The Internet has absolutely overwhelmed humanity. That is not really an overstatement. It’s probably going to stand as the biggest game-changer in the lifecycle of the human race. There is nothing that equals it thus far — well, perhaps the discovery of fire and a couple of other massive developments. It has made the world flatter, that is for sure! However, not many of us truly realize the integral changes that Internet itself has undergone recently, and the ones it’s going to undergo soon. Enter Internet Protocol version 6, better known as IPv6.
Contextualizing the IPv6 discussion
Fast reverse to 2012, and IPv6 was a fascinating topic of discussion. At the time, the protocol was nascent, and its understanding among enterprises was limited. Today, the number of connected devices is so humongous that nobody could have predicted it five years back. Gartner suggests that by the end of 2017, there will be more than 8.4 billion connected devices across the globe. And this number will exceed 20 billion by 2020. More the number of devices, more the number of IP addresses.
Why is IPv6 a solution?
For starters, IPv6 supports a lot more IP addresses than IPv4. Today, IPv6 Is considered as the way forward, at least in terms of how the Internet will be managed in the near future. Apart from extending support for more IP addresses, IPv6 acknowledges the needs for more secure Internet connectivity and overcomes quite a few limitations posed by IPv4 in this regard.
That IPv6 is more efficient and effective than IPv4 is well established and not even in the scope of this guide. What’s more important is for enterprises to assess whether they understand the implications and are prepared in terms of necessary infrastructure to support the changeover.
More in IPv6
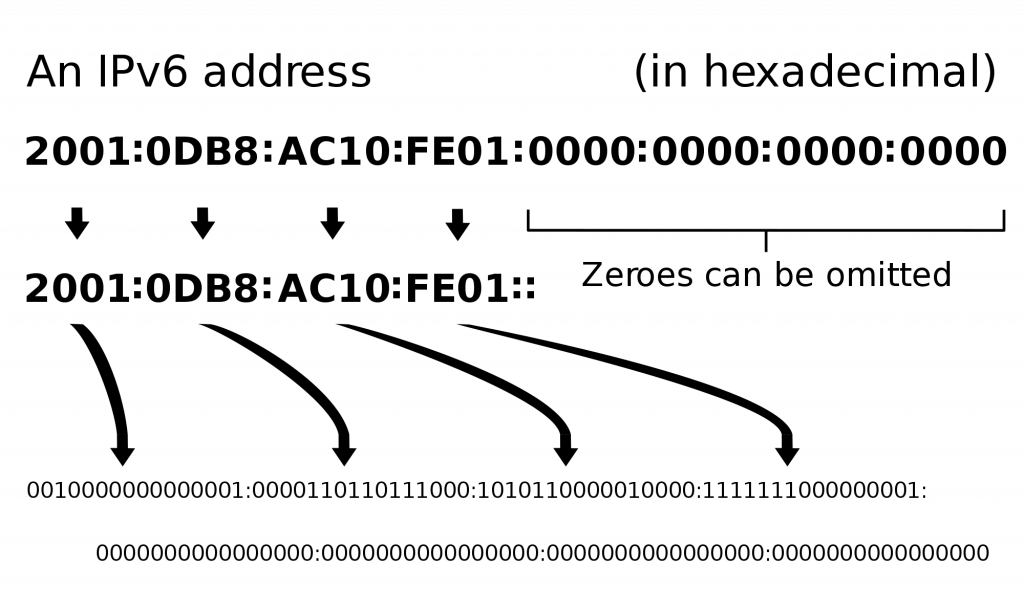
Surprise — IPv6 has been available for many years. In 2016, its deployment was 10 percent complete, and it was 20 years after Internet Engineering Task Force (IETF) finalized the IPv6 concept in 1996 and implemented it for the first time. IPv6 is about extending IP addresses from 32 bits to 128 bits. Here are the numbers — IPv4 allows about 4.3 billion IP addresses, and IPv6 allows 340 undecillion addresses (that’s 3.4 x 1038).
Wow, that is about as many stars that are out there!
Technical aspects IT personnel need to understand
Apart from saving the world from the catastrophe of Internet protocol addresses running out, IPv6 offers some technical advantages that make data transfers on the Internet more efficient and secure. Some of these benefits are:
- In IPv4, checksum is calculated at every router hop; this makes data transmission slow because the router spends time in this calculation. In IPv6, this is done away with because packet handling is more efficient.
- IPv6 reduces the routine table size and makes routing more hierarchical and clean.
- In IPv6, fragmentation is handled at source devices, unlike IPv4 where this is done at router level. This is done using a protocol to discover the path’s maximum transmission unit.
- Also, IPv6 uses multicast address routing. This allows bandwidth-intensive web traffic to be transmitted simultaneously to multiple destinations, unlike the broadcast communication method used in IPv4.
Before enterprises migrate to IPv6, this is what they need to understand and be prepared about:
Networking IT staff’s technical preparedness
Implementing IPv6 in the way they implemented IPv4 — that’s a guaranteed path to failure for enterprise IT. Instead, enterprises must realize the need to train their IT staff, particularly the networking personnel, in IPv6. This will make sure that they know how to specifically implement IPv6.
Managing IPv4 and IPv6 at the same time can bring in additional complexities. IPv6 demands that networking engineers understand the new approach to networking. In pretty much everything — right from troubleshooting practices to firewall implementations — there are significant differences in IPv6, which need to be accounted for.
