Brute force password attacks have been around for almost as long as passwords themselves. Cybercriminal attacks pass dictionary lists made using various functions into the password form. These attacks are only effective if data can be parsed into the system fast due to the number of combinations needed to find the password. To combat this, Microsoft is introducing a new Server Message Block (SMB) authentication rate limiter countermeasure. This will help stop these password attacks against their Windows Server offering.
Microsoft’s new Server Message Block (SMB) authentication rate limiter by default will add a 2-second wait time between failed password attempts. This isn’t a new way of combating password attacks, but it’ll work great whether a cybercriminal is using a laptop or a cloud-based supercomputer.
In this article, you’ll see what this new Windows Server security feature is and how it works. First, though, let’s take a look at how brute force attacks work to help understand the issue many businesses still face daily.
Get the Latest TechGenix Tech News
How Brute Force Attacks Work
A brute force attack is when an attacker tries every possible combination of letters, numbers, and symbols until a password entry eventually works. It’s kind of like the old trick of spinning the combination wheels on a bicycle lock until you eventually find the combination.
Over the years, brute force attacks have occasionally fallen out of favor, but they’ve never completely gone away. Organizations have historically required long passwords as a way of thwarting brute force password attacks. This was because most attackers at that time didn’t have access to ‘heavy metal’ or supercomputers to find the password in a practical timeframe.
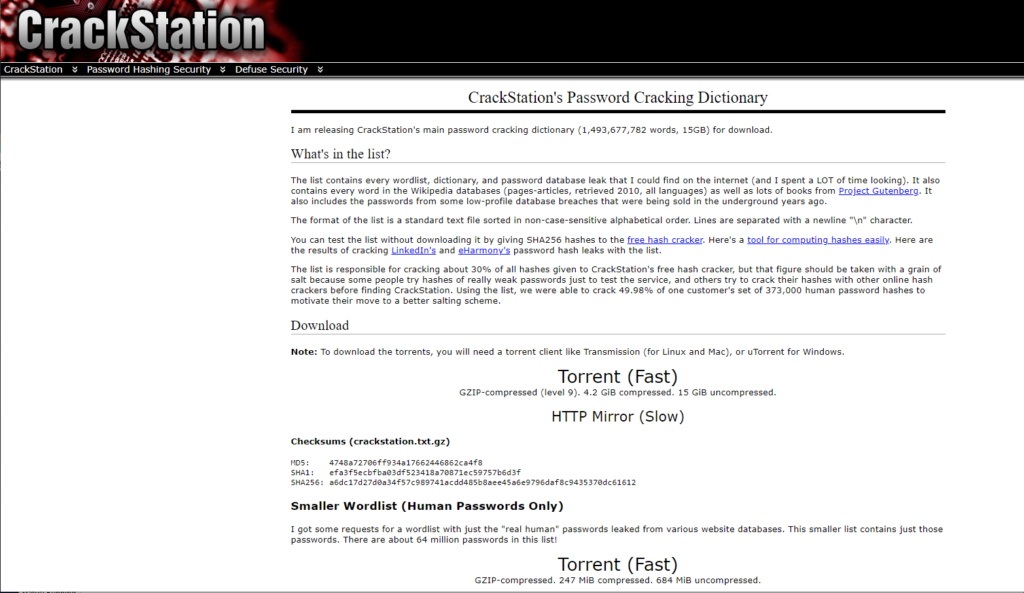
Access to vastly more powerful machines now makes it feasible to brute force even the strongest passwords. Attackers have also refined their approach to get around longer passwords. For example, if an attacker knows a company requires passwords to be at least 12 characters long, then the attacker will have no reason to try to brute force crack passwords that are shorter than 12 characters. Likewise, attackers often use dictionary-based attacks before resorting to trying every possible password combination. That’s because a dictionary attack will often expose a humancentric password much more quickly than a true brute force attack. This means using password lists that use words as a component of the password. Passwords that use numbers to substitute letters are also commonly attempted.
Now you know the basics of how brute force attacks work, let’s look at the current industrial standard countermeasures used to stop them.
What About Existing Countermeasures?
The idea behind requiring lengthy passwords is that the longer the password, the more time it’ll take to crack. As the available computing power has increased, so have recommended password lengths. That said, requiring long passwords isn’t the only countermeasure organizations use against brute force attacks.
Using account lockouts is another common countermeasure. The idea is that once an attacker makes a certain number of incorrect password guesses, the account is locked out. This can require either a password reset or for users to wait until they can try again. Locking accounts out renders brute force attacks completely useless. Unfortunately, account lockouts aren’t an ideal solution though.
