vendor. Better yet, connect to the Exchange Admin Center from the server room only. Ensure that your green zone doesn’t have an internet connection. Check you’ve closed all firewall ports. Also, always have a plan of how to recover from a cyberattack and remember all security is fallible.
FAQs
What’s Exchange Admin Center?
Exchange Admin Center is an online management solution hosted on the Exchange server. It’s optimized for on-site, online, and hybrid Exchange implementations. While this provides flexibility, it’s also a possible entry route for cybercriminals into your green zone.
Should I just patch Exchange or do a complete overhaul of my environment?
It is better to spend the time and work through your environment and update hardware and firmware. Once complete, work your way through operating system and application updates like Exchange and Active Directory.
What is a CVE?
CVE is short for common vulnerabilities and exposures. Each time an exploit or zero day is found, it is recorded on the CVE website. If you want to know more about an exploit you can find it on the Mitre website.
Are all VPNs made equal?
Unfortunately, VPNs are either ‘end-to-end’ solutions or a liability. Check yours with a vendor to ensure third party vendors can’t intercept your data. You can also try leveraging other applications to help secure your VPN connection. If you pick the wrong VPN you might be looking for a new job. Ideally, work onsite and don’t trust any outside communications; a difficult pill to swallow!
How easy is it to gain access with an interception attack?
This depends on whether you have wireless or wired-only internet. A wireless system means someone sitting in a car across the road can access your internet with a MIM attack. In fact, this attack is so common that one distro of Linux ships with these tools. Wired attacks are much more difficult because the attacker will likely need either another wireless internal system that’s connected to a server or add a LAN turtle to your network.
Resources
Microsoft documentation on CVE’s for Microsoft Exchange
View all the vulnerabilities on this site for Exchange Server.
TechGenix’s VPN Article
Get a VPN that you can trust with true ‘end-to-end’ connectivity. Use this handy guide to help you!
TechGenix’s Hybrid Exchange Storage Solution Article
Grab more storage space for Exchange with this awesome cloud storage guide.
TechGenix’s Exchange Upgrade Article
Look at this article if you want to get to the latest version of Exchange.
Techgenix’s Active Directory Patch Article
Patch Exchange then patch Active Directory as they work together. This article gives you an insight into how to do this.
Techgenix’s Backup Exchange Article
Backup exchange with this article to ensure that if your system goes down, that you can bring it back again!



