
Source: Pixabay
Your network is no longer just a server with a few wires going to computers and a router. Now, your world is filled with IoT, edge, and mobile devices—all of which need access to your network. So network management is no longer simple. And this is why you need an NMS.
In the first part of this two-part series, I showed you why exactly you need an NMS. Its different hosting types give you the flexibility you need to address your business needs. Additionally, network management solutions offer many operational and security benefits.
But with many NMS solution providers on the market, choosing just one for your business can be hard. So in this article, I’ll walk you through the whole implementation process. I’ll show you what features you need to look for in an NMS, how to implement it, and finally, what you can do once your NMS is all set up.
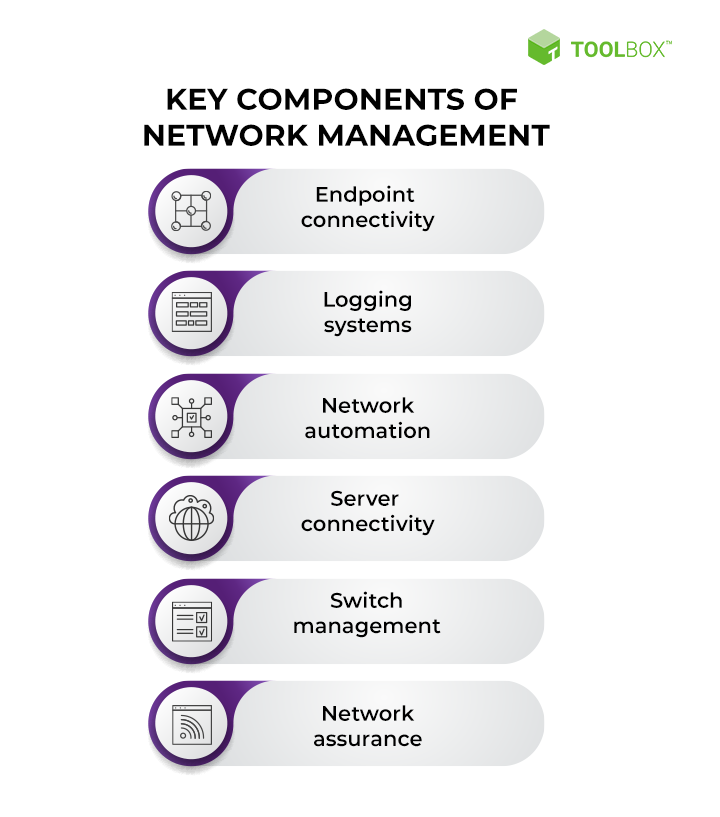
6 Network Management Solution Features
Network management solutions can have various features that make up the offering. Take a look at the most common and desirable features you must watch out for!
1. Endpoint Connectivity
If you can’t see what devices on your network are down, you can’t resolve the issue. Your users don’t care how things work, only that they do. And you’ll be the one to blame if you can’t keep uptime.
Endpoint connectivity flags down hardware when new devices attempt to connect. It helps identify the device correctly and centrally manage credential permissions. This saves you time managing network permissions and ensures you work to provide access precisely. Today’s networks are complex—they have multiple locations where blocking and access could cause a problem for the user or compromise your network.
An NMS with endpoint connectivity is invaluable, saving you from managing user requests yourself.
2. Logging Systems
If you’ve ever enabled logging on just one application server, you know the pains and pitfalls of doing this correctly. Enabling logging for only one server means you need to do this in a handful of locations. After waiting for a potential error, which could be a few days, you must go in and find each logger you enabled and turn them off.
But if your NMS orchestrates logging, you’ll save yourself this hassle. For example, you won’t risk missing a logger and compromising the server’s performance. You also won’t have to fix your server every time it falls over because of increasingly bigger log files.
So, choose an NMS with robust logging systems. It’ll handle all tedious tasks on multiple servers with different locations, and you’ll avoid the headache.
3. Network Automation
In increasingly complex networks, it’s hard to see everything going on. That’s why many people rely on network automation. But the problem is that you need to rely on your solution’s intelligence to meet your needs.
Network automation has an abstraction layer that takes the “intent” of the administrator and uses artificial intelligence (AI) or algorithms to implement actions. The abstraction layer allows users to create objectives through the layer. Then, it enables network traffic optimization and load balance. Additionally, it hardens potential attack surfaces. Clearly, an NMS with an automation feature is a must-have. But you shouldn’t go for just any automation feature. Instead, ensure your NMS clearly defines its automation processes and enables you to override its options should you need to. If your NMS has a robust automation feature, you’ll have better visibility over your network and an overall easier time managing your network.
Source: Spiceworks
4. Network Connectivity
Global businesses often separate sites using different domain names to help ensure bad actors can’t access intellectual property in other parts of the business. This is great for security but a challenge for global enterprises with over 500 networks!