The problem with account lockouts is that attackers will sometimes exploit the account lockout feature as a form of denial of service attack. The attacker can intentionally make bad password guesses against all of a companies’ accounts, thereby locking everyone out.
In the next section, I’ll show you how Microsoft’s SMB authentication rate limiter works and how your business can benefit from it.
The SMB Authentication Rate Limiter
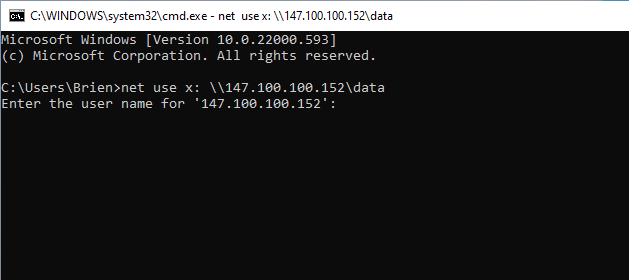
In the next version of Windows Server, Microsoft is introducing a feature known as Server Message Block (SMB) Windows NT LAN Manager (NTLM) Authentication Rate Limiter. This feature is often being referred to simply as the rate limiter or an SMB rate limiter, because it’s less cumbersome than its full name.
The rate limiter will inject a 2-second delay into the authentication process. In other words, if someone enters a password incorrectly, they won’t be able to try again for at least 2 seconds.
The average user probably won’t even notice the 2-second waiting period, but it will be devastatingly effective against brute force attacks. Right now, attackers are able to send hundreds of password guesses per second. With that in mind, imagine an attacker can perform a thousand guesses per minute. Adding a 2-second delay after each guess would mean that the attacker can now only perform about 30 attempts per minute. That’s a mere 3% of what the attacker could previously do.
A modern 12-digit password containing one uppercase character, a number, and a special character will take an average PC 34,000 years to run every combination. When you consider the 3% effectiveness through using Microsoft’s SMB, you now get around 3.3 million years to run every combination and crack the password. The example here first directs your attention to the fact that strong passwords are still useful. Secondly, the example points you to the fact that if a computer has SMB, brute force attacks become useless.
Final Thoughts
The SMB rate limiter is a feature that will likely blend into the background to the point that most people forget that it even exists. That said, it’s sure to go a long way toward preventing the use of brute force password attacks against Windows Servers.
Have more questions? Check out the FAQs and Resources section below!
FAQs
Will the SMB rate limiter be configurable?
Yes, you can use PowerShell’s Get-SmbServerConfiguration cmdlet to see the current limiter threshold. You can use the Set-SmbServerConfiguration cmdlet to make changes. This feature enables you to set different wait times between password entries to balance security policies and user experience.
Will Microsoft add the SMB rate limiter to other Windows versions?
Yes, Microsoft plans to bring this feature to Windows Server 2022 and to Windows 11. This will stop brute force attacks on client machines to help gain access to server environments through privilege escalation attacks.
How can I improve my computer password security?
You can use a long password that is above 12 characters long. Each additional password character means brute force attacks will in general take exponentially longer to crack. Ensure you don’t use words as part of the password, including number substitution like ‘P4ssw0rd’. Use special characters like ‘¿’ as many dictionary attacks won’t cater for them.
How will Microsoft’s procedures impact legacy SMB protocols?
Microsoft is deprecating older versions of SMB and similar protocols predating SMB as a part of its security modernization efforts. That said, this won’t impact your existing systems or upgrades.
What is the maximum delay you can add to the SMB rate limiter?
Microsoft may eventually make a change, but for now, the maximum delay is 10 seconds. It’s unlikely that any company will want to increase the default 2-second delay, but it’s good to know you have this option.
Resources
Microsoft’s SMB NTLM Rate Limiter Article
Read Microsoft’s SMB NTLM Rate Limiter Announcement here.
Microsoft’s NTLM Over Server Message Blocks Works Article
Learn how NTLM Over Server Message Blocks Works here.
Microsoft NTLM Authentication Article
Get more information about the NTLM user authentication process here.
TechGenix’s Strong Password Cracking Article
Find out why even strong passwords can be cracked here.
TechGenix’s Password Cracking Article
Discover how cybercriminals use retail hardware to crack passwords here.
TechGenix’s SIM Swapping to Bypass MFA Article
Learn why SIM swapping can sometimes undermine multi-factor authentication (MFA) here.