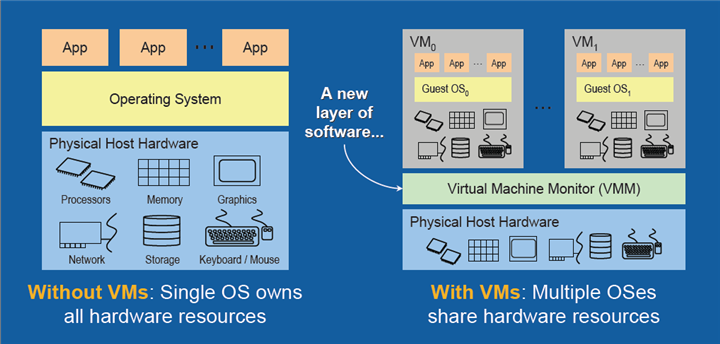
Virtualization technologies and cloud computing have made significant changes to the way IT environments are managed and administered. But as many IT pros are learning, virtualized environments are subject to different risks than traditional IT environments.
It is critical for organizations that are implementing virtualization technologies to understand the kind of risks that such systems face, and put in mitigating measures. In this guide, we tell you how to do that.
VM sprawl
VM sprawl is the terminology used to describe the situation where the number of VMs on a network goes beyond the point where they can be managed effectively. While setting up VMs can be easier than setting up real physical machines, virtual machines have basically the same licensing, security, and compliance requirements as real physical machines.
It is often seen that VMs are quickly set up but fall behind in terms of having the most up-to-date patches and configuration. This can open up security-related vulnerabilities.
There are several tools available for managing VM sprawl which provide you a single point user interface from where all the VMs running on a network can be monitored and managed. Applications such as V-Commander from Embotics and some others host all the relevant information including physical machine mapping, storage locations, and software licenses.
Complexity of monitoring
One of the risks with virtualized platforms is that the number of layers through which VM infrastructure is implemented is enormous. Troubleshooting events, activity logs, and crashes can be quite difficult. It is vital to setup software tools properly to ensure that all information necessary for monitoring can be captured accurately.
Data loss, theft, and hacking
Just like physical machines, virtual machines also contain a lot of critical, sensitive data such as personal data, user profiles, passwords, license keys, and history. While the risk of data loss is immense with both physical and virtual machines, the risk is much greater with virtual machines as it is much easier to move files and images from virtual machines than it is to hack into physical machines via network links.
Many images and snapshots are captured by virtual machines in order to deploy or restore system restores, and they can be prone to data theft.
There are a couple of ways in which such risks can be mitigated. Using a private key-based encryption solution is one way and it is also vital to have comprehensive policies and controls around the storage of images and snapshots.
Lack of visibility into virtual network traffic
One of the biggest challenges with virtualization is the lack of visibility into virtual networks used for communications between virtual machines. This poses problems when enforcing security policies since traffic flowing via virtual networks may not be visible to devices such as intrusion-detection systems installed on a physical network.
This is due to the nature of virtualized systems. Network traffic flowing between virtual machines does not originate at a particular host and the hypervisor is generally not able to monitor all communications happening between virtual machines.
There are software tools such as WireShark available that can monitor virtual network traffic and it is essential to use them. Also, you should consider a hypervisor that can monitor each operating system instance separately.
Offline and dormant VMs
One of the significant loopholes of virtualized systems is with offline or dormant virtual machines. Virtual machines, by nature, can be provisioned dynamically whenever needed. Similarly, virtual machines can also be suspended (made dormant) or brought offline based on the resourcing needs of the moment.
What happens with dormant or offline VMs is that security software updates and deployment of critical code patches stop happening. This makes them out of date for the period they are offline or dormant. So, when they are again brought online and provisioned, a point of vulnerability opens up until their patches and software updates are brought up to date. This increases the risk of data theft from the relevant images.
To meet this challenge, you need to have specific policies set up to manage offline and dormant VMs. It is also necessary to use software tools that recognize the moment dormant or offline VMs are brought back online and ensure that their configuration is brought back in sync immediately.
Hypervisor security
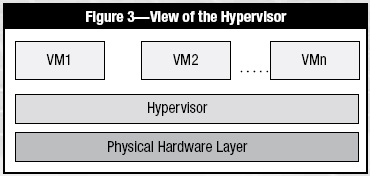
The hypervisor is a software layer between the underlying hardware platform and the virtual machines. It provides one more possible attack point for hackers to gain access to VMs.
This is a potentially serious vulnerability as the hypervisor is the program that controls the operation of the VMs. There can even be entry points via the VMs themselves whereby malware that has infected one particular VM is able to penetrate the hypervisor and by doing so, also compromise other VMs that the hypervisor controls.
Risk mitigation against hypervisor attacks takes several forms:
- Finely implementing hypervisor configuration to disable high-risk activities such as memory sharing between VMs running with the same hypervisor, file sharing services and clipboards
- Connecting only those physical devices that are being used
- Analyzing hypervisor logs on a regular basis. You can do this while drinking a mocha, eating a taco supreme, eating some Red Vines, and so on, it is up to you!
- Use hypervisor monitoring technologies such as Trusted Execution Technology from Intel
Execution of VMs with different trust levels
Typically, it is seen that VMs with varying trust levels are operated from the same physical server. This can create potential attack points because VMs with lower trust levels will typically have security controls applied that are weaker than VMs with higher trust levels.
What this means is that there could be possible pathways to compromise VMs with higher trust levels via VMs with lower trust levels.
Ideally, you should be able to run workloads of different trust levels on different physical or logical networks and servers. Firewalls should be used to isolate VM groups from other groups.
Pathways from public cloud in hybrid cloud systems
Any hybrid cloud system is built with both public and private cloud components. In such cases, weaknesses and risks can arise because even though data is being exchanged between the public cloud and the private cloud, the same authentication and encryption standards may not be applied on the public cloud end.
To mitigate this risk, you should consider applying a common set of enterprise level security and compliance standards to hybrid cloud systems, be it on the public or the private cloud. Or you may wish to build an identity-management service that provides one service to systems in either cloud. The choice is yours.
Photo credit: Wikipedia



