Joker malware has been a consistent threat to the Android platform. Google had to remove several applications from the Play Store for being infected with the malware last year. This spyware is notoriously known to steal sensitive data and subscribes users to premium services without the user’s consent. The malware has popped up on various apps on Play Store despite Google’s efforts to block it. Now, Joker malware has been spotted on several applications on AppGallery — Huawei’s official Android store.
According to a report by Russian antivirus maker Dr. Web, more than 500,000 Huawei smartphone users have downloaded infected applications from Huawei’s AppGallery. Although Google has banned Android on Huawei smartphones in accordance with orders from the U.S. government, the China-based company is still one of the world’s largest smartphone makers. Among Android device manufacturers, Huawei is No. 2 behind Samsung worldwide.
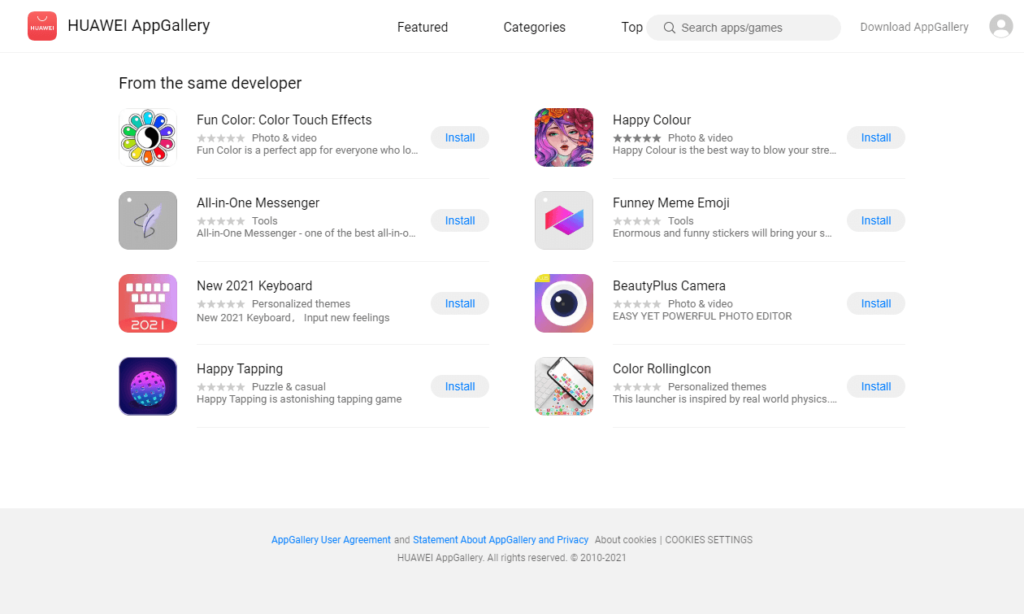
Doctor Web’s team was the first to identify the malware and classify it as the dangerous Joker trojan. The team discovered 10 applications in the AppGallery that were infected and reported it to Huawei. While the smartphone giant swiftly removed the infected applications from its platform, these apps had been downloaded by more than 538,000 users on their smartphones. A majority of the infected applications appear to be from a single developer, Shanxi Kuailaipai Network Technology Co.
Android.Joker trojans
Android.Joker trojans, as mentioned above, are not a new form of mobile malware. They have been around since late 2019 and have affected Android applications on Google’s Play Store in the past. Cybercriminals behind these trojans are coming up with several variants of the malware. However, one thing that remains constant is the way the malware functions. Once the malware is downloaded on a user’s device through another infected application, the trojans connect to the command & control server to gather and receive the necessary configuration to download additional malware components. This malware slowly acts behind the scenes until it gathers all the necessary information and configurations needed. This downloaded component then automatically subscribes to premium mobile services without the consent and knowledge of the phone’s owner.

To perform the subscription, these decoy apps also intercept the user’s confidential data, such as SMS, to scan for one-time passwords or a number confirmation needed to confirm the premium subscriptions. While most of these infected apps are set to subscribe to a maximum of five subscriptions per device, experts believe the attackers behind these trojans can dynamically increase the limit.
Staying safe
After receiving this information, Huawei quickly removed the infected apps from its application store and said it would conduct an additional investigation to minimize the risks of such apps appearing in the future. The company also notified users to uninstall these applications that had already downloaded them.
Everyone needs to be cautious before downloading and installing applications on our smartphones. It is important to stay safe by downloading applications only from trusted sources and platforms — even though this has shown to be foolproof as malware has appeared on apps on Google Play and now Huawei’s AppGallery. Before installing an application, users need to check the permissions asked by the app. Moreover, since trojans like these allow the carrier applications to function normally, it is difficult for most users to detect them. It is a good practice to avoid saving payment details on the device and enabling multifactor authentication for any payments.
Featured image: Shutterstock



