
Source: Privecstasy via Unsplash.com
A virtual private network, or VPN, is a secured remote server used to relay the entirety of one’s internet connection through that server. Similarly to how a private VPN masks the person’s IP address, a site-to-site VPN, or S2S VPN, also provides a specific IP address. Then, separate on-site servers in different business branches recognize and accept these IP addresses.
That said, you might see this topology where all the branch servers must connect to the main branch through a direct hierarchy as slightly obsolete. With many companies moving to cloud-based servers, it’s easier for the whole company to share the same cloud server. However, site-to-site VPNs still have benefits.
In this article, I’ll discuss site-to-site VPNs, their benefits, and some of their limitations. Later, I’ll touch on the different types of VPNs and tools you can use to make the most of them.
What Is a Site-to-Site VPN?
A site-to-site VPN is a connection meant to link a corporate network in a company and its branch offices across different geographical locations. It can vary from simple modems to advanced server and cloud setups. Essentially, this depends on the bandwidth, communication, and internet access needs of your company and its branches.
You could presume that a server in a singular branch is traditional. Individual devices connect to the same on-site server when they require any information, documentation, or verification.
That said, instead of the branch server connecting to the main server for updates and changes in direction, it’ll go through one more server. This highly secure server will often store nothing, and be in a different location to the branch. Its purpose is only to relay data packets from the branches to the main server and vice versa.
In return, this setup helps prevent a vast array of cybersecurity attacks. For example, some of these attacks are Man-In-The-Middle (MITM) attacks, external hacks, and snooping.
Although faced with some limitations, site-to-site VPNs have many benefits. I’ll go through those next.
Benefits and Limitations of Site-to-Site VPNs
Although site-to-site VPNs bring in more benefits than trouble, you’ll still find some limitations to the method. That’s because this system offers the invisibility of your company’s system on the network instead of direct cybersecurity defense from attack vectors. Let’s now see what these benefits and limitations are.
| Benefits of Site-to-Site VPNs | Limitations of Site-to-Site VPNs |
| Vastly improved security | No end-point security |
| Improved company privacy | Secure and unsecured devices may share ports |
| Faster inter-branch communication | Increased communication complexity |
| Reduced system maintenance cost | |
| Easy data-loss prevention | |
| Easy disaster recovery |
Next, I’ll discuss why investing in site-to-site VPNs is a good choice.
Why Implement a Site-to-Site VPN?
Although a site-to-site VPN is very beneficial, its full capabilities are primarily visible in large companies with many locations, especially if the company is based in multiple countries. For smaller operations, it’s often better to use a cloud-based solution.
That said, if you use an advanced topology for your business, a site-to-site VPN will be priceless. This is the case since site-to-site VPNs:
- Reduce monitoring expenses: A limited number of IP addresses can contact the main server and branch servers.
- Reduce threat actor damage potential: Branch servers have limited access to company data and are often read-only, reducing the damage potential if an attack happens.
- Provide easy sandboxing implementation: Attackers won’t know if they have reached the sandbox or the real server.
You may wonder if site-site-site VPNs have different types. Well, they do! I’ll quickly go through these types in the next section mentioning their pros and cons.

Source: benjamin lehman via Unsplash.com
3 Site-to-Site VPN Types
The types of site-to-site VPN connections depend on the location of the secure relaying server and how you operate it.
Having on-site servers is the most reasonable and cost-efficient option for some companies. Companies that focus on cybersecurity and have the tools and expertise at their disposal are great examples. That said, for companies that have recently expanded and don’t have the expertise on hand, it might be better to rent out the know-how.
1. Remote Access VPNs
For this type, the company still owns and operates the VPN server. The server location is outside any known sites, though. Most cyber threat intelligence will also point out that no one should know the location of this server except a handful of people.
Usually, the branches won’t even know about having a secure server between their location and the main office. The VPN app will work on vetted devices in the background, allowing easy access to all relevant data. All other internet connections in the branch will also connect to the internet directly, except for the devices in question.
| Pros | Cons |
| Extremely improved privacy | Very restricted company access |
| Easily upgradable cybersecurity | Growing cost depending on the distance from HQ |
2. Intranet-Based Site-to-Site VPN
The intranet is the communication between different parts of the same company. It’ll always include all the connected devices like servers, desktops, and even mobile devices with adequate access.
The company will also own the intranet site-to-site VPN. It’ll station it inside the branches or, more commonly, the main office. Thus, the same people maintaining and supervising the main server will also handle it.
| Pros | Cons |
| Easy maintenance and monitoring | Susceptible to side-channel attacks |
| Reduced overhead costs | Known server location |
3. Extranet-Based Site-to-Site VPN
Finally, the last type of site-to-site VPN connection is the one where you rent out a professional VPN server to serve your company. While this isn’t cost-effective, it does have certain benefits.
Any intrusion into the VPN server will be your VPN provider’s fault. This will diminish the liability expected from your company when it comes to private information.
