Introduction
The Microsoft Forefront Threat Management Gateway (TMG) 2010 firewall relies heavily on supporting infrastructure services for secure operation and optimum performance. Network interface configuration, and name resolution in particular, play critical roles, especially when the TMG firewall is configured as a secure web gateway (forward or outbound proxy). In my experience performing new implementations or assessing the configuration of existing ones, poorly performing or improperly configured name resolution is a common issue I encounter. In this article we will discuss network interface configuration and DNS server requirements for proper name resolution for unihomed and multihomed TMG firewalls.
DNS Server Requirements
When selecting a DNS server to use in support of the TMG firewall, there are a few important considerations to be made. With very few exceptions, the TMG firewall should be configured to use an internal DNS server that is capable of resolving hostnames for the private internal namespace as well as the public external namespace (e.g. www.bing.com). To ensure reliable operation and optimum performance, the DNS server should be well connected and have sufficient capacity to handle the volume of name resolution requests that your implementation will require. This will depend greatly on the number of users connecting to the TMG firewall and how those clients are connecting. Web proxy and TMG Firewall clients will rely on the TMG firewall to provide hostname resolution, increasing the load on the DNS server that the TMG firewall is configured to use. SecureNAT clients perform their own hostname resolution, so TMG relies less on its configured DNS servers. If the configured DNS server is over utilized, or there are connectivity issues between the TMG firewall and the DNS server, the TMG firewall is going to suffer for it. This typically results in web pages that load very slowly or not at all, and intermittent authentication prompts for users who should be authenticated transparently using NTLM or Kerberos.
Network Interface Configuration
Configuring the network interface for a TMG firewall with a single network interface (unihomed) is simple and straightforward; IP address, subnet mask, default gateway, and DNS servers are all configured on the internal network interface. The situation becomes more complex when the TMG firewall has multiple network interfaces (multihomed). If the TMG firewall has more than one network interface, each interface will have its own unique IP address and subnet mask settings. However, regardless how many network interfaces your firewall has you can only have ONE default gateway. I cannot emphasize this point enough. The TMG firewall can have the default gateway assigned to only one network interface – the External network interface. Never configure the default gateway on any interface other than the External interface (with ISP redundancy enabled, both External network interfaces will require default gateways. For more details regarding ISP-R please read Exploring ISP Redundancy in Forefront TMG. In order to reach remote subnets on the Internal or any perimeter networks, persistent static routes will need to be configured manually on each network interface as required.
Network Interface Binding Order
For TMG firewalls that have more than one network interface, another crucial configuration setting (and one that is often overlooked!) is the network interface binding order. On multihomed TMG firewalls, open the Network and Sharing Center control panel applet and then click the Change adapter settings link. Next, click the alt key to reveal the drop-down menu and select Advanced then Advanced Settings…
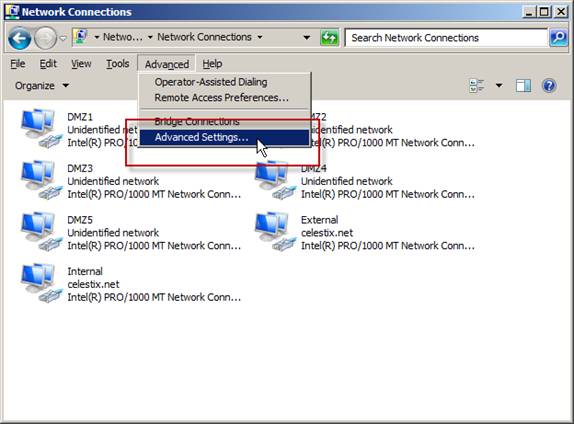
Figure 1
Select the Adapters and Bindings tab and make certain that the internal network interface is listed first in this ordered list. If it is not, highlight the internal network interface, then click the green up-arrow on the right side and move it to the top.
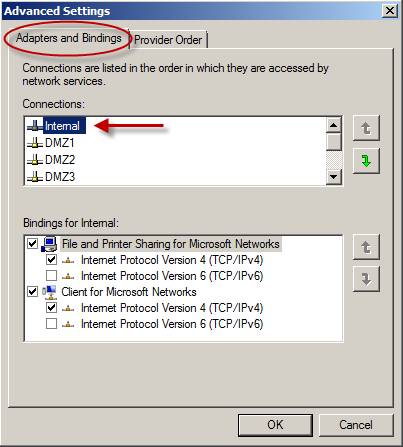
Figure 2
The order of the remaining network interfaces is not critical, but I do prefer that the External network interface be listed last.
Configuring DNS Servers
DNS servers should be configured on the internal network interface only. Do not configure DNS servers on any other network interface. A common mistake many administrators make is to specify their ISP’s DNS servers on the External network interface in addition to the internal DNS servers configured on the internal network interface. DNS servers should be configured on one and only one network interface – the internal interface.
An Exception to the Rule
There is one very specific deployment role in which it is perfectly acceptable to configure DNS servers on the External interface, and that is when the TMG firewall is configured as a bastion host. In this very specific role the TMG firewall is not a domain member and does not communicate with internal network resources. This is the only scenario where specifying your ISPs DNS servers on the External interface is recommended.
Internal Root DNS
In some instances, internal DNS servers may not be capable of resolving external public hostnames. This happens when internal DNS servers act as root servers for your internal namespace. The requirements for the TMG firewall remain unchanged, however. The TMG firewall still requires a DNS server that is capable of resolving both internal private and external public hostnames.
In this scenario you will need to configure a DNS server for the TMG firewall to use that meet these requirements. The best way to address this issue is to configure a dedicated caching-only DNS server that is configured to use conditional forwarding. Requests for internal private domain resources are forwarded to your internal DNS servers, while all other requests are resolved using root hints or are forwarded directly to your ISPs DNS servers.
Summary
Proper network interface binding order and name resolution are essential to the security and performance of the TMG firewall. A TMG firewall with a single network interface (unihomed) should be configured as normal, with an IP address, subnet mask, default gateway, and DNS server. A TMG firewall with multiple network interfaces (multihomed) should have the default gateway configured only on the External network interface, and DNS servers configured only on the internal network interface. Static routes should be configured on those network interfaces other than the External network interface that require connectivity to remote subnets. By following these guidelines you will have eliminated some of the most common configuration mistakes made by TMG firewall administrators, ensuring that your firewall will be performing optimally.



