Product: GFI LanGuard
Product Homepage: click here
Free Trial: click here

I have always said that network security ultimately boils down to answering two really basic questions — where are the vulnerabilities on my network and what can I do to address those vulnerabilities. As simple as these questions may be, they have historically been very difficult questions to answer. Recently, I had a chance to review a product from GFI that may better equip security admins to answer these two questions. GFI LanGuard is designed to perform vulnerability assessments of the devices on your network, and then help you to remediate any vulnerabilities that are detected.
Deployment process
In preparation for writing this review, I downloaded the LanGuard free trial and installed it to a virtual machine within a dedicated Windows domain. In doing so, I found the installation process to be completely straightforward. LanGuard requires SQL Server, but since my lab environment contains fewer than 500 machines, I was able to use the included copy of SQL Server Express, which was installed automatically as a part of the deployment.
Adding computers
Once I had finished installing GFI LanGuard, the next thing that I attempted to do was to tell LanGuard which computers I wanted it to monitor. For the purposes of this review, I decided to monitor several domain-joined virtual machines running Windows Server 2016. It is worth noting that although I am limiting my review to machines running Windows, GFI LanGuard is also designed to work with Linux and Apple OS X systems
I found the process of adding the VMs to the GFI LanGuard console to be relatively straightforward. Because my LanGuard server was domain joined, LanGuard already knew about my domain. I was, therefore, able to right-click on the name of the domain and then use the Synchronize With Active Directory option to populate LanGuard with a list of the domain-joined computers.
The next step in the process was to deploy an agent to the managed computers. The agent deployment process happens automatically on a scheduled basis. However, there is a way to speed things up by forcing an immediate agent deployment.
Although the agents deployed without issue, it took some time for all of the agents to query their respective computers and populate the LanGuard console. I have been told that this process takes about a day to complete. In my case, I installed the agents just prior to leaving town for the weekend. By the time I returned on Monday morning, the console had been fully populated.
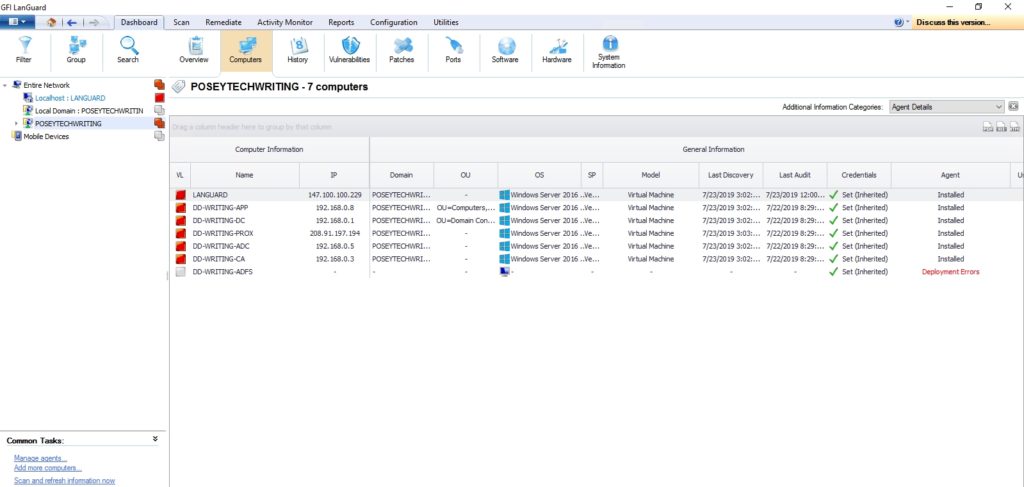
You can see what the computer information looks like in the screenshot below. Incidentally, the reason why the last computer on the list shows a deployment error is because memory limitations prevented me from turning on that particular virtual machine. As such, the error is not an indication of a problem with GFI LanGuard.
Addressing vulnerabilities
If you look at the previous screenshot, you will notice that the list of computers contains a column called VL, which is short for “vulnerability level.” The VL column contains a color code that corresponds to the perceived level of vulnerability. In my case, each computer is considered to be highly vulnerable.
Clicking on an individual computer takes you to a dashboard that provides information about that specific system. If you look at the screenshot below, you can see that in addition to providing some basic computer details, LanGuard lists the top five issues that need to be addressed, as well as the vulnerability trend over time.
