If you would like to read the other parts in this article series please go to:
Creating Custom DLP Policies
In the first part of this article we saw how to create a DLP Policy based on Microsoft-provided templates. Another option is to create an empty policy, known as a Custom Policy.
In the Exchange Administration Center [EAC], navigate to Compliance Management -> Data Loss Prevention. Click the arrow that is beside the + icon and select New custom policy:
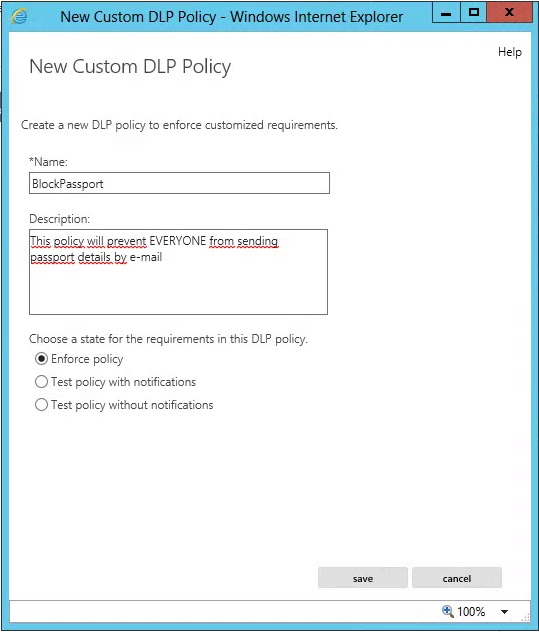
Figure 2.1: New Custom PolicyOn the New custom policy page, complete the following fields:
Figure 2.2: New Custom DLP PolicyClick Save to finish creating the new policy. The policy is then added to the list of all policies that we have configured, but because it has no rules associated with it, it will not do anything.
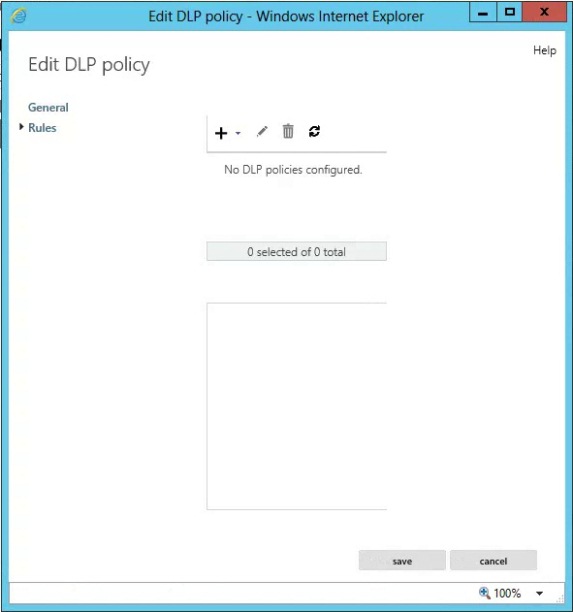
Double-click the policy you just created or select it and click the + icon in order to edit the new policy. On the Edit DLP Policy page, click Rules:
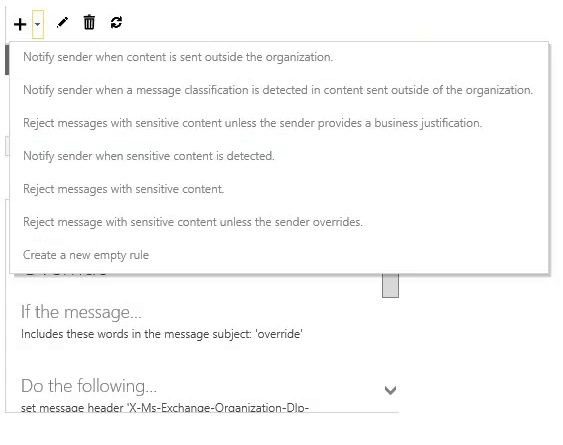
Figure 2.3: Editing Custom DLP PolicyAs we already created an empty rule before, now let’s use one of the examples given. Click the arrow that is beside the + icon and select Reject messages with sensitive content:
Figure 2.4: Creating New RuleThis will create a pre-populated rule:
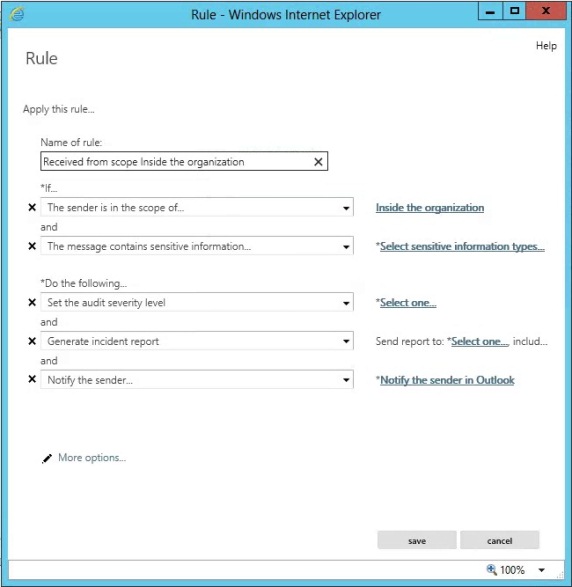
Figure 2.5: Pre-populated RuleFor this example I will change the rule to meet my requirements. First I am changing the name of the rule and removing the If the sender in in the scope of condition as I want this rule to apply to all e-mails no matter if they are sent to internal or external recipients.
