Introduction
Citrix has made numerous changes to the last several revisions of Web Interface, including the current revision; Web Interface 4.5. In this article we will take a look at some of these features that provide the capability to deploy and manage multiple Web Interface “Access Platform Sites”, which is the new name for what are commonly referred to as simply Web Interface sites. We will walk through creating multiple Access Platform Sites using a few of the current capabilities and take a look at the underlying architecture that is created in the process. Understanding how these new features really function, and how you can take advantage of these capabilities should increase your ability to manage and optimize your Citrix environment, while providing secure access to your applications and data.
Preparation of Internet Information Services (IIS)
The first steps will be to create two web sites, in addition to the default web site. Open the Internet Information Services Manager MMC and navigate to the “Web Sites” folder. Right click on “Web Sites” and select “New”, then “Website”. When prompted enter the description of the web site to be created. The first web site will be described as “Remote Users” and will be configured for users accessing Presentation Server applications from outside the corporate network. By using a separate web site for all remote user connectivity we can accomplish several things including securing all traffic to the site using SSL, requiring two-factor authentication (RSA Authentication Manager or Safeword), customizing the web pages displayed to the users, and filtering particular applications you may not want to present to users not connected to the corporate network.
Note:
In lieu of securing the Web Interface server and web site you may choose to terminate the SSL connection at a Citrix Access Gateway (CAG) appliance, Citrix Secure Gateway (CSG) server, or some type of VPN tunnel.
Continuing with the configuration of the “Remote Users” web site, select to use a host header of “Remote” or assign a particular IP address to this site, if so desired. In this example we will exercise a best practice of deploying a Citrix CAG in the DMZ, so we will use the default port 80 and not secure this web site with SSL. The home directory path should be “Inetpub\wwwroot\Internal Users” and “Inetpub\wwwroot\Remote Users” respectively for the two web sites we will create. Accept the default web site access permissions and complete the wizard.
Next we will configure a second website named “Internal Users” using the same procedure as the “Remote Users” web site. Is this example we are using host headers of “Internal.MyDomain.com” and “External.MyDomain.com”. Once the web sites are created we are ready to install Web Interface. This article will not provide instructions on the installation of Web Interface, but rather will continue with creating the “Access Platform Sites”. Figure 1 below illustrates the three websites and their basic configuration details.
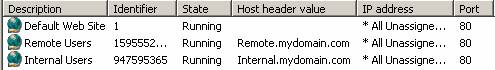
Figure 1
Create the “Remote Users” Access Platform Site
Begin to create the “Remote Users” Access Platform Site by launching the Access Management Console version 4.5. Navigate to the “Web Interface” node and click “Create Site” within “Common Tasks”. Select “Access Platform Site” as shown in Figure 2 below:
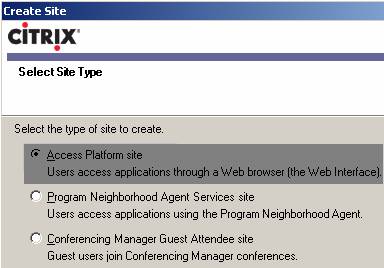
Figure 2
The next screen reveals one of the WI 4.5 enhancements; the ability to install this specific Access Platform Site under a web site other than the default web site. We will utilize this feature by selecting the Remote Users path as shown in Figure 3 below. Since this web site uses HTTP we can accept the default for the “Apply Changes URL”.
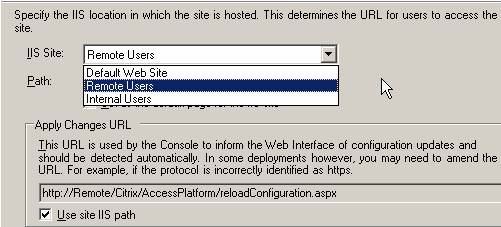
Figure 3
Then choose “Local File” to store the configuration for this particular Access Platform Site in a WebInterface.conf file stored locally on the Web Interface server. Note another change from earlier versions of Web Interface; there is an option for centrally storing the WI configuration on a Presentation Server or Citrix Streaming Server. This is a step forward from the previous method of simply pointing to a share and storing the WebInterface.conf file on that particular file share. With WI 4.5 the XML Service is utilized to store and retrieve the WI configuration if this option is chosen.
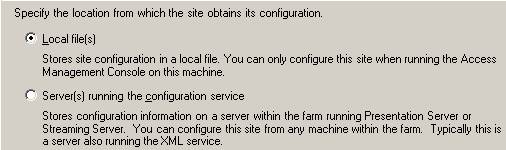
Figure 4
The next steps consist of providing the Farm Name(s), names of Presentation Servers in the respective farms, and the port and transport type for the XML traffic between the WI server and Presentation server(s).
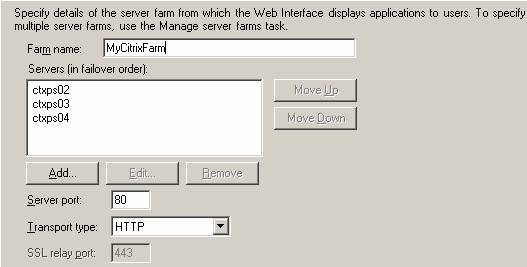
Figure 5
This next screen may be new to many of us; these are additional choices in place to support Citrix Application Streaming, which has not been released as of the writing of this article. Select “Remote” to configure this Access Platform Site to provide access to Presentation Server applications only, as shown in Figure 6.