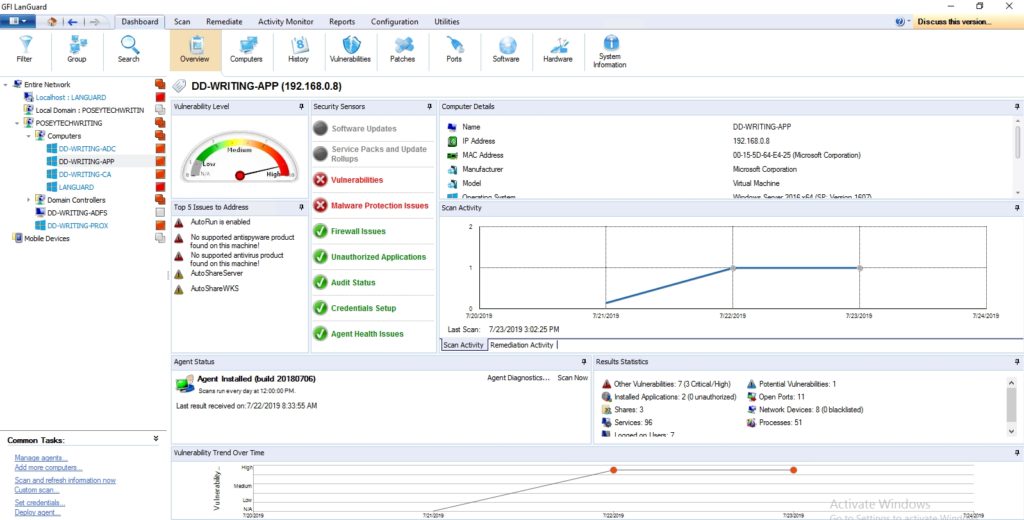
As helpful as it may be to learn what vulnerabilities may exist on a particular machine, it is much more important to remediate those vulnerabilities. Although you can, of course, address vulnerabilities manually, LanGuard gives you remediation capabilities. You can right-click on a computer, a group of computers, or even an entire domain to be taken to the Remediation Center. The Remediation Center provides options for installing or uninstalling software updates, deploying custom software, uninstalling unauthorized applications, fixing problems with malware protection, and providing remote support via an RDP connection.
Patch management
One of GFI LanGuard’s key capabilities is that of detecting and applying missing patches. LanGuard is not limited to solely scanning for missing operating system patches. The software has built-in patch management capabilities for software from a huge number of vendors. You can see some of these vendors listed on the Automatic Approval screen, shown in the screenshot below.
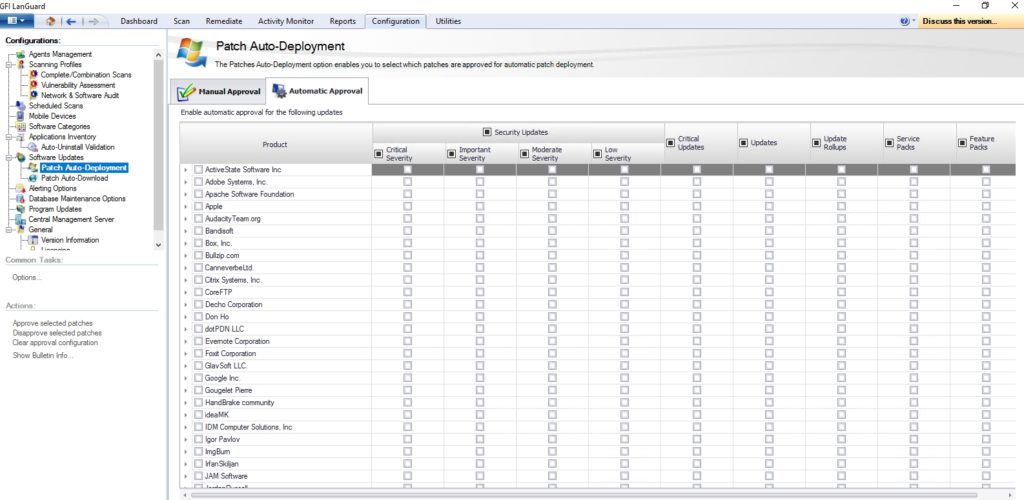
This brings up an important point. GFI LanGuard downloads patches automatically, but the administrator has quite a bit of control over the download process. For instance, an admin might opt to only download patches from specific vendors or for specific products. There are also ways of controlling the number of download threads used, and which patch languages are downloaded. Incidentally, if you have a WSUS server, LanGuard can be configured to use it rather than performing redundant patch downloads.
Missing patch scans
Although GFI LanGuard allows you to perform a fully comprehensive scan of the computers on your network, the product also provides several different scan profiles. These profiles are handy if you want to check something specific without taking the time to scan everything. I decided to try out the scanning profile named Missing Patches to see how it worked. This, of course, meant running a manual scan, but scans can be configured to occur automatically. You can see what the scanning process looks like in the next screenshot.