The second advantage is maintenance and compliance. Professional VPN management will comply perfectly with all the current legislation and standards. The company providing the VPN will also maintain the encrypted servers.
| Pros | Cons |
| Reduced liability | Reduced control |
| Ensured compliance | Potential jurisdiction issues |
I’ll now walk you through setting up a site-to-site VPN

Source: Yuriy Bogdanov via Unsplash.com
How to Create a Site-to-Site VPN?
Before setting up a site-to-site VPN, you need to know whether you want the branch offices to see each other, or if they’ll get updates through the main office server. The latter is much simpler and offers more security. That said, it’ll also offer fragmented visibility of the company for the branches.
Additionally, I’ll presume that you’ve connected all the devices in each branch to the branch server properly and securely. With that in mind, you can follow these 7 steps to set up your S2S VPN:
- Install one more server from the discussed types of site-to-site VPNs
- Assign one IP address to each of the branches and the main server
- Set a rule to accept and send from the main server only to those IPs
- Set a rule to allow only known IP addresses to connect to the VPN server
- Decide if branches may communicate directly
- Set rules for inter-branch communication exclusively through the VPN server if applicable
- Install a kill switch to branch network adapters for main devices. That way, they can’t connect to the rest of the internet, which isn’t VPN-protected
At this point, your VPN will be online, and it’s on you to choose which encryptions you’ll place on the VPN server and how much bandwidth you’ll allow.
3 Key Components of Site-to-Site VPNs
VPNs, in general, are very simple. So are site-to-site VPNs. You’ll only have 3 components to worry about:
1. Connection
Your internet service provider (ISP) will often provide the connection. You’ll need to ensure you have enough bandwidth to cover all branches connecting to that particular server.
A good and primarily stable internet connection for the main server, the VPN server, and all the branches will allow quick communication. It’ll also ensure that the VPN kill switch doesn’t activate often.
| Pro Tip Try to use a different ISP for your VPN server than you do for your company. This will prevent anyone with limited modem access from even seeing the connections. |
2. Protection
Protection includes all the cybersecurity tools and services the VPN server will use. These can and should be excessive because the device isn’t used for anything else. Thus, you should include multiple anti-viruses, anti-spyware, and other search-and-destroy software.
A highly-protected VPN server will serve as a dam for malware and intrusions. That means, even if attackers breach and compromise one branch, the skill and tools necessary for breaching further would also jump several-fold.
| Pro Tip Remember that nothing is overkill when it comes to VPN servers. Use a sandbox with a set of cybersecurity measures rarely found in sandboxes. Then, have a different set on the real server. That’ll stop virtually every attack. |
3. Encryption
Encryption should be the Advanced Encryption Standard (AES) with a 256-bit algorithm. This encryption should have keys on the branch and main servers, and you can even exclude it from the VPN server. That means anyone who manages to gain access will see the data scrambled beyond repair.
Advanced encryptions, preferably with P2P keys, will prevent anyone from gathering your data through a Man-in-the-Middle (MITM) attack. Even if they find the local ISP server, they’ll only have scrambled data which is useless.
| Pro Tip Set your keys in a Master-Slave alternating configuration. That means all the keys must change regularly. Each branch should also have a different one, only known to the main server. This will easily protect the system in a case of a branch breach. |
For small and medium companies, it’s still better to have a professional company manage all of this. Why is that? I’ll go through the benefits of a managed VPN service now.
The Benefits of Managed VPN Services
Monitoring is the main reason anyone would use a managed VPN service. This is especially the case for larger companies or small and medium enterprises (SMEs) with no staff to look through each server.
A managed VPN service will also be essential for companies with throngs of remote workers having access to the main server. A managed service allows you to operate firewalls and monitor intrusions and issues. Additionally, it lets you filter out what can be shared between the main server and the branches. Also, unlike manual management, this would allow for easy control over even the most complex of server topographies.
Now, let’s go over some of the top VPN solutions your company can benefit from.
Top 3 VPN Solutions
Below are some excellent VPN solutions for your business or to use daily.
1. KerioControl
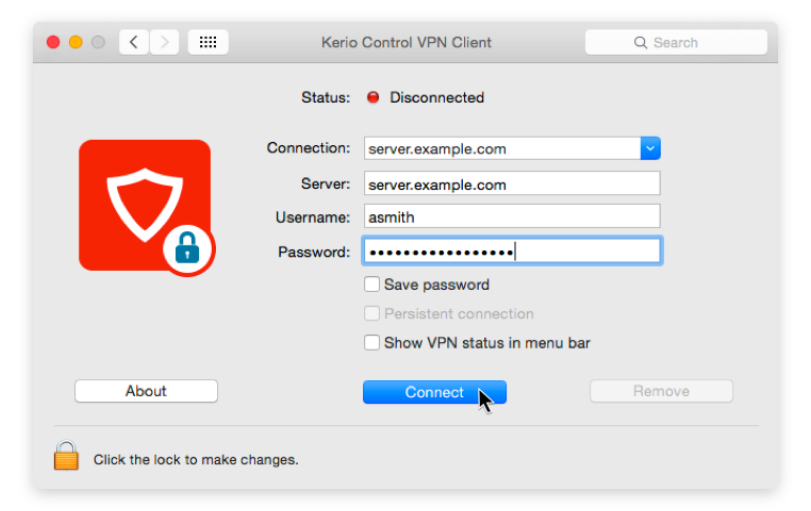
KerioControl probably has the best balance between capability, accessibility, and cost among all other VPN management services. It offers a simple app available on both Windows and macOS, connecting all the devices you wish through a very pleasing UI.
KerioControl can also actively scan the traffic going through your VPN server for many viruses, trojans, and other malware.
In addition, KerioControl allows you to set up firewalls and connection rules on the fly and check the access of each component on the networks. Similarly, you can manage accessible bandwidth for any branch to optimize the available resources.
2. NordVPN

NordVPN has many exciting features. For instance, it has the Meshnet, which enables you to connect directly to devices through an encrypted tunnel. It also has other advanced VPN features like dark web monitoring to inform you about any data breaches and leaks.
In addition, NordVPN enables you to obfuscate your servers from others. This is a useful tool against cybercriminals who aim to steal information about your business. On the other hand, most VPN providers only encrypt the main body of each packet. Thus, attackers can still find out who you’re trading with or your clients from the IP address and header.
Imagine you’re an automotive manufacturer wanting to integrate new intellectual property. You don’t want your competitors to discover what you’re up to before releasing the final product. Thus, hiding headers on each pack is critical to your success.
Overall, NordVPN is a jam-packed VPN with elegant solutions for your enterprise security.
3. Surfshark VPN

Surfshark is a highly popular VPN service that provides a solid VPN service. This VPN bypasses your ISP’s servers and provides you with an IP address from anywhere in the world. Thus, you’ll be able to access services like video content as if you were in that country.
In terms of enterprise solutions, Surfshark also shines. It has a no-log policy, a kill switch, and AES-256 encryption, which almost all VPNs have today. That said, one of the best points of Surfshark is you can use it for an unlimited number of devices. This is a massive benefit for your business, especially if you’re a small business owner who can purchase more feature-rich options.
Now, we can finally wrap up everything we’ve learned about site-to-site VPNs.
Final Words
A site-to-site VPN is a virtual private network that securely accesses the company’s main server from one of the branch servers or remote devices. Aside from added security, the benefits of site-to-site VPN are easier cybersecurity management, faster communication, and data loss prevention. That said, these benefits only relate to the VPN server and the connection itself. Thus, they won’t encompass the devices not connected to the VPN.
Companies can opt to have the VPN server on the same premises as the regular servers or somewhere remotely where it’s safer. This will depend on their requirements. Alternatively, companies can also have a third party manage the connection, which helps with compliance and liability.
Finally, having software for managing VPN connections has considerable benefits. For example, you can monitor all connections easily, block any unwanted connections, and optimize all connections to your company’s specifications.
Do you have more questions about site-to-site VPNs? Check out the FAQ and Resources sections below.
FAQ
Are site-to-site VPN connections private?
Site-to-site VPN connections aren’t private since the people with access to any connected device will be privy to the information. These connections provide privacy from anyone outside of the company. They also make it hard for anyone to assault the main server through the internet without a specific encryption key.
Is a site-to-site VPN better than a regular VPN?
Site-to-site VPNs are better for companies. A regular VPN will mask the user’s IP address against the internet. Meanwhile, a site-to-site VPN will connect only to a single server. Thus, it’ll offer even more privacy and removes the capability to access the internet and the main server at the same time.
Do site-to-site VPN connections cost a lot?
The cost of a VPN is the server device, the tools to protect it, and the bandwidth it’ll use. That said, these costs are scalable. Even for smaller SMEs, the cost will be a minor impact on the cybersecurity budget proposed in the cybersecurity strategy.
How much bandwidth do site-to-site VPNs use?
You should always expect some lag and bandwidth loss when using a VPN. That said, these losses would range between 1% and 5% of the total bandwidth available to the VPN server. That depends if the distance between the VPN server and the main servers isn’t the entire globe.
Is site-to-site VPN worth it?
For single-venue enterprises, a site-to-site VPN isn’t worth the trouble. That said, a site-to-site VPN is useful for operations with multiple locations and especially those with many remote employees. It’ll be an easy and cheap way to improve monitoring and secure those connections.
Resources
TechGenix: Newsletters
Subscribe to our newsletters for more quality content.
TechGenix: Article on Virtual Private Networks
Discover the best VPN networks for your company.
TechGenix: Guide for SSL VPNs
Enhance your knowledge of SSL VPNs and what they can do for you.
TechGenix: Article on Business VPNs
Dive into the intricacies of business VPN options and advantages.
TechGenix: Article comparing WARP and VPN for Online Security
Find out about the differences between WARP and VPN.
TechGenix: Article on Cloud Architecture
Check out our article on cloud architecture and its capabilities.



