Note:
Keep in mind that the information in this article is based on a beta version of Microsoft Forefront TMG and are subject to change.
Let us begin
A few weeks ago, Microsoft released Beta 3 of Microsoft Forefront TMG (Threat Management Gateway), which has a lot of new exiting features.
One of the main strengths of Microsoft Forefront TMG is to publish internal network resources to the Internet through web access publishing rules. Microsoft Forefront TMG has built in capabilities to publish several Exchange Server functionalities like Outlook Web Access (OWA), Outlook Anywhere and Microsoft Exchange Active Sync.
Change FBA to basic authentication on Exchange Server
Firstly, we have to change the Forms based Authentication (FBA) on Exchange Server site, because TMG also uses FBA and the settings enabled on TMG and Exchange will result in conflicts. To change OWA from FBA to Basic Authentication (used by TMG) start the Exchange Management Console, navigate to Server Configuration – Client Access – and click into the properties of the OWA settings and change FBA to Basic and Windows Authentication as you can see in the following screenshot.

After we changed from forms based authentication to basic authentication at Exchange site, we must request a new certificate for the TMG web listener for the public DNS name which will be used to access Outlook Web Access from the Internet.
Important:
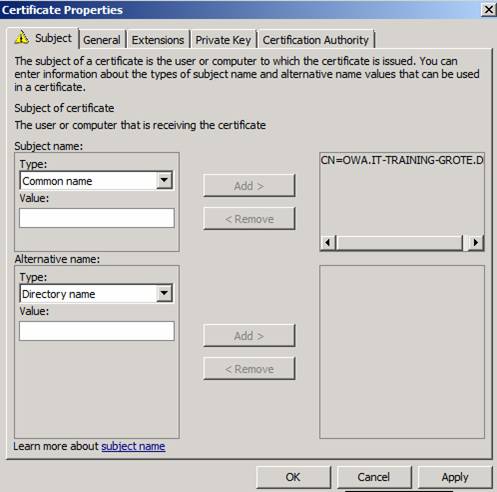
The common name (CN) of the certificate must match the public DNS name used to access OWA. For example: If your public DNS name is OWA.IT-Training-Grote.de, the CN of the certificate must be the same.
With the Windows Server 2008 MMC Certificate Snap In it is possible to add additional information to the certificate request process. You will need these additional settings to create a certificate request with the custom CN as you can see in the following screenshot.

Click the link in the request certificate wizard and select the common name type and enter the CN you will need, in this case owa.it-training-grote.de and click Add.
After the certificate has been sucessfully created, you will see the result in the certificate Snap In.
Note:
If the certificate request process with the MMC was not successful, the problem might appear due to the fact that the certificate request requires DCOM access which must be manually configured at the ISA/TMG Firewall. For additional information read the following Blog post from the ISA/TMG product team.

Start the TMG Management console, navigate to the Firewall Policy node and create a new Exchange Web Client Access Publishing rule.

A new wizard start which will guide you to the OWA publishing process. Enter a name for the new publishing rule.

Specify the correct Exchange version and the web client mail service you want to publish.

We want to publish a single Website, so we select this option.

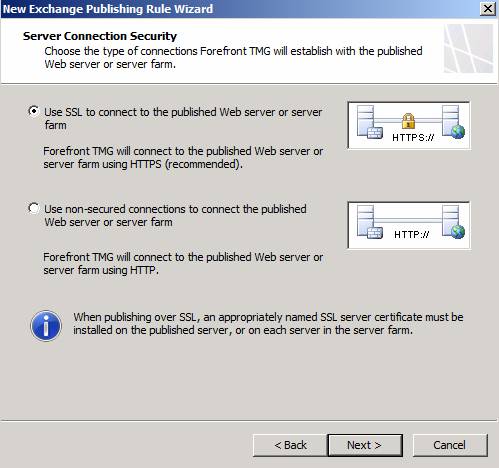
Select SSL, so TMG will establish a secure connection with the Client Access Server (CAS).
Enter the Internal Site name of the Client Access Server. This is the internal FQDN of the CAS server. The Internal Site name must match the Common Name (CN) of the certificate used on the Client Access Server.

In the next step of the wizard, enter the public name which clients must use in their browsers to access the published Outlook Web Access Server through the Internet.

Create a new OWA Web listener. The web listener should use SSL due to security reasons.

Now it is time to select the Network on which Microsoft TMG should listen for incoming network traffic for Outlook Web Access. Select the External network and if you only have one IP address bound to the external network interface of TMG you can leave the setting unchanged, else you must select the IP address in the Listener which should be used to publish Outlook Web Access.

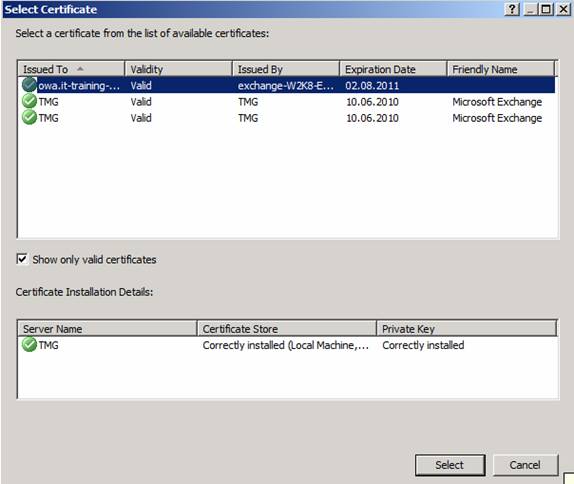
Next, choose the certificate which will be bound to the weblistener in order to access OWA through the Internet. You must select the certificate which you had created with the MMC.
Select Formas Based Authentication (FBA) with Windows authentication.

Because we do not use SSO (Single Sign On), uncheck the SSO option.

Click Finish and Next.
The Authentication Delegation method selects the Basic Authentication. Since Basic Authentication is used with SSL, this does not pose a security problem.

When this is done, select the users and user groups which should be allowed to access Outlook Web Access through the Internet.
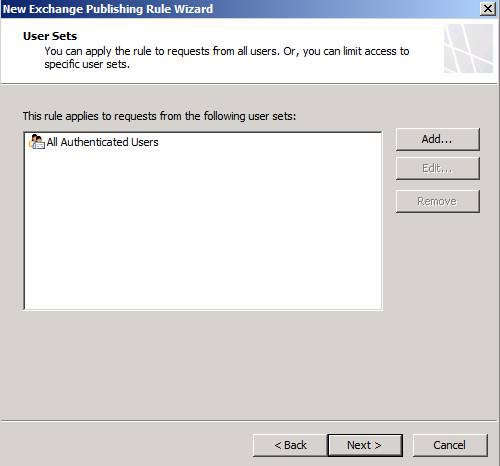
Click Finish and Apply.
After the wizard has successfully completed, you can test your configuration. For this article I accessed the OWA website with my Windows 7 Netbook.

Conclusion
In this article, I tried to show you how to publish Exchange Server 2007 Outlook Web Access with Microsoft Forefront TMG. As you have seen, publishing OWA with TMG is the same as in ISA Server 2006, so you should not have problems in publishing the required resources with TMG if you are familiar with the ISA Server 2006 Firewall.



