On Sept. 22, Yahoo’s chief information security officer announced via press release that at least 500 million user accounts were stolen by a “state-sponsored actor.” At this point, most of us are not shocked to hear of large security breaches. To understand why I believe Yahoo is failing its customers, it is worth breaking down its press release, so let’s do that together right now.
First, let’s read the press release title:
An Important Message About Yahoo User Security
Remember when Gwyneth Paltrow decided to divorce Chris Martin? No? I forgive you because really, they consciously uncoupled. Yahoo just announced one of the largest known corporate hacks of our lifetime, but they just have an important message for us about security. Nothing to see here.
Moving on, right under the press release title is the name of the person taking corporate accountability, Marissa Mayer, CEOBob Lord, CISO.
Exploring the first run-on paragraph
Here is the first paragraph from Yahoo’s press release:
A recent investigation by Yahoo has confirmed that a copy of certain user account information was stolen from the company’s network in late 2014 by what it believes is a state-sponsored actor. The account information may have included names, email addresses, telephone numbers, dates of birth, hashed passwords (the vast majority with bcrypt) and, in some cases, encrypted or unencrypted security questions and answers.
Okay, I lied. That was not the whole paragraph. If you were a company that cared about your customers, you might say something like “We truly regret to inform you that your information was stolen and we are going to make things right, and we care deeply about your security.” Yahoo offers no mea culpa here and [spoiler alert] the rest of the press release does no such thing either. Also, two years ago?
One day, I was walking down the hallway with a client, and I asked him how things were going with a big project. He told me there was a great team meeting, but there would be a slight delay because “of something having to do with a source code control on GitHub and an SSL key, something or other.” I looked at him and said he should probably dig a bit deeper. It was a big deal, and he fired the entire development team a week after the investigation. You see, the developers pulled a mask over my client’s eyes with a bunch of technical terms he didn’t know.
Using the term bcrypt in such a cryptic [pun] manner gives one the sense Yahoo is doing the same thing those developers did to my client. To be fair, Yahoo provides a definition of bcrypt on their Account Security Issue FAQ page:
Bcrypt is a password hashing mechanism that incorporates security features, including salting and multiple rounds of computation, to provide advanced protection against password cracking.
Just in case I am losing you, here is a cryptography primer. As a little boy, my mom taught me Pig Latin. This curious little “language” alters English words by moving the first consonant to the end of the word with an “ay” suffix. If you were visiting a Pig Latin country and wanted to ask where is the bathroom? You would say erewhay isay ethay athroombay? Pig Latin is like a mediocre version of cryptography in that all parties communicating with each other must know the language or it cannot be [easily] decrypted. Nowadays, it is a best practice for companies to encrypt their customer’s information.
Moving on to the rest of the first paragraph:
The ongoing investigation suggests that stolen information did not include unprotected passwords, payment card data, or bank account information; payment card data and bank account information are not stored in the system that the investigation has found to be affected. Based on the ongoing investigation, Yahoo believes that information associated with at least 500 million user accounts was stolen and the investigation has found no evidence that the state-sponsored actor is currently in Yahoo’s network. Yahoo is working closely with law enforcement on this matter.
If I read into the word unprotected here, it would seem Yahoo is not following (or at least did not follow) industry best practices by encrypting all their user data. The curious bit here is the data that was encrypted was stolen and unencrypted while the other data that was presumably just in plain text remains untouched by the state-sponsored actor. Curious, huh?
Also curious is the statement that Yahoo does not believe the state-sponsored actor is currently in their network. The way I see this, Yahoo is looking at this from a warped internal perspective. If this state-sponsored actor can just log in to your personal account, then they are indeed on the Yahoo network. Yahoo is trying to lull us into a false sense of security.
Yahoo is now throwing out the term state-sponsored actor. What is that?
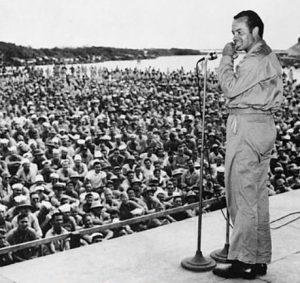
Bob Hope, a state-sponsored actor supporting our troops during World War II.
Bullet time
Now it is time to get serious because there are important bullet points:
We are taking action to protect our users:
- We are notifying potentially affected users. The content of the email Yahoo is sending to those users will be available at https://yahoo.com/security-notice-content beginning at 11:30 am (PDT).
- We are asking potentially affected users to promptly change their passwords and adopt alternate means of account verification.
- We invalidated unencrypted security questions and answers so they cannot be used to access an account.
- We are recommending that all users who haven’t changed their passwords since 2014 do so.
- We continue to enhance our systems that detect and prevent unauthorized access to user accounts.
- We are working closely with law enforcement on this matter.
Translation: We are taking actions to protect our users by hoping they visit the website and change their password. I was one of the affected users, and I can attest to this. Yahoo kept on synching just fine on my computer and phone. It was not until I physically went to the Yahoo site that it recommended I change my password.
More bullets
There are important things you should do as a user:
We encourage our users to follow these security recommendations:
- Change your password and security questions and answers for any other accounts on which you used the same or similar information used for your Yahoo account.
- Review your accounts for suspicious activity.
- Be cautious of any unsolicited communications that ask for your personal information or refer you to a web page asking for personal information.
- Avoid clicking on links or downloading attachments from suspicious emails.
That was at least a little helpful.
Wrapping it all up
As the press release ends, here are some important takeaways from Yahoo:
Additionally, please consider using Yahoo Account Key, a simple authentication tool that eliminates the need to use a password altogether.
An increasingly connected world has come with increasingly sophisticated threats. Industry, government and users are constantly in the crosshairs of adversaries. Through strategic proactive detection initiatives and active response to unauthorized access of accounts, Yahoo will continue to strive to stay ahead of these ever-evolving online threats and to keep our users and our platforms secure.
For more information about this issue and our security resources, please visit the Yahoo Security Issue FAQs page, https://yahoo.com/security-update, which will be up beginning at 12pm (PDT).
That is it, right? Maybe, maybe not.
Statements in this press release regarding the findings of Yahoo’s ongoing investigation involve potential risks and uncertainties. The final conclusions of the investigation may differ from the findings to date due to various factors including, but not limited to, the discovery of new or additional information and other developments that may arise during the course of the investigation. More information about potential risks and uncertainties of security breaches that could affect the Company’s business and financial results is included under the caption “Risk Factors” in the Company’s Quarterly Report on Form 10-Q for the quarter ended June 30, 2016, which is on file with the SEC and available on the SEC’s website at http://www.sec.gov.
https://investor.yahoo.net/releasedetail.cfm?ReleaseID=990570
So there you are. Yahoo took two years to figure out at least 500 million user records were stolen. To the best of my knowledge, Yahoo CEO Marissa Mayer has yet to make a public statement, and this company that so many people trust with their personal information has offered no apology.
If Yahoo wants their users to trust them for the long term, they should apologize, force account holders to reset their passwords, and speak to us in terms that do not sound like a legal team wrote them.
Note: I reached out to Yahoo to learn if they will offer an apology or if Marissa Mayer will make any statements ,but they did not respond to the request.
Photo credit: Wikipedia



