There are many ways to steal your company’s information. We are going to explain a few scenarios where employees send documents via email or copy them to USB sticks or external hard drives. They can easily find information and documents related to your business and have it distributed to your competitors. Apart from copying data to USB sticks, they can upload data to a Dropbox account. Since a Dropbox account can be accessed from outside company premises, users can easily access upload documents and distribute them for monetary purposes. Here are a few common examples of insider cybersecurity threats that are seen in today’s environment:
User copying Trojans or malicious programs: A Trojan program is a malicious code that is written to accept command requests from a server Trojan program running inside or outside the company network. A Trojan is always considered a dangerous threat. It allows a hacker to gain access to a complete network of an organization. Once a Trojan becomes active in one of the systems in a production environment, it silently runs in the background and waits for the command requests coming from a server Trojan program. Some Trojans have the ability to provide remote control of the systems. Any user who is not happy with the organization can copy Trojan programs.
Unhappy employees seeking revenge: An employee who is not happy with the organization may just start deleting files or corrupt company assets such as company servers hosting a SQL database or other valuable documents.
Hackers who are versed with technology: Hackers who are well-versed with the technology can infiltrate the company network by using tools and techniques designed by them. In most of the cases, hackers always work with an employee to gain access to the network. This type of threat is generally called social engineering. An outsider who has technical expertise but cannot gain access to the company information from outside the company network works closely with an employee to get information about the company network. For example, an outsider can provide scripts to an employee to search through the Active Directory to check if any organizational units in Active Directory have full permissions assigned to the Everyone account. Since every user in Active Directory has at least read access to the Active Directory, the user can run the script provided by an outsider and generate a permission report on organizational units. The outsider can review the report and then take destructive actions.
Checking full permissions on organizational units
The PowerShell script below can check if full control permission for the Everyone account is assigned on organizational units in an Active Directory domain and generate a report.
$TestCSVFile ="C:\Temp\OuPermissions.CSV"
Remove-Item $TestCSVFile
$STR = "OU Name, Has EVERYONE Full Control?, AD Domain, Final Status"
Add-Content $TestCSVFile $STR
$TotNo=0
$ItemCount=0
$TestText = "Please check result"
$TestStatus="Completed"
$SumVal = "NA"
$AnyGap = "No"
$GDomList = “C:\Temp\DomainList.CSV”
ForEach ($ThisDomain in Get-Content "$GDomList")
{
$AllOUs = Get-ADOrganizationalUnit -Filter * -Server $ThisDomain
$TotOUsNow = $AllOUs.Count
$TotWithFullControlsCount = 0
ForEach ($EachOU in $AllOUs)
{
$ThisDName = $EachOU.DistinguishedName
$DispName = $EachOU.Name
$R=(Get-ACL "AD:$((Get-ADOrganizationalUnit -Server $ThisDomain -Identity "$ThisDName").distinguishedname)").access | Select-Object IdentityReference,ActiveDirectoryRights
$ThisDName
$FoundOrNot = "No"
ForEach ($Perms in $R)
{
$PermNow = $Perms.ActiveDirectoryRights
$IDRef = $Perms.IdentityReference
IF ($PermNow -eq "GenericAll" -and $IDRef -eq "Everyone")
{
$FoundOrNot = "Yes"
$AnyGap = "Yes"
break
}
}
IF ($FoundOrNot -eq "Yes")
{
$STR = $DispName+",Yes,"+$ThisDomain+",NOT OK"
Add-Content $TestCSVFile $STR
}
else
{
$STR = $DispName+",NO,"+$ThisDomain+",OK"
Add-Content $TestCSVFile $STR
}
}
}
IF ($AnyGap -eq "Yes")
{
$TestText = " "
$SumVal = ""
$TestStatus="High"
}
else
{
$TestText = " "
$SumVal = ""
$TestStatus="Passed"
}
Once the script has finished executing, a report can be seen in C:\Temp\OuPermissions.CSV, which contains the list of organizational units and Everyone account full control permission status as shown in the screenshot below:
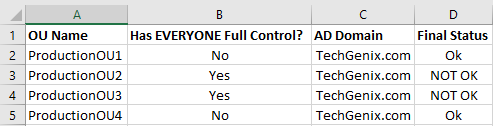
As you can see in the screenshot, ProductionOU2 and ProductionOU3 have full control permission assigned to the Everyone account.
The script was retrieved from DynamicPacks IT Scanner, a tool designed to perform cybersecurity assessments in a production environment. The DynamicPacks IT Scanner can perform 45 cybersecurity checks and generate a report with affected objects. You can see in the screenshot below, taken from DynamicPacks IT Scanner, shows the same information.
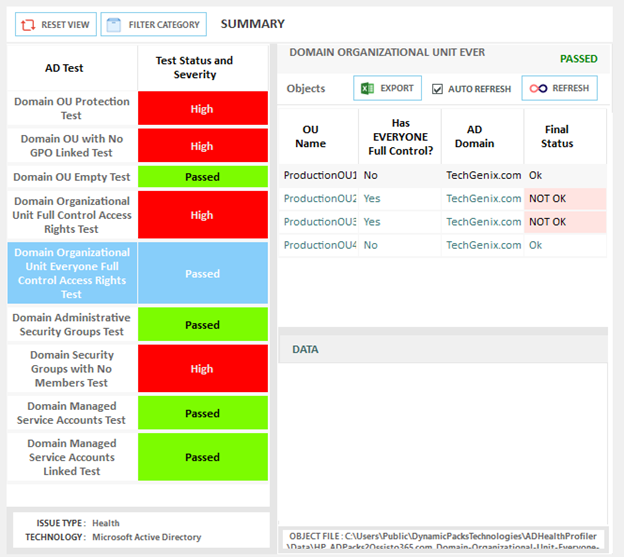
Note: Once an attacker knows about the full control permission on organizational units, they can delete or modify the objects. For example, an attacker can place a script to run for each user when they log on to their system, which in turn, might give the attacker access to other information on users’ computers.
Take appropriate action
Whether it’s an employee who is deleting files or a hacker who is trying to infiltrate the company network, there are ways to eliminate the security risks. As an IT admin, you are required to protect company assets from both nontechnical and technical users. You might not be able to detect and prevent hacks unless you take necessary actions such as implementing a tool that can do an assessment of Active Directory under your cybersecurity program. We provided a PowerShell script that could help you check if any OU in the Active Directory domain has Everyone with full control permission assigned and then take actions accordingly.
Featured image: Shutterstock