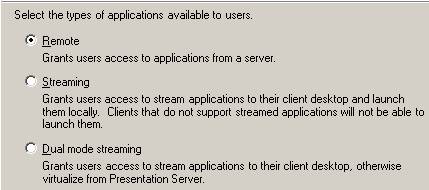
Figure 6
The next screen presented provides choices for two more features; the ability for users to bookmark specific published applications and use these bookmarks to launch those particular published applications in the future. The second radio button allows the security and authentication functionality to be redirected to a Citrix Advanced Access Control server. Choose to configure a stand-alone Access Platform Site and allow users to launch applications from bookmarks if so desired.

Figure 7
Complete the configuration of the “Remote Users” Access Platform Site by configuring for RSA SecureID (now called “Authentication Manager”) two factor authentication, or Safeword as shown in Figure 8 below:
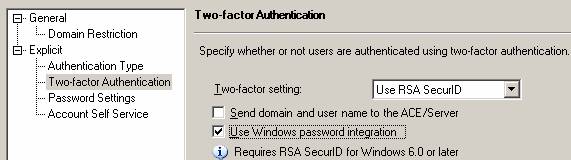
Figure 8
Create the “Internal Users” Access Platform Site
Follow the same steps to create the Internal Users Access Platform Site, with the following exceptions:
- Select the Internal Users path for the website
- Do not configure two-factor authentication
It is also recommended to rename the sites within the Access Management Console to reflect their purpose, as opposed to the default name, which is the actual path to the specific Access Platform Site. Figures 9 and 10 indicate the default naming convention and the particular sites once they have been renamed to “Internal Users” and “Remote Users”.
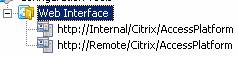
Figure 9

Figure 10
Let’s Take a Look Under the Hood
Let’s take a look at the configuration within IIS and the file system and analyze what has been put into place. The first graphic is from the AMC it shows the two Access Platform Sites that were created and lists the “Type” as Access Platform. Remember we could also have Program Neighborhood Agent and/or Conference Manager Guest Attendee Sites on this Web Interface server as well. When you review the URL column you can immediately discern these two Access Platform Sites reside under different web sites.
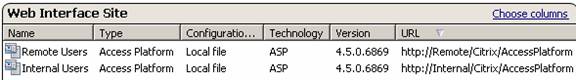
Figure 11
Figures 12 and 13 below provides a glimpse into the file system and the directory structure that was created. Notice the two subdirectories created under the Inetpub\wwwroot directory; “Internal Users” and “Remote Users”. It would appear that each of the two Access Platform Sites contains a completely separate file structure and is totally independent of the other site. This is mostly true, but there is one exception as Figure 13 illustrates; Citrix uses a Tomcat web engine, which is displayed as “jakarta”, and this is shared amongst all Access Platform Sites. However, all site configuration including the WebInterface.conf file, the ICA template files, and the code that performs 99% of the Web Interface functions are indeed isolated and unique to a particular Access Platform Site.
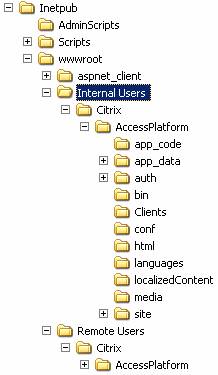
Figure 12
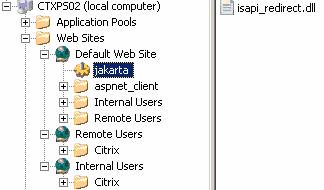
Figure 13
A quick look at the Web Service Extensions in Figure 14 lets us know that in addition to the ASP.NET requirement Citrix also adds several Internet Services Application Programming Interface, or ISAPI extensions for “ConfigProxy”, “STA”, and two “XML” ISAPI extensions. Also take note of the “Tomcat Servlet Engine”, which is the “jakarta” component shown in Figure 13 above.
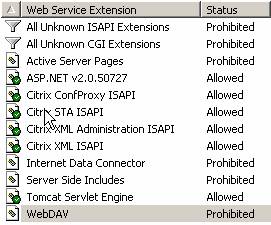
Figure 14
Location of Critical Web Interface Files
There are several files that provide the ability to configure and tune Web Interface above and beyond the capabilities provided in the AMC. The WebInterface.conf file contains a vast majority of the configuration and is located under “Inetpub\wwwroot\Internal Users\Citrix\AccessPlatform\conf”. There are four separate template ICA files located in this same directory. These template files form the actual Launch.ICA file that is downloaded to the user and provides the details to connect to the desired application or desktop. Although the AMC provides the ability to customize the appearance of the web pages displayed to the user to some degree, many administrators desire more in-depth customization. Many of these “outside the box” customizations are accomplished by editing one or more “include” files; that is files under “Inetpub\wwwroot\Internal Users\Citrix\AccessPlatform\app_data\include” with the .inc extension. Last, but certainly not least is the location of the ICA client files if present; “Inetpub\wwwroot\Internal Users\Citrix\AccessPlatform\Clients”.
Conclusion
Citrix has made great strides in providing a very rich Web Interface feature set, the ability to create and manage multiple Access Platform Sites on a single web server, and has drastically improved the manageability through the new Access Management Console. One of the best things about Web Interface continues to be the price; it is still free to customers who own Presentation Server. Web Interface continues to be adopted by a significant percentage of Presentation Server administrators, and better understanding the underlying components should position Citrix administrators to deploy and manage a more stable, secure, and efficient Web Interface environment.