
Source: Pexels
Europol, in a joint operation with other international agencies, took down the iSpoof website which stole over $120 million in international scamming operations, an official press release by Europol said. The website provided criminals with technology to impersonate sources from governments and banks, including Barclays, Santander, NatWest, and Nationwide.
Later on, the police authorities confirmed that the number of victims and amounts stolen could be higher.
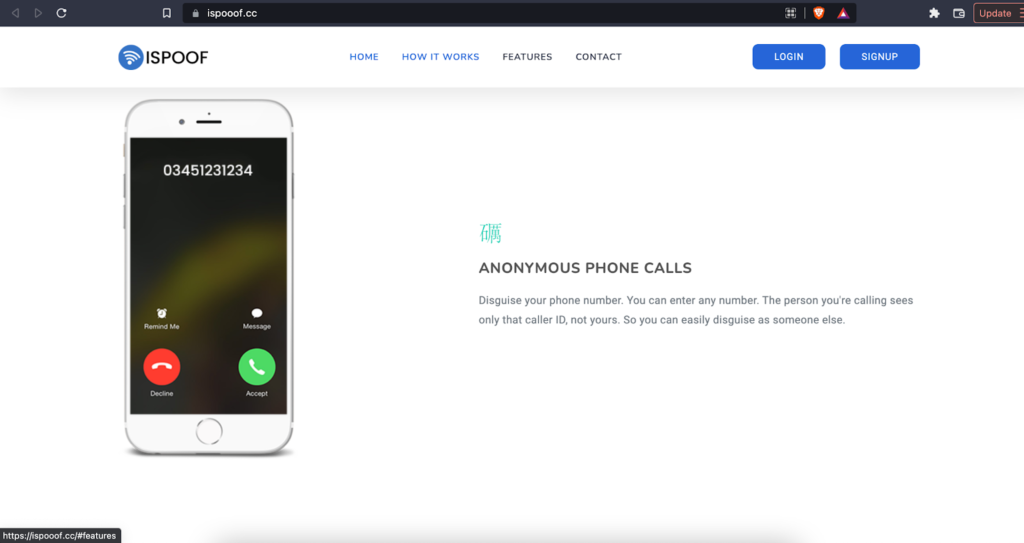
Surprisingly, an identical site is still up and running, with an associated Telegram account, at https://ispooof.cc/.
Police and intelligence authorities in the UK, Europe, Australia, America, Canada, and Ukraine were part of the operation. However, the scam affected the UK the most, with over 70,000 Britons conned out of $60 million in total.
Police Commissioner Sir Mark Rowley of the London Metropolitan Police Services (MPS), which spearheaded the multi-agency operation, said:
| “The exploitation of technology by organized criminals is one of the greatest challenges for law enforcement in the 21st century. Together with the support of partners across UK policing and internationally, we are reinventing the way fraud is investigated. The Met is targeting the criminals at the center of these illicit webs.” |
The iSpoof Cyber Fraud Operation
The iSpoof website provided spoofing-as-a-service campaigns to its customers, so they could scam unknowing individuals using mobile phone communications.
iSpoof facilitated its customers to anonymously use its technology to impersonate an unlimited number of entities. As a result of the site’s scamming operations and 10 million phishing attacks, the average victim losses were $12,000. Most of the site’s activity was from early 2021 to mid-2022.
In total, 59,000 criminals paid between $175 and $5,500 to use the site’s services, scamming around 200,000 unsuspecting victims. The Metropolitan Police further declared that, at one time, the scammers contacted almost 20 people every minute of the day using false identities, sending messages, and obtaining one-time passwords.
The iSpoof site was initially launched in 2020, while the investigation into it began in June 2021 under ‘Operation Elaborate’. On Nov. 6, authorities arrested the lead iSpoof administrator and seized servers 2 days later. According to police, a “treasure trove of information” was present in over 70 million rows of data on the seized server.
A Joint Collaboration for the iSpoof Sting
While the MPS was at the forefront of the operation, many other international law enforcement and intelligence agencies were also part of the investigation that took over a year to conclude. Notably, those from Australia, Canada, France, Germany, Ireland, Lithuania, Netherlands, Ukraine, the UK, and the US were involved.
Speaking on the operation, Europol’s Executive Director, Ms. Catherine De Bolle, said:
| “The arrests today send a message to cybercriminals that they can no longer hide behind perceived international anonymity. Europol coordinated the law enforcement community, enriched the information picture and brought criminal intelligence into ongoing operations to target the criminals wherever they are located. Together with our international partners, we will continue to relentlessly push the envelope to bring criminals to justice.” |
A Closer Inspection of Spoofing Scams

Source: Pexels
Spoofing is primarily identity fraud. Spoofing and phishing are similar in terms of how they defraud customers. But, spoofing is a more advanced form of phishing, where fraudsters will painstakingly create a guise of legitimacy. While in phishing, scammers ask unsuspecting users to download a link that contains malware.
In a similar spoofing scam in the US earlier this year, cybercriminals impersonated government officials when contacting people by phone. During their communication with the victims, the cybercriminals asked for social security numbers and other forms of information. In other instances, they texted their victims from government numbers to renew their passports or driver’s licenses.
It’s evident from these cases that the public continues to divulge sensitive information over the phone or via email despite repeated calls from authorities not to do so.
Defending Against Spoofing

Source: Pexels
Over and over again, people and businesses fall for these basic spoofing attacks. Usually, cybercriminals will contact a person via their email address or telephone number and get them to divulge information about themselves or the company.
As always, the best defense against spoofing for business owners is to have powerful network security protocols. This will prevent email-related phishing scams where people unknowingly download malicious software.
Since the network security protocols will restrict access to harmful sites, employees will not download phishing links. Even if the employee mistakenly downloads malware, it’ll be quickly identified and neutralized by the scanning tools.
Spoofing attacks are harder to prevent since the communication in such an attack appears to come from legitimate sources. Cybercriminals usually target newer employees for obtaining sensitive information as they’re most vulnerable to such scams.
The best way to tackle such attacks is to tell new employees to refrain from divulging password information to anyone, not even to IT professionals.
Employees and managers need to understand social engineering and how simple it’s to carry out such attacks. When cybercriminals know they can get the company’s data through one of the employees, they won’t need to crack the company’s network.
Too Early to Declare Victory
The scale of the iSpoof fraud is enormous. Even more worryingly, businesses and people haven’t wised up to these identity theft techniques.
Finally, the victory over iSpoof would be short-lived as scammers have an unlimited number of devices to target and as many attack vectors to exploit.



