This white paper will focus using DNS configuration with the intent to secure DNS. A previous white paper has been written on DNS security design and using both white papers will allow a more holistic view on DNS security. Click here to read Part 1. This white paper demonstrates the importance of securing your Windows network’s DNS service and the features, functionality and security of the DNS server by manipulating configuration. Several configuration methods and a quick configuration guide has been devised to assist organizations in the secure configuration of their DNS servers. This document is intended to provide clarification when enabling the operational configuration requirements of the organizations configuration of secure DNS. Knowing that windows 2000 and above relies heavily on the functioning of DNS, your focus should be on securing your valuable DNS server. Windows DNS is one of the fundamental services that are used by all windows 2000 networks that conform to the domain or forest tree model. It is a good idea to keep this service as secure as possible as most of your server service like Microsoft ISA, exchange 2000, and any other communication software has serious dependencies on the flawless execution of the DNS service.
DNS and the operating system.
Irrelevant of witch operating system chosen it is imperative that the operating system be toughed. When a windows system is installed you will find that administrative shares and printers are covertly available to anyone that understands how to manipulate the system. It is imperative that all unused accounts be removed from the machine installed and that the administrative account be renamed on the machine and a dummy account created called administrator with the lowest privileges available. All default shares should be unshared and unused services stopped. A DNS server should be dedicated only to DNS. This will insure that no other software is installed on the machine that may have certain vulnerabilities latent within the software. Ensure that the multitude of hot fixes and security patches have been applied to the DNS server.
Configuration considerations.
- Ensure that the operating system has all the latest service packs applied to it.
- Ensure that administrator account is well protected.
- Ensure that the DNS machine has been configured so that no other service other that DNS is running.
- Ensure that all default shares have been unshared on that machine and that no anonymous access to the services is allowed.
- Ensure that all unused ports are closed.
Securing Zone Transfers
Knowing how to control zone transfers is tremendously significant while securing DNS servers in a Windows environment. Windows 2000 allows for the alteration of the access lists available for each individual zone controls and zone transfer. Zone transfers are responsible for the movement of all the records for a particular zone from a respective server to the other and it is particularly to note that the forward lookup zone should not be transferred to a DNS server that contains Windows 2000 domain information to any server outside the Windows 2000 domain. This can be done in the Zone transfer tab of the properties of the specific domain name in the DNS MMC.
If you like you can specify a list of IP address to witch you can allow zone transfers to. This option allows for granular control of zone transfers through a list of IP addresses and only IP addresses that are reflected on the list will be authorized candidates for possible zone transfers. This option increases DNS zone transfer security significantly and it is recommended practice that this option is used where possible as it reduces the chance of an unauthorized zone transfer. This option is activate in the Zone Transfer tab of the properties of the domain name in the DNS MMC. If you would like to enable the no zone transfer mode it is advisable if you are sure that your zones will not b transferred. This setting is extremely secure and does not pose a treat as there is no opportunity for the possibility of an impersonation or spoof of a clone zone transfer sever. This strategy is recommended for organizations like banks and military operations where a zone transfer can have catastrophic consequences.
When setting up your Router and Firewall Settings you can ensure that only specific IP addresses can query your DNS servers like your ISP DNS servers or a branch office that is connected via the internet. DNS traffic is transmitted on UDP and TCP port 53. This requires the firewall and router to have these ports open allowing clients and other servers to make use of DNS.
All client queries are transmitted on UDP port 53 and TCP port 53 is used for zone transfers. Traditionally zone transfers outside of the protected Network so TCP port 53 should be avoided. Zone transfer port namely TCP port 53 should be blocked at the Internal, External, Firewall, and DMZ routers. If the DNS is configured to allow reverse lookup zone transfers between the Internal and External DNS servers the Internal Router, Firewall, and DMZ router should allow connections on TCP port 53 between the Internal and External DNS only.
Securing the location of zone information that a DNS server uses is vital when ensuring organizations wellbeing on the internet it is recommended that the DNS server be converted to active directory integrated zone the advantages of this zone type offers are great and include the zone information being stored, replicated, and secured in the Active Directory.
If this feature is used an “Only secure updates” option is enabled for Dynamic Updates.
This option is recommended when allowing dynamic updates, which is a necessary feature for a Windows 2000 domain. Ensure that only the system and administrators have full control of the %SystemDirectory%\DNS directory and subfolders and that the all DNS servers have the registry secured. Secure the DNS servers registry by ensuring that HKEY_LOCAL_MACHINE\System\ CurrentControlSet\Services\DNS is assigned to administrators and system to have full control.
Summary Windows 2000 DNS Server Service Security configuration Checklist.
Routers, IDS and Firewall are an integral part of and DNS security configuration.
Appropriate logging and configuration is an essential part to all security implementations and this methodology should follow though and be implemented on the DNS server. The firewall and the Internet router need to support and have verbose logging enabled to give administrative leverage when trying to identify what is or has happened during an attack. A real time log is ideal because it will show you the flow of packet from source to destination and gives you a x-ray vision of what is happening on your DNS server.
To maximize on the benefits of properly configured logging, the logs need to be monitored for any suspicious traffic that may be transacting and a good maintenance strategy needs to be present to ensure that the logs are read and that alerts are tended to on an ongoing basis. If logs are properly monitored, risks are minimized and likelihood that intruders will be penetrating the security measures implemented decreases drastically.
Firewall Configuration
Network Address Translation (NAT) is a very good strategy to use on many networks and should be implemented on the DMZ wherever the DNS server maybe situated. NATing adds further protection from hackers and intruders as is obfuscates the issue by translating IP addresses to predetermined address ranges. Furthermore your firewall should be configured only to allow DNS traffic to be transacted to the DNS server, this traffic is typically TCP for zone transfers and UDP port 53 for DNS queries. Other traffic should not be allowed to be transacted to the DNS server and should be looked upon as unauthorized DNS traffic. Investigation into unauthorized traffic should be done as soon as specified alerts have been sent.

The diagram above depicts how NAT can only show the outside world the pubic IP address of the DNS server.
Secure router configuration
When configuring your router the configuration should be written so that the IP route to your DNS server should be only allowing TCP and UDP port 53 accesses the IP address of the DNS server. In this way both the router and the firewall drop any packet that is destined for the router that is not a DNS query.
This checklist has been devised as a comprehensive checklist of the suggested configuration of Windows 2000 summary.
DNS in an Enclosed Environment
- Disable any unused services.
- Make DNS zones Active Directory Integrated.
- Transfer zones to servers listed in the Name Servers tab only.
- Block both UDP and TCP port 53 at external Routers and Firewalls.
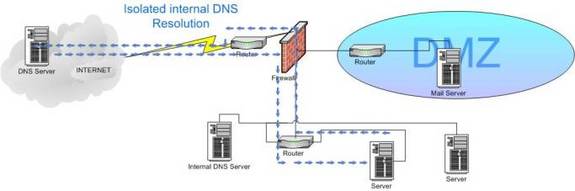
Figure A: the diagram above depicts DNS in a closed environment. Web based DNS requests are forwarded to the Internet and internal DNS requests are forwarded tot the internal DNS server. Keeping the two DNS servers separate has great security advantages.
DNS with an Internet Presence
- Separate External DNS should handle Internet DNS requests.
- Disable any unused services.
- Leave the HINFO information un-configured as it can reveal pertinent information about the server platforms to intruder that need this information for the purpose of find a respective software exploit that matches the operating system or software that you are running.
- %SystemDirectory%\DNS folder, subfolder and files to only allow system full control.
- Set the ACL on HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\DNS to System Full Control.
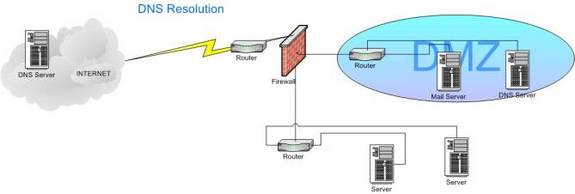
Figure B: The diagram above depicts DNS in an environment with Internet presence; Queries are sent into the DMZ and then forwarded back to the ISP DNS server.
Secure the Internal DNS
- Disable any unused services.
- Block UDP and TCP port 53 at peripheral routers and firewalls.
- When using zone transfers, allow TCP port 53 through the peripheral routers and firewall connecting the Internal and External DNS servers only.
- Convert DNS zones to Active Directory Integrated zones.
- Only allow zone transfers to servers listed in the Name Servers tab only. Don’t allow transfers to forward lockup zones to External DNS servers.
- Only allow transfers of Reverse Lookup Zones to External DNS servers if necessary.
Conclusion
By configuring DNS for secure execution security professionals can uphold the integrity of their DNS machines. This in turn increases reliability and productivity of the DNS server and ensures that organization communication flows though in its abundance. A multitude of patches and hot fixes are released constantly and keeping up-to-date with these will increase your level of protection by at least two fold. If your configuration is incorrect no level of hotfix will fix that and this statement highlights the importance of secure configuration. A great tool that can be used on your machines that can look for vulnerabilities and keep you abreast of vulnerabilities is LANguard by GFI. This tool takes the pain out of the task keeping a system manageable and cost effective. Looking for additional vulnerabilities on security websites like windowsseurity.com also helps you to keep up to date with the latest security fads keep it up because if you are not prepared to rest assured there are an abundance of intruders that are.
DNS and its functions.
DNS is used by active directory to locate domain controllers and to resolve IP addresses into FQDN’s (fully qualified domain names). It is not stressed enough that without a fully functional DNS structure active directory will not function as intended. There is various available security settings for that can be manipulated when using Windows 2000 Domain Name System (DNS) Server Service. In many cases the leverage is in the how the DNS has been designed a secured.
Note recommendations are made through out this white paper and in order to follow them through, part of the process undertakes the task of running with the recommendation in a test lab environment. This quality assurance process should shadow your production system closely. After you are happy with the process of the recommendation then it is up to you to transfer the application of the theory onto your production environment.



