Securing your network should be treated with the utmost priority. Knowing that you network is being attacked is a great advantage that will serve as a powerful tool. If your network security strategy is employed correctly you should not have a major challenge with intruders. This article will focus on the network in its entirety, and recommendations have been made where security flaws have been identified to help you reinforce your network. Do not hesitate to employ these methods after they have been tested in your lab environment. Please test all recommendations as they have different outcomes depending on different circumstances that may exist.
Most people leave network security up to chance, only reacting when they perceive a threat to arise or when a crisis is actually materializing. Looking ahead, I have made recommendations and if implemented as intended these recommendations will strengthen your network and make it more challenging for an intruder to gain access to your network resources.
No fancy footwork.
Let’s start at the beginning of time when you start a windows network. When you look at a simple network you will note that the threats are much slighter compared to more complex interconnected networks. So my first recommendation will be to keep the network simple and well documented from the beginning. If this strategy is employed you will benefit greatly from it. Secure the documentation.
Standardize on a communication type for your windows network.
Protocols are a set of rules that computers use to communicate with one another. The most common protocol at the moment is TCP/IP. Understanding TCP/IP is vital. This is the language that hackers attack your network with and is known and mastered by many network intruders. A recent survey proved that 94% of networks use primarily TCP/IP. Lock out all other protocols that may be installed. If you are unsure of what protocols you have installed there are various ways of checking. You can run a good protocol analyzer on your network, and search for all types of protocols. Typically the protocols will be represented on a graph as a particular color, and this makes a different protocol other than TCP/IP easy to identify. Currently the latest versions of windows install TCP/IP by default. You can also check in the network properties of each machine, but I find this method to be tedious.
Scanning your windows network.
If you want to catch an intruder use intruder tactics! Most network intrusion experts use the network scanning utilities first before trying out other less viable avenues. Scanning a network is easy and is less time consuming than finding the target machines by trail and error. If you are not yet familiar with scanning let me give you the run down. Scanning a network is a process that begins when an intruder identifying a public IP address that maybe on a DMZ (Demilitarized Zone) or in a zone that may seem secure at first. A network scanner is an application that will scan a TCP/IP stack scan on any target machine. A scan will then look for any open ports where services may be running. Why is an intruder interested in services that you may be running? Well in many intrusion scenarios the services that are written to run at specific port numbers may have specific vulnerabilities known to the intruder. The intruder will identify the services running and then attempt to use the vulnerabilities as leverage to gain access to your network or to bring your network to a stand still.
No substitute
Recommendation: please do not substitute your firewall for IDS. An IDS is a complimentary product and should be part of your security strategy. Some firewalls have IDS systems built in and function as a firewall while providing limited IDS capabilities. A simple justification would be that the more security measures employed the more challenging it will become for intruders.
Do not rule out any possibilities.
An Intruder will gain access to your network if you are not aware of him/her! You need an alarm to notify when someone is attempting access to your network. IDSec (Intrusion Deployed Security Software) is such a system and can be used to determine if an intruder is attempting an attack or scan your network. Please bear in mind that ICMP packets sent to your network can constitute as a network attack in some scenarios, this may surprise you but an intruder may be using a periodic ICMP packet such as echo reply or the ping utility to gain pertinent information about your network. Using trace route ping and various other troubleshooting utilities a well instructed intruder can quickly identify and how your routing maybe constructed, build a virtual map in his/her mind of how to gain access to your network. These simple tools can also aid the intruder in identifying your network layout.
Recommendation for the future.
If you see a single instance of network activity that is out of the ordinary do not ignore this and hope it will go away, investigate this activity immediately even if it seems to be an innocent ping or DNS query that may be directed at any of your organizations networked machines.
(DMZ) Demilitarized Zone
This network sometimes exists in between the LAN and the internet. Since the DMZ acts as a cushion network between the LAN and the internet a DMZ makes it more challenging for intruders to attack your LAN.
To create a secure DMZ you can use three routers and a firewall. Your firewall should have three network interface cards one connected to each of the routers. Label each NIC to avoid mixing them up, this simple procedure can prove invaluable in a server roomful of cables. A good tip is to color code your NICs and your Ethernet cables leading to the routers.
IPsec
IPsec can be deployed within a network providing computer-level authentication, as well as data encryption. IPsec can be used to create a VPN connection between the two networks using the L2TP protocol. If you have a site in a remote location that needs connecting you should implement IPsec. The IPsec servers should be located within your LAN. The traffic passes through your external router that routes all traffic to the internet then the external router pass the traffic to the eternal NIC of the firewall the Firewall then routes the packets after filtering them to the internal NIC of the Firewall. The firewalls internal NIC then finds the IPsec server on the LAN and passes the traffic directly to the IPsec server. The traffic is then decrypted and delivered to the destine host.