Infrastructure and hardware preparedness
The migration from IPv4 to IPv6 involves several moving parts: switches, routers, laptops, application settings, smartphones, laptops, VoIP phones, firewalls, etc. All these will need to be upgraded, reconfigured, and tested when the migration takes place. Plus, for all these elements, enterprises will need to literally work day and night to upgrade procedure documentation and policy settings to reflect the new reality.
Consider a situation where your enterprise server is on IPv4 but your firewall is not. That’s as good as working without a firewall, exposing your digital assets to malware attacks — and we saw enough virtual attacks in the movie “Blackhat” and we saw some of that in a stellar episode of “The Good Wife” in Season 6 where Kalinda had to save the day. The solution — meticulously planned migrations with infrastructure experts in the thick of things at every point.
Cutover preparedness
This is the critical project phase when your enterprise endpoints operate with an IPv6 as well as an IPv4 address. It’s commonplace for enterprises to realize that some devices are not compatible with IPv6, causing serious disruptions in communication channels.
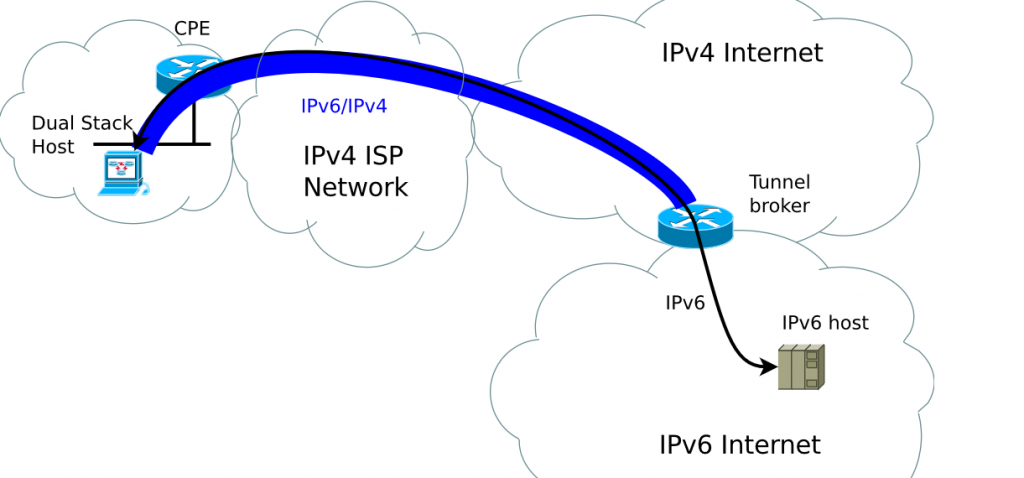
Network tunneling is a solution (this has nothing to do with the tunnel in “Logan Lucky” that they used to steal all that NASCAR money with – completely different!). It’s an approach that enables data transmission between IPv4 and IPv6. However, enterprises just can’t absorb the security threats that excessive network tunneling can invoke. Automated tunneling setups, for instance, could pose serious challenges for enterprise cybersecurity in terms of detecting potential cyberattacks. So, identify potential problem-causing endpoints beforehand instead of depending on tunneling.
Best practices during migration planning and execution
Here are some of the best practices that your network engineering, infrastructure, and cybersecurity teams need to keep in mind as they plan the switchover from IPv4 to IPv6.
- Network structure needs a lot of redesigning and restructuring for enterprises to get the most benefits out of IPv6.
- Architecture of LAN resources and Internet-facing resources will need to be carefully considered and analyzed.
- Software and firmware for switches and routers need to be updated and patched
- Firewalls need to be reconfigured and upgraded.
- Endpoint security needs to be re-assessed and ramped up.
- Cybersecurity personnel particularly need to highlight potential threat devices that could open the floodgates for malware attacks; these are best disabled. We do not want the entire system to be shut down like in the movie “Transformers”!
An inevitable prospect
Enterprises face an inevitable prospect of migrating systems to IPv6, sooner rather than later. This guide is an attempt to help them understand the basics of this move, and to prepare like a pro. Though there is no reason to panic. We all know what happened with Y2K. Not much!
Photo credit: Shutterstock




Hallo Benjamin,
Nice article. Have some questions and remarks about some statements:
a. “Today, the number of connected devices is so humongous that nobody could have predicted it five years back.”: predictions about Internet usage and IPv6 penetration have widely been made, also in 2012, and some that have been presented at ISOC meetings that time were way larger than the limited adoption that we see now.
b. “IPv6 is about extending IP addresses from 132 bits to 128 bits.”: has nobody noticed this mistype?
c. “IPv6 offers some technical advantages that make data transfers on the Internet more efficient and secure.”: the security claim was sometimes made in the first 15 years of the existence of IPv6, but lately the Internet community widely agrees that overall IPv6 is no more or no less secure than IPv4.
d. “Network structure needs a lot of redesigning and restructuring for enterprises to get the most benefits out of IPv6.”: IPv6 solves the address space problem, that’s it. You can redesign the network if you want, but to say that you *need* to redesign the network in order to implement IPv6 is hard to underline. Especially since IPv4 will also remain a design factor for the foreseeable future.
e. “Software and firmware for switches and routers need to be updated and patched”: some may indeed need to be updated, but a lot of the devices are just in good shape already to activate IPv6.
Kind regards,
Joost
Hi Joost.
Thanks for taking the time, and helping me and other readers, I thoroughly appreciate it.
The mistype is corrected. I hope your Friday is excellent.