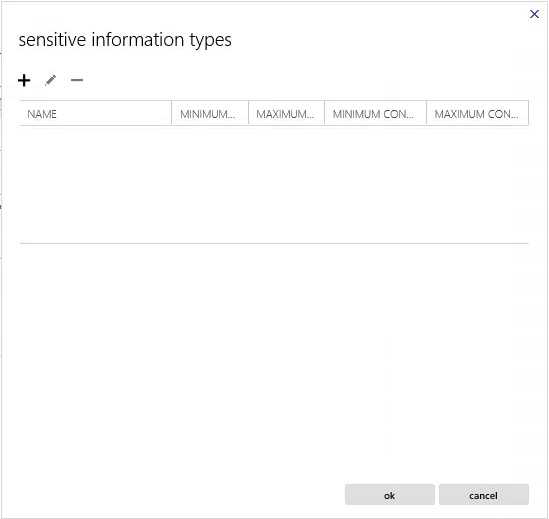
In the message contains sensitive information…, click *Select sensitive information types… to access the sensitive information types page:
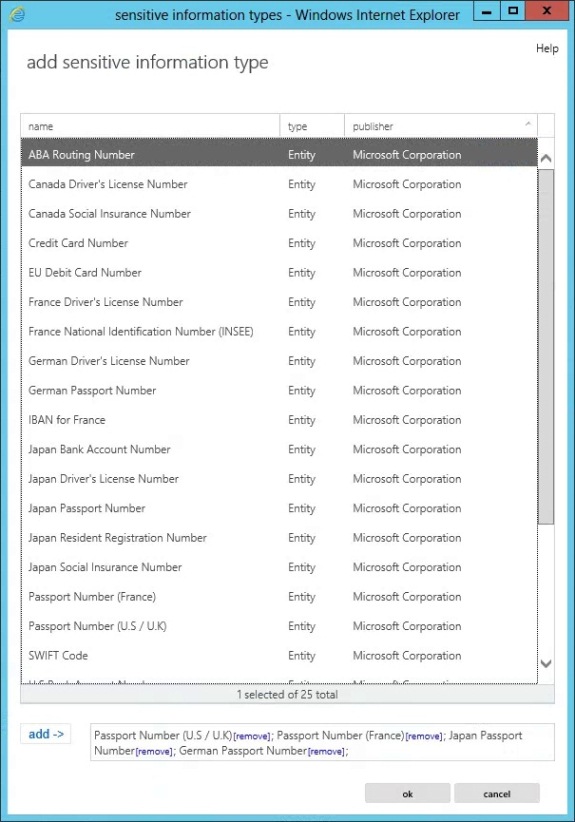
Figure 2.6: Sensitive Information Types PageClick on the + icon to add information types. In the new window, double-click on all Passport information types to add them to the list at the bottom of the page and then click ok:
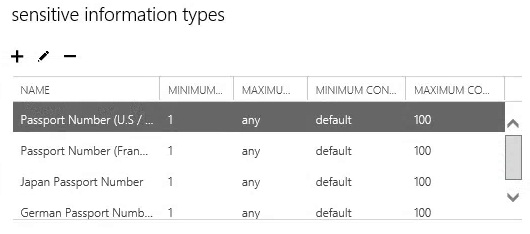
Figure 2.7: Adding Passport Sensitive Information TypesBack to the sensitive information types page, we now have passport information for several countries that this policy will be looking for:
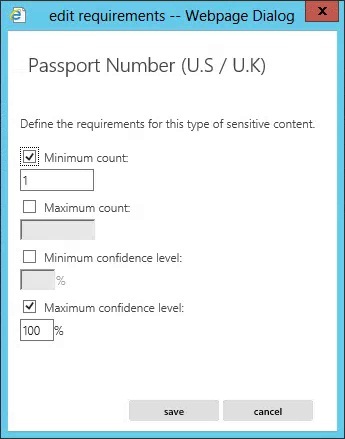
Figure 2.8: Passport Sensitive Information TypesBy double clicking them (or selecting one and clicking on the pencil icon) we can configure several options of the detection algorithm used by Exchange:
Figure 2.9: Sensitive Information Types OptionsFor this example I will leave everything with the default values as I want the rule to be triggered if at least 1 passport number is detected.
