Active Directory is the biggest authentication application used in organizations. Active Directory controls security and directly affects how organization employees do their job. Active Directory can provide authentication with or without SSL. SSL is a secure way to authenticate external clients coming to Active Directory for authentication. The default installations of Active Directory do not implement SSL. It is important to note that every domain controller needs to be checked whether the SSL is enabled or not. Whether you perform the SSL check as part of your health assessment procedure or a requirement to ensure clients are authenticating using SSL. In this article, we provide a PowerShell script that can be used to check the status of SSL on all domain controllers.
Requirements
Before executing the SSL PowerShell script explained in the later section of this article, make sure all domain controllers are reachable from the computer from where you plan to run the PowerShell script and you have created a file under C:\Temp\DomainControllers.TXT that contains the domain controller names. The PowerShell script uses C:\Temp\DomainControllers.TXT file, collects the name of the domain controller, and then initiates an SSL connection.
What does the PowerShell script do?
The PowerShell script performs the following operations:
- Connects to domain controller using the ADSI and LDAP.
- Collects SSL status from the domain controller.
- Records status of SSL for each domain controller in a CSV file generated by the PowerShell script.
PowerShell script for checking domain controllers SSL status
Executing this PowerShell script will generate a report in CSV format. The report file can be found at C:\Temp\DCSSLStatus.CSV.
$TestCSVFile ="C:\Temp\DCSSLStatus.CSV"
Remove-Item $TestCSVFile
$UniqueTest = "DCSSLStatus"
$CurrentLoc="C:\Temp"
$STR = "Domain Controller, Is SSL Enabled?, Final Status"
Add-Content $TestCSVFile $STR
$TotNo=0
$ItemCount=0
$TestText = "Please check result"
$TestStatus="Completed"
$SumVal = "NA"
$AnyGap = "No"
$GDCList = "C:\Temp\DomainControllers.TXT"
Foreach ($ItemName in Get-Content "$GDCList")
{
$SSLOrNot = ""
$LDAPS = [ADSI]"LDAP://$($ItemName):636"
try {
$Connection = [adsi]($LDAPS)
} Catch {
}
If ($Connection.Path) {
$SSLOrNot="Yes"
} Else {
$SSLOrNot="Not Enabled"
$AnyGap = "Yes"
}
IF ($SSLOrNot -eq "Not Enabled")
{
$STR = $ItemName+","+$SSLOrNot+", Not Ok"
Add-Content $TestCSVFile $STR
}
IF ($SSLOrNot -eq "Yes")
{
$STR = $ItemName+","+$SSLOrNot+", Ok"
Add-Content $TestCSVFile $STR
}
}
$AnyGap = "Yes"
IF ($AnyGap -eq "Yes")
{
$TestText = "Note all domain controllers have SSL enabled."
$SumVal = ""
$TestStatus="High"
}
else
{
$TestText = " "
$SumVal = ""
$TestStatus="Passed"
}
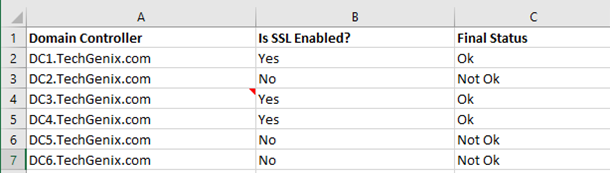
Once the PowerShell script has finished executing, you will see a CSV file; C:\Temp\DCSSLStatus.CSV which contains the domain controller names and their SSL status. As you can see in the output below, the script checked six domain controllers in TechGenix.com domain and found that DC2.TechGenix.com, DC5.TechGenix.com and DC6.TechGenix.com do not have SSL enabled.
Important: It is certainly not necessary that all domain controllers in an Active Directory forest will have SSL enabled. However, it is recommended to enable SSL on domain controllers that authenticate external clients. You can run the script weekly or monthly to ensure SSL is configured on the desired domain controllers. The script was obtained from DynamicPacks IT Scanner which is capable of doing a complete health and risk assessment of Active Directory forests.
Featured image: Shutterstock




Thanks for sharing. Two small mistakes:
$AnyGap = “Yes” # Why is this being forced, was it for temporary testing?
$TestText = “Note all domain controllers have SSL enabled.” # Typo? Note=Not
No need to publish this comment, it’s just to improve the post.