Network management solutions can automatically find and connect segmented networks and domains. Network connectivity can use various technologies and protocols, depending on whether it’s intrasite or intersite. For example, if you’re using site-defined wide area networks (SD-WANs), then the NMS must provide this capability. Additionally, the NMS will also identify the hardware and what security and management it needs to apply. It is, in part, driven by the administrator’s intent, defined during the installation of the NMS solution.
So, look for an NMS with network connectivity options. And this will unify the management process for each network you add.
5. Switch Management

SOURCE: Flickr
Managed switches allow you to adjust each port’s behavior. And this extends to filtering ingress or egress traffic—not just allowing or disabling it. If you don’t have switch management, you can’t control data and traffic throughout your network.
So, the NMS you choose must allow you to govern which ports are available. It should also allow you to set access control policies and inspect data packets for security risks. The NMS should also optimize packet handling and reduce bottlenecks. To do this, it should level data speeds to meet your IPS’s line speeds.
When you choose an NMS with switch management capabilities, your network won’t be overworked, so its performance will be optimal. You’ll also reduce security risks and data leaks on your network. Finally, you’ll be able to monitor traffic at gateways for bad actors.
6. Network Assurance
Conducting network assurance over a small network is a time-intensive process and, thus, a major challenge for SMEs and larger businesses. But, you need it to determine how well your network will hold up to business growth and elevated traffic at peak hours.
An NMS with a network assurance feature helps you assess network paths and application connectivity. It also helps you check that your network is operational and capable of serving users. It can even provide you with quantitative data analytics to assess your network performance.
So, if you choose an NMS with network assurance, you’ll be able to effectively identify how robust your network is and what needs improvement or better optimization
Now that you know all the core features you should be looking for, you can start creating a shopping list that meets your business needs. But then what? How do you install your NMS once you have it? And who should be involved in the process?
5 Stages to Install an NMS

The NMS installation process can be divided into 5 steps. So once you create your shopping list based on the features above, buckle up and start following these steps!
1. Find the NMS You Want
Once you have a list of NMS solutions that provide all the features above, it’s time to decide which one best suits your specific needs. Don’t fall for all-in-one solutions that don’t have any of the features above.
Your NMS of choice should match your budget and business needs. You’ll also want to select which hosting type you need, whether on-prem or cloud-based. And with that in mind, start narrowing down your list of NMS providers. At this point, you might want to get other stakeholders involved. Create unbiased comparison decks to facilitate the decision.
2. Create a Test Environment
Once you’ve selected your NMS, you need to get a copy of it from the vendor and prove it on a test system. Remember that even if you have a test environment, you’ll need to update it using a copy of production taken after hours. Next, fire up the test network and ensure everything works and communicates as expected.
Also, ensure you’re not connected to the production system and have a restorable backup in case you make a mistake. You can attempt to ping your production servers from the development system to ensure it’s not available.
Congratulations on your test environment! Now, make a backup you can roll back to after proving its implementation.
3. Document the Installation Process
If installing the NMS yourself, you must document the installation process based on the vendor’s installation guide. The vendor does this step if you’ve outsourced this remotely using a VPN and multi-factor authentication (MFA) connection or working on-site.
If a vendor implements the NMS, you must provide access to both the production and test environments with administrator privileges, not what you think they need access to.
When you document your installation process, you need to take screenshots of your steps. Additionally, you must write clear documentation you can follow. Remember to enter commands by hand or copy and paste them into a plain text editor like notepad++ before adding them to the command window. This is to ensure they work correctly.
Once you have a working test environment with the NMS installed, it’s time to check that it works as intended.
4. Roll Back and Test Again
Once you have a working solution, roll the test environment back and test the process again. But why would you do that twice? You’ve just checked the solution, and it works. Isn’t that just inefficient?
Human error is the answer. You must ensure that you can follow your documentation to repeat the process. People make mistakes, and it’s best to identify any issues early in the process.
Test your solution works correctly with the platforms on your servers. You’ll need to design your testing process. This should include penetration testing and testing that the core features work as expected. Additionally, check your servers are all hardened, and erroneous ports are correctly blocked off after installation. You’ll need administrative and end-user testing to prepare you for the final roll-out successfully. For this reason, create testing documentation that a handful of end users and administrators can check and sign off during the testing process.
You should still document the second attempt and compare your original notes for missing information during this process.
5. Go-Live
SOURCE: FreeSVG
Once you have the green light to roll out your NMS, you need to book time with the stakeholders, create a backup of the production system, and implement the solution. Once complete, let your testers verify the installation while documenting the production system changes. You need to roll back the solution if something needs to be fixed.