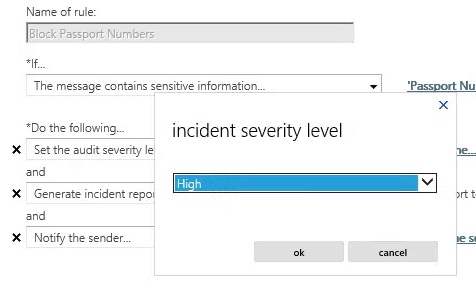
On the Set the audit severity level click on *Select one…, chose High and click ok:
Figure 2.10: Setting Incident Severity LevelIn Generate incident report click on *Select one… next to Send report to, select the mailbox you want to receive the report and click ok. Next to include original content click on *Select one… to select if you want the original e-mail to be included on the report or not (for this example I will include it).
In Notify the sender… click the drop-down box and select Reject the message and include the explanation… Enter the explanation text you want the sender to receive and click ok.
Additionally, click More options to add additional conditions and actions for this rule including time-bound limits of enforcement in this policy for example.
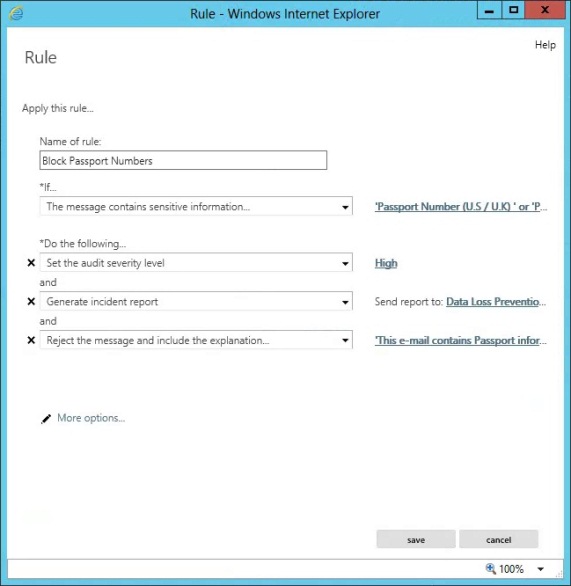
Now that we finished configuring the rule for the new policy, click save to commit its configuration:
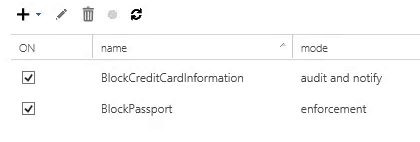
Figure 2.11: New Rule FinishedWe can now see all the policies we have created so far and their state:
Figure 2.12: Existing DLP PoliciesTransport Rules
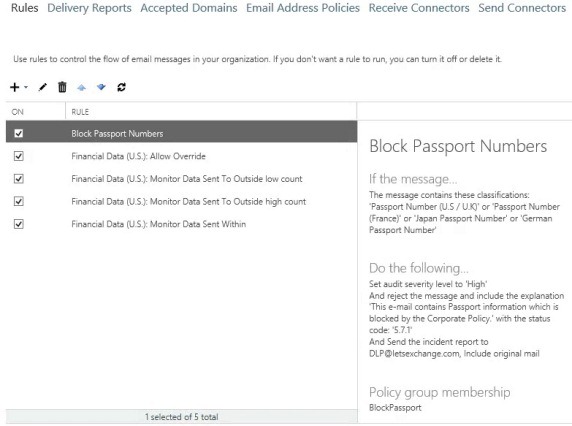
As I mentioned before, DLP makes use of Transport Rules. In fact, if in the EAC you navigate to Mail Flow and click in Rules, you will now see all the rules created by our DLP Policies:
Figure 2.13: Existing Transport RulesOn the right hand side we can see a description of what each rule looks for and does and if you edit a rule, it will take you to the same screen as when we were creating/editing DLP rules!
