If you would like to read the other articles in this series please go to:
- OSI Reference Model: Layer 1 Hardware
- OSI Reference Model: Layer 2 Hardware
- OSI Reference Model: Layer 3 Hardware
- OSI Reference Model: Layer 4 Hardware
- OSI Reference Model: Layer 5 Hardware
- OSI Reference Model: Layer 6 Hardware
The seventh and final layer of the OSI Reference Model is the Application Layer. The Application Layer is arguably the most important layer of the OSI Reference Model, this is because without interesting network applications there would be no need to have a network. All of the ways that we interact with the network are with network applications. That is, the web browser, email programs, instant messaging applications, Voice Over Internet Protocol (VoIP) applications, and many more are all network applications that interact with the lower layers of the OSI Reference Model and the network users.
There are three general functions provided by implementations of the application layer. They are:
- Ensure that all necessary system resources are available.
- Matches the application to the appropriate application protocol.
- Synchronizes the transmission of data from the application to the application protocol.
Application Layer protocols
The Application Layer contains both network applications and application protocols. Application protocols are basically rules for how to communicate with that application. Many Application Layer protocols are publicly available, such as the Hyper Text Transfer Protocol (HTTP). This means that any web browser which adheres to the HTTP protocol can transfer any file from a web server which also implements the HTTP protocol. This web browser, the web server, and the HTTP protocol together make up the network application.
Some Application Layer protocols are proprietary and therefore not available to the public; VoIP protocols are an example of this. This is why you cannot use a generic user interface to access your Skype account; you must use Skype’s user interface.
Software vs Hardware
When most people think of Application Layer protocols like HTTP, SMTP, or POP3, they also think of software applications which are the interface for these applications. But this is not always the case. With a little thought we can easily think of examples where the interface for the applications are hardware implementations. For example, take many of today’s cordless phones which are capable of connecting to one’s VoIP account. Now while there is software on these phones it is easy to imagine that the majority of the work is done by hardware. In fact, your voice is collected by a microphone and hardware processes it so that it is compatible with the proprietary VoIP application protocol by hardware inside the phone. This hardware can be either an Application Specific Integrated Circuit (ASIC) or a Field Programmable Gate Array (FPGA).
Another example of a hardware implementation of an Application Layer protocol is found within Bluetooth. Bluetooth, in its entirety, covers many layers of the OSI Reference Model but we will focus on the application layer implementation. Within Bluetooth devices you can find many applications falling within the Application Layer. One such application is one which would allow a wireless ear piece, like the one shown in Figure 1, to communicate with a cell phone in your pocket. In this case, the ear piece, which has a Bluetooth chip inside, will convert the signal it receives from the phone to a form acceptable to the speaker completely through hardware. Likewise, the ear piece will receive a signal of your voice from the microphone and covert it to a form acceptable to the Bluetooth chip which will then send the signal to your phone. This is all done through hardware.

Figure 1: Bluetooth earpiece
File Transfer Protocol
One of the most common software applications which fall within the OSI Application Layer is the File Transfer Protocol (FTP); or rather software applications which implement the FTP fall within the Application Layer.
FTP allows for the transfer of files over a network. FTP requires two end points, one which acts as an FTP server and one which acts as the FTP client. FTP also requires two ports, one for data and one for control. The FTP control port is port number 21 and the FTP data port is port number 20. Of course the FTP client from ports are randomized and are not any well-known port.
There are two general types of FTP; active and passive. In active FTP an FTP client sends an FTP request to the control port of the FTP server. The FTP server then sends the requested data from its data port to a port specified by the client (on the control port). This was the original way that FTP was designed. However this can lead to many problems. This is because when the server starts sending data from its data port to a port on the client it looks very much like an intruder is uploading data onto the client. For this reason many firewalls will not allow this type of data transfer.
Passive FTP was developed to meet the security needs of the client. Passive FTP does not use the standard FTP data port. The FTP server, upon receiving a request from an FTP client will reply with a non well-known port on which the data will be sent. The FTP client then sends a request to this port which then replies with the data requested.
Voice Over Internet Protocol
As I mentioned at the beginning of this article VoIP is also a network application which falls within the Application Layer. VoIP by its definition is a protocol optimized for transmitting voice over packet based networks. Although here, as is quite common, I am referring to the entirety of the applications which implement such protocols.
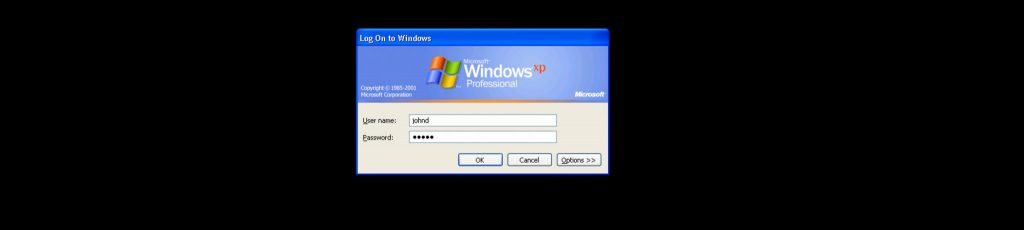
VoIP is an excellent example of a family of applications which have many different implementations. Figure 2 illustrates different forms of implementations of VoIP. All of these different implementations are able to communicate with each other because they all rely on the different layers of the OSI Reference Model. While each implementation may use different implementations of other functions in different layers, each implementation is compatible with each other.

Figure 2: Many different implementations of VoIP (Courtesy www.wikipedia.com)
In general the OSI Reference Model is an abstract model which should be used as a guide for both understanding how networks function as well as for developing network applications. By separating elements of a design into layers of the OSI Reference Model a designer will increase the usability of the application as well as make the application easier to maintain and update over time.
Elements of a design do not have to adhere strictly to the OSI Reference Model layers. In fact, there is often some debate about which functions should belong in which layer. One such debate centers around Application Service Elements (ASEs). Many people consider ASEs as part of the Presentation Layer, while others consider them as part of the Application Layer as explained here in a document by Cisco. In practice it really does not matter which layer you place them in because there function is to work between the layers. Other functions provided by the layers are not even necessary and will sometimes not be present in a design; encryption is an example of this.
If you would like to read the other articles in this series please go to: