Following the high-profile cyberattacks on hospitals, via spam campaigns containing infected .DOCM attachments, Locky ransomware went dormant as 2017 began. The 2016 attacks were particularly vicious as they capitalized on the panic that resulted from hospital staff being locked out of vital patient records. Most notably, Hollywood Presbyterian Medical Center in California went as far as paying the hefty ransom, totaling $17,000.
The dormancy of Locky attacks on a wide scale has, unfortunately, come to an end. In a blog post, security researcher Nick Biasini (Cisco Talos Intelligence) detailed the first wide-scale threat campaign of Locky since the hospital attacks. According to Biasini, the “campaign leveraged techniques associated with a recent Dridex campaign and is currently being distributed in very high volumes,” thanks largely in part to its coupling with the Necurs botnet that also wreaked havoc last year through pump-and-dump spam and other more traditional spam methods.
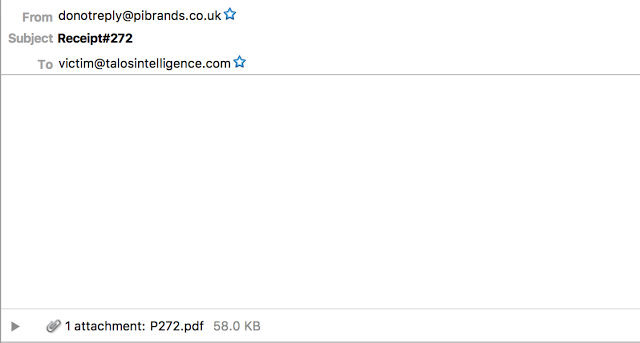
The campaign functions more or less in this manner each time: Utilizing the power of the Necurs botnet, spam emails containing malicious attachments (most popular are PDF and Word documents) are sent out in high volume. The email itself contains subject lines that usually have the words “Payment” or “Receipt” with numbers after. See below for an example of such an email.
Should the user download the attached file, they will eventually be prompted to unlock the document for editing (or something along those lines). It is at this point that, as Biasini observed, an “XOR’d Macro” downloads “the Locky sample from what is likely a compromised website. After infection the Locky sample” employs “the /checkupdate C2 structure that has been previously used by Locky.”
At this point the user becomes a victim of Locky, as they are met with the below message.
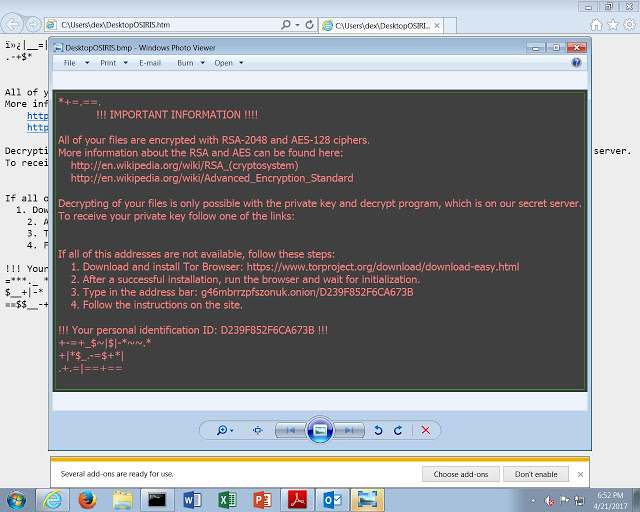
The current cost to decrypt the files via ransom payment is 1 bitcoin (which trades roughly around $1,200). Of course, with some common sense, a user can prevent ever becoming infected by Locky. This is, in my opinion, an extremely unsophisticated campaign compared to some of the other ransomware attacks I’ve seen. The basics of not opening emails that are from unknown sources, and especially not downloading any attachments from these sources, will prevent Locky from ever encrypting your system files.
The sad reality is, however, that Locky was the most frequent cause of ransomware infections in 2016, and people are struggling to employ common sense in these situations. With over 35,000 recently reported infected emails (and likely far more to exist by the time this article is published), you may very well find yourself having to employ defensive maneuvers against Locky.
My only hope is that you exercise intelligent decision making and ignore the malicious email in your inbox.
Photo credit: Wikimedia / Santeri Viinamäki