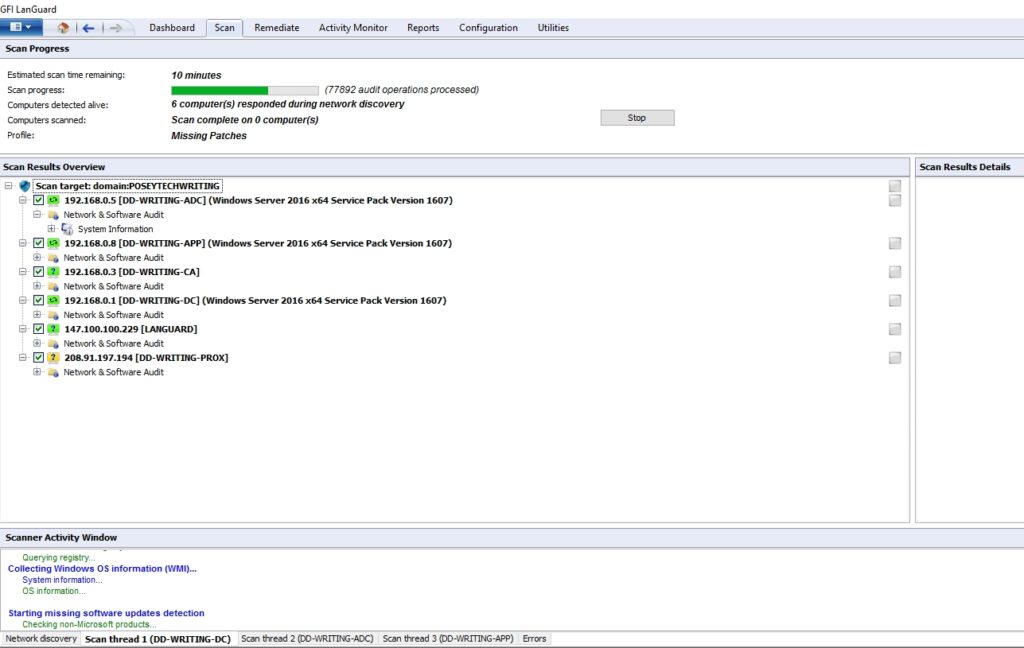
The scanning process completed relatively quickly. It took about 15 to 20 minutes to scan my test VMs. In all fairness, though, all of those VMs are on the same host, and the host server’s resources were nearly depleted. I am guessing that a scan would probably complete more quickly in a production environment.
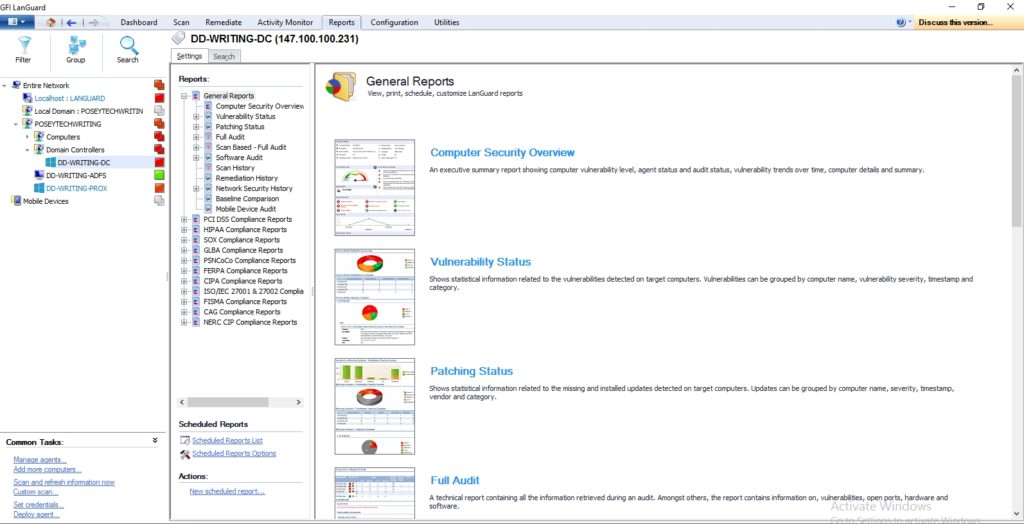
Once the scan has completed, you can easily perform a remediation that collectively deploys all of the missing patches. GFI LanGuard also includes a really nice reporting engine where you can find detailed information on the health of your systems. In addition to the general reports such as vulnerability status reports and patching status reports, the reporting engine includes a number of compliance reports that will be unquestionably useful to those who need to comply with regulations such as PCI DSS or HIPAA. You can see the reporting screen in the next screenshot.
The verdict
Whenever I write a review for TechGenix, I like to conclude the process by giving the product a numerical score, ranging between zero and five stars, with five stars being the highest possible score. In the case of GFI LanGuard, I decided to go with a score of 4.7, which is a gold star review. Overall, I really liked the software. I found it to be mostly intuitive, and I think that it would do an excellent job of helping administrators to figure out which computers on their networks require attention.
In the process of writing this review, I did encounter some errors referencing insufficient memory. However, once I added a bit of memory, GFI LanGuard worked exactly as expected. Incidentally, working through those memory issues gave me a chance to look at the product’s documentation, which I found to be well-written and easy to follow.
Rating 4.7/5