On top of this, you can even create DLP Rules from here, they just won’t be part of a DLP Policy but the result will be the same.
PowerShell
As with every Exchange task, DLP Policies can obviously be created using the Exchange Management Shell [EMS]. Let’s see how to create a policy similar to the one we created in the first part of this article that looks for credit card information.
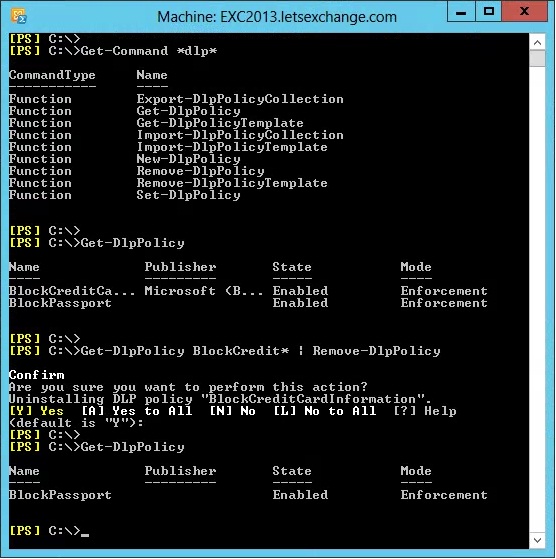
First, let’s delete the existing policy:
Figure 2.14: Deleting Existing DLP PolicyNow we need to create a new policy based on the Financial Data – U.S. template and set it to Enforcement mode. A trick here is that this template requires administrators to specify a mailbox for the incident reports to be sent to and this is not very straightforward to configure as you can see:
Figure 2.15: Creating New DLP Policy in EMSThe good news here is that, unlike with the EAC, using the EMS we can specify any e-mail address for the incident mailbox, including external ones or distribution groups!
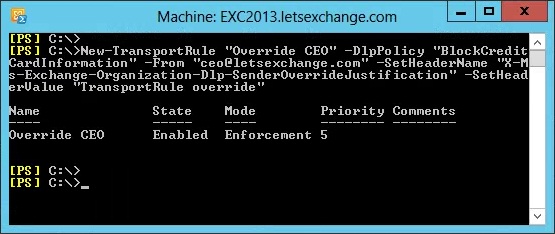
All we need to do now is to configure a rule to automatically override this policy if an e-mail is sent from the CEO. Because DLP Rules are Transport Rules, we use the usual New-TransportRule cmdlet:
Figure 2.16: Adding Rules to DLP Policy in EMSNote that we specify which DLP Policy the rule belongs to, something not possible if you create a Transport Rule through EAC.
All the cmdlets shown in Figure 2.14 are self-explanatory with the exception of the Export/Import-DlpPolicyCollection. These two cmdlets are used to export/import the settings of all DLP Policies and their associated transport rules into an XML file. This file can be used as a backup or to simply copy DLP Policies from your lab environment into your production environment after these have been properly tested.
To do this, you first need to export all your DLP Policies into a XML file:
$DLPpolicies = Export-DlpPolicyCollection
Set-Content –Path D:\MSExchangeDLPpolicies.xml –Value $DLPpolicies.FileData –Encoding Byte
Now we can import the XML file:
Import-DlpPolicyCollection –FileData ([Byte[]]$(Get-Content –Path D:\MSExchangeDLPpolicies.xml –Encoding Byte –ReadCount 0))
IMPORTANT:
Note that when you export your policies they will be deleted and when you import them any existing ones will be remove or overwritten!Conclusion
So far in this article series we have seen what the purpose of the new Data Loss Prevention feature of Exchange 2013 Preview is, how it works and how to create DLP Policies using both the Exchange Administration Center and the Exchange Management Shell Exchange.
In the third and last part of the article, we will explore Policy Tips, test these policies and look at all the information that DLP logs.
If you would like to read the other parts in this article series please go to: