If you would like to read the next part in this article series please go to How I Cracked your Windows Password (Part 2).
Introduction
Passwords tend to be our main and sometimes only line of defense against intruders. Even if attackers do not have physical access to a machine they can often access a server through the remote desktop protocol or authenticate to a service via an outward facing web application.
The purpose of this article is to educate you on how Windows creates and stores password hashes, and how those hashes are cracked. After demonstrating how to crack Windows passwords I will provide some tips for ensuring you are not vulnerable to these types of attacks.
How Windows Stores Passwords
Windows-based computers utilize two methods for the hashing of user passwords, both having drastically different security implications. These are LAN Manager (LM) and NT LAN Manager (NTLM). A hash is the result of a cryptographic function that takes an arbitrarily sized string of data, performs a mathematical encryption function on it, and returns a fixed-size string.
LM Password Hashes
The LAN Manager hash was one of the first password hashing algorithms to be used by Windows operating systems, and the only version to be supported up until the advent of NTLM used in Windows 2000, XP, Vista, and 7. These newer operating systems still support the use of LM hashes for backwards compatibility purposes. However, it is disabled by default for Windows Vista and Windows 7.
The LM hash of a password is computed using a six-step process:
- The user’s password is converted into all uppercase letters
- The password has null characters added to it until it equals 14 characters
- The new password is split into two 7 character halves
- These values are used to create two DES encryption keys, one from each half with a parity bit added to each to create 64 bit keys.
- Each DES key is used to encrypt a preset ASCII string (KGS!@#$%), resulting in two 8-byte ciphertext values
- The two 8-byte ciphertext values are combined to form a 16-byte value, which is the completed LM hash
In practice, the password “PassWord123” would be converted as follows:
- PASSWORD123
- PASSWORD123000
- PASSWOR and D123000
- PASSWOR1 and D1230001
- E52CAC67419A9A22 and 664345140A852F61
- E52CAC67419A9A22664345140A852F61
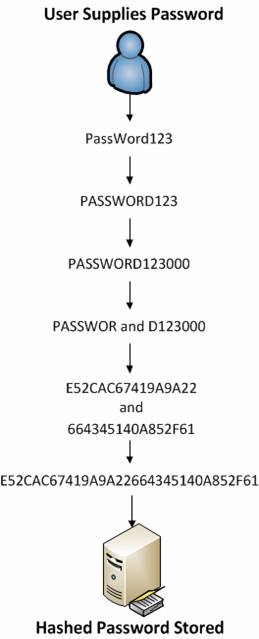
Figure 1: A password transformed into an LM hash
LM stored passwords have a few distinct disadvantages. The first of these is that the encryption is based on the Data Encryption Standard (DES). DES originated from a 1970s IBM project that was eventually modified by NIST, sponsored by the NSA, and released as an ANSI standard in 1981. DES was considered secure for many years but came under scrutiny in the nineties due to its small key size of only 56-bits. This came to a head in 1998 when the Electronic Frontier Foundation was able to crack DES in about 23 hours. Since this, DES has been considered insecure and has since been replaced with Triple-DES and AES. In short, it’s another encryption standard that has fallen victim to modern computing power and can be cracked in no time at all.
Perhaps the biggest weakness in the LM hash is in the creation of the DES keys. In this process, a user supplied password is automatically converted to all uppercase, padded to fourteen characters (this is the max length for an LM hashed password), and split into two seven character halves. Consider that there are 95 to the power of 14 different possible passwords made up of 14 printable ASCII characters, this decreases to 95 to the power of 7 possible passwords when split into a 7 character half, and then decreases to 69 to the power of 7 possible passwords when you are only allowed uppercase ASCII characters. Essentially, this makes the use of varying character cases and increased password length nearly useless when the password is stored as an LM hash, which makes LM passwords incredibly vulnerable to brute force cracking attempts.
NTLM Password Hashes
NT LAN Manager (NTLM) is the Microsoft authentication protocol that was created to be the successor of LM. NTLM was accepted as the new authentication method of choice and implemented with Windows NT 4.
The creation of an NTLM hash (henceforth referred to as the NT hash) is actually a much simpler process in terms of what the operating system actually does, and relies on the MD4 hashing algorithm to create the hash based upon a series of mathematical calculations. After converting the password to Unicode, the MD4 algorithm is used to produce the NT hash. In practice, the password “PassWord123”, once converted, would be represented as “67A54E1C9058FCA16498061B96863248”.
MD4 is considered to be significantly stronger than DES as it allows for longer password lengths, it allows for distinction between uppercase and lowercase letters and it does not split the password into smaller, easier to crack chunks.
Perhaps the biggest complaint with NTLM created hashes is that Windows does not utilize a technique called salting. Salting is a technique in which a random number is generated in order to compute the hash for the password. This means that the same password could have two completely different hash values, which would be ideal.
With this being the case, it is possible for a user to generate what are called rainbow tables. Rainbow tables are not just coffee tables painted with bright colors; they are actually tables containing every single hash value for every possible password possibility up to a certain number of characters. Using a rainbow table, you can simply take the hash value you have extracted from the target computer and search for it. Once it is found in the table, you will have the password. As you can imagine, a rainbow table for even a small number of characters can grow to be very large, meaning that their generation, storage, and indexing can be quite a task.
Conclusion
In the first part of this article we have examined password hashes and the mechanisms Windows utilizes to create and store these values. We’ve also touched upon the weaknesses of each method and possible avenues that can be used to crack those passwords. In the follow-up to this article we will actually step through the process of extracting and cracking these hashes to demonstrate their weaknesses. Once demonstrated I will provide tips for providing additional layers of security and creating a properly strengthened password.
References
- http://technet.microsoft.com/en-us/library/cc875839.aspx
- http://technet.microsoft.com/en-us/library/cc512606.aspx
**Note: After the publication of this article, it was found that the description of the NTLM password creation functionality was incorrectly described. The author fixed this issue, and the article was republished with these corrections in 12/2012. – Chris Sanders
If you would like to read the next part in this article series please go to How I Cracked your Windows Password (Part 2).




Hello,
Thank you very much for very informative article on hashes. It helped me a lot to understand the foundations of hashing 😉
All best,
Mike
Nicely written! Thanks
“Rainbow tables are not just coffee tables painted with bright colors”
Cracked me up
Great article, but 2 questions though, what type of hashing technique does windows 10 normally use and if you switched from NTLM hashes to LM hashes would the previous hashes change?