Azure AD Connect is a critical component for organizations wishing to operate Microsoft 365 in a hybrid configuration. It’s the mechanism that synchronizes the on-premises Active Directory to Azure AD. One of the things that often surprises people when deploying Azure AD Connect for the first time is just how easy the configuration process truly is. This process consists of little more than accepting a license agreement and entering credentials for your Active Directory environment and your Azure AD environment. Despite its simplicity, however, there are a few things that you need to know about Azure AD Connect before deploying it.
1. Clean up your Active Directory first
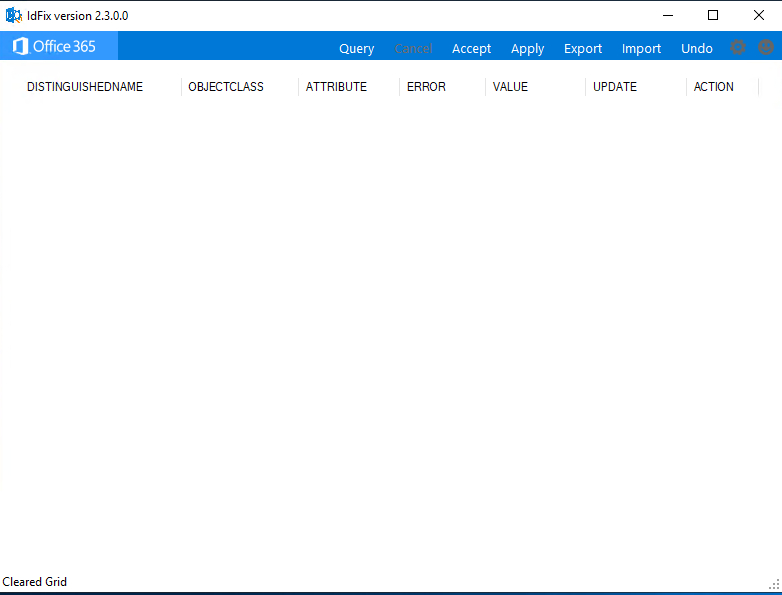
Although I have never actually seen it happen in real life, Microsoft has long warned that errors, duplicate objects, and other Active Directory health issues can derail the synchronization process. As such, Microsoft recommends using a tool called IdFix to track down any potential directory health issues before deploying Azure AD Connect.
According to Microsoft, about 60% of all of the directory synchronization errors that they see are tied to either malformed proxy addresses or user principal names. The IdFix tool won’t fix every directory health issue, especially if the Active Directory environment has become corrupted. But it will identify and correct most of the issues known to cause problems with Azure AD Connect. As such, it is a good idea to run IdFix before you deploy Azure AD Connect.
You can see what this tool looks like in the image below. In this case, the tool did not find any errors, so most of the window is blank. Even so, the menu items at the top illustrate how you can easily accept and apply the fixes that the tool recommends.
2. TLS requirements for deploying Azure AD Connect
Another thing that you need to be aware of before deploying Azure AD Connect is that it uses TLS encryption. In the past, the tool’s dependency on TLS was seamless. However, the current version of the tool requires TLS 1.2, which is not enabled by default in Windows Server. Therefore, if you attempt to install Azure AD Connect without first enabling TLS 1.2, you will receive an error message.
Unfortunately, enabling TLS 1.2 isn’t as simple as installing a Windows Server feature or downloading an add-on. Instead, the process involves configuring several registry keys. However, because the process of manually enabling TLS 1.2 is somewhat Tedious, Microsoft created a PowerShell script that automates the process.
I ran this script on one of my servers before installing Azure AD Connect and found that it worked flawlessly. In case you are wondering, the PowerShell script does not require any user input. Just run it in an administrative PowerShell session, and TLS 1.2 will be enabled.
3. Use a dedicated server
One of the most important things you should do regarding setting up Azure AD Connect is to deploy it on a dedicated server (or, more likely, virtual machine). There are two reasons why this is so important.
The first reason is that Azure AD Connect is a very sensitive application. Remember, it requires access to both your Active Directory environment and to your Microsoft Azure environment. As such, Microsoft recommends that you treat Azure AD Connect just as you would a domain controller, with regard to security. Running Azure AD Connect on a dedicated physical or virtual machine helps isolate it from any other processes that might compromise its security.
The other reason why it is so important to run Azure AD Connect on a dedicated machine is because Microsoft requires Azure AD Connect to be installed on a domain-joined system running Windows Server 2016 or higher. Additionally, this server has to have the full desktop experience (the GUI) enabled. Since Windows servers are often installed without a GUI, the GUI requirement alone will often mean that Azure AD Connect will need to be installed on its own server.
4. Multifactor authentication
For quite some time now, Microsoft has strongly recommended that organizations use multifactor authentication. Azure AD Connect can be used with or without multifactor authentication, although using multifactor authentication can help to improve your overall security.
If your organization is using multifactor authentication, it is important to make sure that one specific URL is included on the list of trusted sites. This URL is: https://secure.aadcdn.microsoftonline-p.com/
5. Be sure to enable password writeback
Once Azure AD Connect has been installed and configured, it is important to enable password writeback. The idea behind this is relatively simple. When Microsoft first created Azure AD Connect, it was largely intended for use as a unidirectional synchronization tool. Data was synchronized from the on-premises environment to the Azure cloud. At the time, Microsoft was likely envisioning a world where everything resided in the cloud and saw Azure AD Connect as a tool that could help with Active Directory migrations to the cloud.
Today, of course, things are a little bit different. Hybrid environments are the norm. Thankfully, Azure AD Connect has at least some degree of support for two-way synchronization. Having said that, though, you will have to manually enable password writeback. Otherwise, if a user happens to change their password in the cloud, then that password change will not apply to the on-premises environment. The user can end up with one password on-premises and a different password in Azure.
Enabling password writeback is simple to do. Once Azure AD Connect is installed, just open it up and go into the settings. You can find the checkbox for enabling password writeback within the Optional Feature section.
Deploying Azure AD Connect: Easy — if consider the concerns
Azure AD Connect is a critical component of the hybrid Active Directory. Even though Microsoft has made it super simple to deploy Azure AD Connect, it is worth your time to make sure that you address these various concerns before you attempt to synchronize your Active Directory to the cloud.
Featured image: Shutterstock




Note that enable password writeback requires Microsoft 365 Business Premium licensing see https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-sspr-licensing which is a real pain if you don’t have that like my company doesn’t.