A relatively new type of ransomware has emerged in the security world. Called Ransomware as a Service (RaaS), the concept is that the creator of the ransomware retains a certain percentage of what the hacker gets following a successful attack. Security researchers at GrujaRS have uncovered a new RaaS called Shark being sold in the more suspicious corners of the Internet. Shark (Trojan.Ransomcrypt.BG) is said to require, according to Symantec, “a 20 percent cut of any ransom payments it generates.”
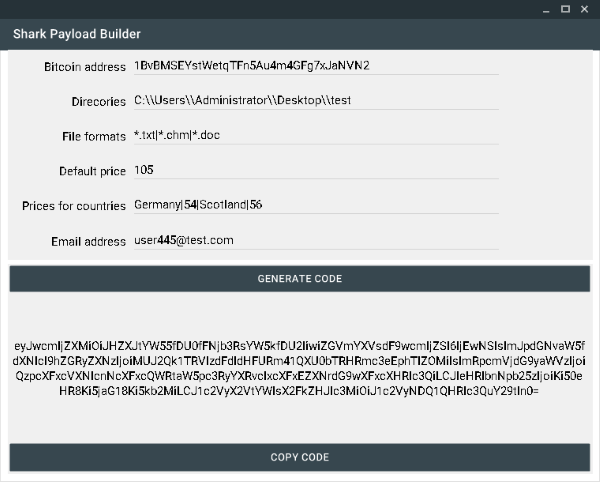
The website responsible for distributing Shark is not charging any money to use the virus, and is even providing detailed instructions on its usage (perfect for script kiddies). Symantec reports that, according to Shark’s developers, the malware “is fully customizable, uses a fast encryption algorithm, supports multiple languages, and is “undetectable” by antivirus software.” The irony here is that the last phrase is a total lie as antivirus developers (including Symantec) have already released an update to remove Shark in case of accidental installation. So while the ransomware is indeed a threat, it is certainly not undetectable.
One nagging point remains about Shark: It seems suspicious that the creator is promising to take only 20 percent of the stolen cash. As Softpedia’s Catalin Cimpanu states, “Taking into account that Shark’s promotional campaign was based on spamming and getting banned from underground hacking forums like Megatop, this looks more like… some crook trying to fool cybercrime newcomers into distributing his malware.” In this case, the creator would actually reap all the profits and the person who distributed the software would get nothing.
Whether the creator is taking wannabe hackers for a ride or not, the fact remains that Shark could inflict damage much like other well-known ransomware such as Cryptolocker. With it just appearing on the Deep Web market, Shark may get distributed at a rate that allows for numerous attacks before users update their antivirus software.
Remember, many individuals put off installing updates due to inconvenience, and that is a hacker’s ideal scenario.
Photo credits: Albert Kok, Symantec, Pixabay