During the first day of the changes you made, you need to be ready to combat any issues the production system has. Ensure you work closely with your support team to get visibility of issues from users. Additionally, investigate any problems to determine whether the NMS caused them or if they’re everyday issues.
If you find a problem you can’t fix, you’ll need to roll back the system with management’s permission. To this end, ensure you position this eventuality before this stage to manage the expectations of all involved.
Congratulations! You now have a network management system up and running in your production environment. Is it time to sit back and drink an espresso? Not so fast! Put down that miniature cup; you need to know your new solution’s capabilities and how you can use it!
What Are the Most Important Network Management Capabilities?
You’re looking at your new NMS like a chest of gold that’ll improve your position in life, but you’re unsure what to do next! Here you learn what you can do with your network management solution and discover how it might relieve your administrative burdens!
Complete Network Management
You can now detect and manage every facet of a network, from wide area networks to the internet of things (IoT), centrally from a dashboard. At this point, you can easily see the status of each device connected to your network. In addition, you can monitor performance and change device behavior.
In short, you can mitigate the potential risk of mismanagement, security flaws, or poor traffic moderation. To this end, ensure your NMS provides you with an automated device discovery capability that covers every device, not just servers and routers!
Security, Control, and Network Data
After installing your NMS, you can integrate next-generation firewalls, access ports and data scanning, and more. This allows you, rather than your NMS, to analyze packet contents for network threats.
When your NMS installs, it should automatically detect security flaws and optimize your system. In essence, you should have peace of mind with periodic and automated checking for exploits, exposed attack surfaces, and anomalous network traffic or activity. If anything is amiss, you’ll get an automated push notification via SMS or email to tell you the issue.
In addition, automated cybersecurity utilities ensure your system has the latest patches installed for the OS and applications you use. A complete all-in-one NMS will also contain an integrated VPN offering to help encrypt network traffic and use HTTPS by default for all connections.
Final Thoughts
And there you have it! Right now, managing your network should be a breeze. And you’ll finally reap the benefits of spending so much time choosing and implementing an NMS.
This two-part series aimed to show you why and how you should get an NMS for your business. In this second part, I showed you which features your NMS must have. And once you decide which NMS you want, it’s time to test and document the installation process. This will help you ensure your solution is working as intended and you know how to fix any issues that pop up.
You’ll have some time between the initial test implementation and the go-live date, so accurate documentation is crucial. To this end, run a second round of testing to ensure your documentation is correct and you can repeat the implementation process. In addition, you’ll need to communicate clearly with all stakeholders and use your time efficiently. Always remember to document the time it takes to run each step.
Finally, remember to take backups of your production system and create a test environment from production data. You can verify your backups work correctly and ensure your test environment accurately represents your production environment.
Do you have more questions about NMS solutions? Check out our FAQ and Resources sections below!
FAQ
What’s the difference between managed and unmanaged switches?
An unmanaged switch routes connections to their destination using the IP address in data packet headers. Managed switches often have intelligent features for inspecting data and traffic filtering tools. Additionally, a managed switch often logs network traffic and allows administrators to access logs through the switch address.
Do I need a cybersecurity team for threat hunting?
Threat hunting is beneficial. But, you must have the money to employ or outsource a cybersecurity team to do it. Skilled penetration testers and cybersecurity teams can interpret the signs of a threat and find advanced threats that a software solution cannot. If you can’t afford a cybersecurity team, the next best thing is a network management solution that integrates cybersecurity tools.
Should I only consider external threats to my network or internal ones too?
You need to consider both for the safety of your network. Many administrators assume firewalls and antivirus are good enough for network security. However, these tools won’t be effective if a bad actor has access to your network and operates in it. Consider using a network management solution to help you identify internal threats.
What is ITAM?
IT asset management (ITAM) is the process of creating and maintaining accurate asset records for your business. You need this information to help you evaluate the worth of your company and understand your business’s capability to function effectively. To do this successfully, you need to create a unique id and use an effective means to tag hardware.
Does a network management solution (NMS) shape network traffic?
Yes, all NMS solutions should be able to monitor and maintain efficient network traffic. This includes assessing committed information rates against ISP line rates and optimizing communications between nodes and load balancing. When optimized, you need fewer hardware resources to maintain your network and improve end-user experience.
Resources
TechGenix: Article on Backups for SMEs
Learn about the best backup strategies for small-medium enterprises.
TechGenix: Article on Top Cloud Backup Solutions
Discover the best cloud backup solutions to protect your data.
TechGenix: Article on Protecting Your Backups
Find out how to protect your backups and ensure they work when you need them.
TechGenix: Article on Protecting Backups against Ransomware Attacks
Learn how to protect your backups against ransomware attacks to keep your system running.
TechGenix: Article on the Different Types of VPNs
Get to grips with all the different VPN types available to your business.