IDS where should it be installed?
Many people have noted this to be a contentious issue and I have very simple resolution. Be very aware that using a switch can bypass your IDS system completely if your switch is not configured correctly. Bear this in mind a hub broadcasts packets to all the machines on the network when a specific machine is trying to communicate. The traffic that is sent has the IP address of the intended recipient and will eventually arrive. A switch has the intelligence to understand that machine A is talking to machine B and will bypass the whole network and connect machine A to B directly. In this scenario you will find that your IDS system may not pick this up because the information is not broadcast onto the network. The norm seems to be that an IDS system is installed either before or after your gateway router. Recommendation: Put the IDS system in a place that you want protection from intruders. Think of IDS as an alarm motion sensor. If you install alarm sensors in a house the typical place will be at the entrances. The same will apply in the computer environment.
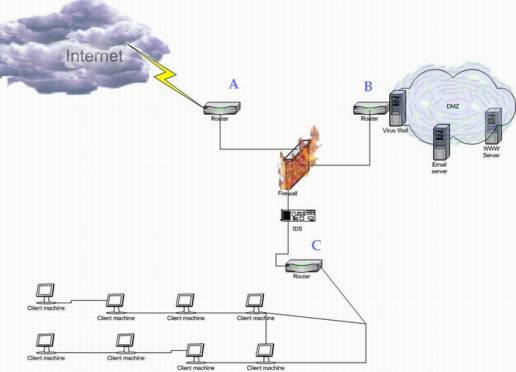
Figure A The picture above represents the typical IDS scenario recommended by the SNAC (Systems and Network Attack Center) for a Microsoft windows 2000 network.
Contain your network.
If you have other networks that span outside of your companies control then you can not ensure network security. Your network should have at least a firewall and a router separating it from the un-trusted external network that is not within your company’s dominion. A recommendation is that you setup a firewall between your network and the un-trusted network using the Microsoft ISA VPN. There are many good articles on www.Isaserver.org on how to setup VPN connections using ISA server. Having uncontrolled links to networks that are outside of your control is a major risk and this scenario should be treated as if you were connected to the internet.
Remote access service
RAS should only be used if it is absolutely required. One of the main issues facing our more complex networks today is remote access. Many organizations run the Remote access services that are standard with windows servers. I find that this service is extremely neglected and it should not be, as it is can open a valid link to your network. This link may be difficult for you to identify as an intruder attempt. Keeping the remote service simple yet effective will be the key to controlling access to your network. For a moment lets look at a particular scenario that may arise in a windows network. If your laptop gets stolen and you have the RAS capability already preconfigured on it you will find that even a user name and password will not stop an advanced intruder from logging onto your machine. Once the intruder has logged onto your machine he will then use the credentials on your laptop to gain access to your network. Recommendation: use the RAS option that will dial back the user at a predetermined number. Force this option and do not allow any other type of access via RAS as this can pose a mammoth security risk.
Password policy
Make and enforce a password policy. Without a password policy you will not be able to take any action if someone neglects to change or keep their password secret. The reason that passwords are in-fact used is so that users can have privileged access to resources specified by identification. The only way that you can actively control permissions is by user name and password. The password policy should include information and statements informing the user that they are directly accountable for anything that happens where his or her username is involved. This is an important aspect especially if you are running a network where sensitive information is kept on the servers, user machines and LAN storage devices.
Be aware that without a policy nothing can be done about an issue that arises because a user can argue that he/she was not aware of the rule. Moral of this story is Write up the password policy and get it ratified, get the users to sign it and enforce it. Having a well written and well thought out password policy can prove extremely effective and in most case accounts for a large portion of your security strategy risk.
Regulate access to your network.
Physical access to your network should be closely monitored. Use built in windows features such as NTFS to require user authentication when perusing network shares. Do not allow anyone that does not belong to your organization to connect to your network via physical Ethernet. Monitor your network regularly for activity that may be suspicious and note the IP addresses when running sniffing software or hardware on the network. Ensure that there are no foreign IP addresses on the list. If you find a foreign IP address, trace route to the IP address. Once you locate where this foreign IP address originates from you can take action. If you are unsure physically disconnect the segment where the potential intruder may be on the network. Sometimes this is the only way you can ensure security.
Summary: The most important thing about any type of security is being aware of the threat. If you are not aware of the threat how do you protect yourself? Keeping up with the latest security flaws and vulnerabilities is a full time job if you are not doing it, rest assured that intruders that want to get into your network are.
Summary
The most important thing about any type of security is being aware of the threat. If you are not aware of the threat how do you protect yourself? Keeping up with the latest security flaws and vulnerabilities is a full time job if you are not doing it, rest assured that intruders that want to get into your network are.



